Dynamic profiling
The learning feature is a pattern filter that observes and learns activities on the back-end server. Based on the observation, the learning engine generates up to 2000 rules or exceptions (relaxations) for each security check. To automate the process and auto deploy the relaxation rules, NetScaler appliance uses dynamic profiling.
With dynamic profiling, the appliance records the learnt data for a pre-defined threshold and sends an SNMP alert to the user. If the user does not skip the data within a grace period, the appliance auto deploys it as a relaxation rule. Earlier, the user had to manually deploy the relaxation rules. Currently, dynamic profiling is available only for the follow security checks:
- HTML SQL injection
- HTML Cross Site scripting
- Field format
- Start URL
- Content-type
- Field formats
- CSRF form tagging
- Cookie consistency
- Deny URL
- Buffer Overflow
- Credit Card
- Content-type protection
- JSON Cmd Injection protection
For example, consider the HTML SQL Injection security check enabled with dynamic profiling. You can use learning for a list of IPs (called the Trusted Learning Clients list) from which the learning feature must generate recommendations. To configure a list of trusted clients, see Learning Trusted Clients topic. If the incoming traffic has violations, it is recorded as a learnt data. If the learned data is recorded in the learning engine, the appliance sends an SNMP alert to the user. If the user does not recognize a false positive and does not skip the learnt data within a grace period, the appliance auto deploys it as a relaxation rule.
Note: After you configure the dynamic profile, you must periodically review the appliance configuration for the auto-deployment of the relaxation rules and save it on the appliance.
Configure dynamic profiling by using the NetScaler command interface
Dynamic profiling is available for Start URL, HTML Cross-Site Scripting, Field Format, or HTML SQL Injection security checks. To configure dynamic profiling, you must complete the following steps.
- Configure dynamic learning
- Configure auto deployment grace period
Configure dynamic learning
As a first step, you must configure dynamic learning on your appliance. At the command prompt, type:
set appfw profile <profile_name> dynamicLearning <security_checks>
Example
set appfw profile test1 dynamicLearning SQLInjection CrossSiteScripting fieldFormat startURL
Configure auto deployment grace period
Once you enable the feature on specific security checks, you must configure the grace period for the auto deployment.
set appfw learningsettings <profile name> -crossSiteScriptingAutoDeployGracePeriod <seconds>
set appfw learningsettings <profile name> fieldFormatAutoDeploymentGracePeriod <seconds>
set appfw learningsettings <profile name> SQLInjectionAutoDeploymentGracePeriod <seconds>
set appfw learningsettings <profile name> –startURLAutoDeployGracePeriod <seconds>
Example
set appfw learningsettings test1 –crossSiteScriptingAutoDeployGracePeriod 30
set appfw learningsettings test1 –startURLAutoDeployGracePeriod 7
set appfw learningsettings test1 –fieldFormatAutoDeploymentGracePeriod 10
set appfw learning settings test1 –SQLInjectionAutoDeploymentGracePeriod 12
Note:
Here, the auto deployment grace period is in minutes.
Configuring dynamic profiling by using the NetScaler GUI
- Navigate to Security > NetScaler Web App Firewall > Profile.
- In the details pane, select a profile and click Edit.
- In the Citrix Web App Profile page, click Dynamic Profiling under Advanced Settings.
- In the Dynamic Profiling section, select a security check and click Edit.
-
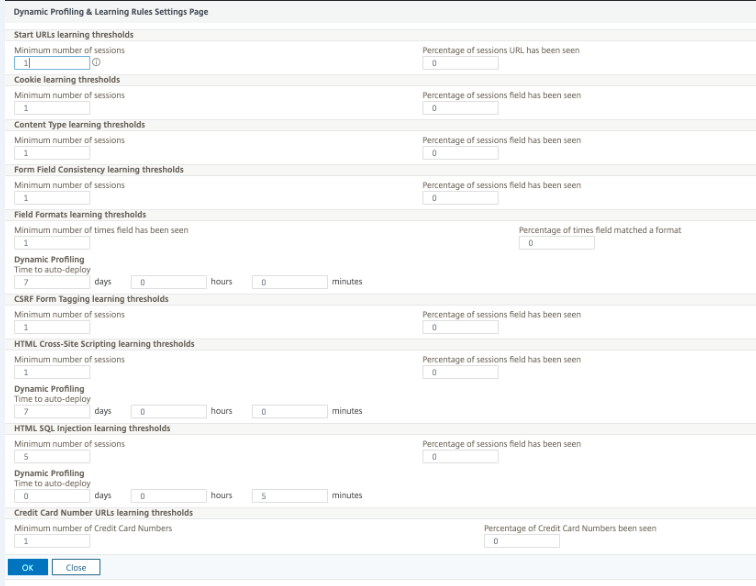
In the Dynamic Profiling and Learning Settings page, set the grace period the security check.
- Click OK and Done.
Export and import of relaxation rules
When you enable dynamic profiling, the learnt data is auto deployed as relaxation rules. Along with this, the appliance also enables you to export the dynamic profiling based relaxation rules and regular relaxation rules. You can export the rules from staging environment and import it to the production environment.
Note:
When you import rules to the production environment, you must ensure the process is additive and does not override the existing configuration.
