Certificates for Workload Balancing
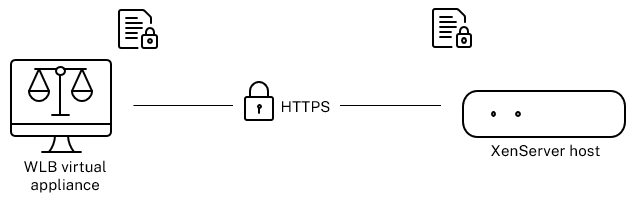
XenServer and Workload Balancing communicate over HTTPS. During Workload Balancing Configuration, the wizard automatically creates a self-signed test certificate. This self-signed test certificate lets Workload Balancing establish a TLS connection to XenServer. By default, Workload Balancing creates this TLS connection with XenServer automatically. You do not need to perform any certificate configurations during or after configuration for Workload Balancing to create this TLS connection.
Note:
The self-signed certificate is a placeholder to facilitate HTTPS communication and is not from a trusted certificate authority. For added security, we recommend using a certificate signed from a trusted certificate authority.
To use a certificate from another certificate authority, such as a signed one from a commercial authority, you must configure Workload Balancing and XenServer to use it.
By default, XenServer does not validate the identity of the certificate before it establishes connection to Workload Balancing. To configure XenServer to check for a specific certificate, export the root certificate that was used to sign the certificate. Copy the certificate to XenServer and configure XenServer to check for it when a connection to Workload Balancing is made. XenServer acts as the client in this scenario and Workload Balancing acts as the server.
Depending on your security goals, you can either:
Note:
Certificate verification is a security measure designed to prevent unwanted connections. Workload Balancing certificates must meet strict requirements or the certificate verification doesn’t succeed. When certificate verification fails, XenServer doesn’t allow the connection.
For certificate verification to succeed, you must store the certificates in the specific locations in which XenServer expects to find the certificates.
Configure XenServer to verify the self-signed certificate
You can configure XenServer to verify that the XenServer Workload Balancing self-signed certificate is authentic before XenServer permits Workload Balancing to connect.
Important:
To verify the XenServer Workload Balancing self-signed certificate, you must connect to Workload Balancing using its host name. To find the Workload Balancing host name, run the
hostnamecommand on the virtual appliance.
To configure XenServer to verify the self-signed certificate, complete the following steps:
-
Copy the self-signed certificate from the Workload Balancing virtual appliance to the pool coordinator. The XenServer Workload Balancing self-signed certificate is stored at
/etc/ssl/certs/server.pem. Run the following command on the pool coordinator:scp root@<wlb-ip>:/etc/ssl/certs/server.pem . <!--NeedCopy--> -
If you receive a message stating that the authenticity of
wlb-ipcannot be established, typeyesto continue. -
Enter Workload Balancing virtual appliance root password when prompted. The certificate is copied to the current directory.
-
Install the certificate. Run the following command in the directory where you copied the certificate:
xe pool-certificate-install filename=server.pem <!--NeedCopy--> -
Verify the certificate was installed correctly by running the following command on the pool coordinator:
xe pool-certificate-list <!--NeedCopy-->If you installed the certificate correctly, the output of this command includes the exported root certificate. Running this command lists all installed TLS certificates, including the certificate you installed.
-
To synchronize the certificate from the coordinator to all hosts in the pool, running the following command on the pool coordinator:
xe pool-certificate-sync <!--NeedCopy-->Running the
pool-certificate-synccommand on the coordinator synchronizes the certificate and certificate revocation lists on all the pool hosts with the coordinator. This action ensures all hosts in the pool use the same certificates.There is no output from this command. However, the next step does not work if this one did not work successfully.
-
Instruct XenServer to verify the certificate before connecting to the Workload Balancing virtual appliance. Run the following command on the pool coordinator:
xe pool-param-set wlb-verify-cert=true uuid=uuid_of_pool <!--NeedCopy-->Tip:
Pressing the Tab key automatically populates the UUID of the pool.
