Citrix Secure Web™
Citrix Secure Web is an HTML5 compatible mobile web browser that provides secure access to internal and external sites. You can configure Secure Web to be pushed to user devices automatically when the devices are enrolled in Secure Hub. Alternatively, you can add the app from the Endpoint Management app store.
For Secure Web and other mobile productivity apps system requirements, see System requirements.
Integrating and delivering Secure Web
Note:
The MDX Toolkit 10.7.10 is the final release that supports the wrapping of mobile productivity apps. Users access mobile productivity apps versions 10.7.5 and later from the public app stores.
To integrate and deliver Secure Web, follow these general steps:
-
To enable Single sign-on (SSO) to the internal network, configure Citrix Gateway.
For HTTP traffic, Citrix ADC can provide SSO for all proxy authentication types supported by Citrix ADC. For HTTPS traffic, the Web password caching policy enables Secure Web to authenticate and provide SSO to the proxy server through MDX. MDX supports basic, digest, and NTLM proxy authentication only. The password is cached using MDX and stored in the Endpoint Management shared vault, a secure storage area for sensitive app data. For details about Citrix Gateway configuration, see Citrix Gateway.
- Download Secure Web.
- Determine how you want to configure user connections to the internal network.
- Add Secure Web to Endpoint Management, by using the same steps as for other MDX apps and then configure MDX policies. For details about policies specific to Secure Web, see “About Secure Web policies” later in this article.
Configuring user connections
Secure Web supports the following configurations for user connections:
- Tunneled – Web SSO: Connections that tunnel to the internal network can use a variation of a clientless VPN, referred to as Tunneled – Web SSO. This is the default configuration specified for the Preferred VPN mode policy. Tunneled – Web SSO is recommended for connections that require single sign-on (SSO).
- Full VPN tunnel: Connections that tunnel to the internal network can use a full VPN tunnel, configured by the Preferred VPN mode policy. Full VPN tunnel is recommended for connections that use client certificates or end-to-end SSL to a resource in the internal network. Secure Web, however, is not an app that can read client certificates stored on a mobile device. Some third-party, wrapped enterprise apps may be installed that can offer this capability. Full VPN tunnel handles any protocol over TCP and can be used with Windows and Mac computers, in addition to iOS and Android devices.
- The Permit VPN mode switching policy allows automatic switching between the full VPN tunnel and Tunneled – Web SSO modes as needed. By default, this policy is off. When this policy is on, a network request that fails due to an authentication request that cannot be handled in the preferred VPN mode is retried in the alternate mode. For example, full VPN tunnel mode accomodates server challenges for client certificates, but not the Tunneled – Web SSO mode. Similarly, HTTP authentication challenges are more likely to be serviced with SSO when using Tunneled – Web SSO mode.
The following table notes whether Secure Web prompts a user for credentials, based on the configuration and site type:
| Connection mode | Site type | Password Caching | SSO configured for Citrix Gateway | Secure Web prompts for credentials on first access of a website | Secure Web prompts for credentials on subsequent access of the website | Secure Web prompts for credentials on after password change |
|---|---|---|---|---|---|---|
| Tunneled – Web SSO | HTTP | No | Yes | No | No | No |
| Tunneled – Web SSO | HTTPS | No | Yes | No | No | No |
| Full VPN | HTTP | No | Yes | No | No | No |
| Full VPN | HTTPS | Yes; If the Secure Web MDX policy Enable web password caching is On. | No | Yes; Required to cache the credential in Secure Web. | No | Yes |
Secure Web policies
When adding Secure Web, be aware of these MDX policies that are specific to Secure Web. For all supported mobile devices:
Allowed or blocked websites
Secure Web normally does not filter web links. You can use this policy to configure a specific list of allowed or blocked sites. You configure URL patterns to restrict the websites the browser can open, formatted as a comma-separated list. A plus sign (+) or minus sign (-) precedes each pattern in the list. The browser compared a URL against the patterns in the order listed until a match is found. When a match is found, the prefix decides the action to take, as follows:
- A minus (-) prefix instructs the browser to block the URL. In this case, the URL is treated as if the web server address cannot be resolved.
- A plus (+) prefix allows the URL to be processed normally.
- If neither + or - is provided with the pattern, + (allow) is assumed.