How to export and import relaxation rules
To export and import the relaxation rules, you must complete the following steps:
- You must first export the dynamic profiling-based data. For this, the export option is available for the relaxation rules in the WAF profile. When you select this option, you export the dynamic profiling relaxation rules and regular relaxation rules. You can use the export option to download the configuration as a compressed bundle on the appliance.
- Once you have exported the data from the staging environment, you must import it to another NetScaler appliance. For this, you must use the import option available in the relaxation rules of the WAF profile. When you select this option, the appliance imports the specified relaxation rules bundled and restores it to the WAF profile of the selected appliance.
Note:
If you are going to import relaxation rules in a WAF profile, there are two types of action: Augment – This action ensures import is additive, thus not overriding any existing configuration. Overwrite – This action overwrites the existing configuration with configuration present in the compressed export bundle.”
Import archived relaxation rules file by using CLI
To import the relaxation rules, you must import the archive into the NetScaler appliance and then run the restore command to extract the configuration. The following set of CLI commands can be used for exporting, importing, and managing the configurations.
To import the archived file from the specific location and restore, at the command prompt, type:
import appfw archive <src> <name> [-comment <string>]
Where,
“src”: Indicates the source of the tar archive file in the form, <protocol>://<host>[:<port>][/<path>]
“name”: Indicates name of archive.
“comment”: Comments associated with this archive.
restore appfw profile <archivename> [-relaxationRules] [-importProfileName <string>] [-matchUrlString <string>] [-replaceUrlString <string>] [-overwrite] [-augment]
Where,
archivename: Indicates source for tar archive. This is a mandatory argument.
“relaxationRules”: Option to import all appfw relaxation rules.
importProfileName: Indicates profile name created or updated to associate the relaxation rules during restore operation.
“matchUrlString”: Indicates action URL string to match in archived relaxation rules.
replaceUrlString: Indicates string to replace in action URL while restoring relaxation rules.
overwrite: Existing rules action to purge existing relaxation rules and replace during import.
augment: Existing rules action to augment relaxation rules during import.
Example:
import appfw archive local: dutA_test_pr.tgz demo
restore appfw profile dutA_test_pr
Export the archived file to the selected appliance by using the CLI
If you use CLI to export the appfw relaxation rules, you must archive the configuration and then export it. To archive and export the archived file, at the command prompt, type:
archive appfw profile <name> <archivename> [-comment <string>]
Where,
archive name: Indicates source for tar archive. This is a mandatory argument.
name: Indicates the appfw profile name containing the relaxation rules to export
export appfw archive <name> <target>
Where, Name. Name of tar archive. This is a mandatory argument. Maximum Length: 31 Target. Path to the file to be exported. This is a mandatory argument. Maximum Length: 2047
Example:
> archive appfw profile test_pr archived_test_pr
> export appfw archive archived_test_pr local:dutA_test_pr
To export relaxation rules by using NetScaler GUI
Follow the steps given below to export relaxation rules:
- Navigate to Security > NetScaler Web App Firewall.
- In the details page, click NetScaler Web App Firewall Profiles link under Configuration Summary section.
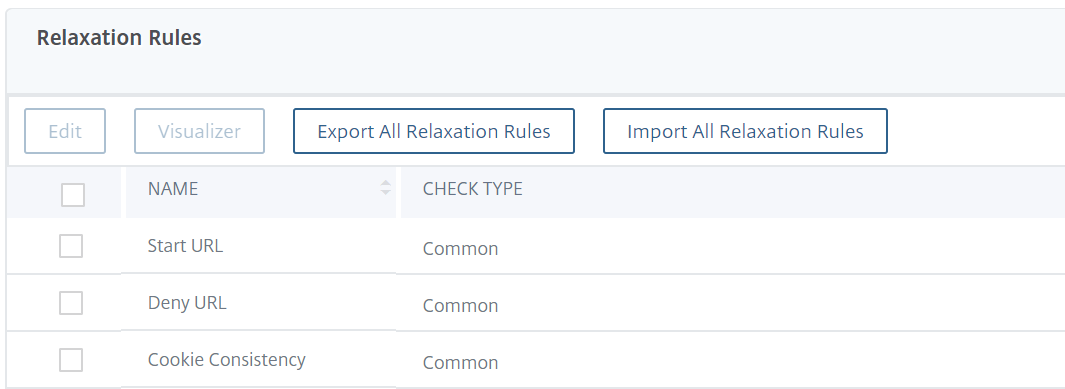
- In the NetScaler Web App Firewall Profile page, click the Relaxation Rules link under Advanced Settings section.
-
In the Relaxation Rules section, click Export All Relaxation Rules. The action applies to all security checks and on the ones which dynamic learning is enabled on that profile.
To import relaxation rules by using NetScaler GUI
Complete the steps to import relaxation rules:
- Navigate to Security > NetScaler Web App Firewall.
- In the details page, click the NetScaler Web App Firewall Profiles link under Configuration Summary section.
- In the NetScaler Web App Firewall Profile page, click the Relaxation Rules link under Advanced Settings section.
- In the Relaxation Rules section, click Import All Relaxation Rules.
- In the Configure NetScaler Web App Firewall Profile page, set the following parameters:
- Local file. Name of the compressed archived file containing the relaxation rules.
- Profile Name. Name of the profile to which the relaxation rules are bound.
- Matching URL String. Portion of the URL that matches.
- Replace URL String. Portion of the URL that replaces the URL string.
- Existing Rule Action. Select if the rule must overwrite existing rules or augment the existing rules.
- Click OK.