This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Certificate authentication
Citrix SD-WAN ensures secure paths are established between appliances in the SD-WAN network by using security techniques such as network encryption and virtual path IPsec tunnels. In addition to the existing security measures, certificate based authentication is introduced in Citrix SD-WAN 11.0.2.
Certificate authentication, allows organizations to use certificates issued by their private Certificate Authority (CA) to authenticate appliances. The appliances are authenticated before establishing the virtual paths. For example, if a branch appliance tries to connect to the data center and the certificate from the branch does not match with the certificate that the data center expects, the virtual path is not established.
The certificate issued by the CA binds a public key to the name of the appliance. The public key works with the corresponding private key possessed by the appliance identified by the certificate.
Note
In the current release, the CA certificates need to be manually uploaded to all the appliances in the network. The future release will include automatic distribution of the network certificates.
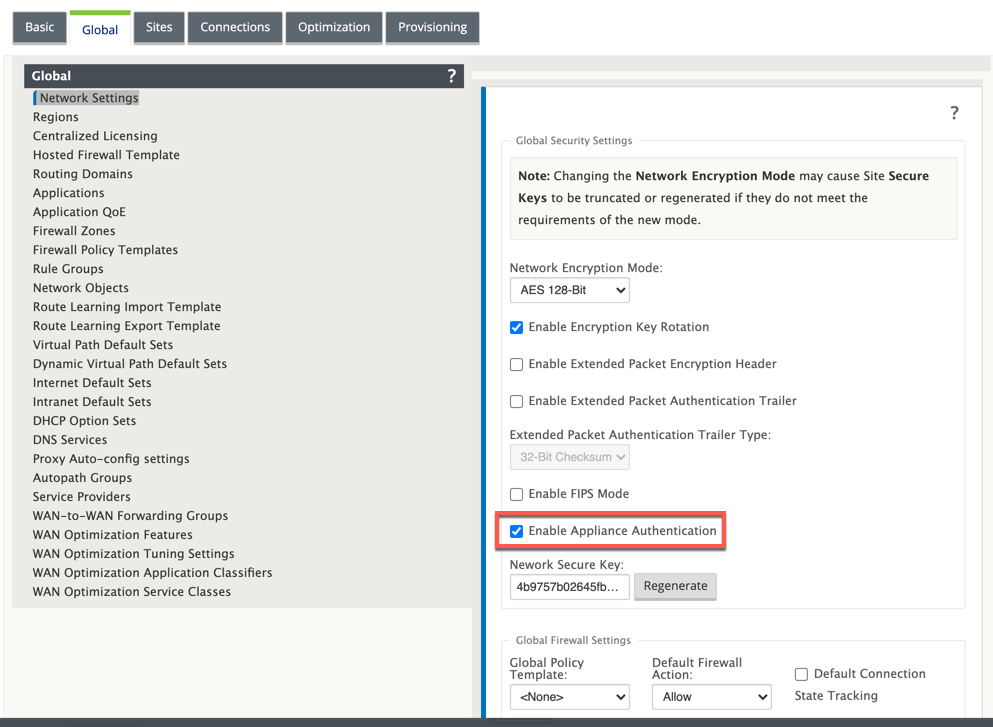
To enable appliance authentication, in the configuration editor, navigate to Global > Network Settings and select Enable Appliance Authentication.
