-
-
Office 365 optimization
-
-
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Office 365 optimization
The Office 365 Optimization features adhere to the Microsoft Office 365 Network Connectivity Principles, to optimize Office 365. Office 365 is provided as a service through several service endpoints (front doors) located globally. To achieve optimal user experience for Office 365 traffic, Microsoft recommends redirecting Office365 traffic directly to the Internet from branch environments and avoiding practices such as backhauling to a central proxy. This is because Office 365 traffic such as Outlook, Word, and so on are sensitive to latency and backhauling traffic introduces additional latency resulting in poor user experience. Citrix SD-WAN allows you to configure policies to break out Office 365 traffic to the Internet.
The Office 365 traffic is directed to the nearest Office 365 service endpoint, which exists at the edges of Microsoft Office 365 infrastructure worldwide. Once traffic reaches a front door, it goes over Microsoft’s network and reaches the actual destination. This minimizes latency as the round trip time from the customer network to the Office 365 endpoint reduces.
Office 365 endpoints
Office 365 endpoints are a set of network addresses and subnets. Endpoints are segregated into the following three categories:
-
Optimize - These endpoints provide connectivity to every Office 365 service and feature, and are sensitive to availability, performance, and latency. It represents over 75% of Office 365 bandwidth, connections, and volume of data. All the Optimize endpoints are hosted in Microsoft data centers. Service requests to these endpoints must breakout from the branch to the Internet and must not go through the data center.
-
Allow - These endpoints provide connectivity to specific Office 365 services and features only, and are not so sensitive to network performance and latency. The representation of Office 365 bandwidth and connection count is also significantly lower. These endpoints are hosted in Microsoft data centers. Service requests to these endpoints might breakout from the branch to the Internet or might go through the data center.
-
Default - These endpoints provide Office 365 services that do not require any optimization, and can be treated as normal Internet traffic. Some of these endpoints might not be hosted in Microsoft data centers. The traffic in this category is not susceptible to variations in latency. Therefore, direct breaking out of this type of traffic does not cause any performance improvement when compared to Internet breakout. In addition, the traffic in this category might not always be Office 365 traffic, hence it is recommended to disable this option when enabling Office 365 breakout in your network.
How Office 365 optimization works
The Microsoft endpoint signatures are updated at most once a day. Agent on the appliance polls the Citrix service (sdwan-app-routing.citrixnetworkapi.net), every day to obtain the latest set of end-point signatures. The SD-WAN appliance polls the Citrix service (sdwan-app-routing.citrixnetworkapi.net), once every day, when the appliance is turned on and Office 365 optimization is enabled. If there are new signatures available, the appliance downloads it and stores it in the database. The signatures are essentially a list of URLs and IPs used to detect Office 365 traffic based on which traffic steering policies can be configured.
Note
First packet detection and classification of Office 365 traffic is performed only if the Office 365 breakout feature is enabled.
When a request for Office 365 application arrives, the application classifier, does a first packet classifier database lookup, identifies, and marks Office 365 traffic. Once the Office 365 traffic is classified, the auto created application route and firewall policies take effect and breaks out the traffic directly to the Internet. The Office 365 DNS requests are forwarded to specific DNS services like Quad9. For more information, see Domain name system.
