Offloading Kerberos authentication from physical servers
The Citrix ADC appliance can offload authentication tasks from servers. Instead of the physical servers authenticating the requests from clients, the Citrix ADC authenticates all the client requests before it forwards them to any of the physical servers bound to it. The user authentication is based on Active Directory tokens.
There is no authentication between the Citrix ADC and the physical server, and the authentication offload is transparent to the end users. After the initial logon to a Windows computer, the end user does not have to enter any additional authentication information in a pop-up or on a logon page.
In the current Citrix ADC appliance release, Kerberos authentication is available only for authentication, authorization, and auditing traffic management virtual servers. Kerberos authentication is not supported for SSL VPN in the Citrix Gateway Advanced Edition appliance or for Citrix ADC appliance management.
Kerberos authentication requires configuration on the Citrix ADC appliance and on client browsers.
To configure Kerberos authentication on the Citrix ADC appliance
-
Create a user account on Active Directory. When creating a user account, verify the following options in the User Properties section:
- Make sure that you do not select the Change password at next logon option.
- Be sure to select the Password does not expire option.
-
On the AD server, at the CLI command prompt, type:
- ktpass -princ HTTP/kerberos.crete.lab.net@crete.lab.net -ptype KRB5_NT_PRINCIPAL -mapuser kerbuser@crete.lab.net -mapop set -pass Citrix1 -out C:\kerbtabfile.txt
Note
Be sure to type the above command on a single line. The output of the above command is written into the C:\kerbtabfile.txt file.
-
Upload the kerbtabfile.txt file to the /etc directory of the Citrix ADC appliance by using a Secure Copy (SCP) client.
-
Run the following command to add a DNS server to the Citrix ADC appliance.
- add dns nameserver 1.2.3.4
The Citrix ADC appliance cannot process Kerberos requests without the DNS server. Be sure to use the same DNS server that is used in the Microsoft Windows domain.
-
Switch to the command line interface of Citrix ADC.
-
Run the following command to create a Kerberos authentication server:
- add authentication negotiateAction KerberosServer -domain “crete.lab.net” -domainUser kerbuser -domainUserPasswd Citrix1 -keytab /var/mykcd.keytab
Note
If keytab is not available, you can specify the parameters: domain, domainUser, and -domainUserPasswd.
-
Run the following command to create a negotiation policy:
add authentication negotiatePolicy Kerberos-Policy "REQ.IP.DESTIP == 192.168.17.200" KerberosServer<!--NeedCopy-->
-
Run the following command to create an authentication virtual server.
add authentication vserver Kerb-Auth SSL 192.168.17.201 443 -AuthenticationDomain crete.lab.net<!--NeedCopy-->
-
Run the following command to bind the Kerberos policy to the authentication virtual server:
bind authentication vserver Kerb-Auth -policy Kerberos-Policy -priority 100<!--NeedCopy-->
-
Run the following command to bind an SSL certificate to the authentication virtual server. You can use one of the test certificates, which you can install from the GUI Citrix ADC appliance. Run the following command to use the ServerTestCert sample certificate.
bind ssl vserver Kerb-Auth -certkeyName ServerTestCert<!--NeedCopy-->
-
Create an HTTP load balancing virtual server with the IP address, 192.168.17.200.
Ensure that you create a virtual server from the command line interface for NetScaler 9.3 releases if they are older than 9.3.47.8.
-
Run the following command to configure an authentication virtual server:
set lb vserver <name>-authn401 ON -authnVsName Kerb-Auth<!--NeedCopy-->
-
Enter the host name Example in the address bar of the Web browser.
The Web browser displays an authentication dialog box because the Kerberos authentication is not set up in the browser.
Note
Kerberos authentication requires a specific configuration on the client. Ensure that the client can resolve the hostname, which results in the Web browser connecting to an HTTP virtual server.
-
Configure Kerberos on the Web browser of the client computer.
- For configuring on Internet Explorer, see Configuring Internet Explorer for Kerberos authentication.
- For configuring on Mozilla Firefox, see Configuring Internet Explorer for Kerberos authentication.
-
Verify whether you can access the backend physical server without authentication.
To configure Internet Explorer for Kerberos authentication
- Select Internet Options from the Tools menu.
- Activate the Security tab.
- Select Local Intranet from the Select a zone to view change security settings section.
- Click Sites.
- Click Advanced.
- Specify the URL, Example and click Add.
- Restart Internet Explorer.
To configure Mozilla Firefox for Kerberos authentication
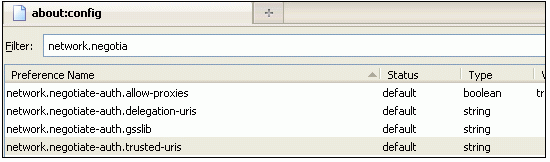
- Enter about:config in the address bar of the browser.
- Click the warning disclaimer.
- Type Network.Negotiate-auth.trusted-uris in the Filter box.
-
Double click Network.Negotiate-auth.trusted-uris. A sample screen is shown below.
- In the Enter String Value dialog box, specify www.crete.lab.net.
- Restart Firefox.