-
Basic components of authentication, authorization, and auditing configuration
-
-
401 based authentication
-
On-premises NetScaler Gateway as an identity provider to Citrix Cloud
-
Authentication, authorization, and auditing with commonly used protocols
-
Troubleshoot authentication and authorization related issues
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
401 based authentication
With 401 based Authentication, the NetScaler appliance presents a pop-up dialog box to the end user.
Form based AAA-TM works on the redirect messages. Some applications do not support redirects, in such cases the 401 authentication enabled AAA-TM is used.
Enable the following parameters for 401 Authentication AAA-TM to work.
-
‘authnVsName’ parameter value for the load balancing virtual server must be the name of the authentication virtual server to be used to authenticate users.
-
‘authn401’ parameter must be enabled. The command for configuring the same is as follows:
set lb vs lb1 –authn401 on –authnvsName <aaavs-name>
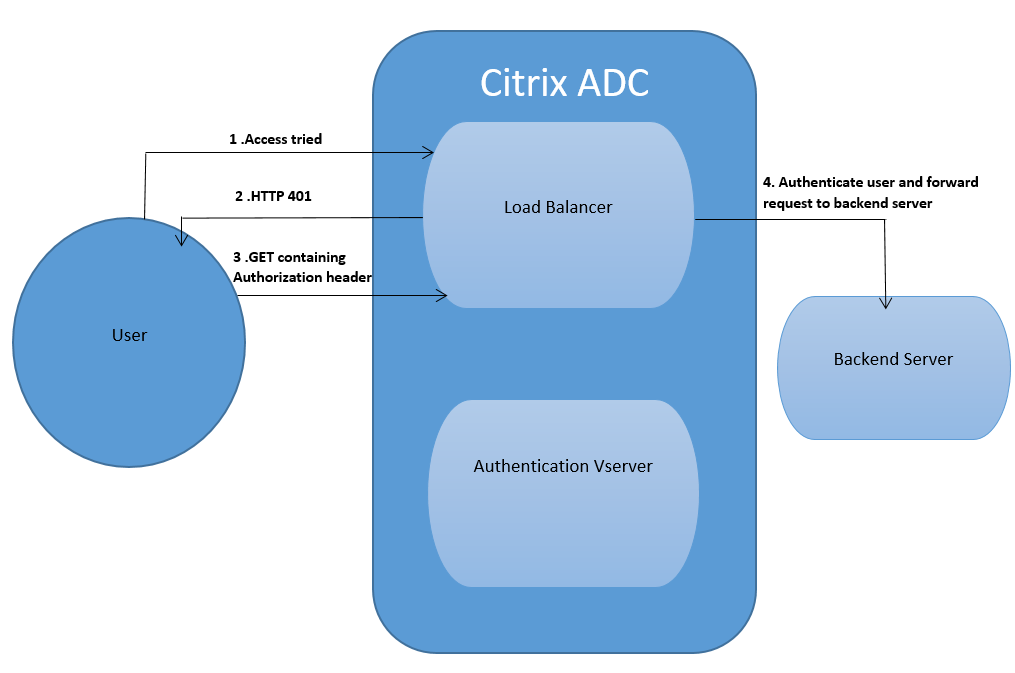
The following steps walk through how the 401 Authentication works:
-
User tries to access a particular URL using the load balancing virtual server.
- The load balancing virtual server sends a 401 HTTP response back to the user indicating that authentication is required for the access.
- The user sends its credentials to the load balancing virtual server in the authorization header.
-
The load balancing virtual server authenticates the user and then connects the user to the back end servers.
Important:
For a load balancing virtual server with 401 authentication ON, several authentication and authorization sessions might be created for the same user in a short time. This configuration might lead to a spike in the memory. You can apply the following configuration on the NetScaler appliance to debug and identify the end client application.
set syslogparams -userDefinedAuditlog yes
add audit messageaction 401_log_act InFORMATIONAL '"LB-401 accessed: User: <" + AAA.USER.NAME + "> SessionID <"+ AAA.USER.SESSIONID + "> Client :<" + CLIENT.IP.SRC + "> accessed URL: <" + HTTP.REQ.URL + ">"'
add rewritepolicy rewrite_401_log true NOREWRITE -logAction 401_log_act
bind lb vserver <lb_name> -policyName rewrite_401_log -priority 100 -type reqUEST
<!--NeedCopy-->
Share
Share
In this article
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.