Configure LDAP authentication on the NetScaler appliance for management purposes
You can configure user logon to the NetScaler appliance using the active directory credentials (user name and password) for management purposes (superuser, read-only, network privileges and all others).
Prerequisites
- Windows Active Directory domain controller servers
- A dedicated domain group for NetScaler administrators
- NetScaler Gateway 10.1 and later versions
The following figures illustrate the LDAP authentication on the NetScaler appliance.
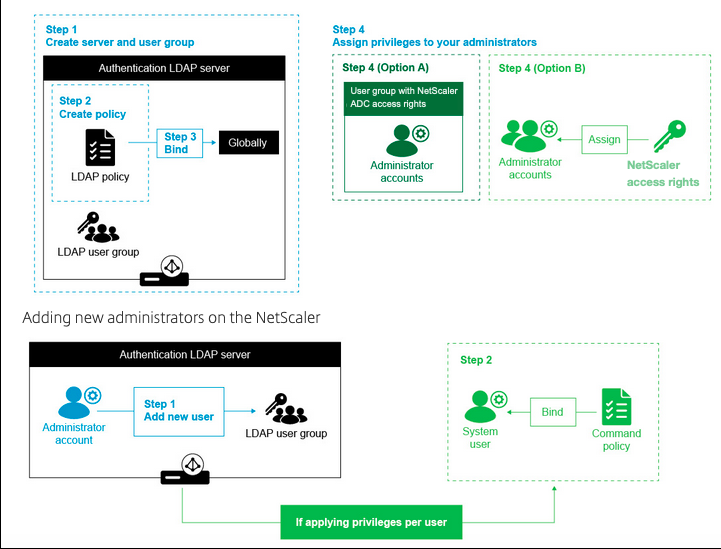
High level configuration steps
- Create an LDAP server
- Create an LDAP policy
- Bind the LDAP policy
- Assign privileges to your administrators by one of the following ways
- Apply privileges on group
- Apply privileges individually for each user
Create an authentication LDAP server
- Navigate to System > Authentication > LDAP.
- Click the Server tab and then click Add.
- Complete the configuration, and then click Create.
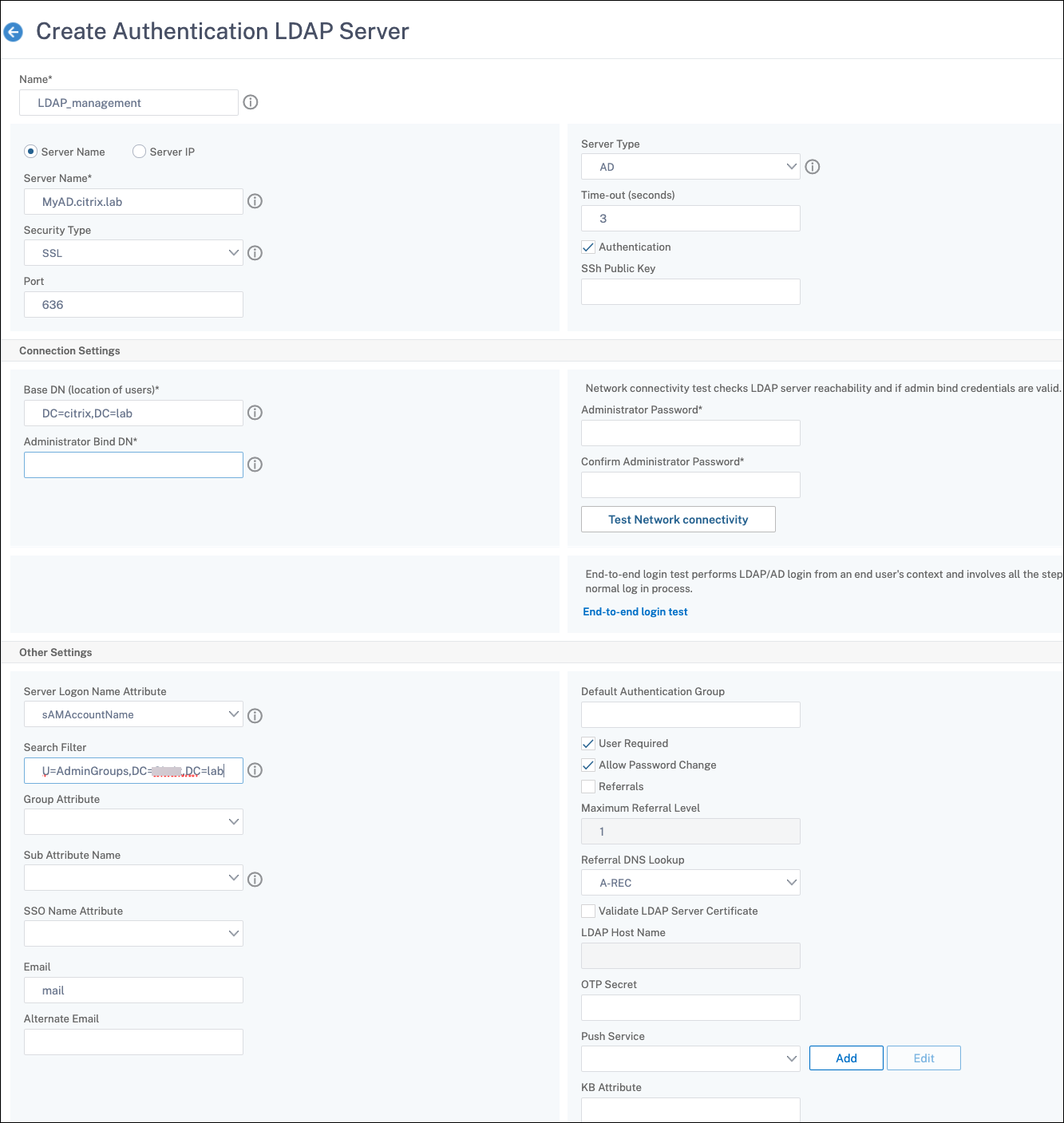
Note:
In this example, the access is limited to the NetScaler appliance by filtering the authentication on the user group membership by setting Search Filter. The value used for this example is - &(memberof=CN=NSG_Admin,OU=AdminGroups,DC=Citrix,DC=lab)
Create an LDAP Policy
- Navigate to System > Authentication > Advanced Policies > Policy.
- Click Add.
- Enter a name for the policy, select the server that you created in the previous steps.
- In the Expression text field, enter the appropriate expression, and then click Create.
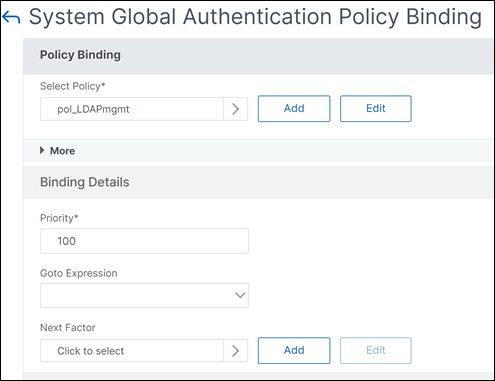
Bind the LDAP policy globally
- Navigate to System > Authentication > Advanced Policies > Policy.
- In the Authentication Policies page, click Global Bindings.
