iOS VPN installation
Note:
This article is deprecated. The article describes functionality that we no longer support.
On iOS 10 and later devices, Secure Hub VPN is used for secure local data sharing between Secure Hub and MDX apps. Secure Hub VPN runs on iOS 10 and later devices. Secure Hub VPN provides an ideal user experience because Secure Hub and MDX apps can communicate seamlessly through this VPN.
Secure Hub VPN works for apps signed by Apple Enterprise developer account (“team id”) certificates, Citrix® certificates, Enterprise certificates, or third-party ISV certificates.
Secure Hub VPN is used by default on iOS 10 devices. If Secure Hub VPN is not running on the iOS 10 device, MDX uses the iOS shared keychain for secure data sharing. The iOS shared keychain mechanism requires all participating apps to be signed with the same certificate to access the specific shared keychain for that iOS “team id” certificate. If an app is not signed with the same certificate as the Citrix-signed Secure Hub app, the app might flip to Secure Hub to get the required information.
Secure Hub VPN is available only for Citrix Endpoint Management™ Enterprise and MAM-only deployments. Secure Hub VPN does not apply to Endpoint Management MDM-only environments, and the VPN is not installed in MDM-only enrollments.
Secure Hub VPN is used for communication between Secure Hub and mobile productivity apps. It does not filter or monitor network traffic on the device and is independent of the MDX micro-VPN mechanism.
Note:
Citrix recommends that you leave Secure Hub VPN enabled in environments where it is enabled by default.
Because iOS does not allow more than one VPN client to run on an iOS device simultaneously, however, be aware of the following situation. The Secure Hub VPN cannot be used if another VPN app, such as Cisco AnyConnect or Citrix VPN, needs to run on iOS devices to establish a device-level VPN. You can set up an iOS per-app VPN even if Secure Hub VPN is not disabled. The app using the iOS per-app VPN establishes a per-app VPN connection when the app is in the foreground.
To disable Secure Hub VPN, see the following section in this article. When Secure Hub VPN is disabled, users might experience more flips from a managed app to Secure Hub.
Disabling or reenabling Secure Hub VPN in Endpoint Management
Secure Hub VPN is enabled by default when users start using Secure Hub 10.3.10 and later on iOS 10.
To disable Secure Hub VPN and set iOS devices in your deployment to use the shared keychain mechanism, do the following:
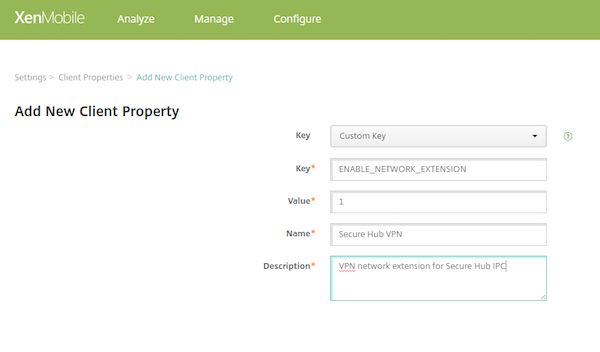
- In the Endpoint Management console, go to Settings > Client > Client Properties.
-
On the Client Properties page, create a custom client property called ENABLE_NETWORK_EXTENSION and set the value to 0.
To reenable Secure Hub VPN, go to the Secure Hub VPN and set the value of ENABLE_NETWORK_EXTENSION to 1.
Installing Secure Hub VPN on the client device
The Secure Hub VPN is installed in two cases: after Secure Hub 10.3.10 or later is installed on an iOS 10 device or when a user upgrades a device running Secure Hub 10.3.10 or later to iOS 10.
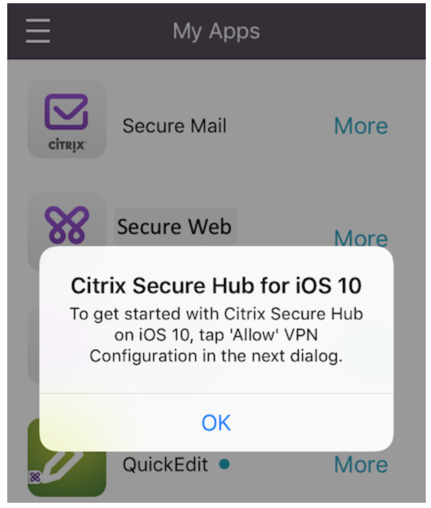
Users see this informational message.
Next, users see an iOS message asking for permission to add VPN configurations. This message is shown only one time, when the VPN is first installed. It is not shown when users open Secure Hub again.
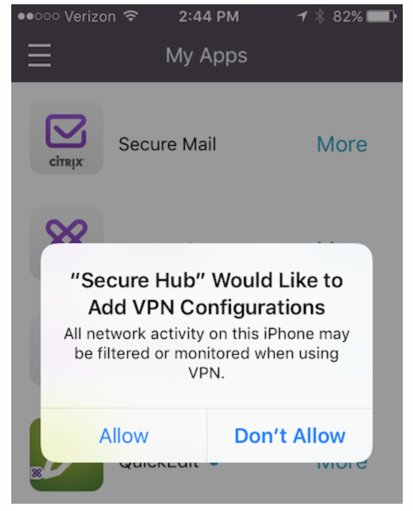
The message on this screen is not customizable. It is a standard iOS dialog box used for all VPN installations.
On the screen asking for permission to add the VPN configuration: If users select Don’t Allow, they see another message indicating that they must install the VPN to access Secure Hub.
Running Secure Hub VPN on the client device
When the Secure Hub VPN is running as designed, the text Connecting appears in the General > VPN screen of the iOS Settings app.
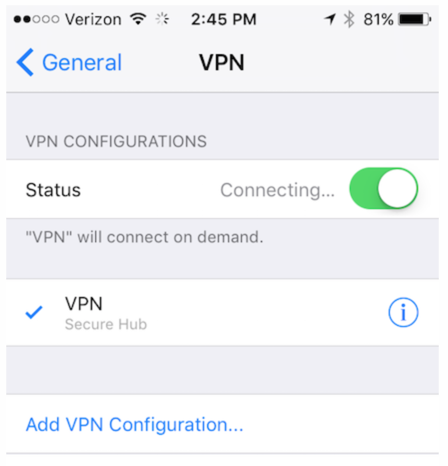
This is expected and does not mean that the MDX sharing and communication mechanisms are not functioning. There is no action required from users if they see this message.