- If the URL does not match any pattern in the list, the URL is allowed
To block all other URLs, end the list with a minus sign followed by an asterisk (-*). For example:
- The policy value
+http://*.mycorp.com/*,-http://*,+https://*,+ftp://*,-*permits HTTP URLs withinmycorp.comdomain, but blocks them elsewhere, permits HTTPS and FTP URLS anywhere, and blocks all other URLs. - The policy value
+http://*.training.lab/*,+https://*.training.lab/*,-*allows users open any sites in Training.lab domain (intranet) via HTTP or HTTPS. However, you cannot open public URLs such as Facebook, Google, and Hotmail, regardless of the protocol.
Default value is empty (all URLs allowed).
Block pop-ups
Popups are new tabs that websites open without your permission. This policy determines whether Secure Web allows popups. If On, Secure Web prevents websites from opening pop-ups. Default value is Off.
Preloaded bookmarks
Defines a preloaded set of bookmarks for the Secure Web browser. The policy is a comma-separated list of tuples that include a folder name, friendly name, and web address. Each triplet must be of the form folder, name, url where folder and name might optionally be enclosed in double quotes (“).
For example, the policy values,"Mycorp, Inc. home page",https://www.mycorp.com, "MyCorp Links",Account logon,https://www.mycorp.com/Accounts "MyCorp Links/Investor Relations","Contact us",https://www.mycorp.com/IR/Contactus.aspx define three bookmarks. The first is a primary link (no folder name) titled “Mycorp, Inc. home page”. The second link is placed in a folder titled “MyCorp Links” and labeled “Account logon”. The third is placed in the “Investor Relations’ subfolder of the “MyCorp Links” folder and displayed as “Contact us”.”
Default value is empty.
Home page URL
Defines the website that Secure Web loads when started. Default value is empty (default start page).
For supported Android and iOS devices only:
Browser user interface
Dictates the behavior and visibility of browser user interface controls for Secure Web. Normally all browsing controls are available. These include forward, backward, address bar, and the refresh/stop controls. You can configure this policy to restrict the use and visibility of some of these controls. Default value is All controls visible.
Options
- All controls visible. All controls are visible and users are not restricted from using them.
- Read-only address bar. All controls are visible, but users cannot edit the browser address field.
- Hide address bar. Hides the address bar, but not other controls.
- Hide all controls. Suppresses the entire toolbar to provide a frameless browsing experience.
Enable web password caching
When Secure Web users enter credentials when accessing or requesting a web resource, this policy determines whether Secure Web silently caches the password on the device. This policy applies to passwords entered in authentication dialogs and not to passwords entered in web forms.
If On, Secure Web caches all passwords users enter when requesting a web resource. If Off, Secure Web does not cache passwords and removes existing cached passwords. Default value is Off.
This policy is enabled only when you also set the Preferred VPN policy to Full VPN tunnel for this app.
Proxy servers
You can also configure proxy servers for Secure Web when used in Tunneled – Web SSO mode. For details, see this blog post.
DNS suffixes
On Android, if DNS suffixes aren’t configured, the VPN might fail. For details on configuring DNS suffixes, see Supporting DNS Queries by Using DNS Suffixes for Android Devices.
Preparing intranet sites for Secure Web
This section is for website developers who need to prepare an intranet site for use with Secure Web for Android and iOS. Intranet sites designed for desktop browsers require changes to work properly on Android and iOS devices.
Secure Web relies on Android WebView and iOS WkWebView to provide web technology support. Some of the web technologies supported by Secure Web are:
- AngularJS
- ASP .NET
- JavaScript
- jQuery
- WebGL
- WebSockets
Some of the web technologies not supported by Secure Web are:
- Flash
- Java
The following table shows the HTML rendering features and technologies supported for Secure Web. X indicates the feature is available for a platform, browser, and component combination.
| Technology | iOS Secure Web | Android 6.x/7.x Secure Web |
|---|---|---|
| JavaScript engine | JavaScriptCore | V8 |
| Local Storage | X | X |
| AppCache | X | X |
| IndexedDB | X | |
| SPDY | X | |
| WebP | X | |
| srcet | X | X |
| WebGL | X | |
| requestAnimationFrame API | X | |
| Navigation Timing API | X | |
| Resource Timing API | X |
Technologies work the same across devices; however, Secure Web returns different user agent strings for different devices. To determine the browser version used for Secure Web, you can view its user agent string. From Secure Web, navigate to https://whatsmyuseragent.com/.
Troubleshooting intranet sites
To troubleshoot rendering issues when your intranet site is viewed in Secure Web, compare how the website renders on Secure Web and a compatible third-party browser.
For iOS, the compatible third-party browsers for testing are Chrome and Dolphin.
For Android, the compatible third-party browser for testing is Dolphin.
