Citrix Secure Hub™
Citrix Secure Hub is the launchpad for the Citrix Endpoint Management™ (formerly, XenMobile) experience. Users enroll their devices in Secure Hub to gain access to the Store. From the store, they can add Citrix-developed mobile productivity apps and third-party apps.
For Secure Hub and other mobile productivity apps system requirements, see System requirements.
Administering Secure Hub
You perform most of the administration tasks related to Secure Hub during the initial configuration of Endpoint Management. To make Secure Hub available to users, for iOS and Android, upload Secure Hub to the iOS App Store and the Google Play Store.
Secure Hub refreshes most MDX policies stored in the Endpoint Management for the installed apps when a user’s Citrix Gateway session renews after authentication using Citrix Gateway.
Important:
Changes to any of these policies requires the user to delete and reinstall the app to apply the updated policy: Security Group, Enable encryption, and Secure Mail Exchange Server.
Citrix PIN
You can configure Secure Hub to use the Citrix PIN, a security feature enabled in the Endpoint Management console in Settings > Client Properties. The setting requires enrolled mobile device users to sign on to Secure Hub and activate any MDX wrapped apps by using a personal identification number (PIN).
The Citrix PIN feature simplifies the user authentication experience when logging on to the secured wrapped apps. Users don’t have to repeatedly enter another credential like their Active Directory user name and password.
Users who sign on to Secure Hub for the first time must enter their Active Directory user name and password. During sign-on, Secure Hub saves the Active Directory credentials or a client certificate on the user device and then prompts the user to enter a PIN. When users sign on again, they enter the PIN to access their Citrix apps and the Store securely. They don’t use the PIN again until the next idle timeout period ends for the active user session. Related client properties enable you to encrypt secrets using the PIN, specify the passcode type for the PIN, and specify PIN strength and length requirements. For details, see Client properties.
When fingerprint (touch ID) authentication is enabled, users can sign on by using a fingerprint when offline authentication is required because of app inactivity. Users still have to enter a PIN when signing on to Secure Hub for the first time, restarting the device, and after the inactivity timer expires. For information about enabling fingerprint authentication, see Fingerprint or touch ID authentication.
Certificate pinning
Secure Hub for iOS and Android supports SSL certificate pinning. This feature ensures that the certificate signed by your enterprise is used when Citrix clients communicate with Endpoint Management. Certificate pinning prevents connections from clients to Endpoint Management when installation of a root certificate on the device compromises the SSL session. When Secure Hub detects any changes to the server public key, Secure Hub denies the connection.
As of Android N, the operating system no longer allows user-added certificate authorities (CAs). Citrix recommends using a public root CA in place of a user-added certificate authority.
Users upgrading to Android N may experience problems if they use private or self-signed CAs. Connections on Android N devices break under the following scenarios:
- Private/self-signed CAs and the Required Trusted CA for Endpoint Management option in the AutoDiscovery Service is set ON. For details, see Endpoint Management AutoDiscovery Service.
- Private/self-signed CAs and the Endpoint Management AutoDiscovery Service (ADS) are not reachable. Due to security concerns, when ADS is not reachable, Required Trusted CA turns ON even it was set as OFF initially.
Before you enroll devices or upgrade Secure Hub, consider enabling certificate pinning. The option is Off by default. When you enable certificate pinning, users cannot enroll in Endpoint Management with a self-signed certificate. If users try to enroll with a self-signed certificate, they are warned that the certificate is not trusted. Enrollment fails if users do not accept the certificate.
To use certificate pinning, request that Citrix upload certificates to the Citrix ADS server. Open a technical support case using the Citrix Support portal. Then, provide the following information:
- The domain containing the accounts with which users enroll.
- The Endpoint Management fully qualified domain name (FQDN).
- The Endpoint Management instance name. By default, the instance name is
zdmand is case-sensitive. - User ID Type, which can be either UPN or Email. By default, the type is UPN.
- The port used for iOS enrollment if you changed the port number from the default port 8443.
- The port through which Endpoint Management accepts connections if you changed the port number from the default port 443.
- The full URL of your Citrix Gateway.
- Optionally, an email address for your Endpoint Management administrator.
- The PEM-formatted certificates you want added to the domain.
Certificate + one-time-password authentication
You can configure Citrix ADC so that Secure Hub authenticates by using a certificate plus a security token that serves as a one-time password. This configuration provides a strong security option that doesn’t leave an Active Directory footprint on devices.
To enable Secure Hub to use this type of authentication, add a rewrite action and a rewrite policy in Citrix ADC that inserts a custom response header of the form X-Citrix-AM-GatewayAuthType: CertAndRSA to indicate the Citrix Gateway logon type.
Ordinarily, Secure Hub uses the Citrix Gateway logon type configured in the Endpoint Management console. However, this information isn’t available to Secure Hub until Secure Hub completes the logon for the first time. The custom header is required to allow Secure Hub to do this logon method.
Note:
If different logon types are set in Endpoint Management and Citrix ADC, the Citrix ADC configuration overrides the configuration. For details, see Citrix Gateway and Endpoint Management.
