Administration
The My Account section is where the end-user can administer the account, the users that can access the account, and the users that can access Fusion purge features.
In addition, from the menu you can view invoices that are due, and manage OAuth API credentials.
Manage Users
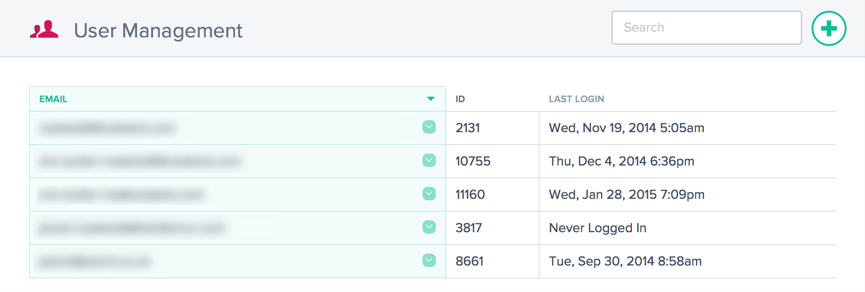
Within the Users menu you can Add/Remove users and reset password access to the account.
In addition to the user management you are able to enter email addresses for Service notifications and see when a user last logged in.
Adding or Removing Users and Resetting Passwords
When creating or adding users, ensure you use a valid email address. Passwords are created automatically and emailed to the email address that is entered as the user name.
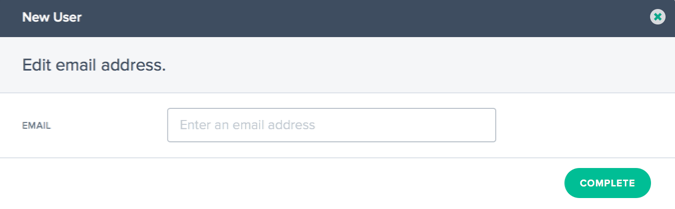
To add a new user, click the + in the upper right corner. Enter a valid email address and click Complete.
To reset the password for a user, click the down arrow to the right of the user’s email address, choose Reset Password, and confirm the action in the dialog by clicking Yes. A password reset email is sent to the user.
A user can be removed from the system by clicking the down arrow to the right of the user’s email address and choosing Delete. Confirm the action and the user will be deleted from the system.
Single Sign On
We support using third party identity providers for Single Sign On login to the Portal via SAML 2.0.
Single Sign On is used for authentication of user logins. We do not currently pass authorization information in via SAML SSO. To be able to log in, a user must exist in the NetScaler Intelligent Traffic Management Portal with the same email address as a user in the SSO identity provider.
Single Sign On is managed per account. Once SSO is turned on for an account, all users must use an SSO login to access the Portal.
You find the SAML configuration information in the SSO Configuration menu item. The information is specific your account and allows you to configure SSO in your identity provider. If you do not find the SSO Configuration menu, please contact the support team.
The setup is different for each identity provider but you need the following information, which is shown in the SSO Configuration page:
- Assertion Consumer Service (ACS) URL
- Entity ID
- Logout URL (optional, depending on provider)
- Start URL (optional, depending on provider)
- Name Format: Email
- Signed Response: No
Turn on Single Sign On
Generic steps for adding SSO to the NetScaler Intelligent Traffic Management Portal:
- Using the data in the SSO Configuration screen, set up the identity provider
- Download the SSO IDP metadata file from the identity provider
- Upload the file to the SSO Configuration page
- When ready to enable SSO, click Enable
- Users will now need to login via the SSO login page.
Turn off Single Sign On
If SSO is configured and enabled, click the Disable button.
Any user in the account that wants to log in will now need to use a Citrix password on the standard login screen. If a user does not know their password, an account administrator can send a password reset email or the user can request a password reset email from the login screen.
