-
-
Direct Internet Access with integrated firewall
-
-
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
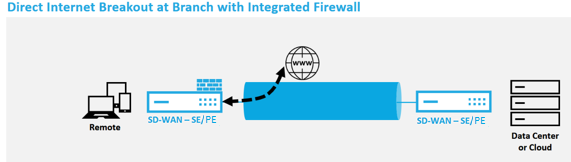
Direct Internet Breakout at Branch with Integrated Firewall
Perform the following steps to enable Internet Service for any site (Client node or MCN):
-
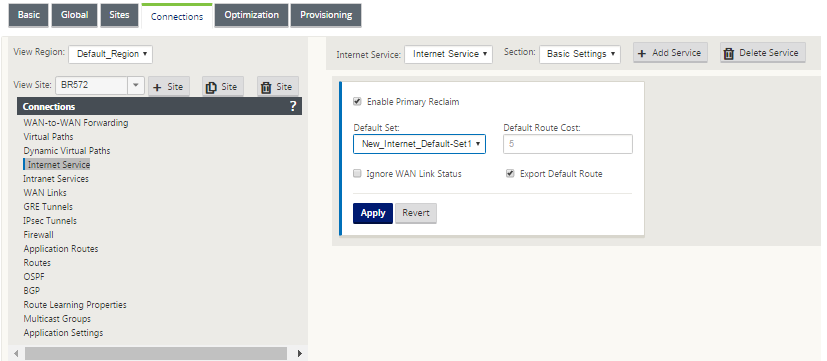
In the Configuration Editor, navigate to the Connections tile. Click the add (+) icon to add an Internet Service for that site. Only one Internet Service can be created per site.
-
In the Basic Settings for the Internet Service, there are several options on how you want the Internet Service to behave during unavailability of WAN links. An Internet Default Set can be defined in the Global tile with a set of Rules that can be applied to any node in the configuration which has Internet Service enabled, giving central control for Internet Service management without having to configure each node separately.
-
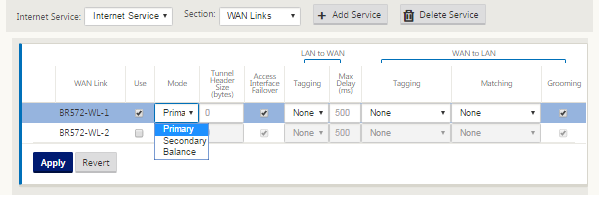
In the Internet Service WAN Links node, the WAN links built in the Site tile are made available to select which WAN link you would like to use for Internet traffic. In addition to other options, the Modes available are Primary, Secondary, and Balanced, allowing the admin to use the available WAN links simultaneously or in an active/passive role.
-
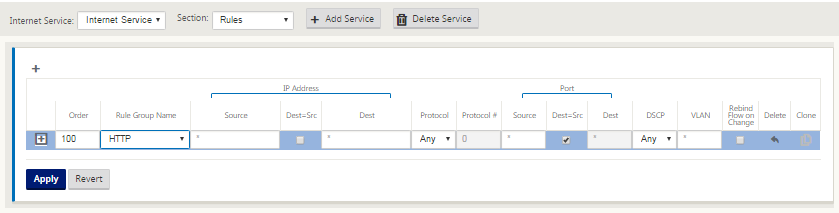
Site node specific Rules are available, enabling the capability of customization of each site uniquely overriding any general settings configured in the global default set. Modes include desired delivery over a specific WAN link, or as an Override Service allowing for passthrough or discard of the filtered traffic.
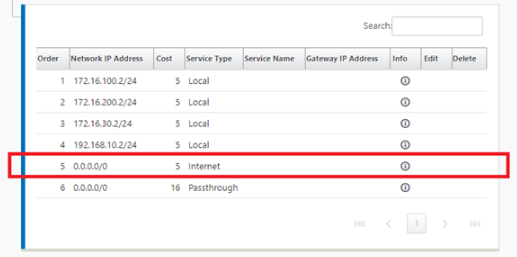
As an Internet Service is created for a node, the Route table for that particular node is automatically updated with a 0.0.0.0/0 route for Service Type equal Internet and a Route cost of 5, otherwise the default route with cost 16 with Passthrough as the Service Type would be enacted, and Internet traffic would be handed off to the underlay network to route.
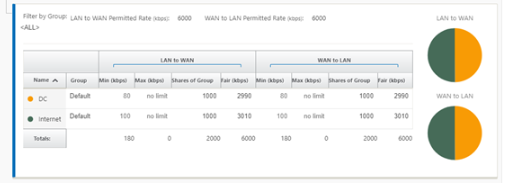
With Internet Service being enabled for a site node, the Provisioning tile is made available to allow for the bidirectional (LAN to WAN / WAN to LAN) distribution of bandwidth for a WAN link among the various services utilizing the WAN link. The Services section allows for users to further fine-tune bandwidth allocation. In addition, fair share can be enabled, allowing for all services to receive their minimum reserved bandwidth before fair distribution is enacted.
The Internet Service can be utilized in the various deployment modes supported by Citrix SD-WAN.
- Inline Deployment Mode (SD-WAN Overlay)
Citrix SD-WAN can be deployed as an overlay solution in any network. As an overlay solution, SD-WAN generally is deployed behind existing edge routers and/or firewalls. If SD-WAN is deployed behind a network firewall, the interface can be configured as trusted and Internet traffic can be delivered to the firewall as an internet gateway.
- Edge or Gateway Mode
Citrix SD-WAN can be deployed as the edge device, replacing existing edge router and/or firewall devices. Onboard firewall feature allows SD-WAN to protect the network from direct internet connectivity. In this mode, the interface connected to the public internet link is configured as untrusted, forcing encryption to be enabled, and firewall and Dynamic NAT features are enabled to secure the network.
Share
Share
In this article
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.