-
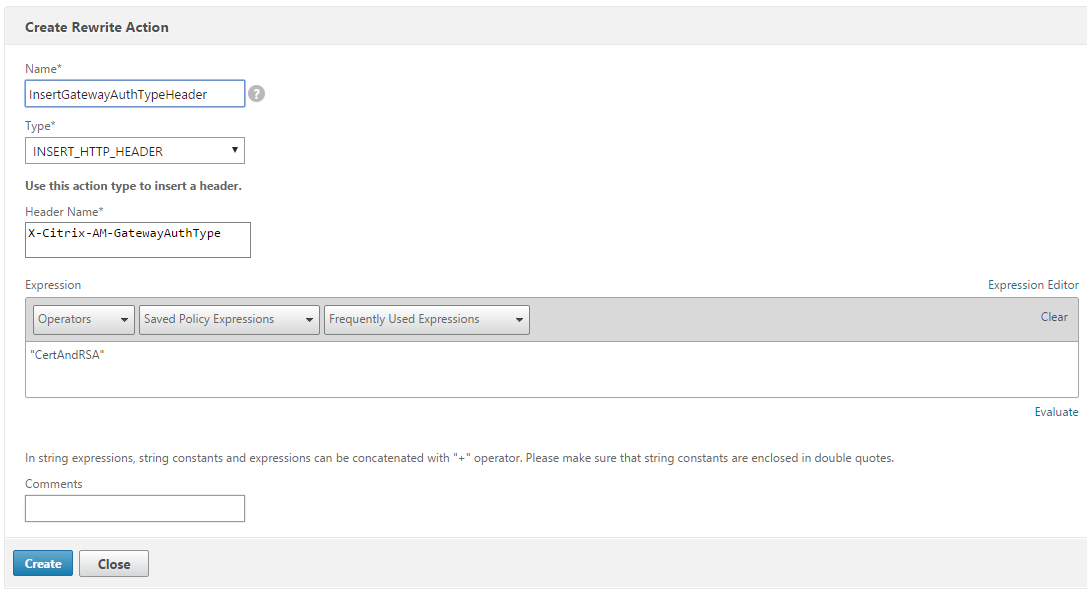
In Citrix ADC, navigate to Configuration > AppExpert > Rewrite > Actions.
-
Click Add.
The Create Rewrite Action screen appears.
-
Fill in each field as shown in the following figure and then click Create.
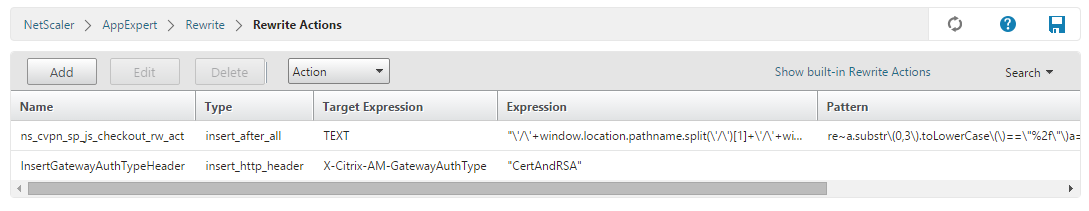
The following result appears on the main Rewrite Actions screen.