Configuration Steps for Google G Suite
The following are the steps necessary to use Single Sign On with Google G Suite logins:
In Google G Suite:
- Open the G Suite administrative console to the Apps section
- Click the SAML apps category
- Click the Enable SSO for a SAML Application button
- At the bottom of the dialog, choose SETUP MY OWN CUSTOM APP
- On the Google IDP Information dialog, download the IDP metadata file under Option 2.
- In Basic Information for your Custom App, the Application Name can be “NetScaler Intelligent Traffic Management”
-
Fill in the following information from the SSO Configuration in Portal:
- ACS URL: from the SSO Configuration info
- Entity ID: from the SSO Configuration info
- Start URL: from the SSO Configuration info (optional)
- Name ID Format: EMAIL
- Leave the Attribute Mapping dialog empty, click FINISH to create the SAML App
- In the Apps list, click the vertical dots on the right of the Portal item and choose ON for everyone
In the Portal:
- From the SSO Configuration page, upload the IDP metadata file; click the Choose File button to open the file browser and select the IDP metadata file downloaded from G Suite.
- If the metadata file validates correctly, a green check mark appears.
- Click Enable to enable SSO for all users in the account.
Users can now log in to the NetScaler Intelligent Traffic Management Portal from the SSO login page or the Apps menu in G Suite.
For more information about Google G Suite SSO, refer to the Google help.
Setting Purge ACLs
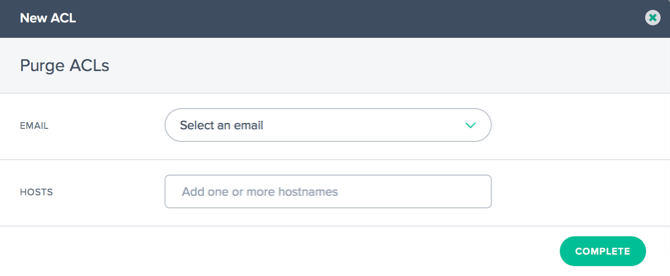
In the Purge ACLs menu, users can have limitations placed on their ability to execute the Fusion Purge functionality. By default, users can run a purge on any host configured in the Fusion Purge settings. The Purge ACLs are used to limit users to only allow a purge on specified hosts.
Add new restrictions for a user by clicking the ’+’ button in the upper right corner. The following dialog appears:
| Field | Description |
|---|---|
| Select the email for the user you would like to configure limited purge access. | |
| Hosts | Enter the host names for the user to run purges. Any host names not included in the list for the user will be unavailable for purge by the user. |
Invoices
The Invoices menu option provides all the Invoices for the NetScaler Intelligent Traffic Management services you have consumed. If there are any problems with the invoices, contact your sales representative or alternatively contact the support team.
API
Manage OAuth
The API menu option provides details on the Authenticated OAuth API Tokens you may want to use. If you want to use this functionality, contact your account manager.
REST API Rate Limits
REST APIs can be used to access data and settings stored in the platform. However, we limit the number of requests (to access this data) by putting a rate limit on them i.e., we limit the number of API calls a customer can make in a given time period. This is done to balance the load on the system.
Rate Limit Attributes
Rate limits have the following attributes:
- Time range (in minutes)
- Number of allowed requests
- Concurrent requests
Customers can request increases to their rate limits for their specific use case.
Default Rate Limits
The following table lists different types of API calls, and default rate limits that apply to each of them.
| API Types | Default Rate Limits |
|---|---|
| Reporting Endpoints | GET |
/v2/reporting/radar.json /v2/reporting/plt.json /v2/reporting/openmix.json /v2/reporting/sonar.json
|
15 requests per 15 minutes. 3 concurrent requests |
| Updating Applications | PUT, POST |
/v2/config/applications/dns.json |
10 requests per minute. 3 concurrent requests |
| Fusion Purge | GET |
/v2/actions/fusion/purge.json |
150 requests per minute |
| Fusion Purge | POST |
/v2/actions/fusion/purge.json |
1 request per minute. 3 concurrent requests |