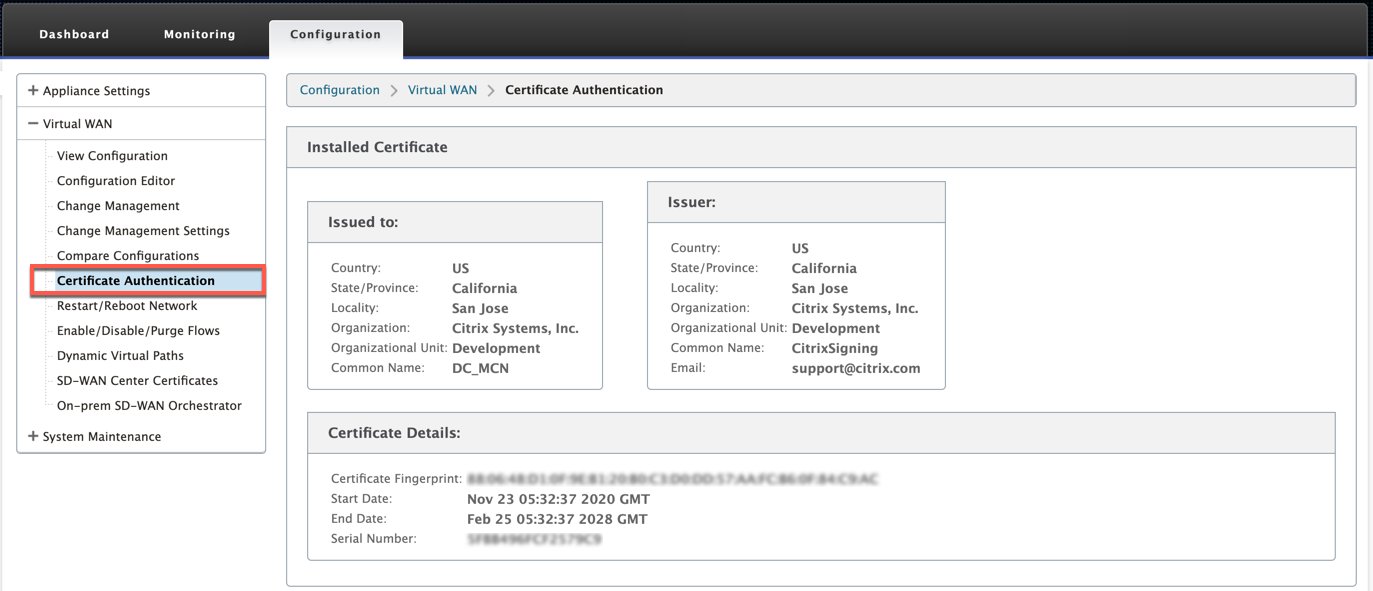
After the configuration is staged and applied, a new Certificate Authentication option is listed under Configuration > Virtual WAN.
You can manage all the certificates used for virtual path authentication from the Certificate Authentication page.
Installed certificate
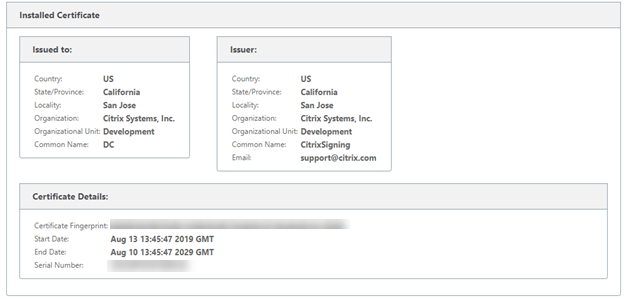
The Installed Certificate section provides a summary of the certificate that is installed on the appliance. The appliance uses this certificate to identify itself in the network.
The Issued to section provides details about who the certificate was issues to. The Common Name in the certificate matches with the name of the appliance, since the certificate is bound to the appliance name. The Issuer section provides the details of the certificate signing authority, who signed the certificate. The Certificate details include the fingerprint of the certificate, serial number, and the validity period for the certificate.
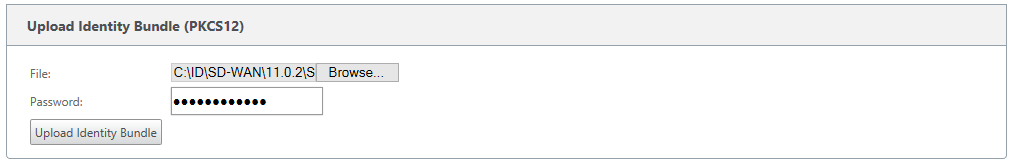
Upload identity bundle
The Identity bundle includes a private key and the certificate associated with the private key. You can upload the appliance certificate issued by the CA into the appliance. The certificate bundle is a PKCS 12 file, with .p12 extension. You can choose to protect it with a password. If you leave the password field blank it is treated as no password protection.
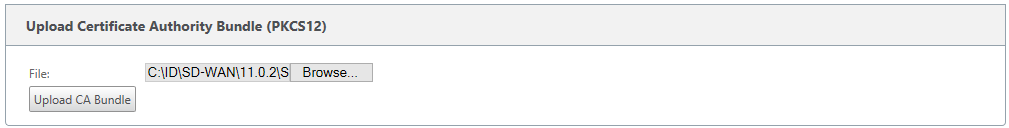
Upload certificate authority bundle
Upload the PKCS 12 bundle that corresponds to the certificate signing authority. The certificate authority bundle includes the complete chain of signatures, the root and all the intermediate signatory authority.