-
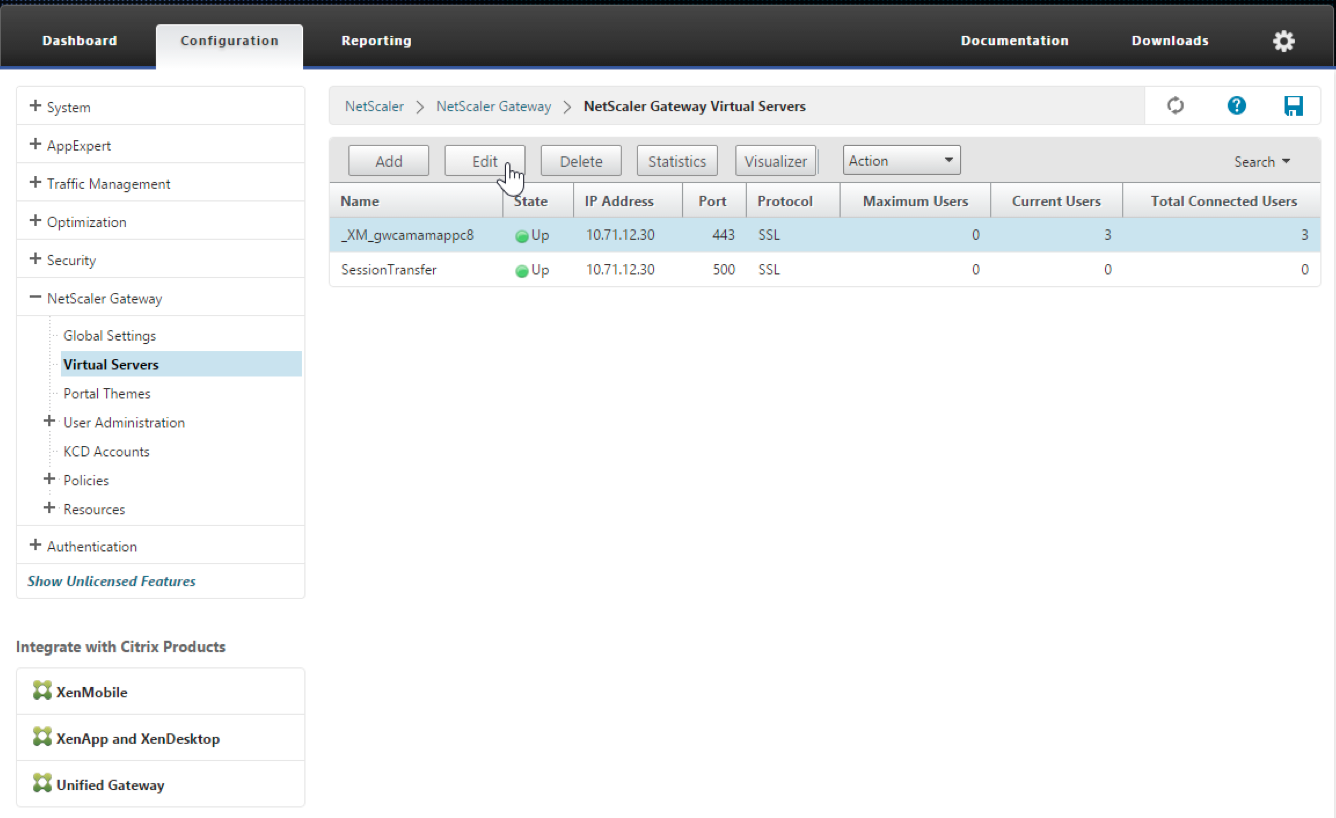
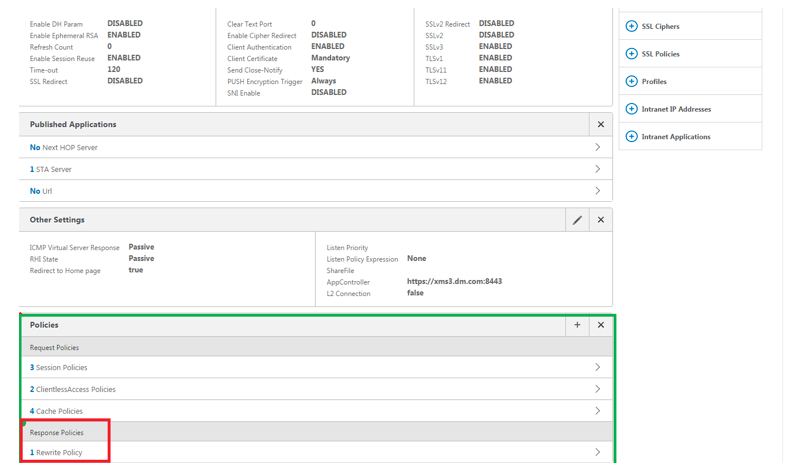
Bind the rewrite action to the virtual server as a rewrite policy. Go to Configuration > NetScaler® Gateway > Virtual Servers and then select your virtual server.
-
Click Edit.
-
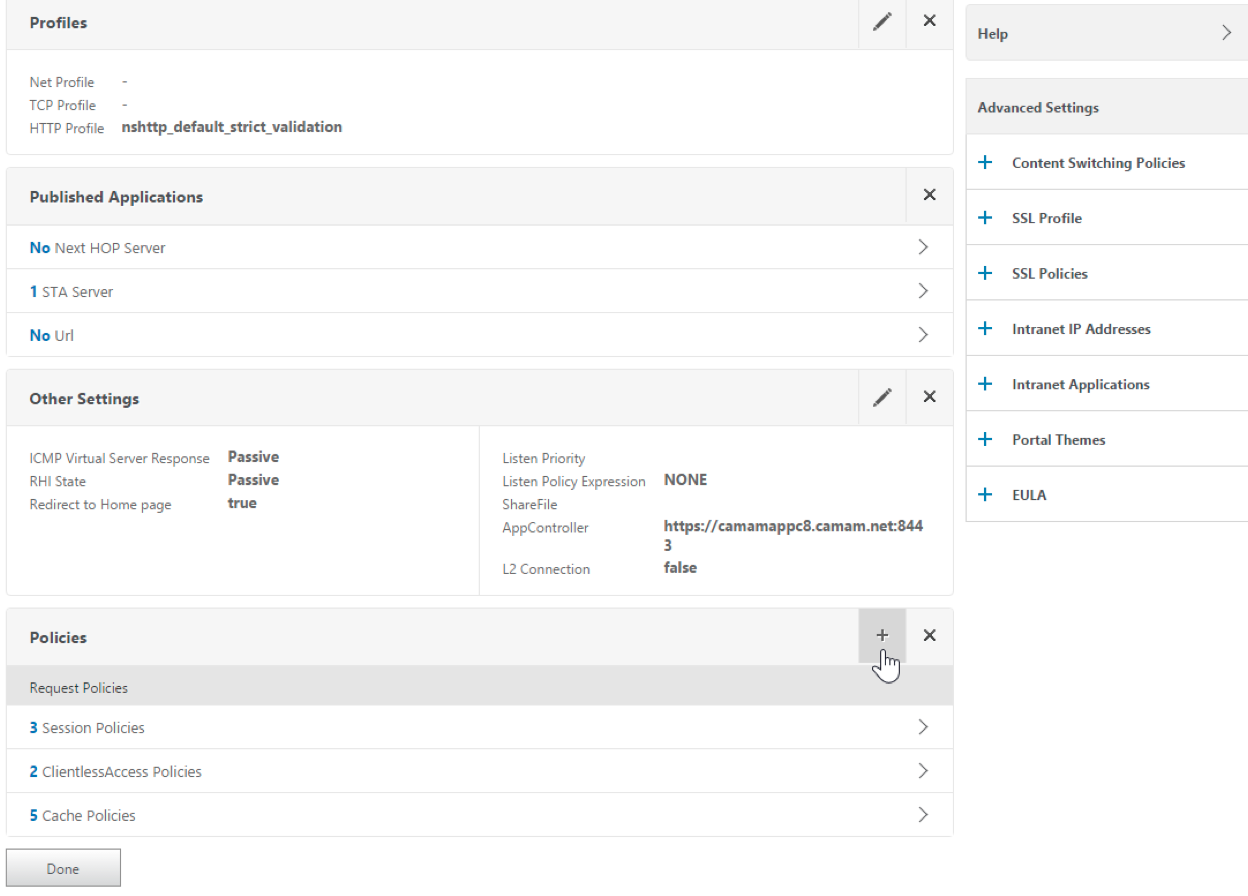