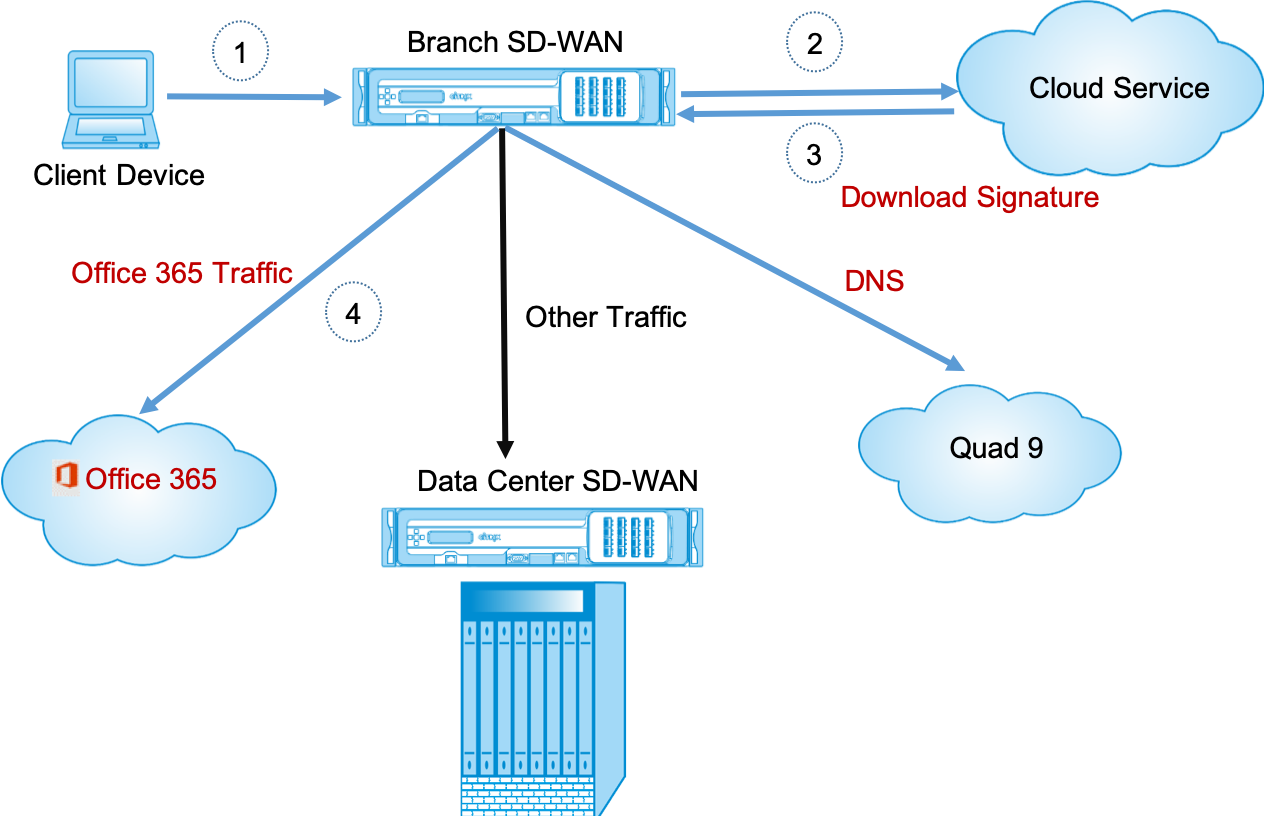
The signatures are downloaded from Cloud Service (sdwan-app-routing.citrixnetworkapi.net).
Configure Office 365 breakout
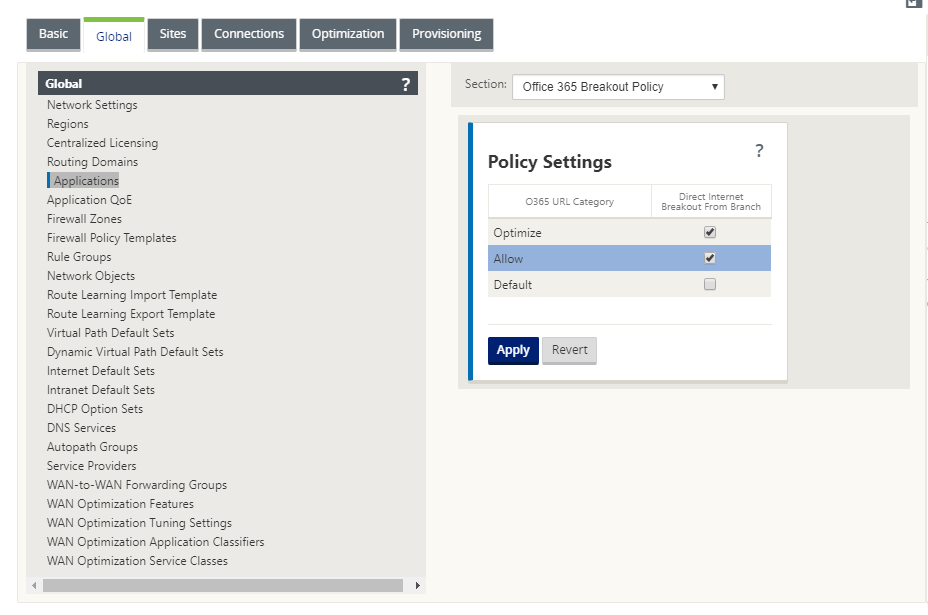
The Office 365 breakout policy allows you to specify which category of Office 365 traffic you can directly break out from the branch. On enabling Office 365 breakout and compiling the configuration, a DNS object, application object, application route, and a firewall policy template is auto-created and applied to branch sites with Internet service.
