Profiles and Templates
A profile is a live configuration template. A regular template aids the creation of a new entity. But once the template is created, subsequent changes in the template do not apply to the existing entities created using the base template. A profile serves as the live central master entity. The all child entities inherit from the profile, not only during creation but also throughout the life of a profile. All the child entities associated with the profile, automatically inherit any changes made in a profile.
For example, an admin creates a site configuration profile called the small retail store and applies it to all the small retail stores owned by a company. Now, any changes made to the small retail store profile at any given time would be applied automatically to all the stores inheriting this profile. Based on what’s common across all the entities, and what’s not, certain parameters in the profile configuration can be left unset. Such parameters would be customizable and can vary across the entities inheriting the same profile.
Site profiles
Site profiles help you to easily and quickly configure sites. You can create a site profile once and reuse it multiple times while creating sites.
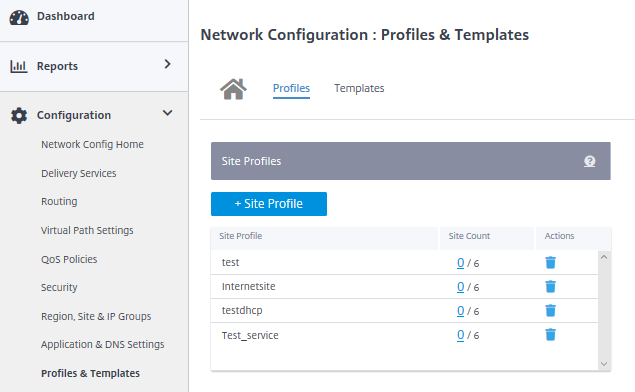
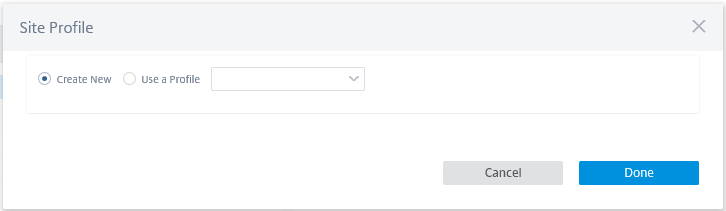
To create a site profile, click + Site Profile. You can create a profile from scratch or edit an existing site profile and save it as a new profile.
To create a site profile, you need to configure the Site Details, Interfaces, and WAN Links. For detailed description of configuring sites, see Site details.
Provide the device details.
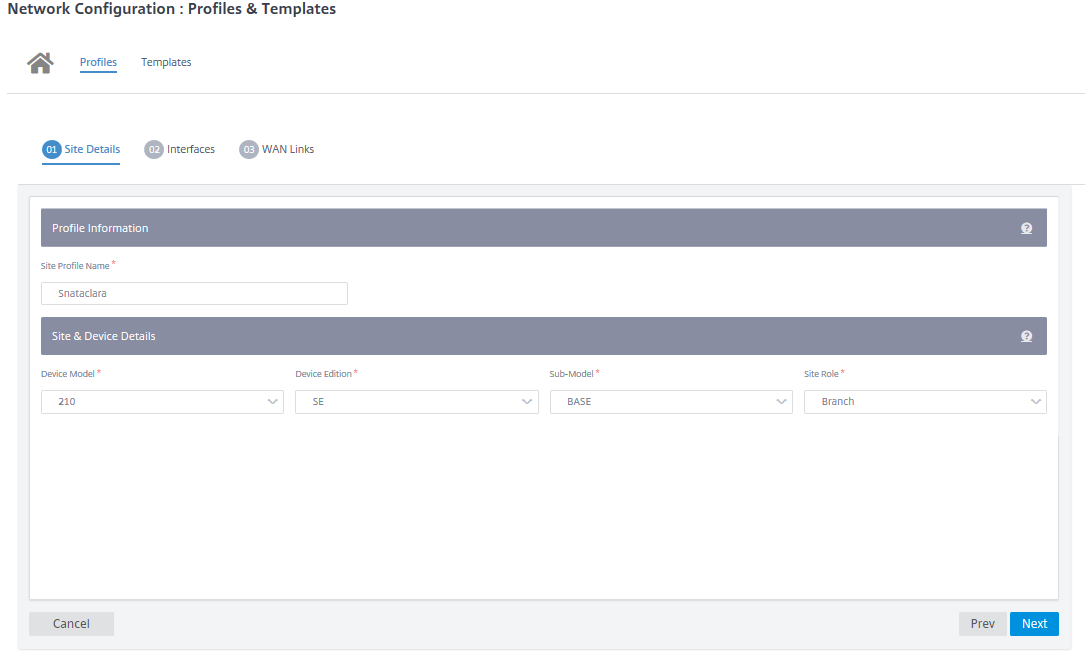
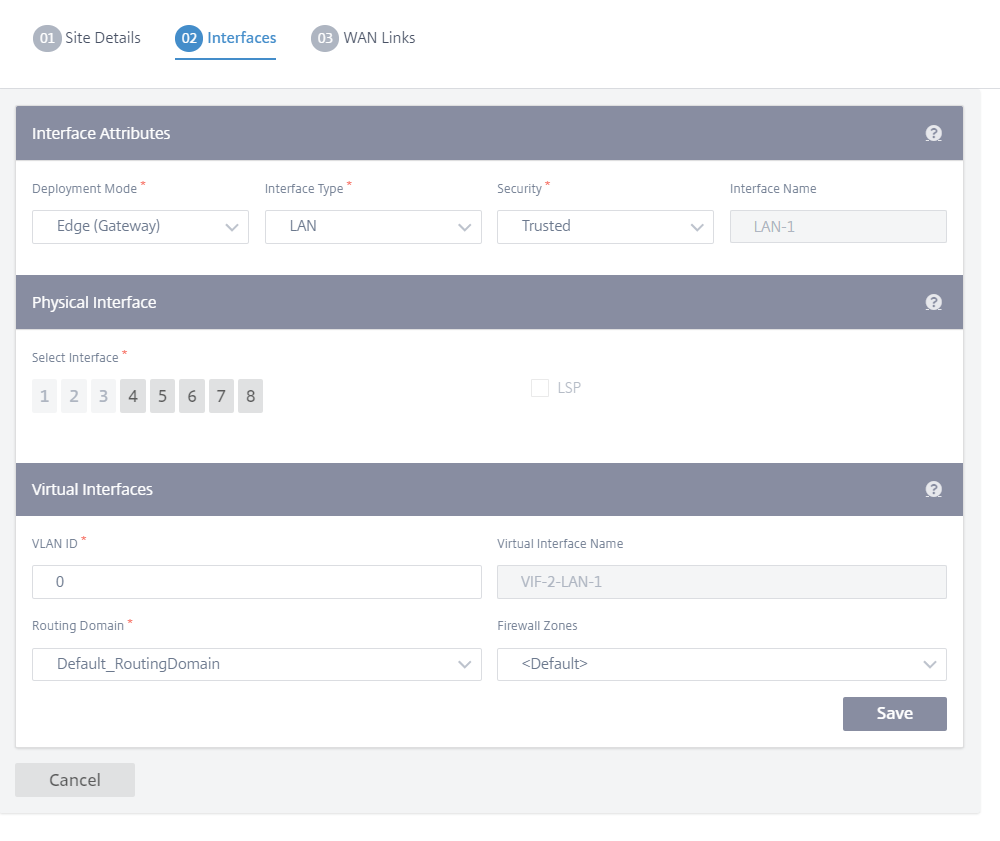
Assign an interface for the site by clicking the + Interface option. To add an interface, you need to fill the Interface Attributes, Physical Interface, and Virtual Interfaces fields. For detailed description of configuring interfaces, see Interfaces.