On the Virtual Servers configuration screen, scroll down to Policies.
-
Click + to add a policy.
-
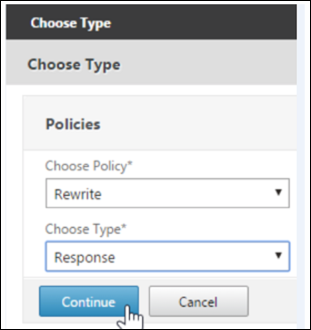
In the Choose Policy field, choose Rewrite.
-
In the Choose Type field, choose Response.
-
Click Continue.
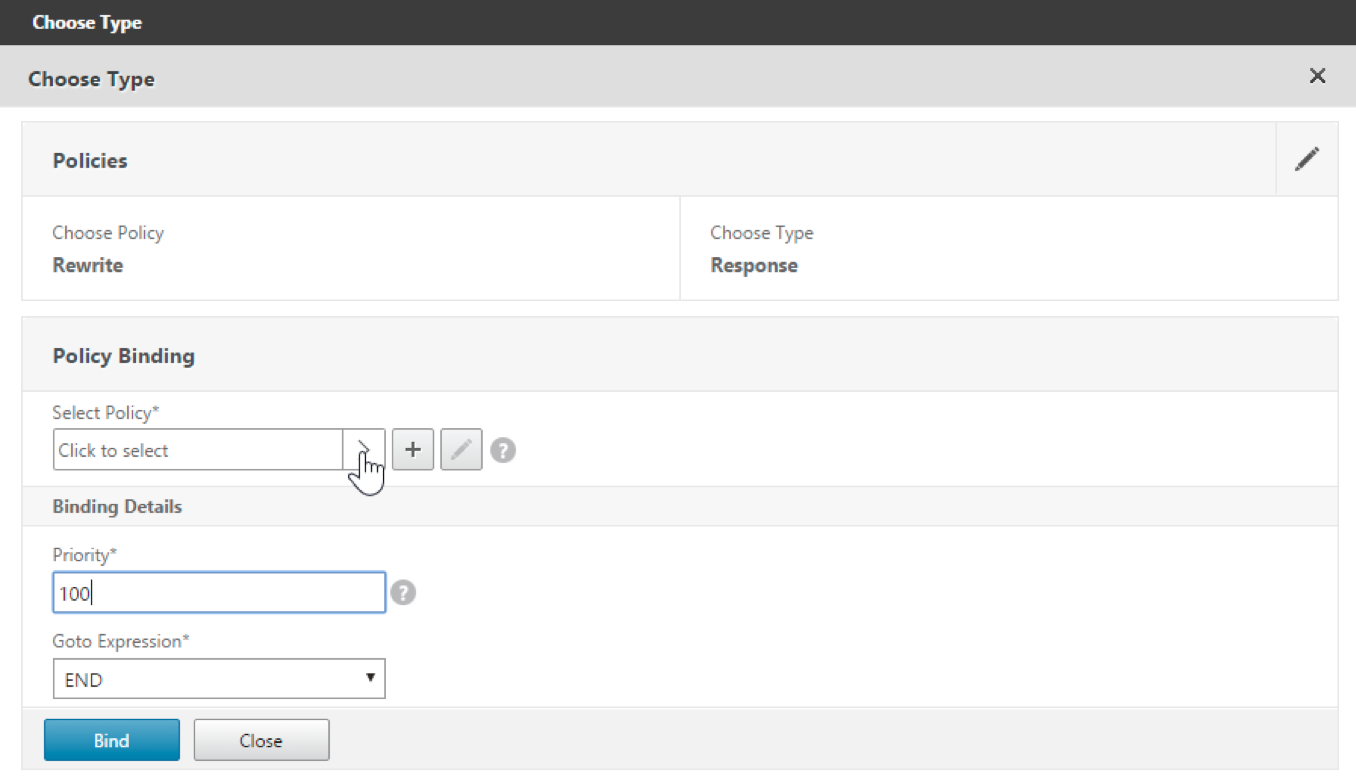
The Policy Binding section expands.