Note:
Chrome is a native browser on Android. Do not use it for the comparison.
In iOS, make sure the browsers have device-level VPN support. You can configure VPN on the device by navigating to Settings > VPN > Add VPN Configuration.
You can also use VPN client apps available on the App Store, such as Citrix VPN, Cisco AnyConnect, or Pulse Secure.
- If a webpage renders the same for the two browsers, the issue is with your website. Update your site and make sure it works well for the OS.
- If the issue on a webpage appears only in Secure Web, contact Citrix Support to open a support ticket. Provide your troubleshooting steps, including the tested browser and OS types. If Secure Web for iOS has rendering issues, include a web archive of the page as described in the following steps. Doing so helps Citrix resolve the issue faster.
To create a web archive file
Using Safari on macOS 10.9 or later, you can save a webpage as a web archive file (referred to as a reading list). The web archive file includes all linked files such as images, CSS, and JavaScript.
-
From Safari, empty the Reading List folder: In the Finder, click the Go menu in the Menu bar, choose Go to Folder, type the path name ~/Library/Safari/ReadingListArchives/, and then delete all folders in that location.
-
In the Menu bar, go to Safari > Preferences > Advanced and enable Show Develop menu in menu bar.
-
In the Menu bar, go to Develop > User Agent and enter the Secure Web user agent: (Mozilla/5.0 (iPad; CPU OS 8_3 like macOS) AppleWebKit/600.1.4 (KHTML, like Gecko) Mobile/12F69 Secure Web/ 10.1.0(build 1.4.0) Safari/8536.25).
-
In Safari, open the website you want to save as a reading list (web archive file).
-
In the Menu bar, go to Bookmarks > Add to Reading List. The archiving occurs in the background and can take a few minutes.
-
Locate the archived reading list: In the Menu bar, go to View > Show Reading List Sidebar.
-
Verify the archive file:
- Turn off network connectivity to your Mac.
-
Open the website from the reading list.
The website renders completely.
-
Compress the archive file: In the Finder, click the Go menu in the Menu bar, choose Go to Folder, type the path name ~/Library/Safari/ReadingListArchives/. Now compress the folder that has a random hex string as a file name. You can send this file to Citrix support when you open a support ticket.
Secure Web features
Secure Web uses mobile data exchange technologies to create a dedicated VPN tunnel for users to access internal and external websites and all other websites. This includes sites with sensitive information, in an environment secured by your organization’s policies.
The integration of Secure Web with Secure Mail and Citrix Files offers a seamless user experience within the secure Endpoint Management container. Here are some examples of integration features:
- When users tap Mailto links, a new email message opens in Citrix Secure Mail™ with no additional authentication required.
- In iOS, users can open a link in Secure Web from a native mail app by inserting ctxmobilebrowser:// in front of the URL. For example, to open
example.comfrom a native mail app, use the URL ctxmobilebrowser://example.com. - When users click an intranet link in an email message, Secure Web goes to that site with no additional authentication required.
- Users can upload files to Citrix Files that they download from the web in Secure Web.
Secure Web users can also perform the following actions:
- Block pop-ups.
Note:
Much of Secure Web memory goes into rendering pop-ups, so performance is often improved by blocking pop-ups in Settings.
- Bookmark their favorite sites.
- Download files.
- Save pages offline.
- Auto-save passwords.
- Clear cache/history/cookies.
- Disable cookies and HTML5 local storage.
- Securely share devices with other users.
- Search within the address bar.
- Allow web apps they run with Secure Web to access their location.
- Export and import settings.
- Open files directly in Citrix Files without having to download the files. To enable this feature, add ctx-sf: to the Allowed URLs policy in Endpoint Management.
- In iOS, use 3D Touch actions to open a new tab and access offline pages, favorite sites, and downloads directly from the home screen.
- In iOS, download files of any size and open them in Citrix Files or other apps.
Note:
Putting Secure Web in the background causes the download to stop.
-
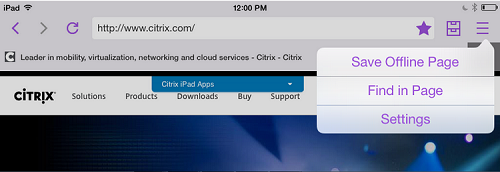
Search for a term within the current page view using Find in Page.
Secure Web also has dynamic text support. The app displays the font that users set on their devices.
Note:
- Citrix Files for XenMobile reached EOL on July 1, 2023. For more information, see EOL and deprecated apps