Office 365 optimization
The Office 365 Optimization features adhere to the Microsoft Office 365 Network Connectivity Principles, to optimize Office 365. Office 365 is provided as a service through several service endpoints (front doors) located globally. To achieve optimal user experience for Office 365 traffic, Microsoft recommends redirecting Office365 traffic directly to the Internet from branch environments. Avoid practices such as backhauling to a central proxy. Office 365 traffic such as Outlook, Word are sensitive to latency and backhauling traffic introduces more latency resulting in poor user experience. Citrix SD-WAN allows you to configure policies to break out Office 365 traffic to the Internet.
The Office 365 traffic is directed to the nearest Office 365 service endpoint, which exists at the edges of Microsoft Office 365 infrastructure worldwide. Once traffic reaches a front door, it goes over Microsoft’s network and reaches the actual destination. It minimizes latency as the round trip time from the customer network to the Office 365 endpoint reduces.
Office 365 endpoints
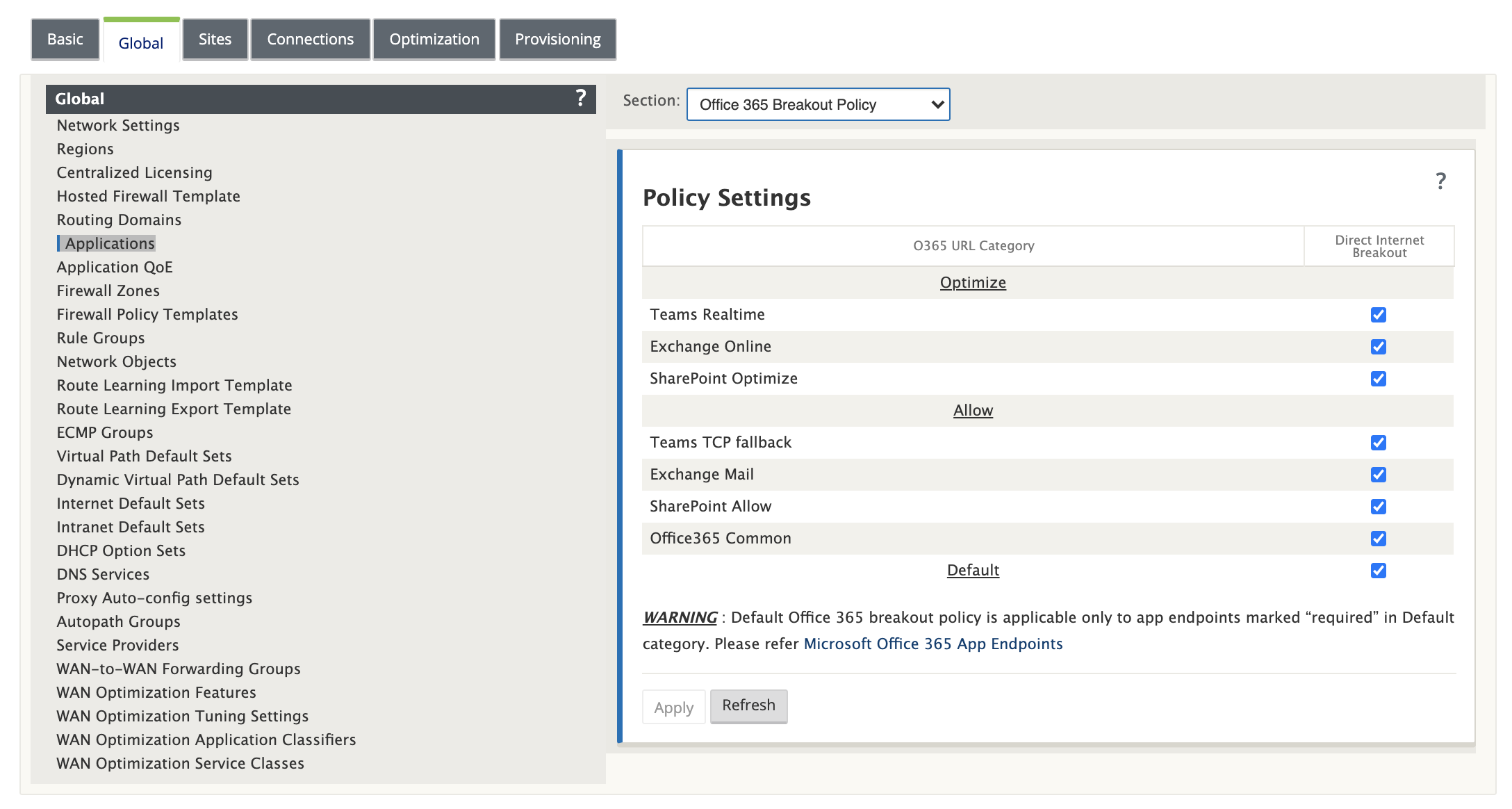
Office 365 endpoints are a set of network addresses and subnets. Office 365 endpoints are classified into Optimize, Allow, and Default categories. Citrix SD-WAN 11.4.0 provides a more granular classification of the Optimize and Allow categories, enabling selective bookending to improve the performance of network-sensitive Office 365 traffic. Directing network-sensitive traffic to SD-WAN in the cloud (Cloud Direct or an SD-WAN VPX on Azure), or from an at-home SD-WAN device to an SD-WAN at a nearby location with more reliable Internet connectivity, enables QoS and superior connection resilience compared to simply steering the traffic to the nearest Office 365 front door, at the cost of an increase in latency. A bookended SD-WAN solution with QoS reduces VoIP dropouts and disconnects, reduces jitter and improves media-quality mean opinion scores for Microsoft Teams:
- Optimize - These endpoints provide connectivity to every Office 365 service and feature, and are sensitive to availability, performance, and latency. It represents over 75% of Office 365 bandwidth, connections, and volume of data. All the Optimize endpoints are hosted in Microsoft data centers. Service requests to these endpoints must breakout from the branch to the Internet and must not go through the data center.
The Optimize category is classified into the following subcategories:
- Teams Realtime
- Exchange Online
- SharePoint Optimize
For information about upgrade considerations, see Important considerations for upgrade.
- Allow - These endpoints provide connectivity to specific Office 365 services and features only, and are not so sensitive to network performance and latency. The representation of Office 365 bandwidth and connection count is also lower. These endpoints are hosted in Microsoft data centers. Service requests to these endpoints might breakout from the branch to the Internet or might go through the data center.
The Allow category is classified into the following subcategories:
- Teams TCP Fallback
- Exchange Mail
- SharePoint Allow
- Office365 Common
For information about upgrade considerations, see Important considerations for upgrade.