-
Click Select Policy.
A screen with available policies appears.
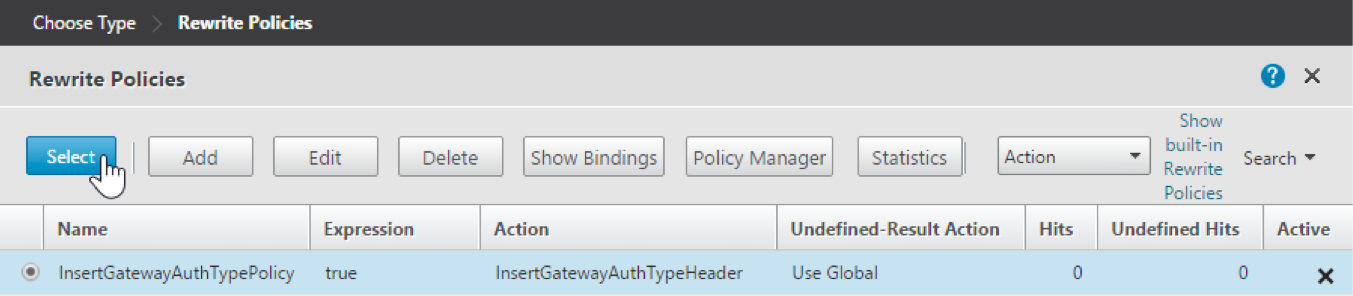
-
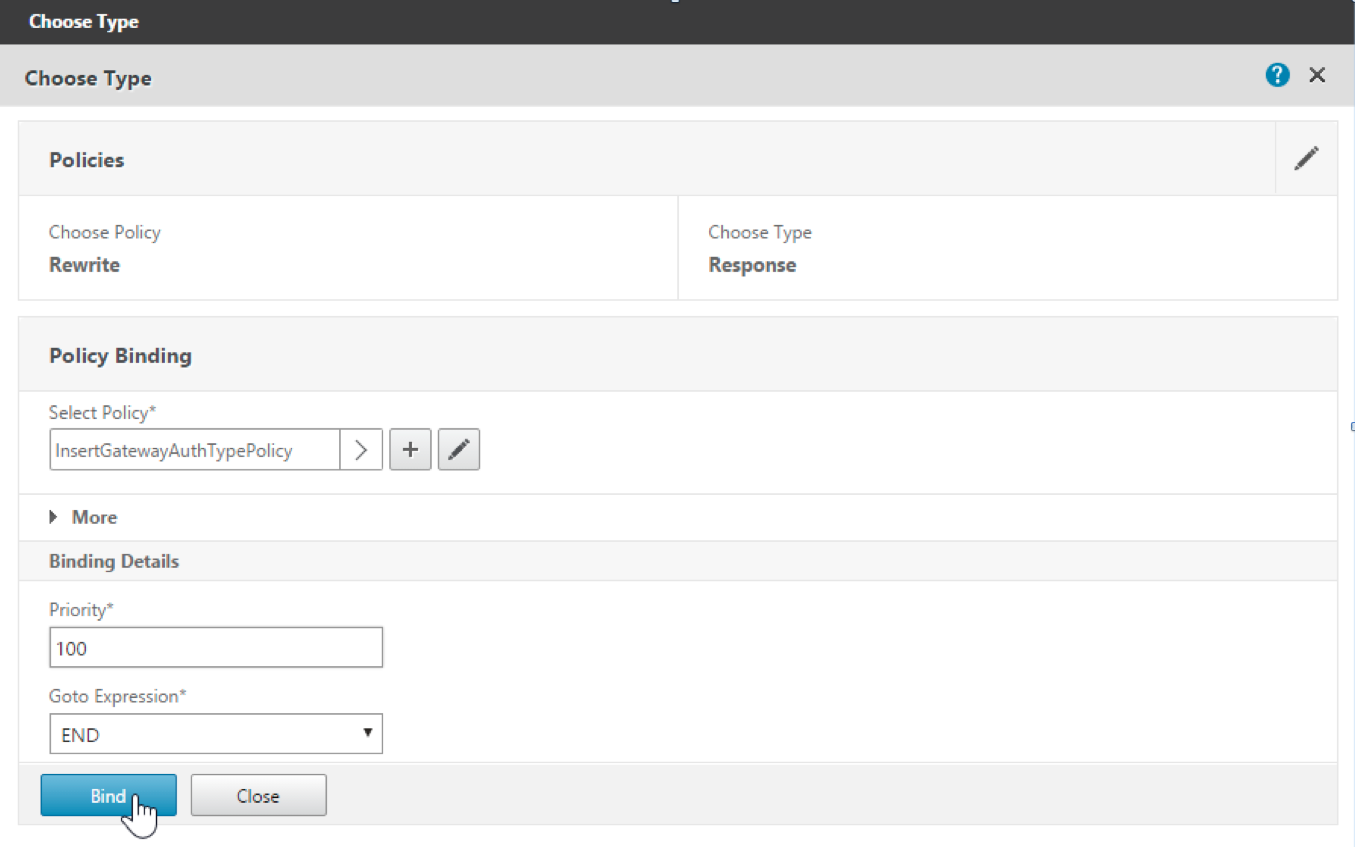
Click the row of the policy you created and then click Select. The Policy Binding screen appears again, with your selected policy filled in.