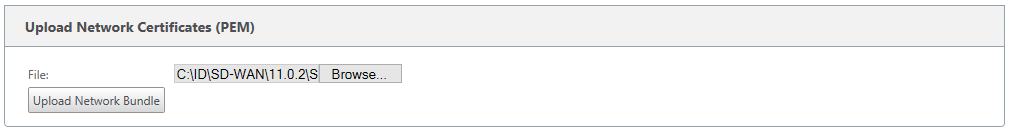
Upload network certificates
Upload all the network certificates that are concatenated together in a single .PEM file. The network certificates have to be uploaded on each of the appliance in the network. When a site initiates a virtual path connection, a message including its certificate is sent to the responder. The responder checks the initiator certificate against the network certificates PEM file. If the initiator certificate matches with a certificate on the database, the virtual path connection is established.
Note
In the current release, the CA certificates need to be manually uploaded to all the appliances in the network. The future release will include automatic distribution of the network certificates.
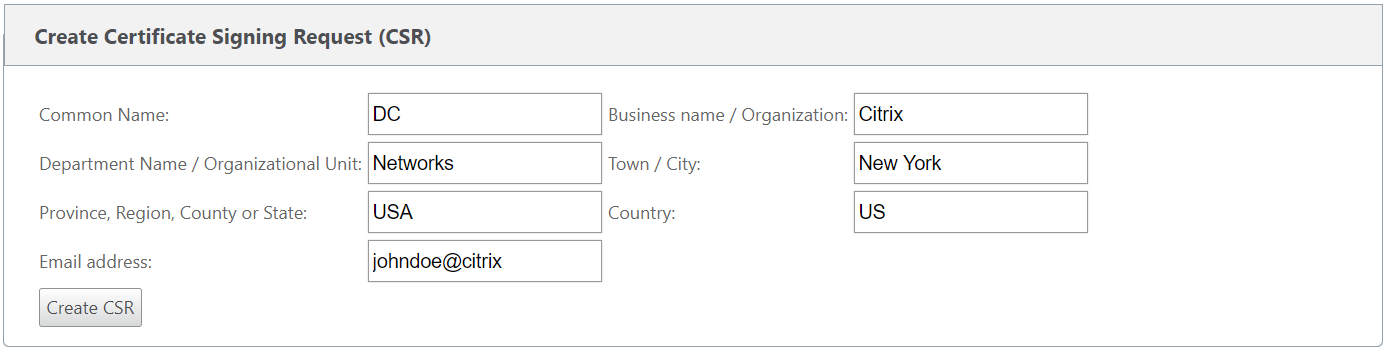
Create certification signing request
The appliance can generate an unsigned certificated and create a Certificate Signing Request (CSR). The CA can then download the CSR from the appliance, sign it and upload it back to the appliance in PEM or DER formats. This is used as an Identity certificate for the appliance. To create a CSR for an appliance, provide the appliance common name, organization details, and address.
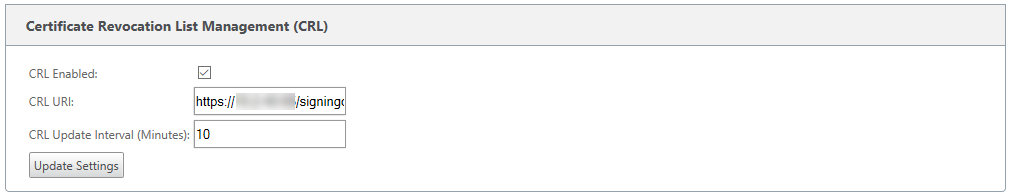
Certificate revocation list manager
A Certificate Revocation List (CRL) is a published list of certificate serial numbers that are no longer valid in the network. The CRL file is periodically downloaded and stored locally on all the appliance. When a certificate is being authenticated the responder examines the CRL to see if the initiators certificate was revoked already. Citrix SD-WAN currently supports version 1 CRLs in PEM and DER format.
To enable CRL, select the CRL enabled option. Provide the location where the CRL file is maintained. HTTP, HTTPS, and FTP locations are supported. Specify the time interval to check and download the CRL file, the range is 1–1440 minutes.
Note
The reauthentication period for a virtua1 path can be between 10–15 minutes, if the CRL update interval is set to a shorter duration, the updated CRL list may include a currently active serial number. Making an actively revoked certificate available in your network for a short duration.
Share
Share
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.