Note
The Teams Realtime subcategory uses the UDP real-time transport protocol to manage Microsoft Teams traffic, whereas the Teams TCP Fallback subcategory uses the TCP transport layer protocol. As media traffic is highly latency sensitive, you might prefer this traffic to take the most direct path possible and to use UDP instead of TCP as the transport layer protocol (most preferred transport for interactive real-time media in terms of quality). While UDP is a preferred protocol for Teams media traffic, it requires certain ports to be allowed in the firewall. If the ports are not allowed, Teams traffic uses TCP as a fallback, and enabling optimization for Teams TCP Fallback ensures better delivery of the Teams application in this scenario. For more information, see Microsoft Teams call flows.
- Default - These endpoints provide Office 365 services that do not require any optimization, and can be treated as normal Internet traffic. Some of these endpoints might not be hosted in Microsoft data centers. The traffic in this category is not susceptible to variations in latency. Therefore, direct breaking out of this type of traffic does not cause any performance improvement when compared to Internet breakout. In addition, the traffic in this category may not always be Office 365 traffic. Hence, it is recommended to disable this option when enabling Office 365 breakout in your network.
How Office 365 optimization works
The Microsoft endpoint signatures are updated at most once a day. Agent on the appliance polls the Citrix service (sdwan-app-routing.citrixnetworkapi.net), every day to obtain the latest set of end-point signatures. The SD-WAN appliance polls the Citrix service (sdwan-app-routing.citrixnetworkapi.net), once every day, when the appliance is turned on. If there are new signatures available, the appliance downloads it and stores it in the database. The signatures are essentially a list of URLs and IPs used to detect Office 365 traffic based on which traffic steering policies can be configured.
Note
Except for the Office 365 Default category, first packet detection and classification of Office 365 traffic is performed by default, irrespective of whether the Office 365 breakout feature is enabled or not.
When a request for the Office 365 application arrives, the application classifier, does a first packet classifier database lookup, identifies, and marks Office 365 traffic. Once the Office 365 traffic is classified, the auto created application route and firewall policies take effect and breaks out the traffic directly to the Internet. The Office 365 DNS requests are forwarded to specific DNS services like Quad9. For more information, see Domain name system.
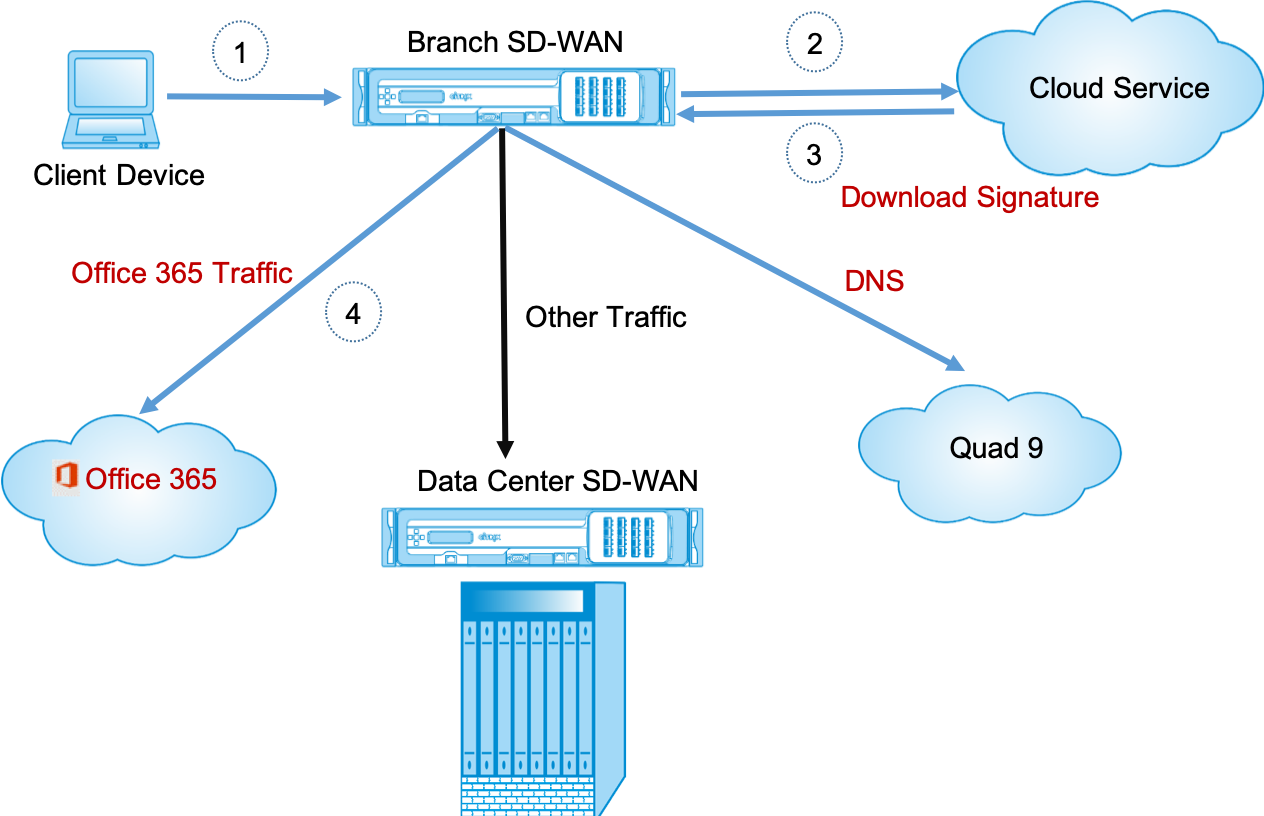
The signatures are downloaded from Cloud Service (sdwan-app-routing.citrixnetworkapi.net).
Configure Office 365 breakout
The Office 365 breakout policy allows you to specify which category of Office 365 traffic you can directly break out from the branch. On enabling Office 365 breakout and compiling the configuration, a DNS object, application object, application route, and a firewall policy template is auto-created and applied to branch sites with the Internet service.
Prerequisites
Ensure that you have the following:
-
To perform Office 365 breakout, an internet service has to be configured on the appliance. For more information on configuring internet service, see Internet access.
-
Ensure that the Management interface has internet connectivity.
You can use the Citrix SD-WAN web interface to configure the management interface settings.