-
Click Bind.
If the bind is successful, the main configuration screen appears with the completed rewrite policy shown.
-
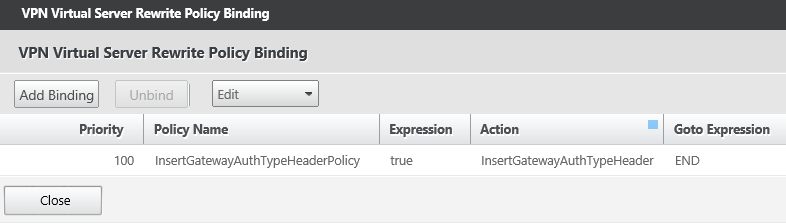
To view the policy details, click Rewrite Policy.
Port requirement for ADS connectivity for Android devices
Port configuration ensures that Android devices connecting from Secure Hub can access the Endpoint Management AutoDiscovery Service (ADS) from within the corporate network. The ability to access ADS is important when downloading security updates made available through ADS. ADS connections might not be compatible with your proxy server. In this scenario, allow the ADS connection to bypass the proxy server.
Important:
Secure Hub for Android and iOS require you to allow Android devices to access ADS. For details, see Port requirements in the Endpoint Management documentation. This communication is on outbound port 443. It’s highly likely that your existing environment is designed to allow this access. Customers who cannot guarantee this communication are discouraged from upgrading to Secure Hub 10.2. If you have any questions, contact Citrix support.
Prerequisites
- Collect Endpoint Management and Citrix ADC certificates. The certificates must be in PEM format and must be a public certificate and not the private key.
- Contact Citrix support and place a request to enable certificate pinning. During this process, you are asked for your certificates.
The new certificate pinning improvements require that devices connect to ADS before the device enrolls. Connecting to ADS first ensures that the latest security information is available to Secure Hub for the environment in which the device is enrolling. If devices cannot reach ADS, Secure Hub does not allow enrollment of the device. Therefore, opening up ADS access within the internal network is critical to enable devices to enroll.
To allow access to the ADS for Secure Hub for Android, open port 443 for the following IP addresses and FQDN:
| FQDN | IP address | Port | IP and port usage |
|---|---|---|---|
discovery.mdm.zenprise.com |
52.5.138.94 | 443 | Secure Hub - ADS Communication |
discovery.mdm.zenprise.com |
52.1.30.122 | 443 | Secure Hub - ADS Communication |
ads.xm.cloud.com: note that Secure Hub version 10.6.15 and later uses ads.xm.cloud.com. |
34.194.83.188 | 443 | Secure Hub - ADS Communication |
ads.xm.cloud.com: note that Secure Hub version 10.6.15 and later uses ads.xm.cloud.com. |
34.193.202.23 | 443 | Secure Hub - ADS Communication |
If certificate pinning is enabled:
- Secure Hub pins your enterprise certificate during device enrollment.
-
During an upgrade, Secure Hub discards any currently pinned certificate and then pins the server certificate on the first connection for enrolled users.
Note:
If you enable certificate pinning after an upgrade, users must enroll again.
- Certificate renewal does not require reenrollment, if the certificate public key did not change.
Certificate pinning supports leaf certificates, not intermediate or issuer certificates. Certificate pinning applies to Citrix servers, such as Endpoint Management and Citrix Gateway, and not third-party servers.
Using Secure Hub
Users begin by downloading Secure Hub onto their devices from the Apple or Android app store.
When Secure Hub opens, users enter the credentials provided by their companies to enroll their devices in Secure Hub. For more details about device enrollment, see Users, accounts, roles, and enrollment.
