This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Querying Windows Event Log
A question we get asked quite often is whether uberAgent is able to query Windows Event Log for specific events IDs. This functionality is not in the product, as Splunk, uberAgent’s primary backend, has this built-in. Hence we generally recommend making use of Splunk’s capabilities.
However, not all of our customers have Universal Forwarder, Splunk’s client software, deployed to their endpoints, mostly for performance reasons. If that is the case for you, too, then this practice guide should be of interest. If you do have Splunk’s Universal Forwarder deployed, please use its functionality instead. UF is more efficient than the script-based solution presented in this article.
The scripts listed in this guide are managed in vast limits’ public GitHub repository.
Collect Event IDs With a Custom Script
As Windows Event Log data is not part of uberAgent’s default data set, we are using the agent’s custom script functionality.
In a nutshell, the uberAgent custom scripts feature executes any script you like and sends the output to Splunk. This works with any scripting engine, of course. In this case, we are using PowerShell.
The following script queries Event Log for a given event ID in a specific event log (Application, System, etc.). It also needs an interval in which it should search. Due to the parameters, you can use that script to query arbitrary events and don’t need a new script for each. The required parameters are passed to the script through an uberAgent timer.
PARAM
(
[Parameter(Mandatory = $true)]
[System.Int32]$EventID,
[Parameter(Mandatory = $true)]
[System.String]$EventLog,
[Parameter(Mandatory = $true)]
[System.Int32]$IntervalMS
)
$IntervalMS = -$IntervalMS
$StartTime=$(get-date).AddMilliseconds($IntervalMS)
$Filter= @{
LogName="$EventLog"
StartTime=$StartTime
Id=$EventID
}
$Events = Get-WinEvent -FilterHashtable $Filter -ErrorAction SilentlyContinue
if (@($Events).Count -gt 0)
{
foreach ($Event in $Events)
{
[Hashtable]$Output = @{
'ProviderName' = "`"$($Event.ProviderName)`""
'Id' = $Event.id
'LevelDisplayName' = $Event.LevelDisplayName
'LogName' = $Event.LogName
'Message' = "`"$($Event.Message)`""
'TimeCreated' = "`"$($Event.TimeCreated)`""
'TaskDisplayName' = "`"$($Event.TaskDisplayName)`""
}
Write-Output $($Output.keys.foreach({"$_=$($Output.$_)"}) -join ' ')
}
}
<!--NeedCopy-->
Save the script somewhere. For this example, we save the script as C:\Program Files\vast limits\uberAgent\Scripts\Get-WinEvent.ps1.
Configure uberAgent® to Run the Script
Create a new timer in uberAgent’s configuration. With the settings shown below, the script will be executed every five minutes.
[Timer]
Name = Get-WinEvent
Interval = 300000
Script = powershell.exe -executionpolicy bypass -file "C:\Program Files\vast limits\uberAgent\Scripts\Get-WinEvent.ps1" -EventID 1000 -EventLog "Application" -IntervalMS 300000
ScriptContext = Session0AsSystem
<!--NeedCopy-->
Note that you define the parameters in the Script setting. The parameter IntervalMS should be the same number of milliseconds as the setting Interval.
Splunk it
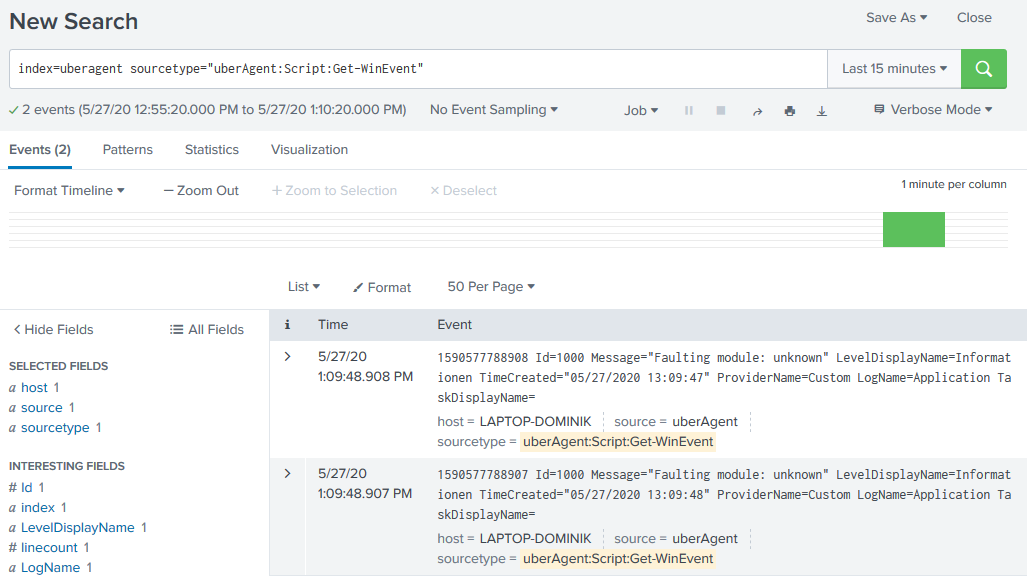
Once the data is in Splunk it can be used to search for Windows Events.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.