User administration
Citrix SD-WAN Orchestrator for On-premises supports role-based access control (RBAC). RBAC regulates access to SD-WAN Orchestrator resources based on the roles assigned to individual users. RBAC allows users to access only the data that their role demands and restricts any other data.
A role defines the permissions to view and perform various activities on Citrix SD-WAN Orchestrator for On-premises. You can assign a user with a role from the list of predefined roles.
By default, a user account is created on Citrix SD-WAN Orchestrator for On-premises with user name admin and password set as password. The user is asked to change the default password during initial login.
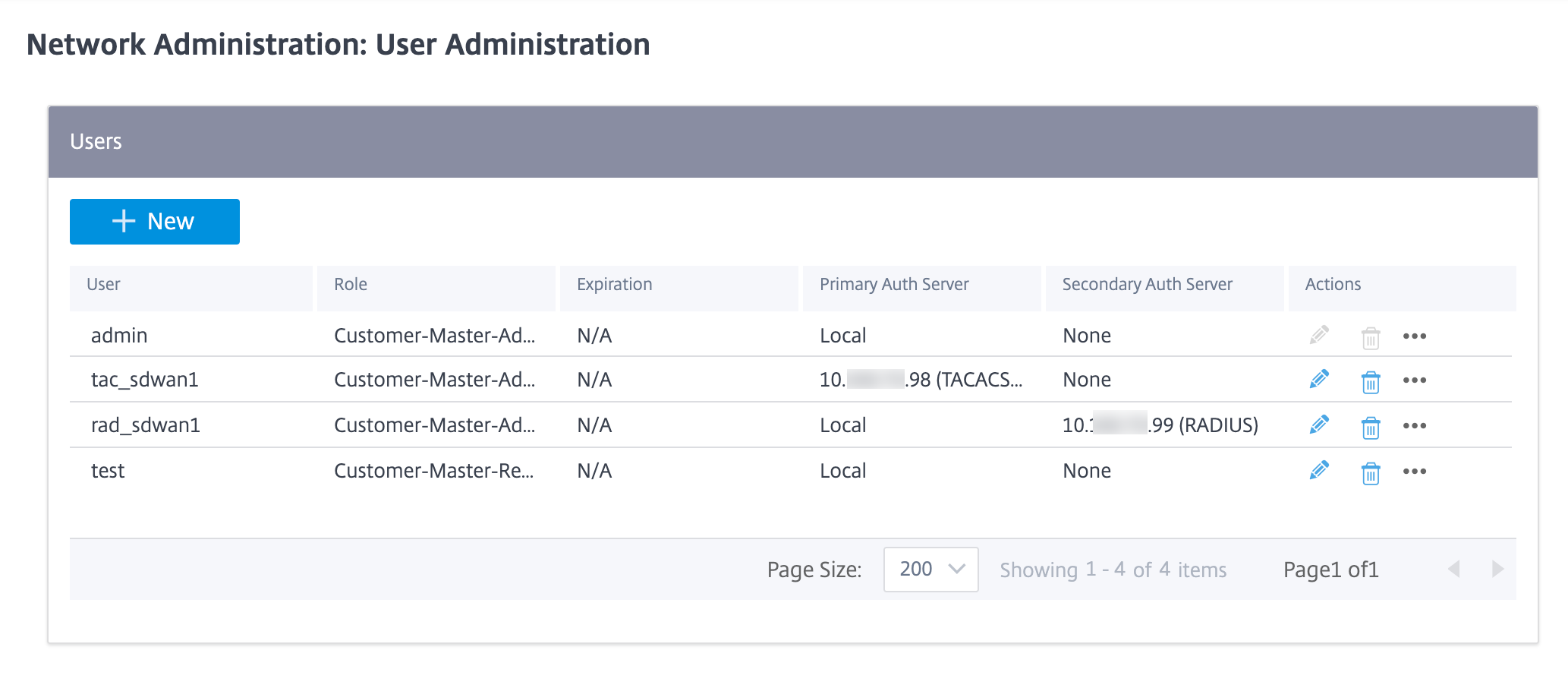
You can add users who can be authenticated locally and remotely. Users who are authenticated remotely are authenticated through RADIUS or TACACS+ authentication servers.