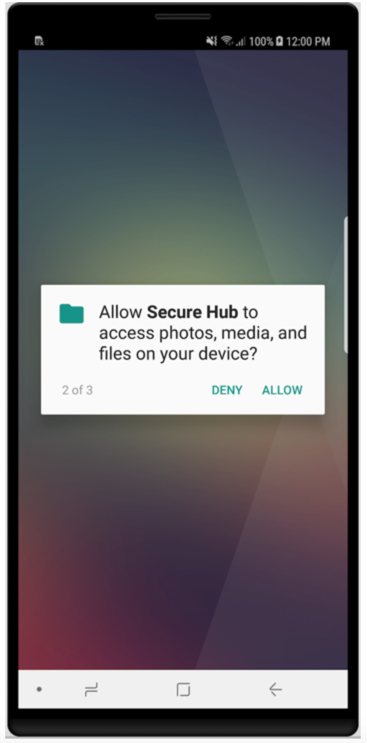
On Secure Hub for Android, during initial installation and enrollment, the following message appears: Allow Secure Hub to access photos, media, and files on your device?
This message comes from the Android operating system and not from Citrix. When you tap Allow, Citrix and the admins who manage Secure Hub do not view your personal data at any time. If however, you conduct a remote support session with your admin, the admin can view your personal files within the session.
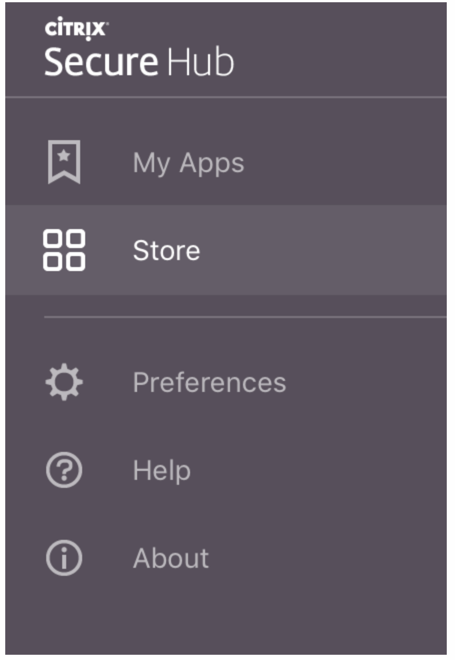
Once enrolled, users see any apps and desktops that you’ve pushed in their My Apps tab. Users can add more apps from the Store. On phones, the Store link is under the Settings hamburger icon in the upper left-hand corner.
On tablets, the Store is a separate tab.
When users with iPhones running iOS 9 or later install mobile productivity apps from the Endpoint Management app store, they see a message. This message states that the enterprise developer, Citrix, is not trusted on that iPhone. The message also states that the app is not available for use until the developer is trusted. When this message appears, Secure Hub prompts users to view a guide that coaches them through the process of trusting Citrix enterprise apps for their iPhone.
Automatic enrollment in Secure Mail
For MAM-only deployments, you can configure CEM so that users who enroll in Secure Hub using email credentials are automatically enrolled in Secure Mail. Users do not have to enter more information or take more steps to enroll in Secure Mail.
On first-time use of Secure Mail, Secure Mail obtains the user’s email address, domain, and user ID from Secure Hub. Secure Mail uses the email address for automatic discovery. The Exchange server is identified using the domain and user ID, which enables Secure Mail to authenticate the user automatically. The user is prompted to enter a password if the policy is set to not pass through the password. Here, the user is not required to enter any more information.
To enable this feature, create three properties:
- The server property MAM_MACRO_SUPPORT. For instructions, see Server properties.
- The client properties ENABLE_CREDENTIAL_STORE and SEND_LDAP_ATTRIBUTES. For instructions, see Client properties.
Customized Store
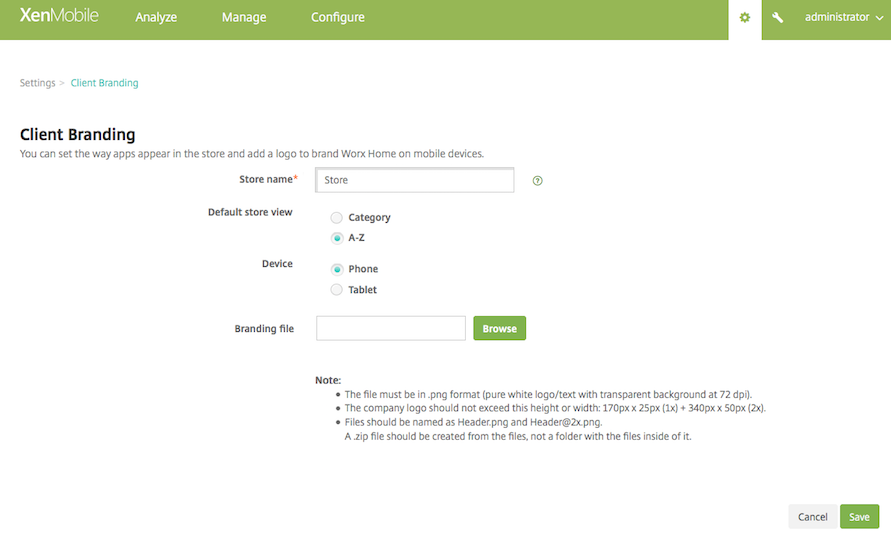
If you want to customize your Store, go to Settings > Client Branding to change the name, add a logo, and specify how apps appear.
