-
Configuration guide for Citrix Virtual Apps and Desktops workloads
-
Citrix SD-WAN Orchestrator on-premises configuration on Citrix SD-WAN appliance
-
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Zones
You can configure zones in the network and define policies to control how traffic enters and leaves zones. By default, the following zones are created:
- Internet_Zone
- Applies to traffic to or from an Internet service using a Trusted interface.
-
Untrusted_Internet_Zone
- Applies to traffic to or from an Internet service using an Untrusted interface.
-
Default_LAN_Zone
- Applies to traffic to or from an object with a configurable zone, where the zone has not been set.
You can create your own zones and assign them to the following types of objects:
-
Virtual Network Interfaces (VNI)
-
Intranet Services
-
GRE Tunnels
-
LAN IPsec Tunnels
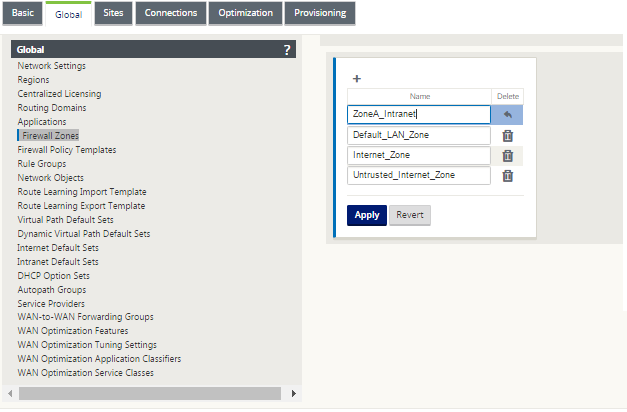
The following illustration displays the three zones pre-configured. Additionally, you can create your own zones as required. In this example, the zone “ZoneA_Intranet” is a user created zone. It is assigned to the Virtual Interface of the bypass segment (ports 1 and 2) of the SD-WAN appliance.
The source zone of a packet is determined by the service or virtual network interface a packet is received on. The exception to this is virtual path traffic. When traffic enters a virtual path, packets are marked with the zone that originated the traffic and that source zone is carried through the virtual path. This allows the receiving end of the virtual path to make a policy decision based on the original source zone before it entered the virtual path.
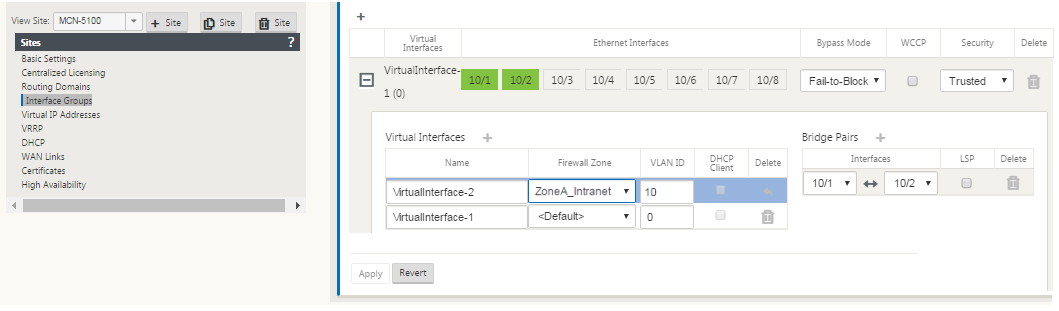
For example, a network administrator may want to define polices so that only traffic from VLAN 30 at Site A is allowed to enter VLAN 10 at Site B. The administrator can assign a zone for each VLAN and create policies that permit traffic between these zones and blocks traffic from other zones. The screenshot below shows how a user would assign the “ZoneA_Intranet” zone to VLAN 10. In this example, the “ZoneA_Intranet” zone was previously defined by the user in order to assign it to Virtual Interface “VirtualInterface-2”.
The destination zone of a packet is determined based on the destination route match. When a SD-WAN appliance looks up the destination subnet in the route table, the packet will match a route, which has a zone assigned to it.
-
Source zone
-
Non-Virtual Path: Determined through the Virtual Network Interface packet was received on.
-
Virtual Path: Determined through source zone field in packet flow header.
-
Virtual network interface - the packet was received on at source site.
-
-
Destination zone
- Determined through destination route lookup of packet.
Routes shared with remote sites in the SD-WAN maintain information about the destination zone, including routes learned through dynamic routing protocol (BGP, OSPF). Using this mechanism, zones gain global significance in SD-WAN network and allow end-to-end filtering within the network. The use of zones provides a network administrator an efficient way to segment network traffic based on customer, business unit, or department.
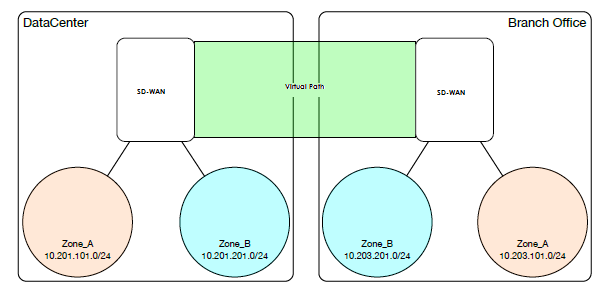
The capability of SD-WAN firewall allows the user to filter traffic between services within a single zone, or to create policies that can be applied between services in different zones, as shown in figure below. In the example below, we have Zone_A and Zone_B, each of which has a LAN Virtual network interface.
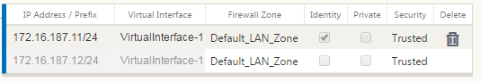
Screenshot below displays the inheritance of zone for a Virtual IP (VIP) from its assigned Virtual Network Interface (VNI).
Share
Share
In this article
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.