-
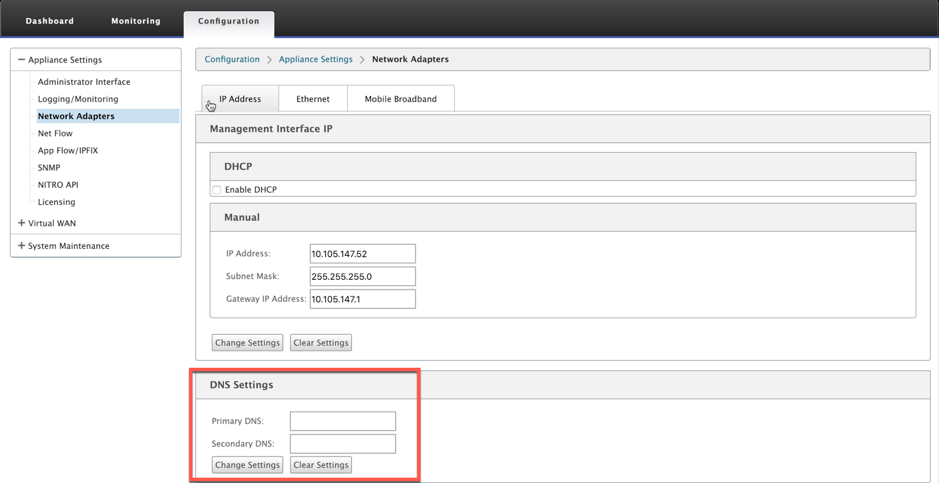
Ensure that the management DNS is configured. To configure management interface DNS navigate to Configuration > Appliance Settings > Network Adapter. Under the DNS Settings section, provide the primary and secondary DNS server detail and click Change Settings.
The Office 365 Breakout Policy setting is available under global settings, select the required Office 365 category for internet breakout and click Apply.
After you configure the Office 365 break out policy settings and compile the configuration. The following settings are auto populated.
-
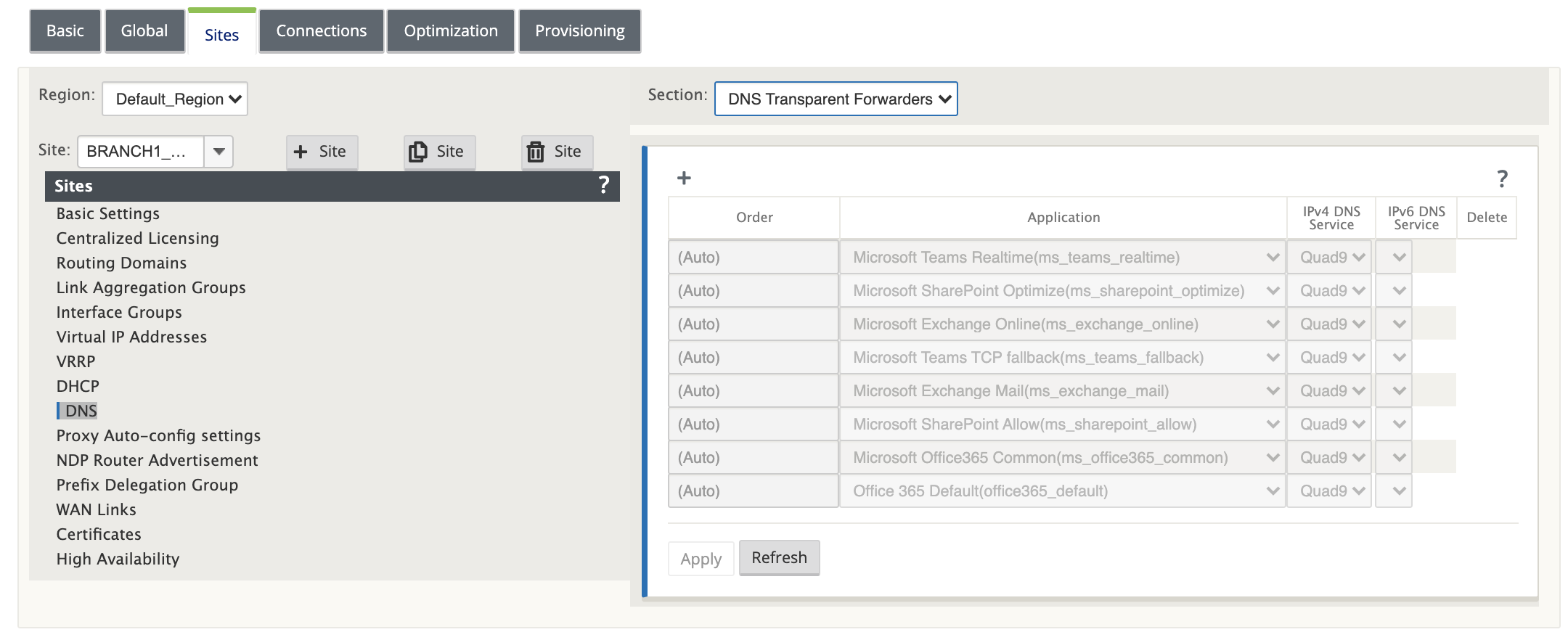
DNS object - The DNS object specifies which type of traffic to be forwarded to the DNS service that the user is configured. The DNS requests are heard on all trusted interfaces, and DNS forwarders are included to direct Office 365 DNS requests to Quad9 service. This forwarder rule takes the highest priority. For more information, see Domain Name Service section.