Provider roles
The following table lists the predefined provider roles.
| Provider role | Description |
|---|---|
| Provider-Master-Admin-All | An administrator who can manage the provider and all of its customer information |
| Provider-Master-Admin-Tenant | An administrator who can manage the provider and a subset of its customer information |
| Provider-Master-ReadOnly-All | An administrator who can only view provider and customer information |
| Provider-Network-Admin (Preview) | An administrator who can only view and edit the network related information |
| Provider-Security-Admin (Preview) | An administrator who can only view and edit the security related information |
The Provider-Master-Admin-All role can perform the following:
- Assign roles to users in Provider and Customer network
- Manage access to customers for all other admin roles
- Edit or delete assigned roles
Customer roles
The following table lists the predefined customer roles:
| Role | Description |
|---|---|
| Customer-Master-Admin | A customer administrator who can view and edit customer information |
| Customer-Master-ReadOnly-Admin | A customer administrator who can only view customer information |
| Customer-Network-Admin (Preview) | A customer administrator who can only view and edit network related information |
| Customer-Security-Admin (Preview) | A customer administrator who can only view and edit security related information |
A user with Customer-Master-Admin role can perform the following:
- Add users and assign customer roles
- Edit or delete assigned roles
Support roles
For troubleshooting purposes, Customers can assign support roles and provide Support Team members the ability to view and edit their information. Support roles have a validity period that is defined while assigning the role. After the validity period expires, the support user loses access to Customer information. However, the support user details continue to appear under the Administration > User Administration. Based on the need, the Customer administrator can either delete or extend the validity of the support role.