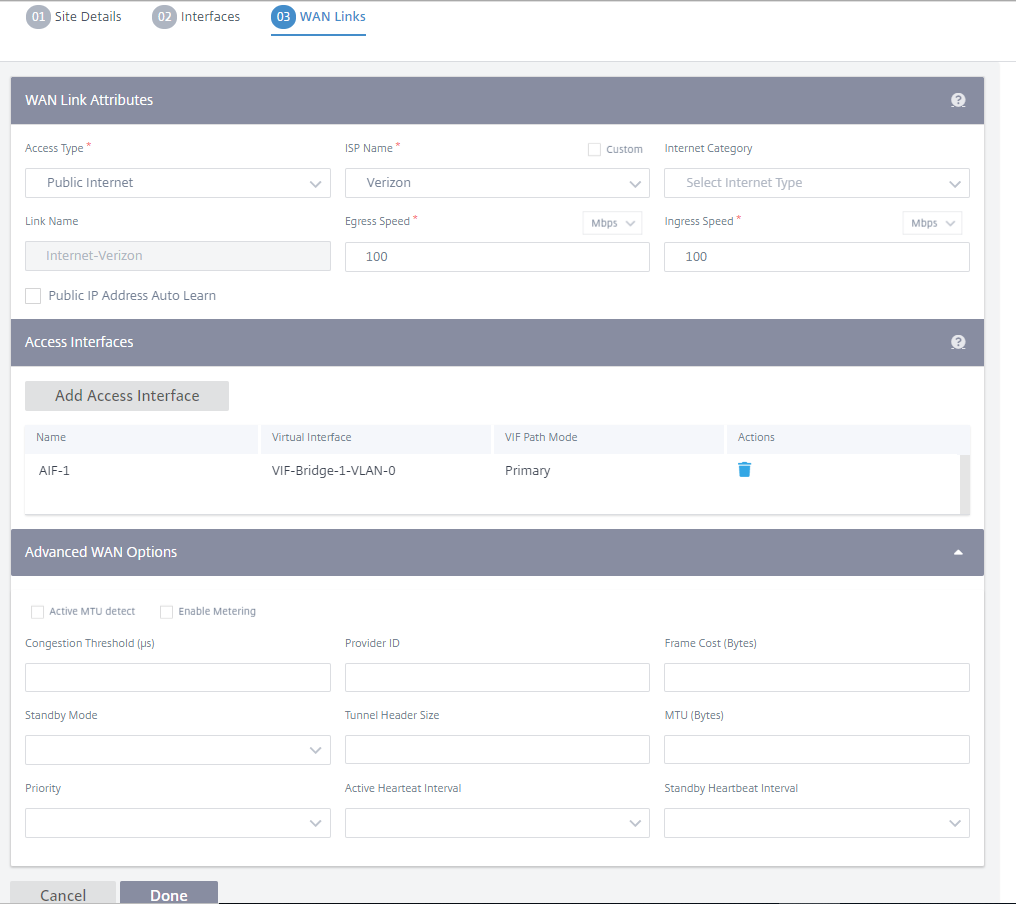
Fill WAN Link Attributes, Access Interfaces, and Services with Advanced Options.
For detailed description of configuring WAN links, see WAN links.
Templates
Citrix SD-WAN Orchestrator service allows you to use templates as a predefined set of fields to configure a new site or a WAN link.
Site template
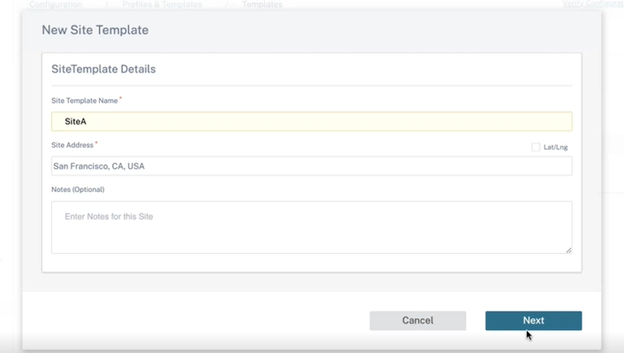
A site template is a predefined template used for site creation. To configure a site using a predefined site template, at the customer level, navigate to Configuration > Profiles & Templates > Templates. In the Site Template section, click Add Site Template.
On the New Site Template screen that is displayed, provide the details as required and click Next.
Note
When you clone a site or create a site using a site template and the source has Wi-Fi configured, the Wi-Fi settings do not get copied to the new site.
WAN link template
WAN link templates help you to configure WAN links easily and quickly. You can create a WAN link template once and reuse it multiple times while configuring WAN links. You can even copy the modified WAN link template configurations to the site WAN link configurations created using the WAN link template.