-
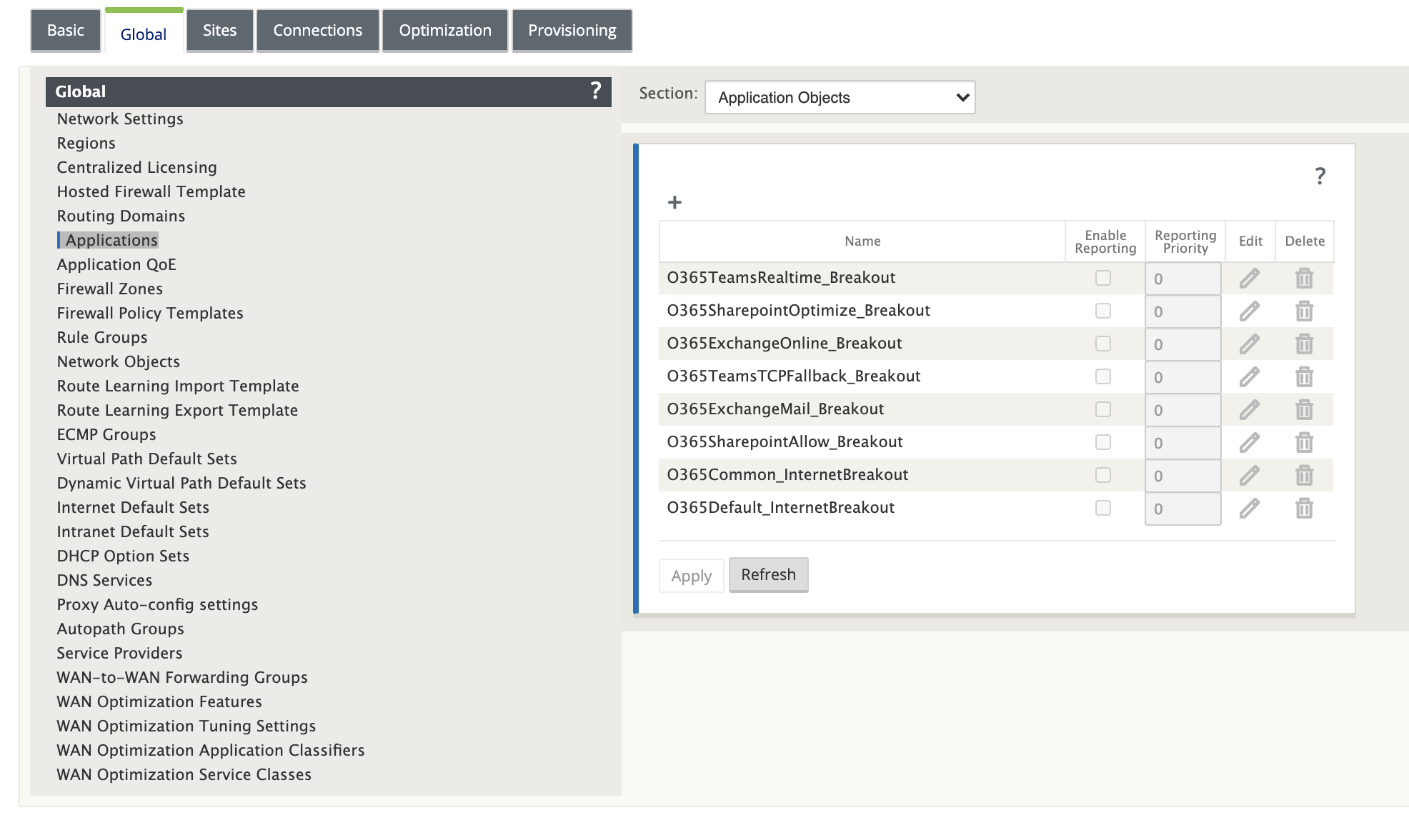
Application object - An application object with the Office 365 category or subcategory selected by the user is created. If you have selected the Default category and the subcategories of Optimize and Allow, the corresponding application objects are created as shown in the following screenshot:
-
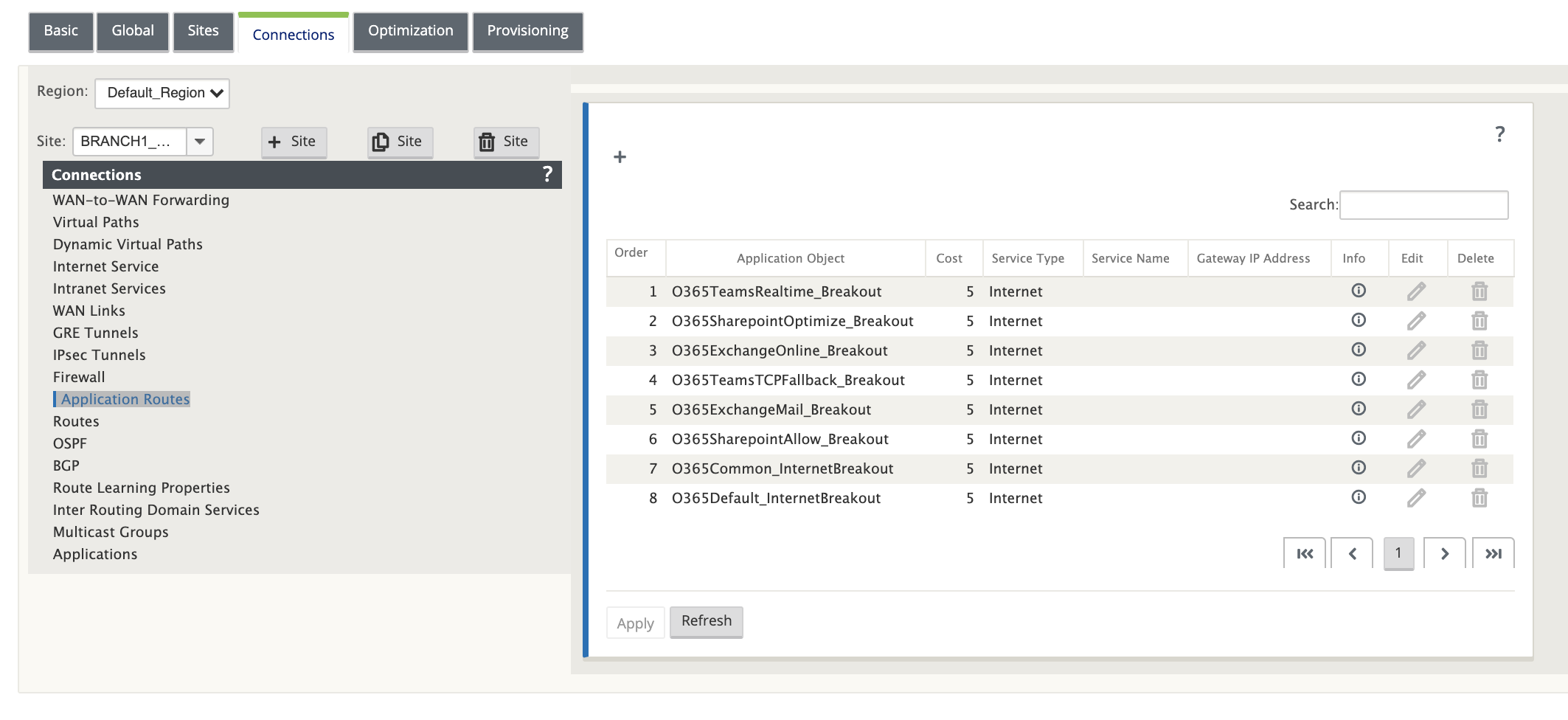
Application route: An application route is created for each of the Office 365 application objects with Internet Service type. For information about upgrade considerations, see Important considerations for upgrade.