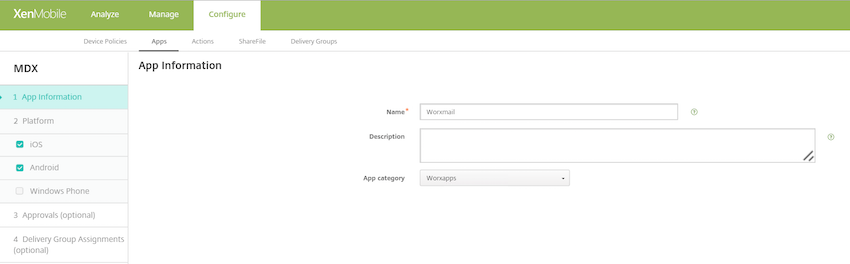
You can edit app descriptions in the Endpoint Management console. Click Configure then click Apps. Select the app from the table and then click Edit. Select the platforms for the app with the description you’re editing and then type the text in the Description box.
In the Store, users can browse only those apps and desktops that you’ve configured and secured in Endpoint Management. To add the app, users tap Details and then tap Add.
Configured Help options
Secure Hub also offers users various ways to get help. On tablets, tapping the question mark in the upper-right corner opens help options. On phones, users tap the hamburger menu icon in the upper-left corner and then tap Help.
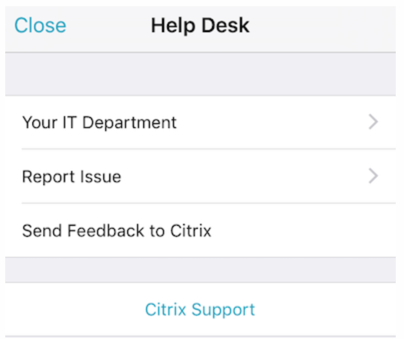
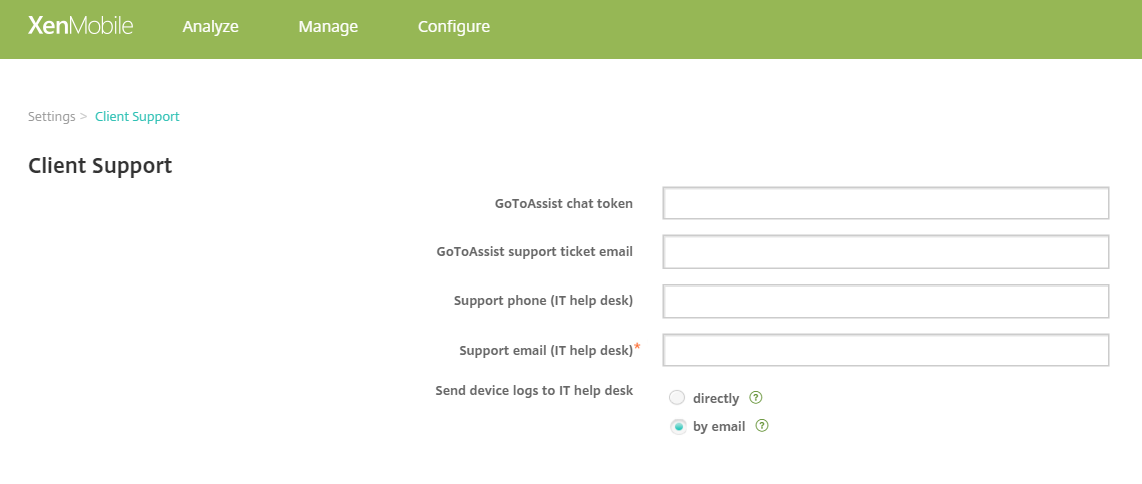
Your IT Department shows the telephone and email of your company help desk, which users can access directly from the app. You enter phone numbers and email addresses in the Endpoint Management console. Click the gear icon in the upper-right corner. The Settings page appears. Click More and then click Client Support. The screen where you enter the information appears.
Report Issue shows a list of apps. Users select the app that has the issue. Secure Hub automatically generates logs and then opens a message in Secure Mail with the logs attached as a zip file. Users add subject lines and descriptions of the issue. They can also attach a screenshot.
Send Feedback to Citrix opens a message in Secure Mail with a Citrix support address filled in. In the body of the message, the user can enter suggestions for improving Secure Mail. If Secure Mail isn’t installed on the device, the native mail program opens.
Users can also tap Citrix Support, which opens the Citrix Knowledge Center. From there, they can search support articles for all Citrix products.
In Preferences, users can find information about their accounts and devices.
Location policies
Secure Hub also provides geo-location and geo-tracking policies if, for example, you want to ensure that a corporate-owned device does not breach a certain geographic perimeter. For details, see Location device policy.
Crash collection and analysis
Secure Hub automatically collects and analyzes failure information so you can see what led to a particular failure. Crashlytics software supports this function.
For more features available for iOS and Android, see the Features by platform matrix for Citrix Secure Hub.