Prerequisites
Ensure that you have the following:
-
To perform Office 365 breakout, an internet service has to be configured on the appliance. For more information on configuring internet service, see Internet access.
-
Ensure that the Management interface has internet connectivity.
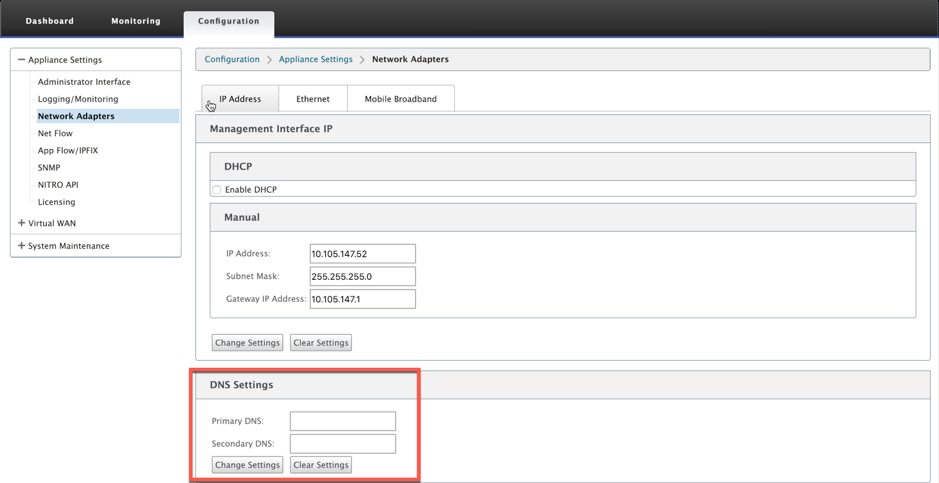
You can use the Citrix SD-WAN web interface to configure the management interface settings.
-
Ensure that the management DNS is configured. To configure management interface DNS navigate to Configuration > Appliance Settings > Network Adapter. Under the DNS Settings section, provide the primary and secondary DNS server detail and click Change Settings.
The Office 365 Breakout Policy setting is available under global settings, select the required Office 365 category for internet breakout and click Apply.
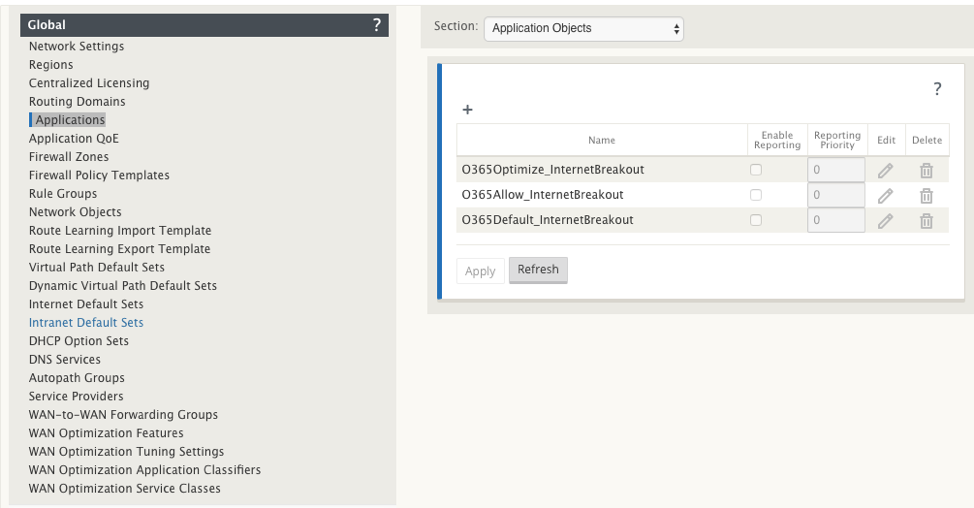
After you configure the Office 365 break out policy settings and compile the configuration. The following settings are auto populated.
