-
-
-
Installing the Splunk Apps
-
-
-
-
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Installing the Splunk Apps
Upgrade
If you are upgrading from an earlier version of the uberAgent Splunk apps please make sure to follow the upgrade instructions.
Please consult the release notes for possible changes in configuration or functionality.
Manual Installation
- Go to the Splunk console’s home page by navigating to
http://servername:8000in your browser. -
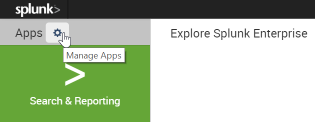
Click Manage apps:
-
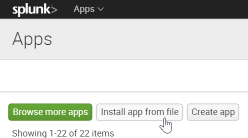
Click Install app from file:
- Select
uberAgent_indexer.tgzand click Upload - The uberAgent® indexer app is now installed
- Install
uberAgent_searchhead.tgzin the same way - Optionally install the uberAgent ESA search head app
uberAgent_ESA_searchhead.tgz, too - Click Settings > Server controls > Restart Splunk
Splunk Enterprise Security uberAgent ESA comes with native support for Splunk Enterprise Security. Install the following apps on your Enterprise Security server to enjoy the benefits:
uberAgent_searchhead.tgzuberAgent_ESA_searchhead.tgz-
uberAgent_ESA_ES_companion.tgz.
Available on Splunkbase.
Using Splunk Cloud The installation process is different when using uberAgent in combination with Splunk Cloud. This knowledgebase article contains all the necessary details.
Distributed Splunk Deployment
If you have a distributed Splunk deployment with separate search heads and indexers please deploy the indexer app to all indexers as well as heavy forwarders and the search head app to all search heads.
Alternative Architectures
Note: This is optional and not required for the recommended architecture.
If you decided to have uberAgent send data to Splunk through a locally installed Universal Forwarder on the monitored endpoints you need to enable receiving Universal Forwarder data as described here, i.e., through Settings > Forwarding and receiving > Receive data > Add new > 9997 > Save.
Sending to Splunk HTTP Event Collector
Note: This is only required when you want uberAgent to send directly to Splunk Cloud, but it can optionally be used with Splunk Enterprise, too.
uberAgent can send the data it collects via HTTP or HTTPS to a Splunk data input called HTTP Event Collector (HEC). Please follow these steps to enable and configure HTTP Event Collector.
Share
Share
In this article
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.