- Select the policy you created (in this example, pol_LDAPmgmt).
- Choose a priority accordingly (the lower the number, the higher the priority)
- Click Bind, and then Done. A green checkmark appears in the Globally Bound column.
Assign privileges to your administrators
You can choose one of the following two options.
- Apply privileges on a group: Add a group in the NetScaler appliance and assign the same access rights for each user who is a member of this group.
- Apply privileges individually for each user: Create each user administrator account and assign rights for each of them.
Apply privileges on a group
When you apply privileges on a group, users who are member of the Active Directory group configured in the Search filter (in this example, NSG_Admin) can connect to the NetScaler Management interface and have superuser command policy.
- Navigate to System > User Administration > Groups.
- Enter the details as per the requirement, and then click Create.

You have defined the active directory group that the users belong to and also the command policy level that must be associated to the account when logging in. You can add new administrator users to the LDAP group you configured on the search filter.
Note:
The group name must match the active directory record.
Apply privileges individually for each user
In this scenario, users who are member of your Active Directory group configured in the search filter (in this example, NSG_Admin) can connect to the NetScaler management interface but do not have any privileges until you create the specific user on the NetScaler appliance and bind the command policy to it.
- Navigate to System > User Administration > Users.
- Click Add.
-
Enter the details as per the requirement.
Note: Make sure to select Enable External Authentication.