-
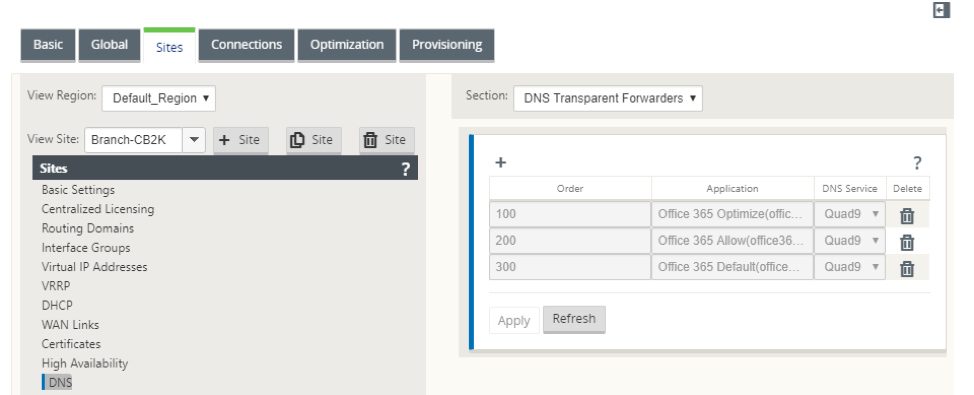
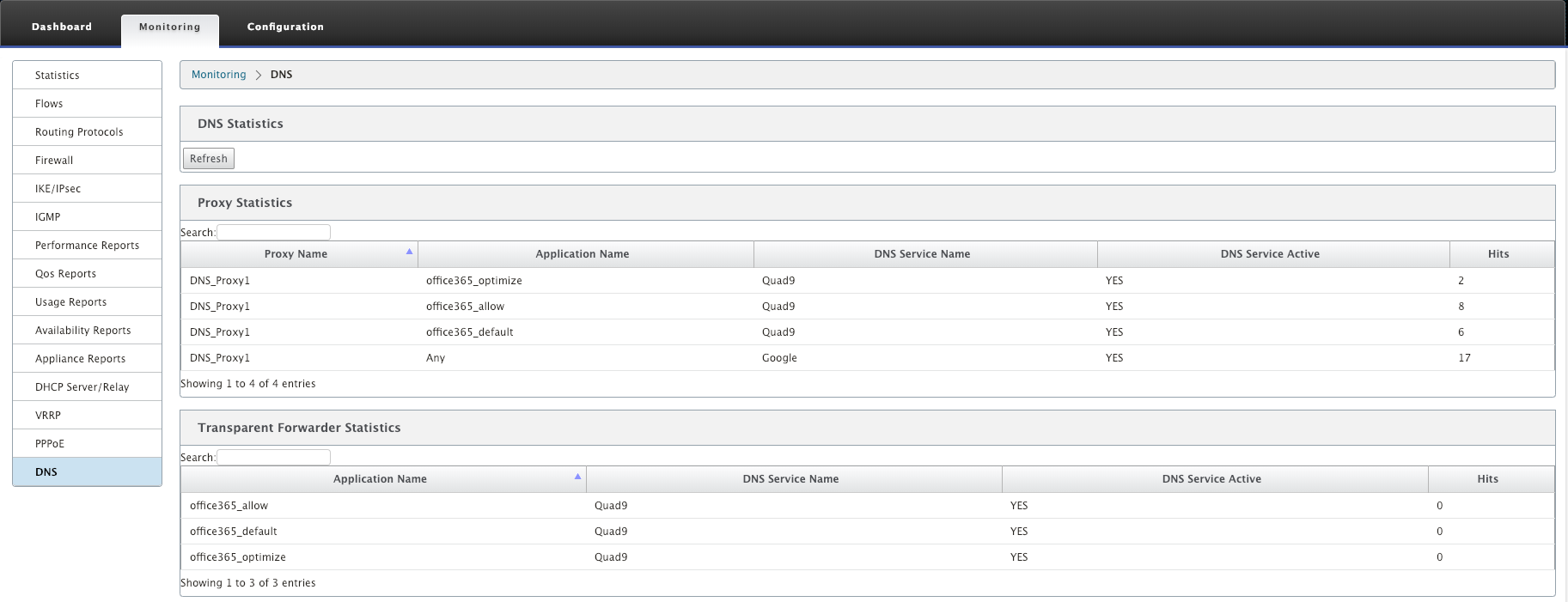
DNS object - The DNS object specifies which type of traffic to be forwarded to the DNS service that the user is configured. The DNS requests are heard on all trusted interfaces, and DNS forwarders are included to direct Office 365 DNS requests to Quad9 service. This forwarder rule takes the highest priority. For more information, see Domain Name Service section.