| Role | Description |
|---|---|
| Customer-Support-ReadWrite | A support team member who can view and edit the customer information |
| Customer-Support-ReadOnly | A support team member who can only view the customer information |
Authentication types
Citrix SD-WAN Orchestrator for On-premises supports the following types of authentication:
- Single-factor authentication: Single-factor authentication presents one authentication method to gain access to Citrix SD-WAN Orchestrator for On-premises for users.
- Two-factor authentication (TFA): Two-factor authentication presents two authentication methods to gain access to Citrix SD-WAN Orchestrator for On-premises for users. It introduces an extra layer of security in the login sequence.
The following authentication methods are supported for single-factor and two-factor authentication:
- Local: When selected, the user must use the password configured on Citrix SD-WAN Orchestrator for On-premises to gain access.
- RADIUS: When selected, the user must use the RADIUS server password to gain access.
- TACACS+: When selected, the users must use the TACACS+ server password to gain access.
The following table lists the primary and secondary authentication methods supported for users who are authenticated locally:
| Primary Authentication Type | Secondary Authentication Type | ||
|---|---|---|---|
| Single-factor authentication | Local | - | |
| Two-factor authentication | Local | RADIUS or TACACS+ | |
The following table lists the primary and secondary authentication methods supported for users who are authenticated remotely:
| Primary Authentication Type | Secondary Authentication Type | ||
|---|---|---|---|
| Single-factor authentication | Local, RADIUS, or TACACS+ | - | |
| Two-factor authentication | Local, RADIUS, or TACACS+ | RADIUS or TACACS+ | |
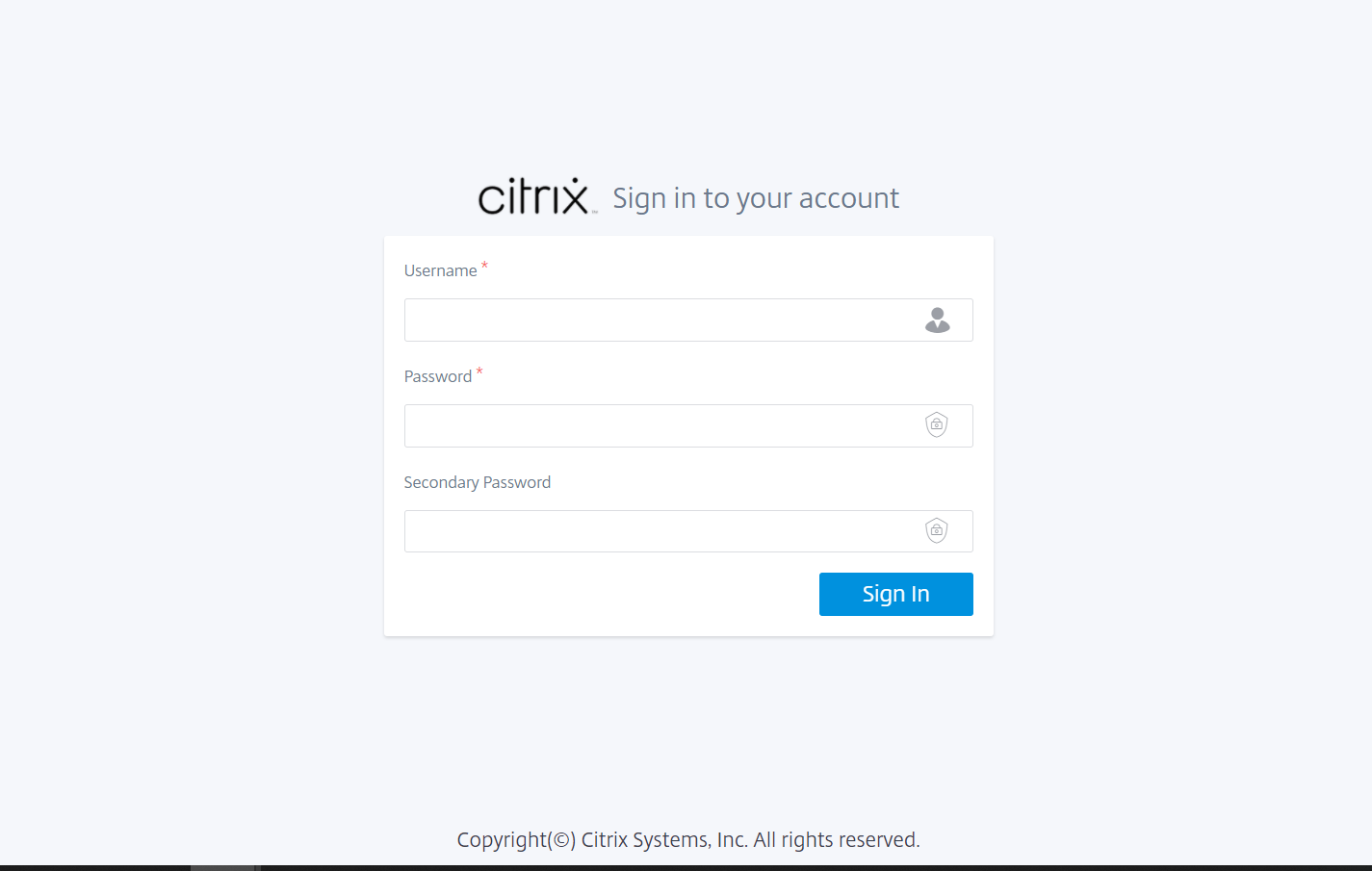
If Two-factor authentication is enabled and the RADIUS/TACACS+ servers are configured as a secondary authentication type, then the Secondary password field is visible at the login page.
