Secure Private Access service
The Secure Private Access™ service provider for hybrid deployment is installed as part of Citrix Cloud Connector. After Citrix Cloud Connector is installed, the Citrix Secure Private Access service can be found in the Windows services. The Secure Private Access service operates under the network service account.
Important:
- Once the Cloud Connector is updated, the Secure Private Access service is disabled. To enable the feature, customers must contact Citrix Support.
- Once enabled, the service status changes to Running, and the Secure Private Access service automatically starts on the connector machine.
Port Configuration for Citrix Secure Private Access service
-
Citrix Secure Private Access uses port 8443 as a plain HTTP service.
-
Ensure that the inbound rule for port 8443 is added to allow access from the data center network. The port 8443 can be opened by manually configuring the firewall rules or by running the Citrix Secure Private Access config tool.
- Navigate to the Citrix Secure Private Access installation folder (default path - C:\Program Files\Citrix\AccessSecurityService).
- Run the command .\Citrix.AccessSecurityService.exe /ENABLE_SPA_PORTS 8443.
After the command is run successfully, the firewall is configured automatically.
- The internal load balancer for Citrix Secure Private Access adds the Cloud Connector back-end service using port 8443.
Secure Private Access load balancer
The load balancer for the Secure Private Access service must be configured with TLS enabled using one of two approaches:
-
SSL offload on the load balancer: The Secure Private Access load balancer communicates with the Secure Private Access service on Cloud Connector over HTTP on port 8443, and the TLS/SSL certificate is installed on the load balancer. Traffic between the load balancer and the Secure Private Access service is plain HTTP and not encrypted. For details, see Configure SSL offloading.
-
SSL bridge: The load balancer forwards encrypted traffic to the Secure Private Access service on Cloud Connector. TLS/SSL certificate must be installed for the Secure Private Access service on each Cloud Connector host. For details, see See Configure SSL bridging.
Configure TLS/SSL certificates for the Secure Private Access service on Cloud Connector
-
Install a valid TLS/SSL certificate on the Cloud Connector’s local machine Personal certificate store. Ensure that the certificate is trusted. Add the issuing CA certificates if necessary.
Note:
Ensure that the TLS/SSL certificate contains Cloud Connector FQDN as part of Subject Alternative Name (SAN).
-
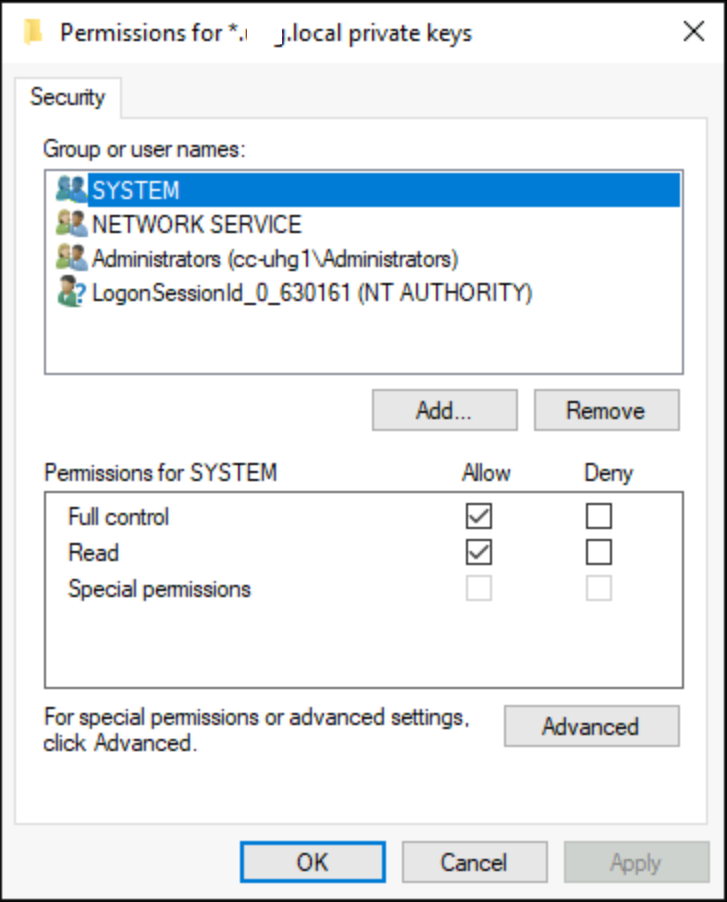
Grant Network Service account permission to access the installed certificate.
- Open the Microsoft Management console and add certificate snap-in to your local computer account, follow the wizard, and click OK.
- In the Microsoft Management Console, go to Console Root > Certificates > Personal > Certificates.