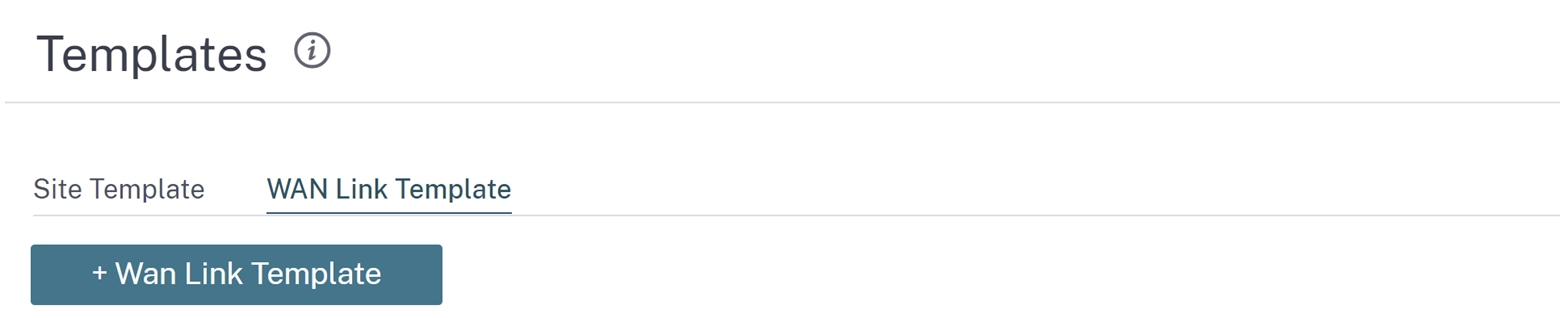
To create a WAN link template, click + WAN Link Template. You can create a template from scratch or edit an existing WAN link template and save it as a new template.
Provide the WAN link information such as Profile Name, Access Type, Internet Category, LAN to WAN Rate (Mbps) and so on to create a WAN profile. For detailed description of configuring WAN links, see WAN links.
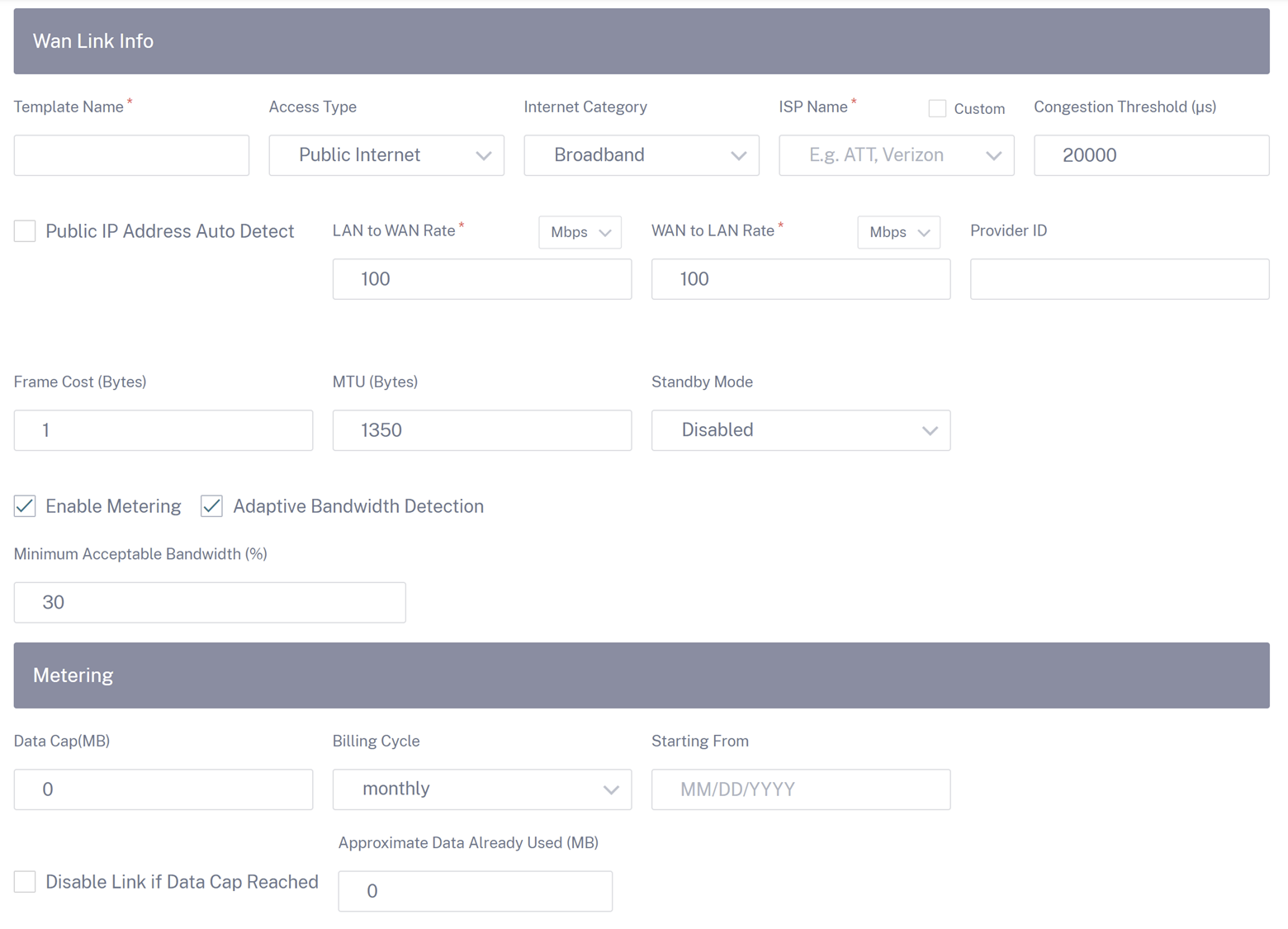
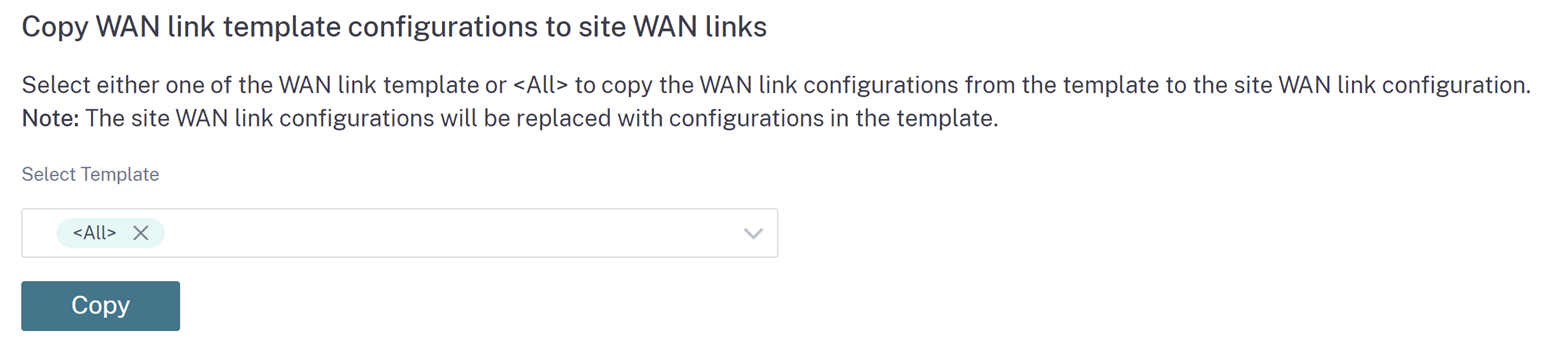
Previously, the option to copy the modified WAN link template configurations to site WAN link configurations was not available. For example, if a user had already created multiple site WAN links using a WAN link template and had to modify a particular configuration (For example, congestion threshold setting), the user had to do it on every site WAN link individually. From now on, the user can update the WAN link template with the new congestion threshold setting and copy the latest WAN link template configurations to all the site WAN links created using the WAN link template.
When you select one or more WAN link templates and click copy, the updates that you make on the WAN link template get copied to the site WAN link configuration created using the selected templates.
Note
The WAN link site configurations that are created using the Site profile feature do not get updated.