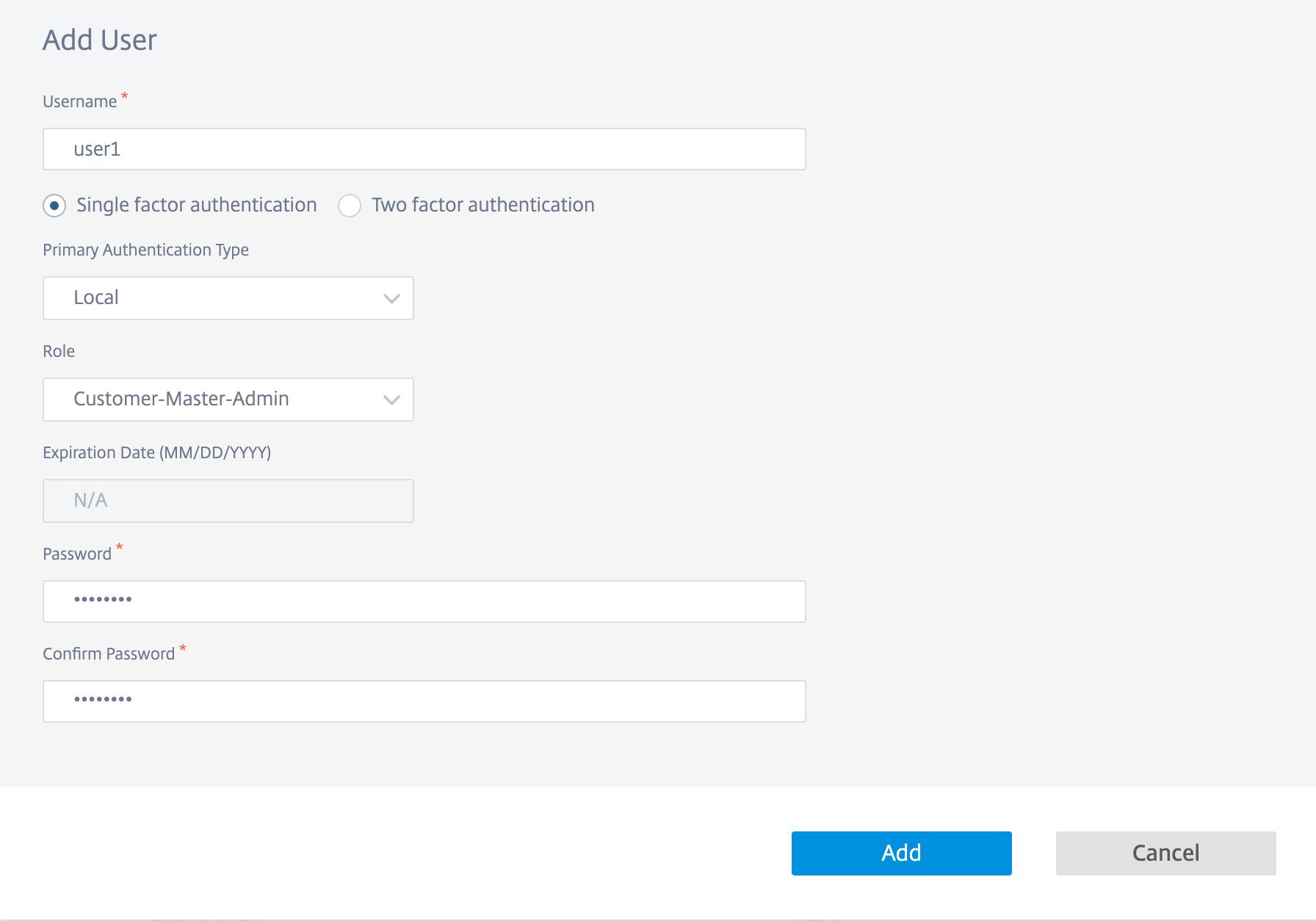
Add a user
Navigate to Administration > User Administration > click + New > Enter the following details > click Add.
- Enter the user name.
- Single factor authentication: Enables only the primary authentication for logging in the users.
- Two factor authentication: Enables both primary and secondary authentication for logging in the users. For more information, see Remote Authentication Servers.
- Primary Authentication Type: Select Local or the IP address of the remote authentication server.
-
Secondary Authentication Type: Select the IP address of the remote authentication server.
NOTE
The Secondary Authentication Type field is grayed out if Single factor authentication is chosen.
- Role: Select a role from the list of the available roles.
- Deny access to Customers: (Available only at the provider level). While adding users, providers can deny access to specific customers.
- Expiration Date (MM/DD/YYYY): The date up to which the support user has access to customer information. The default validity period is for two weeks from the date the role is assigned.
- Enter your password. The length of the password must be between 8–128 characters.