-
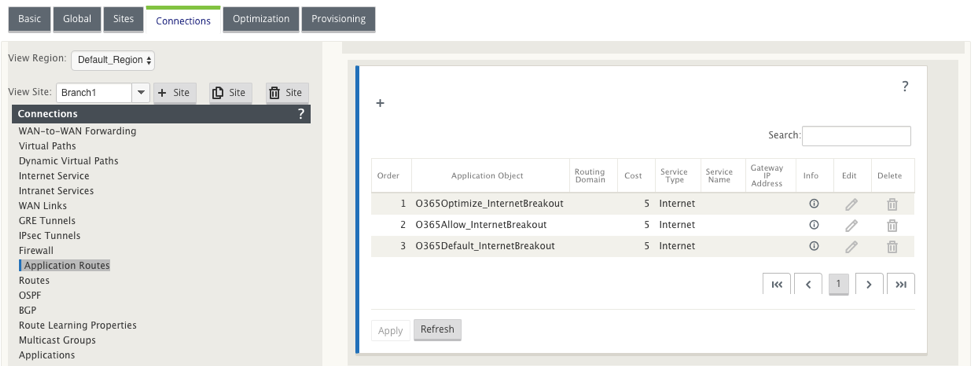
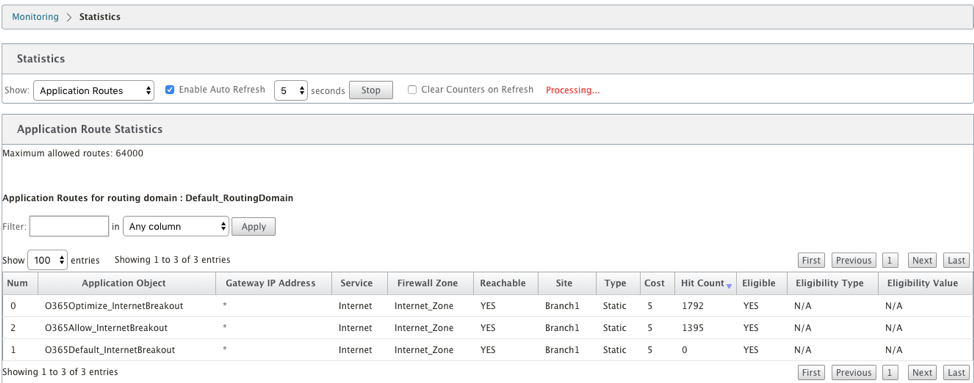
Application object - An application object with the Office 365 category selected by user is created. If you have selected optimize, allow and default categories, the application objects O365Optimize_InternetBreakout, O365Allow_InternetBreakout and O365Default_InternetBreakout are created.
-
Application route: An application route is created for each of the Office 365 application objects with an Internet Service type.
-
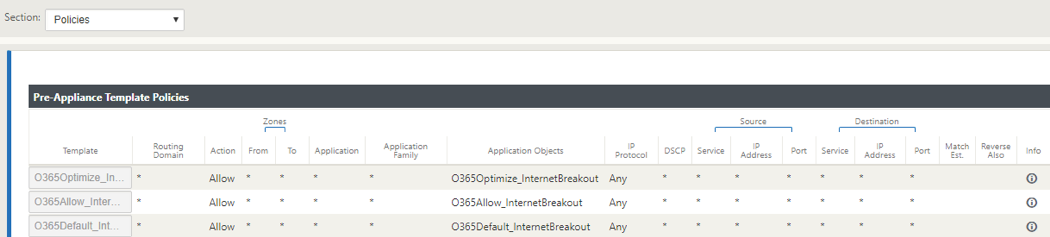
Firewall pre-appliance policy template: A global pre-appliance policy template is created for each configured Office 365 category. This template is applied to all branch sites that have Internet service. The pre-appliance policy takes priority over local and post appliance policy templates.