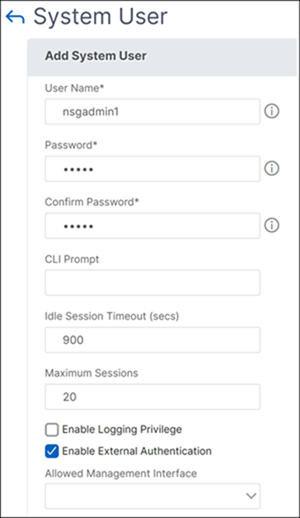
- Click Continue.
You have defined the active directory user and the command policy level that must be associated to the account when logging in.
Note:
- The user name must match the existing user’s active directory record.
- When you add a user to the NetScaler for external authentication, you must provide a password, if the external authentication is not available. For the external authentication to work properly, the internal password must not be the same as the user account LDAP password.
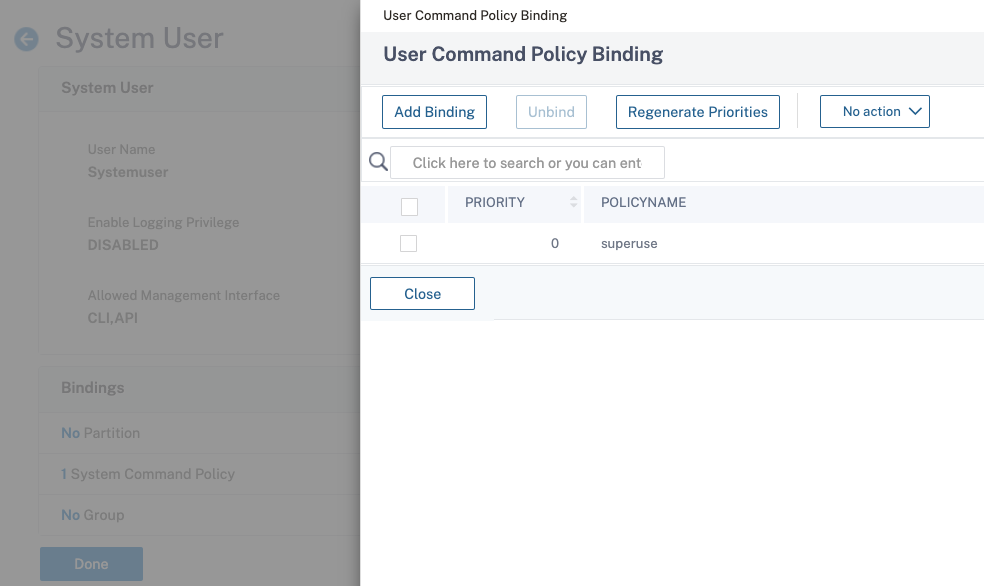
Add command policy to the user
- Navigate to System > User Administration > Users.
- Select the user that you created, and then click Edit.
- In Bindings, click System Command Policy.
- Select the correct command policy to apply to your user.
- Click Bind, then click Close.
To add more administrators;
- Add the administrator users to the LDAP group you configured on the search filter.
- Create the system user in NetScaler and assign the correct command policy.
To configure LDAP authentication on the NetScaler appliance for management purposes by using the CLI
Use the following commands as a reference to configure log on for a group with superuser privileges on the NetScaler appliance CLI.
-
Create an LDAP server
add authentication ldapAction LDAP_mgmt -serverIP myAD.citrix.lab -serverPort 636 -ldapBase "DC=citrix,DC=lab" -ldapBindDn readonly@citrix.lab -ldapBindDnPassword -ldapLoginName sAMAccountName -searchFilter "&(memberof=CN=NSG_Admin,OU=AdminGroups,DC=citrix,DC=lab)" -groupAttrName memberOf <!--NeedCopy--> -
Create and LDAP policy
add authentication ldapPolicy pol_LDAPmgmt ns_true LDAP_mgmt <!--NeedCopy--> -
Binding the LDAP policy
bind system global pol_LDAPmgmt -priority 110 <!--NeedCopy--> -
Assign privileges to your administrators
- To apply privileges on the group
add system group NSG_Admin bind system group NSG_Admin -policyName superuser 100 <!--NeedCopy-->- To apply privileges individually for each user
add system user admyoa bind system user admyoa superuser 100 <!--NeedCopy-->