-
(Optional) To verify this procedure worked successfully, perform the following steps:
-
To test if the certificate synchronized to the other hosts in the pool, run the
pool-certificate-listcommand on those hosts. -
To test if XenServer was set to verify the certificate, run the
pool-param-getcommand with theparam-name=wlb-verify-cert parameter. For example:xe pool-param-get param-name=wlb-verify-cert uuid=uuid_of_pool <!--NeedCopy-->
-
Configure XenServer to verify a certificate-authority certificate
You can configure XenServer to verify a certificate signed by a trusted certificate authority.
For trusted authority certificates, XenServer requires an exported certificate or certificate chain (the intermediate and root certificates) in .pem format that contains the public key.
If you want Workload Balancing to use a trusted authority certificate, do the following tasks:
Before beginning these tasks, ensure:
-
You know the IP address for the XenServer pool coordinator.
-
XenServer can resolve the Workload Balancing host name. (For example, you can try pinging the Workload Balancing FQDN from the XenServer console for the pool coordinator.)
Obtain a signed certificate from the certificate authority
To obtain a certificate from a certificate authority, you must generate a Certificate Signing Request (CSR). On the Workload Balancing virtual appliance, create a private key and use that private key to generate the CSR.
Guidelines for specifying the Common Name
The Common Name (CN) you specify when creating a CSR must exactly match the FQDN of your Workload Balancing virtual appliance. It must also match the FQDN or IP address you specified in the Address box in the Connect to WLB Server dialog box.
To ensure the name matches, specify the Common Name using one of these guidelines:
-
Specify the same information for the certificate’s Common Name as you specified in the Connect to WLB Server dialog.
For example, if your Workload Balancing virtual appliance is named
wlb-vpx.yourdomain, specifywlb-vpx.yourdomainin the Connect to WLB Server dialog and providewlb-vpx.yourdomainas the Common Name when creating the CSR. -
If you connected your pool to Workload Balancing by IP address, use the FQDN as the Common Name and the IP address as a Subject Alternative Name (SAN). However, this approach might not work in all situations.
Create a private key file
On the Workload Balancing virtual appliance, complete the following steps:
-
Create a private key file:
openssl genrsa -des3 -out privatekey.pem 2048 <!--NeedCopy--> -
Remove the password:
openssl rsa -in privatekey.pem -out privatekey.nop.pem <!--NeedCopy-->
Note:
If you enter the password incorrectly or inconsistently, you might receive some messages indicating that there is a user interface error. You can ignore the message and rerun the command to create the private key file.
Generate the Certificate Signing Request
On the Workload Balancing virtual appliance, complete the following steps:
-
Create the Certificate Signing Request (CSR) using the private key:
openssl req -new -key privatekey.nop.pem -out csr <!--NeedCopy--> -
Follow the prompts to provide the information necessary to generate the CSR:
Country Name. Enter the TLS Certificate country codes for your country. For example, CA for Canada or JM for Jamaica. You can find a list of TLS Certificate country codes on the web.
State or Province Name (full name). Enter the state or province where the pool is located. For example, Massachusetts or Alberta.
Locality Name. The name of the city where the pool is located.
Organization Name. The name of your company or organization.
Organizational Unit Name. Enter the department name. This field is optional.
Common Name. Enter the FQDN of your Workload Balancing server. This value must match the name the pool uses to connect to Workload Balancing. For more information, see Guidelines for specifying the Common Name.
Email Address. This email address is included in the certificate when you generate it.
-
Provide optional attributes or click Enter to skip providing this information.
The CSR request is saved in the current directory and is named
csr. -
Display the CSR in the console window by running the following commands in the Workload Balancing appliance console:
cat csr <!--NeedCopy--> -
Copy the entire CSR and use it to request the certificate from the certificate authority.
Specify and apply the new certificate
Use this procedure to specify Workload Balancing use a certificate from a certificate authority. This procedure installs the root and (if available) intermediate certificates.
To specify a new certificate, complete the following steps:
-
Download the signed certificate, root certificate and, if the certificate authority has one, the intermediate certificate from the certificate authority.
-
If you didn’t download the certificates directly to the Workload Balancing virtual appliance, copy them across by using one of the following methods:
-
From a Windows computer, use WinSCP or another copying utility.