- Right-click the certificate that is required to configure Secure Private Access and select All Tasks > Manage Private Keys.
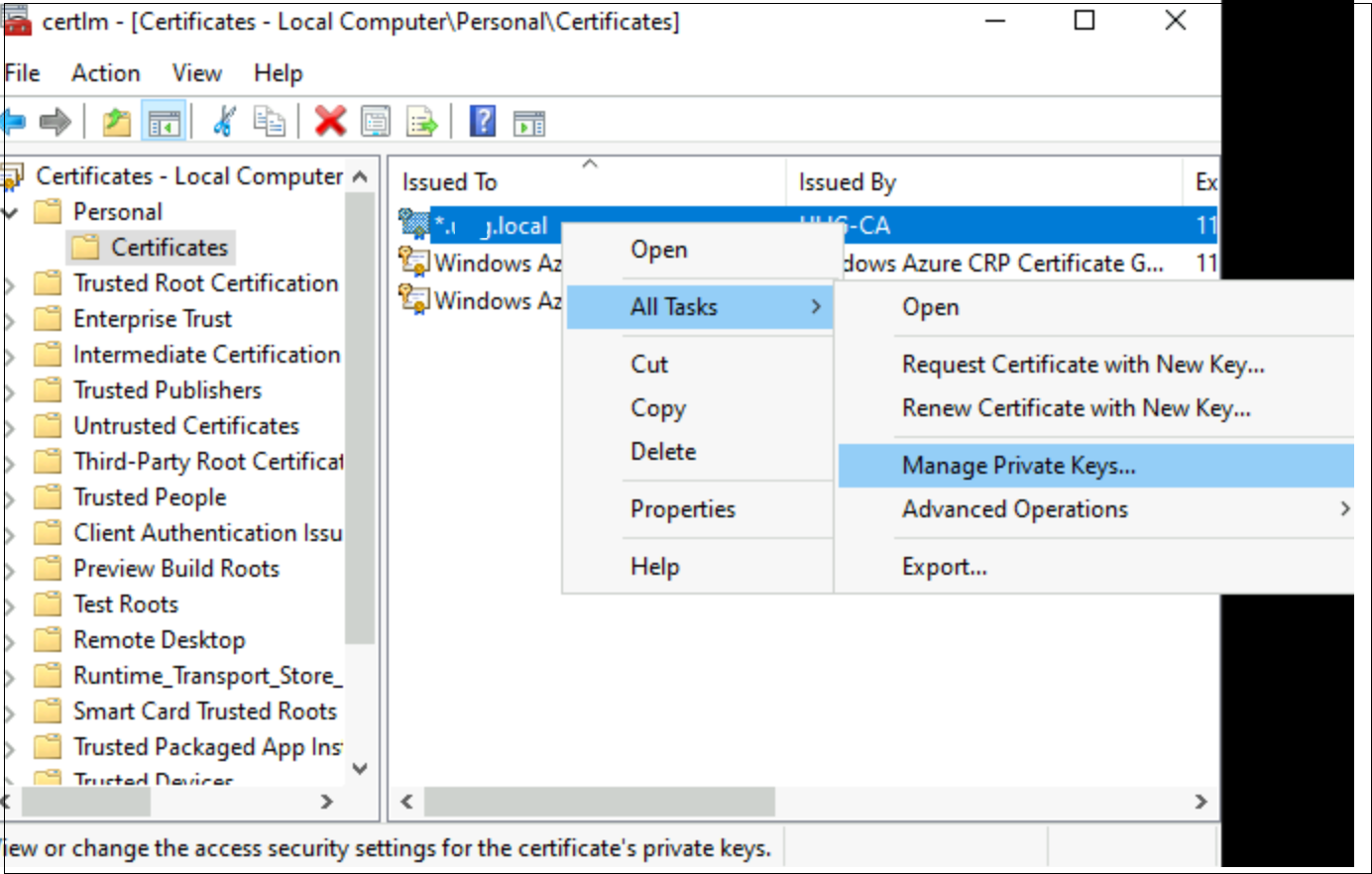
- In the Permissions window, click Add and then search for the Network Service account, and select Read only permission.
-
Configure the Secure Private Access service with TLS/SSL certificate thumbprint.
- Copy the thumbprint from TLS/SSL Certificate Details.
-
Navigate to the Citrix Secure Private Access installation folder (default path - C:\Program Files\Citrix\AccessSecurityService) and run .\Citrix.AccessSecurityService.exe /CERTIFICATE_THUMBPRINT
<ThumbprintValue>. - Restart the Citrix Secure Private Access service.
-
Ensure that the Secure Private Access service is running as a TLS service (use browser or cURL):
https://<Cloud connector address>:<port>/secureAccess/health.Expected result:
response 200 OK with status “Ok”.