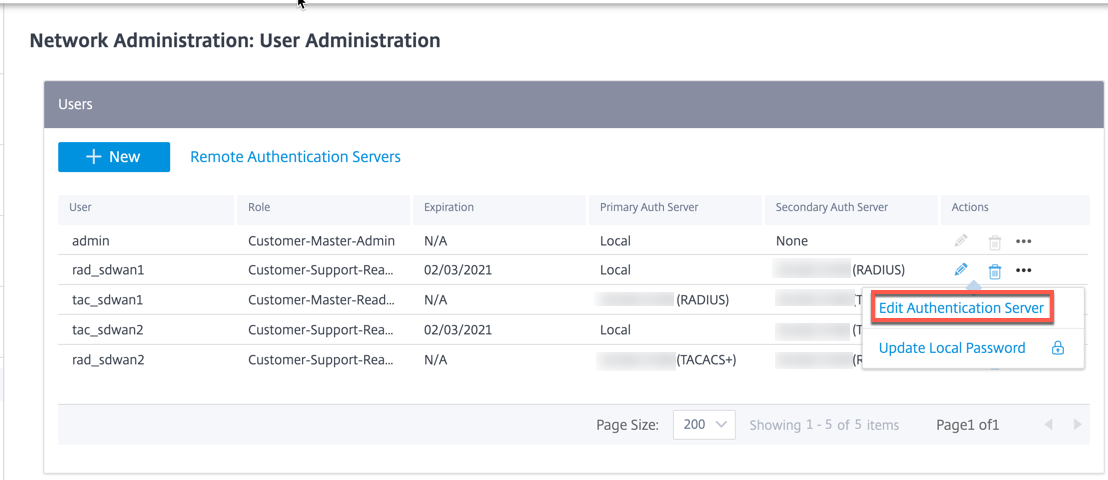
Using the Actions column, you can change the user role, update the password, and edit the authentication type. You can also delete the user if necessary.
Limitation
Citrix SD-WAN Orchestrator for On-premises does not support duplication of user names for a different customer under the same provider. When this action is performed, you see the error message Error while account creation.
Change authentication type
You can change the authentication type of a user from single-factor authentication to two-factor authentication and conversely.
To change the authentication type of a user, in the Actions column, click … and then Edit Authentication Server.
If you have currently selected Single factor authentication, you can switch to two-factor authentication. Click Two factor authentication and select the remote server from Secondary Authentication Type drop-down list. Click Apply.
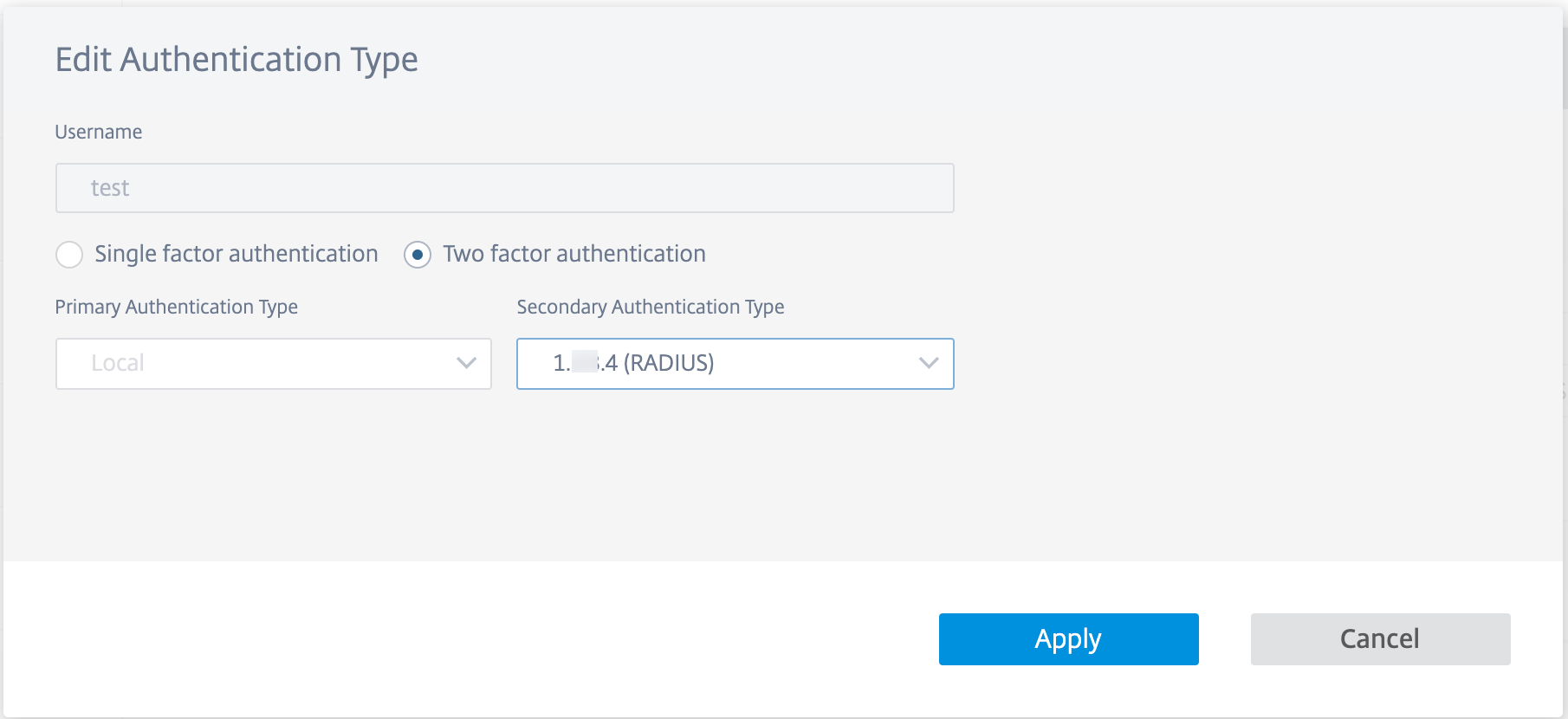