-
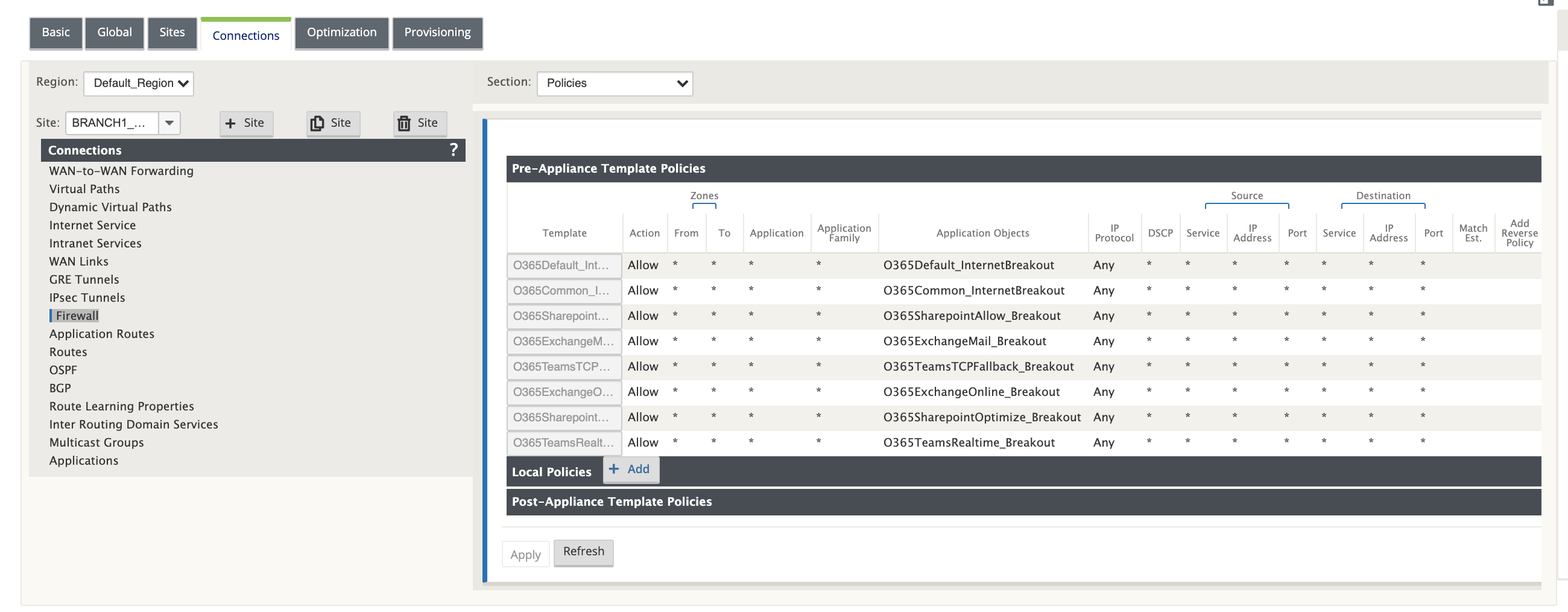
Firewall pre-appliance policy template: A global pre-appliance policy template is created for each configured Office 365 category. This template is applied to all branch sites that have Internet service. The pre-appliance policy takes priority over local and post appliance policy templates. For information about upgrade considerations, see Important considerations for upgrade.
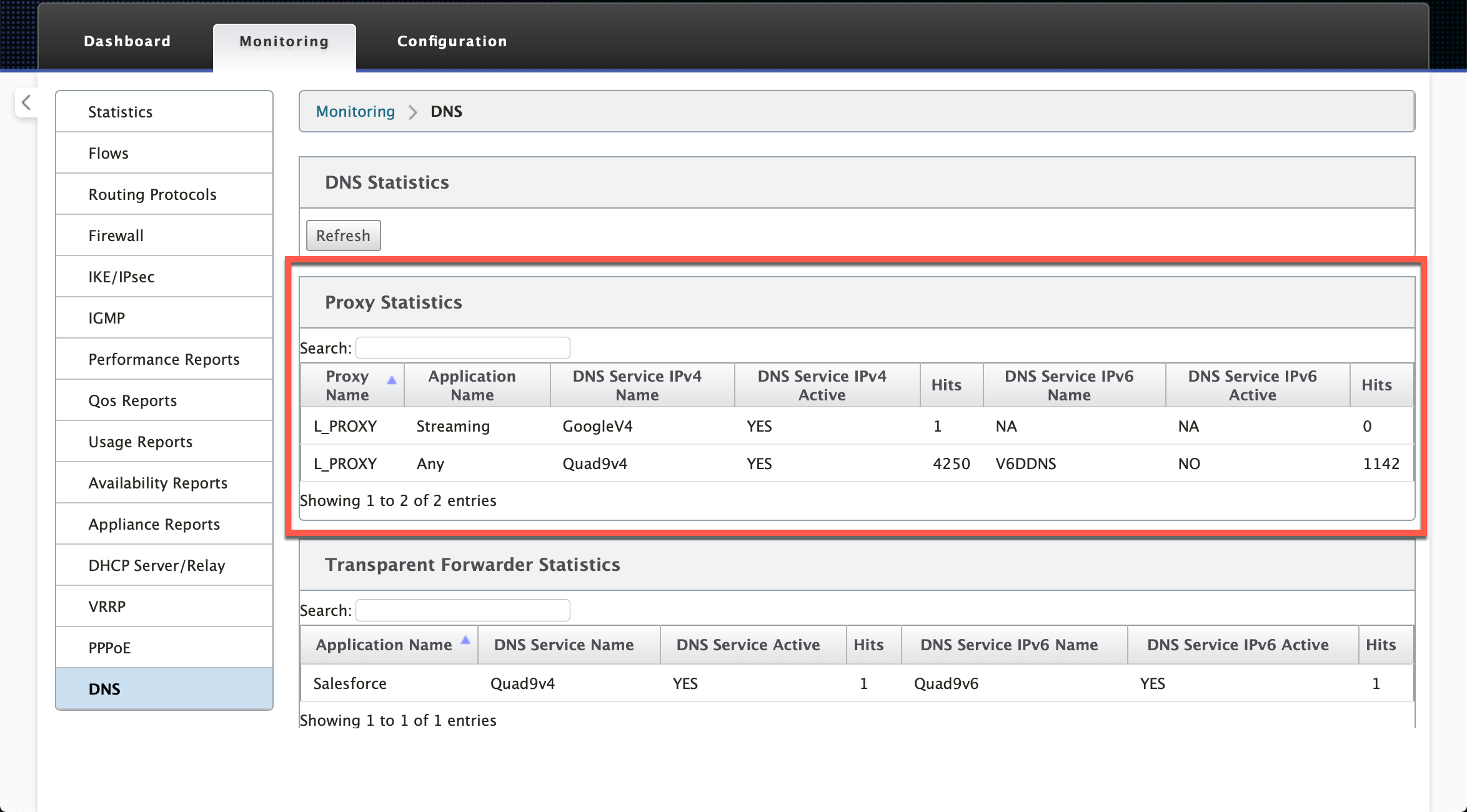
Transparent forwarder for Office 365
The branch breaks out for Office 365 begins with a DNS request. The DNS request going through Office 365 domains have to be steered locally. If Office 365 Internet break out is enabled, the internal DNS routes are determined and the transparent forwarders list is auto populated. Office 365 DNS requests are forwarded to open source DNS service Quad 9 by default. Quad 9 DNS service is secure, scalable, and has multi pop presence. You can change the DNS service if necessary.
