Citrix ADC Support for Microsoft Direct Access Deployment
Microsoft Direct Access is a technology that enables remote users to seamlessly and securely connect to the enterprise’s internal networks, without the need to establish a separate VPN connection. Unlike VPN connections, which require user intervention to open and close connections, a Direct Access-enabled client connects automatically to the enterprise’s internal networks whenever the client connects to the Internet.
Manage-Out is a Microsoft Direct Access feature that allows administrators inside the enterprise network to connect to Direct Access clients outside the network and manage them (for example, performing administration tasks, such as scheduling service updates, and providing remote support.
In a Direct Access deployment, Citrix ADC appliances provide high availability, scalability, high performance, and security. Citrix ADC load balancing functionality sends client traffic through the most appropriate server. The appliances can also forward Manage-Out traffic through the right path to reach the client.
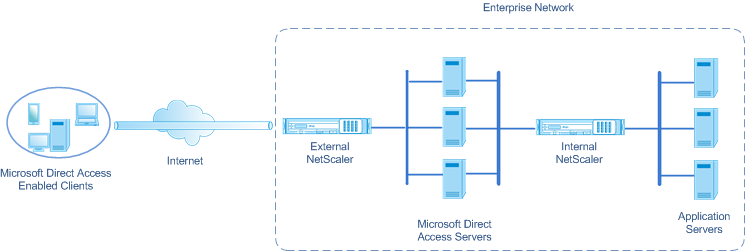
Architecture
The architecture of a Microsoft Direct Access deployment consists of Direct Access enabled clients, Direct Access servers, application servers, and internal and external Citrix ADC appliances. Clients connect to an application server through a Direct Access server. An external Citrix ADC appliance load balance the client traffic to a Direct Access server, and an Internal Citrix ADC appliance forwards the client traffic from the Direct Access server to the destination application server. Direct Access is used for tunneling the client’s IPv6 traffic over the IPv4 network. An IPv4 load balancing virtual server on the external Citrix ADC appliance load balances the client’s tunneled traffic to one of the Direct Access servers. The Direct Access server extracts the IPv6 packets from the received client’s IPv4 packets and sends them to the destination application server through the internal Citrix ADC appliance. The Internal Citrix ADC appliance has forwarding session rules with the source route cache option enabled for storing Layer 2 and Layer 3 connection information about the client’s traffic from the Direct Access Server. The Citrix ADC appliance stores the following Layer 2 and Layer 3 information in a table called the source route cache table:
- Source IP address of the received packet
- MAC address of the Direct Access server that sent the packet
- VLAN ID of the Citrix ADC appliance that received the packet
- Interface ID of the Citrix ADC appliance that received the packet
The Citrix ADC appliance uses the information in the source route cache table for forwarding a response to the same Direct Access server because it has the tunneling information to reach the client. Also, the Internal appliance uses the source route cache table to forward application server’s Manage-out traffic to the appropriate Direct Access server to reach a particular client.
Configuring the Internal Citrix ADC Appliance in a Microsoft Direct Access Deployment
To configure the Internal Citrix ADC appliance for forwarding an application server’s response and manage-out traffic to the appropriate Direct Access Gateway, configure forwarding session rules. In each rule, set the sourceroutecache parameter to ENABLED.
To create a forwarding session rule by using the CLI:
At the command prompt, type:
- **add forwardingSession** <name> ((<network> [<netmask>]) | **-acl6name** <string> | **-aclname** <string>) **-sourceroutecache** ( **ENABLED** | **DISABLED** ]
- show forwardingsession <name>
Sample configuration:
In the following example, forwarding-session rule MS-DA-FW-1 is created on the internal Citrix ADC appliance. The forwarding session stores Layer 2 and Layer 3 information for any incoming IPv6 packets from a Direct Access server that matches source IPv6 prefix 2001:DB8::/96.
> add forwardingSession MS-DA-FW-1 2001:DB8::/96 -sourceroutecache -ENABLED
Done
Displaying the Source Route Cache Table
You can display the source route cache table for monitoring or detecting any unwanted connections between direct access servers and application servers.
To display the source route cache table by using the CLI:
At the command prompt, type:
- show sourceroutecachetable
Example:
> show sourceroutecachetable
SOURCEIP MAC VLAN INTERFACE
2001:DB8:5001:10 56:53:24:3d:02:eb 30 1/2
2001:DB8:5003:30 60:54:35:3e:04:bd 60 1/3
Done
Clearing the Source Route Cache Table
You can clear all the entries from the source route cache table on a Citrix ADC appliance.
To clear the source route cache table by using the CLI:
At the command prompt, type:
- flush ns sourceroutecachetable