If you have currently selected two factor authentication, you can choose to change only the secondary authentication type or switch to single factor authentication.
To switch to single factor authentication, click Single factor authentication. The Secondary Authentication Type drop-down list gets disabled and only the Primary Authentication type drop-down list is enabled.
Primary Authentication Type can only be set at the time of user creation and it cannot be edited later.
Change password
You can change the password of local users. To change the password of a user, in the Actions column, click … and Update Local Password.
NOTE
You can modify the password only for local users. For users authenticated remotely, you must update the password on the external server.
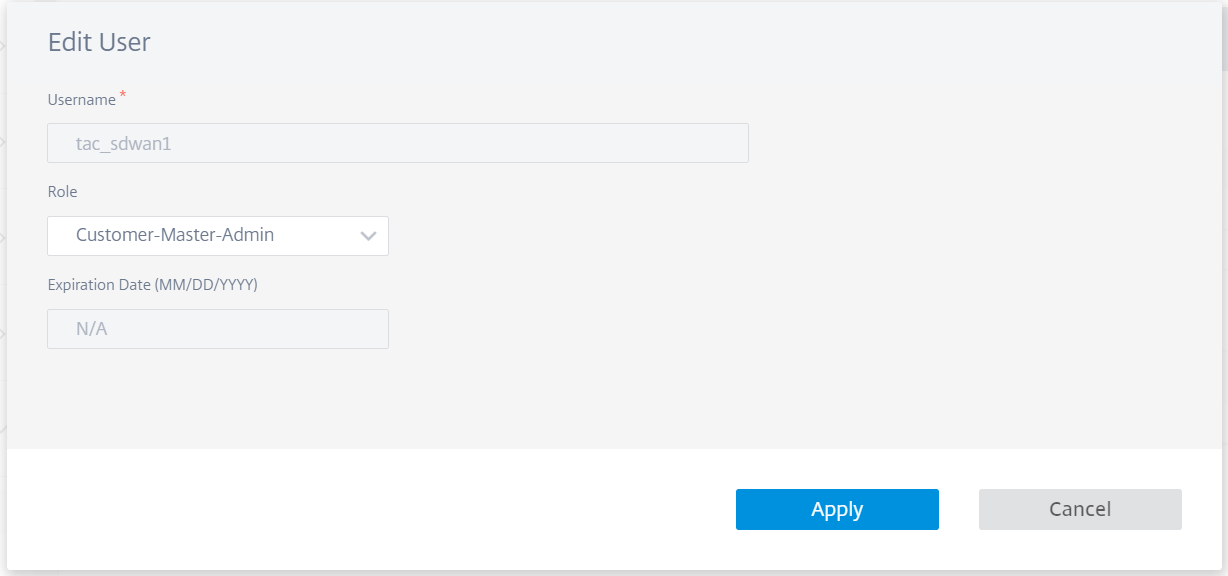
Change user role
To change the user role, click the Edit icon in the Actions column. Select a Role and click Apply.
NOTE
You cannot edit the role of the default admin user.