Transparent forwarders for Office 365 applications are created at every branch that has Internet service and office 365 breakout enabled.
If you are using another DNS proxy or if SD-WAN is configured as the DNS proxy, the forwarder list is auto populated with forwarders for Office 365 applications.
Important considerations for upgrade
Optimize and Allow categories
If you have enabled the Internet breakout policy for the Optimize and Allow Office 365 categories, Citrix SD-WAN automatically enables the Internet breakout policy for the corresponding subcategories upon upgrade to Citrix SD-WAN 11.4.0.
When you downgrade to a software version older than Citrix SD-WAN 11.4.0, you must manually enable Internet breakout for the Optimize or Allow Office 365 category irrespective of whether you enabled the corresponding subcategories in the Citrix SD-WAN 11.4.0 version or not.
Office 365 application objects
If you have created rules/routes using the O365Optimize_InternetBreakout and O365Allow_InternetBreakout auto-generated application objects, ensure to delete the rules/routes before upgrading to Citrix SD-WAN 11.4.0. After the upgrade, you can create rules/ routes using the corresponding new application objects.
If you proceed with Citrix SD-WAN 11.4.0 upgrade without deleting the rules/routes, you see an error and thus, the upgrade becomes unsuccessful. In the below example, a user has configured an Application QoE profile and is seeing an error while trying to upgrade to Citrix SD-WAN 11.4.0 without deleting the rules/routes:
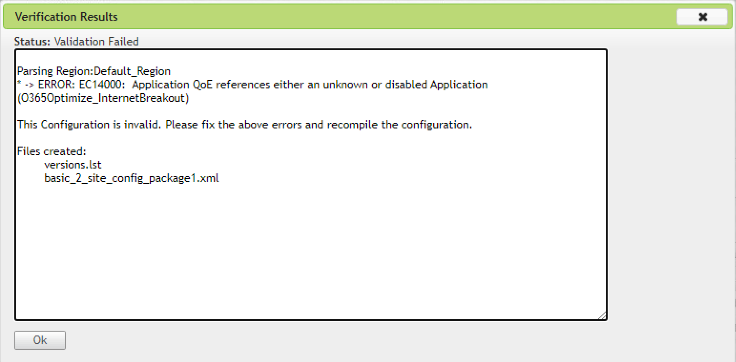
Note