Transparent forwarder for Office 365
The branch breaks out for Office 365 begins with a DNS request. The DNS request going through Office 365 domains have to be steered locally. If Office 365 Internet break out is enabled, the internal DNS routes are determined and the transparent forwarders list is auto populated. Office 365 DNS requests are forwarded to open source DNS service Quad 9 by default. Quad 9 DNS service is secure, scalable, and has multi pop presence. You can change the DNS service if necessary.
Transparent forwarders for Office 365 applications are created at every branch that has Internet service and office 365 breakout enabled.
If you are using another DNS proxy or if SD-WAN is configured as the DNS proxy, the forwarder list is auto populated with forwarders for Office 365 applications.
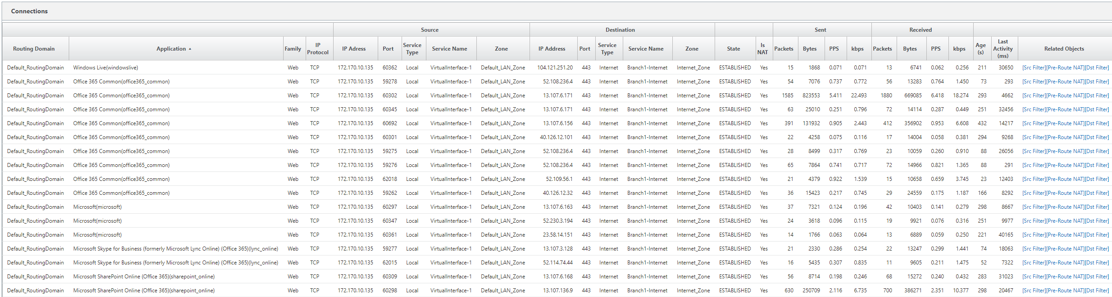
Monitoring
You can monitor the office 365 application statistics in the following SD-WAN statistic reports:
-
Firewall Statistics
-
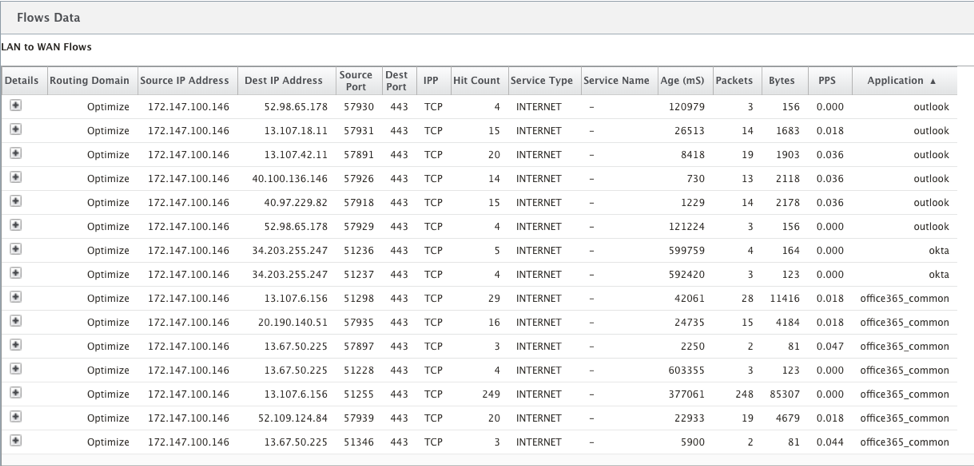
Flows
-
DNS Statistics
-
Application Route Statistics
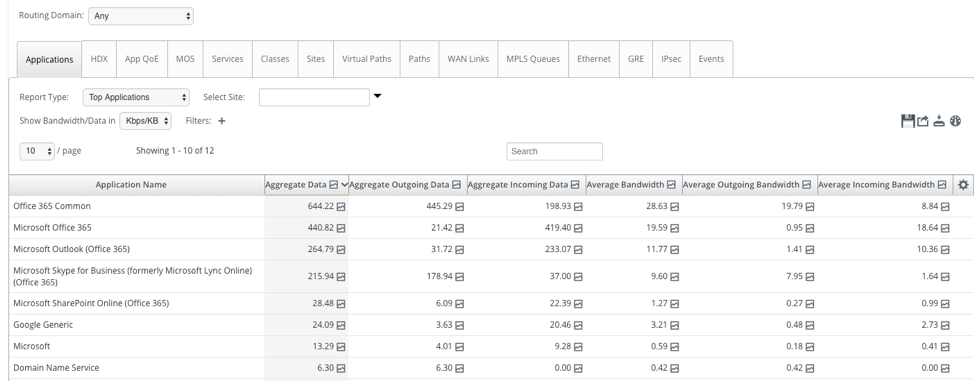
You can also view Office 365 application statistics in the SD-WAN Center Application report.