For the host name, you can enter the IP address and leave the port at the default. The user name and password are typically root and whatever password you set during configuration.
-
From a Linux computer to the Workload Balancing appliance, use SCP or another copying utility. For example:
scp root_ca.pem root@wlb-ip:/path_on_your_WLB <!--NeedCopy-->
-
-
On the Workload Balancing virtual appliance, merge the contents of all the certificates (root certificate, intermediate certificate - if it exists, and signed certificate) into one file. You can use the following command:
cat signed_cert.pem intermediate_ca.pem root_ca.pem > server.pem <!--NeedCopy--> -
Rename the existing certificate and key by using the move command:
mv /etc/ssl/certs/server.pem /etc/ssl/certs/server.pem_orig mv /etc/ssl/certs/server.key /etc/ssl/certs/server.key_orig <!--NeedCopy--> -
Copy the merged certificate:
mv server.pem /etc/ssl/certs/server.pem <!--NeedCopy--> -
Copy the private key created previously:
mv privatekey.nop.pem /etc/ssl/certs/server.key <!--NeedCopy--> -
Make the private key readable only by root. Use the
chmodcommand to fix permissions.chmod 600 /etc/ssl/certs/server.key <!--NeedCopy--> -
Restart
stunnel:killall stunnel stunnel <!--NeedCopy-->
Import the certificate chain into the pool
After you obtain the certificates, import them onto the XenServer pool coordinator. Synchronize the hosts in the pool to use those certificates. Then you can configure XenServer to check the certificate identity and validity each time Workload Balancing connects to a host.
-
Copy the signed certificate, root certificate and, if the certificate authority has one, the intermediate certificate from the certificate authority onto the XenServer pool coordinator.
-
Install the root certificate on the pool coordinator:
xe pool-install-ca-certificate filename=root_ca.pem <!--NeedCopy--> -
If applicable, install the intermediate certificate on the pool coordinator:
xe pool-install-ca-certificate filename=intermediate_ca.pem <!--NeedCopy--> -
Verify both the certificates installed correctly by running this command on the pool coordinator:
xe pool-certificate-list <!--NeedCopy-->Running this command lists all installed TLS certificates. If the certificates installed successfully, they appear in this list.
-
Synchronize the certificate on the pool coordinator to all hosts in the pool:
xe pool-certificate-sync <!--NeedCopy-->Running the
pool-certificate-synccommand on the coordinator synchronizes the certificates and certificate revocation lists on all the pool hosts with the pool coordinator. This action ensures all hosts in the pool use the same certificates. -
Instruct XenServer to verify a certificate before connecting to the Workload Balancing virtual appliance. Run the following command on the pool coordinator:
xe pool-param-set wlb-verify-cert=true uuid=uuid_of_pool <!--NeedCopy-->Tip:
Pressing the Tab key automatically populates the UUID of the pool.
-
If you specified an IP address in the Connect to WLB dialog before you enabled certificate verification, you might be prompted to reconnect the pool to Workload Balancing.
Specify the FQDN for the Workload Balancing appliance in Address in the Connect to WLB dialog exactly as it appears in the certificate’s Common Name. Enter the FQDN to ensure that the Common Name matches the name that XenServer uses to connect.
Troubleshooting
-
If the pool cannot connect to Workload Balancing after configuring certificate verification, check to see if the pool can connect if you turn certificate verification off. You can use the command
xe pool-param-set wlb-verify-cert=false uuid=uuid_of_poolto disable certificate verification. If it can connect with verification off, the issue is in your certificate configuration. If it cannot connect, the issue is in either your Workload Balancing credentials or your network connection. -
Some commercial certificate authorities provide tools to verify the certificate installed correctly. Consider running these tools if these procedures fail to help isolate the issue. If these tools require specifying a TLS port, specify port 8012 or whatever port you set during Workload Balancing Configuration.
-
If the WLB tab shows a connection error, there might be a conflict between the certificate Common Name and the name of the Workload Balancing virtual appliance. The Workload Balancing virtual appliance name and the Common Name of the certificate must match exactly.
For more information, see Troubleshooting.