This upgrade is not required for auto-created rules/routes. It applies only to rules/ routes that you have created.
DNS
If you have created DNS Proxy rules or DNS transparent forwarder rules using the Office 365 Optimize and Office 365 Allow applications, ensure to delete the rules before upgrading to Citrix SD-WAN 11.4.0. After the upgrade, you can create the rules again using the corresponding new applications.
If you proceed with Citrix SD-WAN 11.4.0 upgrade without deleting the old DNS proxy or transparent forwarder rules, you do not see any error and upgrade becomes successful too. However, the DNS proxy rules and transparent forwarding rules do not take effect in Citrix SD-WAN 11.4.0.
Note
This activity does not apply to the auto-created DNS rules. It applies only to DNS rules that you have created.
Monitoring
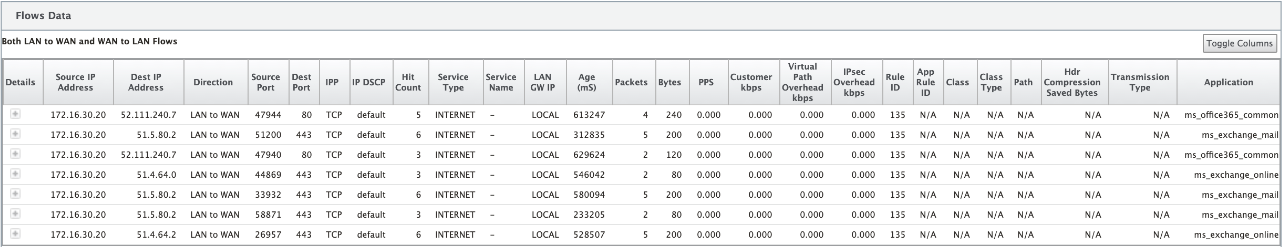
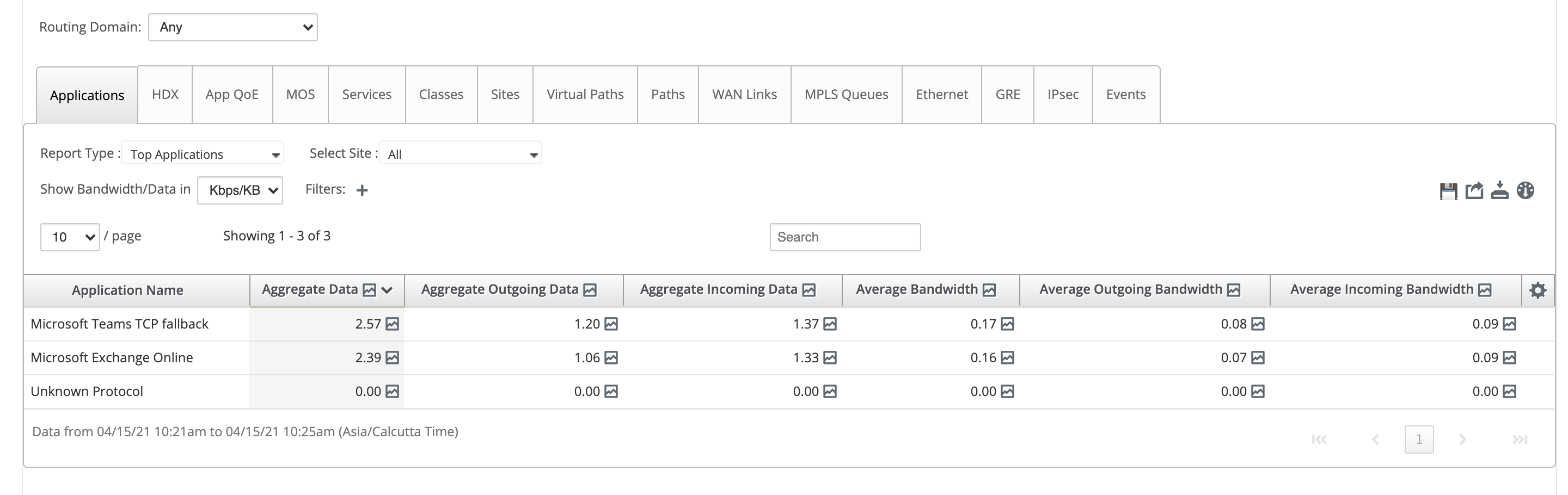
You can monitor the office 365 application statistics in the following SD-WAN statistic reports:
-
Firewall Statistics
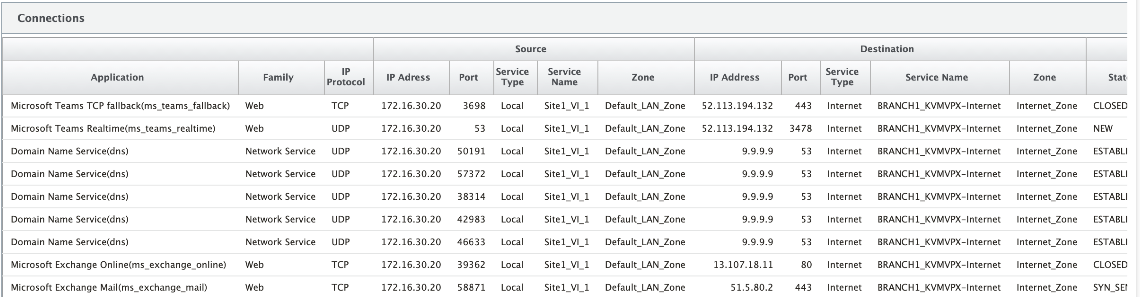
-
Flows
-
DNS Statistics
-
Application Route Statistics
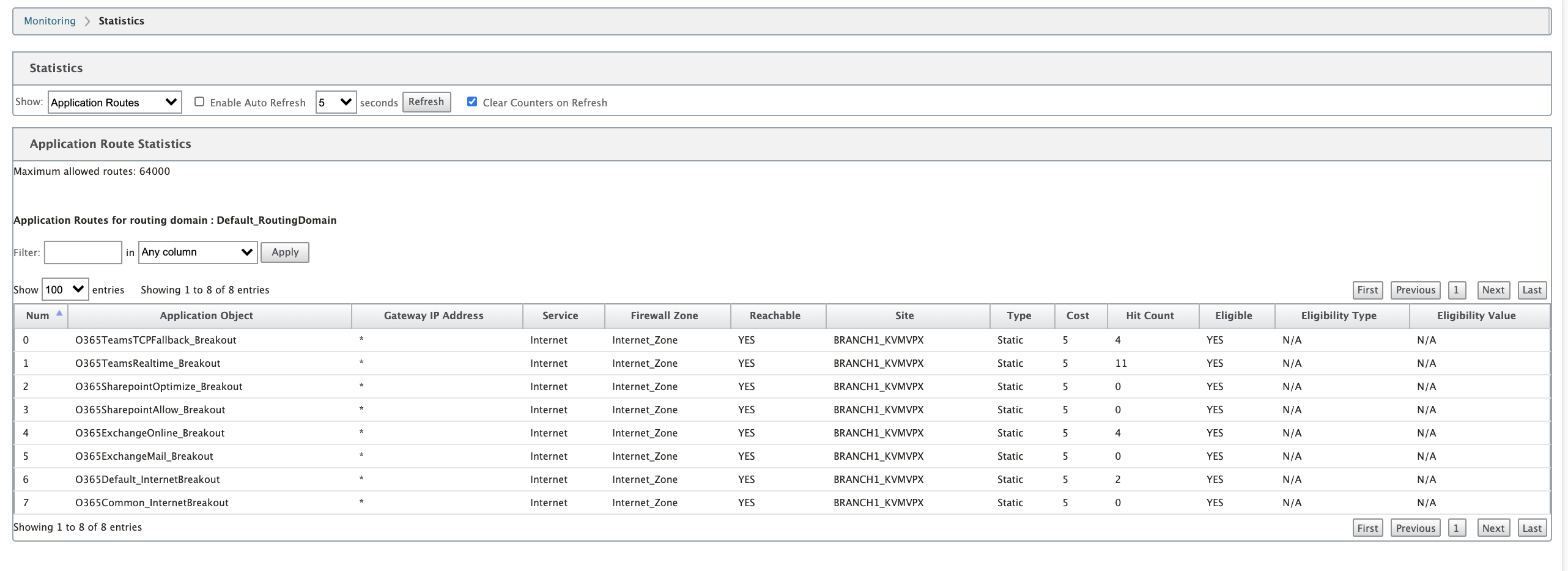
You can also view Office 365 application statistics in the SD-WAN Center Application report.
Troubleshooting
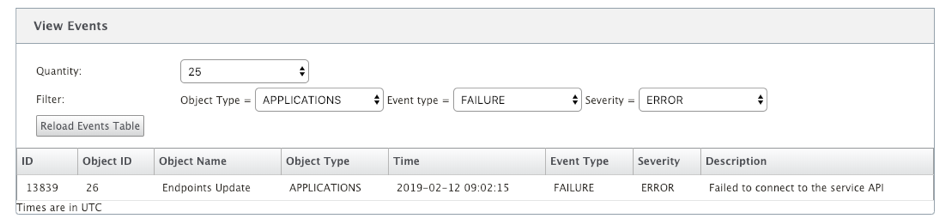
You can view the service error in the Events section of the SD-WAN appliance.
To check the errors, navigate to Configuration > System Maintenance > Diagnostics, click Events tab.
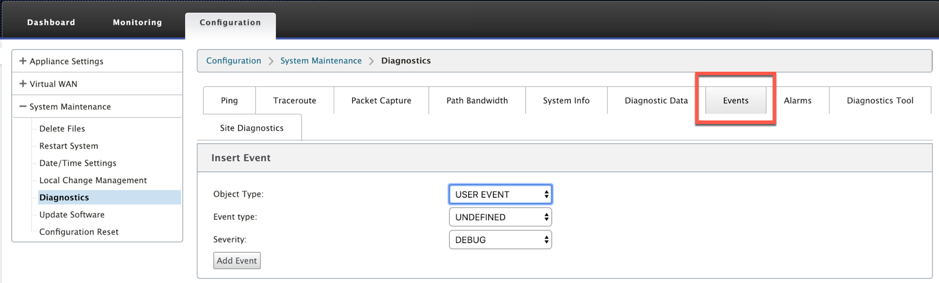
If there is an issue in connecting to the Citrix service (sdwan-app-routing.citrixnetworkapi.net), then the error message reflects under the View Events table.
