Secure user sessions using TLS
As of Version 7.16, the Linux VDA supports TLS encryption for secure user sessions. TLS encryption is disabled by default.
Enable TLS encryption
To enable TLS encryption for secure user sessions, obtain certificates and enable TLS encryption on both the Linux VDA and the Delivery Controller™ (the Controller).
Obtain certificates
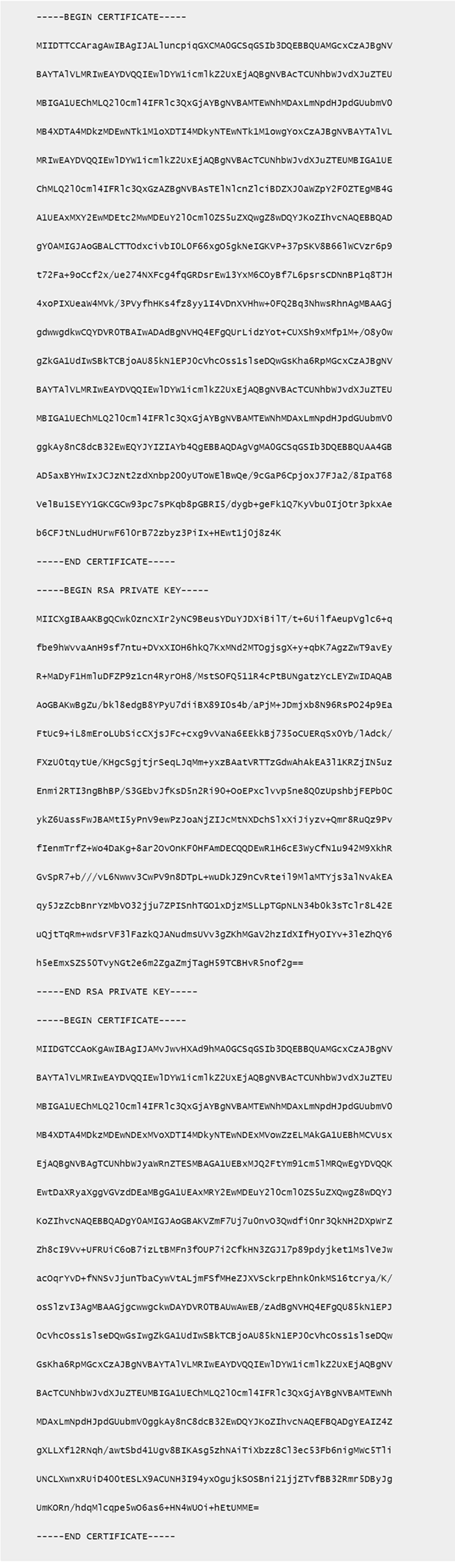
Obtain server certificates in PEM format and root certificates in CRT format from a trusted Certificate Authority (CA). A server certificate contains the following sections:
- Certificate
- Unencrypted private key
- Intermediate certificates (optional)
An example of a server certificate:
Enable TLS encryption
Enable TLS encryption on the Linux VDA
On the Linux VDA, use the enable_vdassl.sh tool to enable (or disable) TLS encryption. The tool is located in the /opt/Citrix/VDA/sbin directory. For information about the options available in the tool, run the /opt/Citrix/VDA/sbin/enable_vdassl.sh -help command.
Tip: A server certificate must be installed on each Linux VDA server and root certificates must be installed on each Linux VDA server and client.
Enable TLS encryption on the Controller
Note:
You can enable TLS encryption only for entire delivery groups. You cannot enable TLS encryption for specific applications.
In a PowerShell window on the Controller, run the following commands in sequence to enable TLS encryption for the target delivery group.
Add-PSSnapin citrix.*Get-BrokerAccessPolicyRule –DesktopGroupName 'GROUPNAME' | Set-BrokerAccessPolicyRule –HdxSslEnabled $true
Note:
To ensure that only VDA FQDNs are contained in an ICA® session file, you can also run the Set-BrokerSite –DnsResolutionEnabled $true command. The command enables DNS resolution. If you disable DNS resolution, an ICA session file discloses VDA IP addresses and provides FQDNs only for the TLS-related items such as SSLProxyHost and UDPDTLSPort.
To disable TLS encryption on the Controller, run the following commands in sequence:
Add-PSSnapin citrix.*Get-BrokerAccessPolicyRule –DesktopGroupName 'GROUPNAME' | Set-BrokerAccessPolicyRule –HdxSslEnabled $falseSet-BrokerSite –DnsResolutionEnabled $false
Troubleshooting
The following “Can’t assign requested address” error might occur in Citrix Workspace™ app for Windows when you try to access a published desktop session:
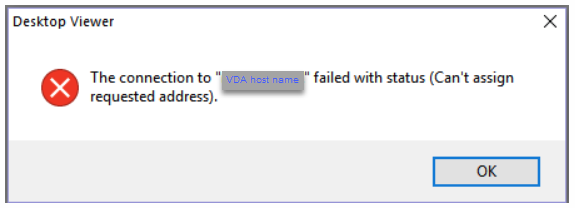
As a workaround, add an entry to the hosts file, which is similar to:
<IP address of the Linux VDA> <FQDN of the Linux VDA>
On Windows machines, the hosts file typically locates at C:\Windows\System32\drivers\etc\hosts.