Troubleshooting
You can view the service error in the Events section of the SD-WAN appliance.
To check the errors, navigate to Configuration > System Maintenance > Diagnostics, click Events tab.
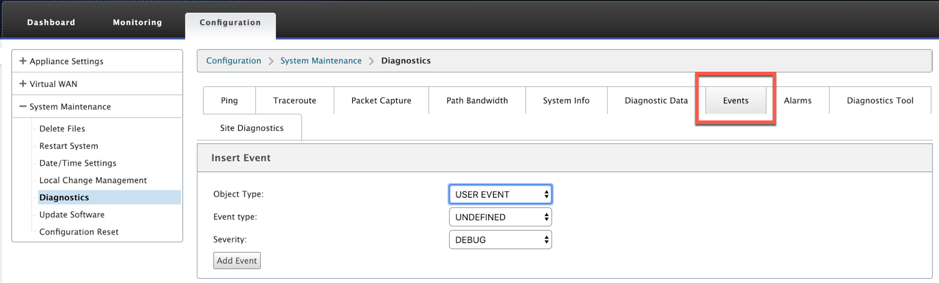
If there is an issue in connecting to the Citrix service (sdwan-app-routing.citrixnetworkapi.net), then the error message reflects under the View Events table.
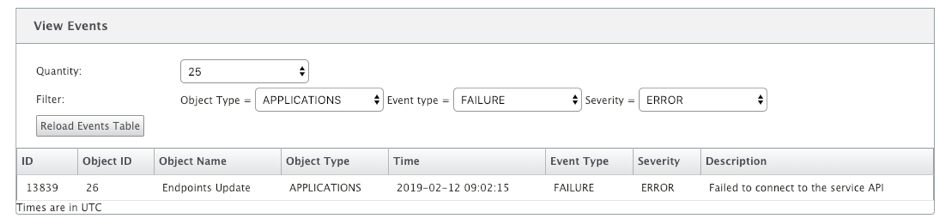
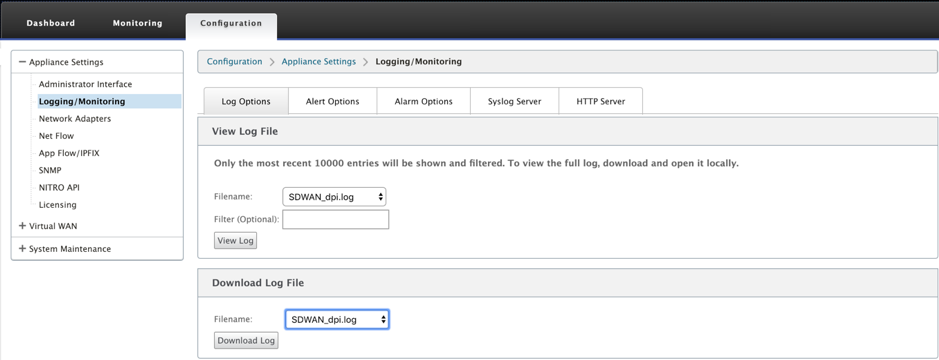
The connectivity errors are also logged to SDWAN_dpi.log. To view the log, navigate to Configuration > Appliance Settings > Logging/ Monitoring > Log Options. Select the SDWAN_dpi.log from the drop-down list and click View Log.
You can also download the log file. To download the log file, select the required log file from the drop-down list under the Download Log file section and click Download Log.
Limitations
- If Office 365 breakout policy is configured, deep packet inspection is not performed on connections destined to the configured category of IP addresses.
- The auto created firewall policy and application routes are uneditable.
- The auto created firewall policy has the lowest priority and is uneditable.
- The route cost for the auto created application route is five. You can override it with a lower cost route.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.