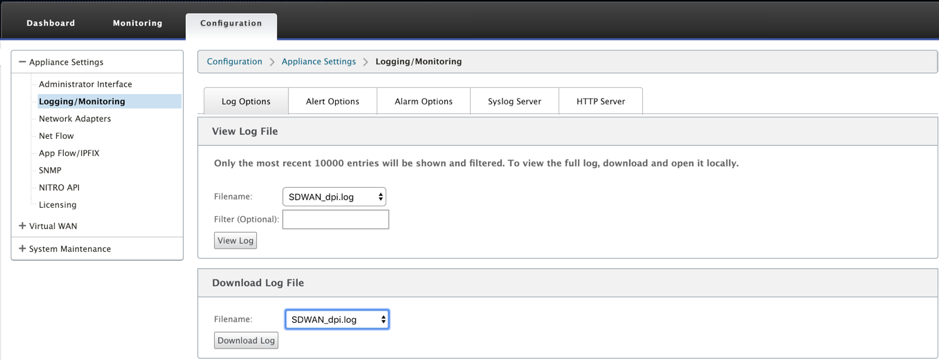
The connectivity errors are also logged to SDWAN_dpi.log. To view the log, navigate to Configuration > Appliance Settings > Logging/ Monitoring > Log Options. Select the SDWAN_dpi.log from the drop-down list and click View Log.
You can also download the log file. To download the log file, select the required log file from the drop-down list under the Download Log file section and click Download Log.
Limitations
- If the Office 365 breakout policy is configured, deep packet inspection is not performed on connections destined to the configured category of IP addresses.
- The auto created firewall policy and application routes are uneditable.
- The auto created firewall policy has the lowest priority and is uneditable.
- The route cost for the auto created application route is five. You can override it with a lower cost route.
Office 365 beacon service
Microsoft provides the Office 365 beacon service to measure the Office 365 reachability through the WAN links. The beacon service is basically a URL - sdwan.measure.office.com/apc/trans.gif, which is probed at regular intervals. Probing is done on each appliance for every internet enabled WAN link. With each probe, an HTTP request is sent to the beacon service and an HTTP response is expected. The HTTP response confirms the availability and reachability of the Office 365 service.
Citrix SD-WAN allows you to not only perform beacon probing, but also determines the latency to reach Office 365 endpoints through each WAN link. The latency is the round trip time taken to send a request and get a response from the Office 365 beacon service over a WAN link. This enables network administrators to view the beacon service latency report and manually choose the best internet link for direct Office 365 breakout. Beacon probing is enabled only through Citrix SD-WAN Orchestrator. By default, beacon probing is enabled on all Internet enabled WAN links when Office 365 break-out is enabled through Citrix SD-WAN Orchestrator.
Note
Office 365 beacon probing is not enabled on metered links.
You can choose to disable Office 365 beacon probing and view latency reports on the SD-WAN Orchestrator. For more information, see Office 365 optimization.
To disable Office 365 beacon service, in SD-WAN Orchestrator, at network level navigate to Configuration > Routing > Routing Policies > O365 Network Optimization Settings and clear Enable Beacon Service.
![]()
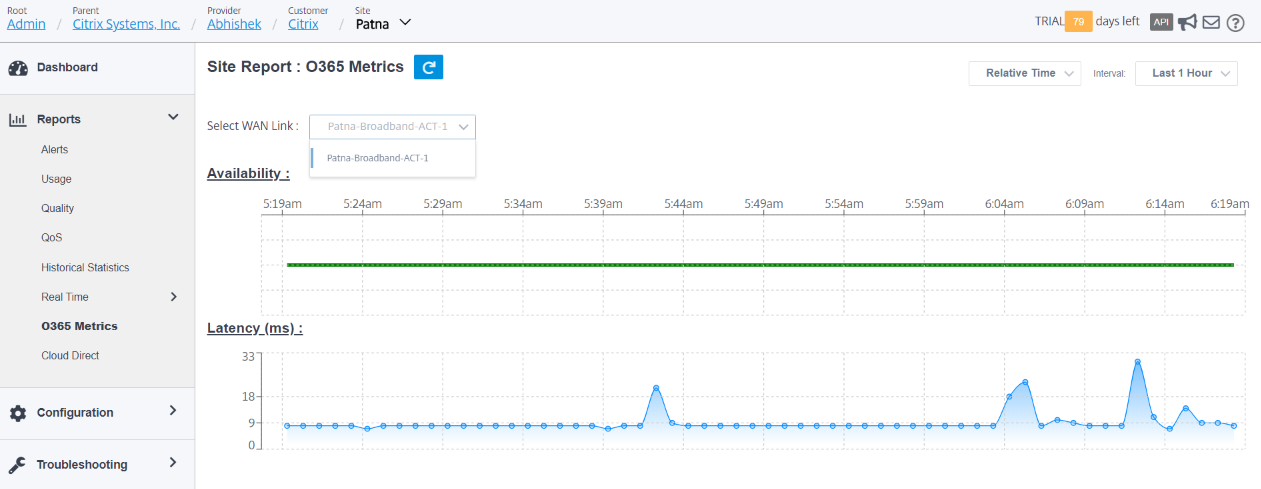
To view the beacon probing availability and latency reports, in Citrix SD-WAN Orchestrator, at network level navigate to Reports > O365 Metrics.
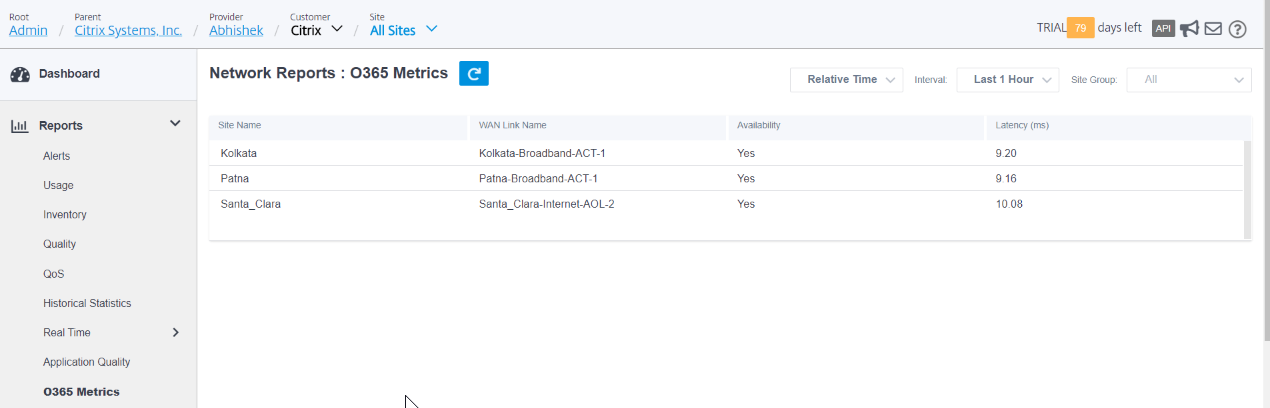
To view a detailed site level report of beacon service, in SD-WAN Orchestrator, at site level navigate to Reports > O365 Metrics.