What’s new
A goal of Citrix is to deliver new features and product updates to Citrix Analytics customers when they are available. New releases provide more value, so there’s no reason to delay updates.
To you, the customer, this process is transparent. Initial updates are applied to Citrix internal sites only, and are then applied to customer environments gradually. Delivering updates incrementally in waves helps to ensure product quality and to maximize the availability.
Citrix Analytics has the following products or offerings. See the What’s new articles specific to each offering to know about the new features and product updates.
This release notes highlight the new features and product updates specific to the Citrix Analytics platform.
September 21, 2023
Simplify StoreFront™ On-boarding Using PowerShell Script
A new PowerShell script has been introduced that automates the process of checking prerequisites, installing, and configuring StoreFront. The customer must run this script in administrator mode on StoreFront to onboard, deboard, perform self-checks, troubleshoot, and verify whether onboarding to the Citrix Analytics Service GUI is successful.
For more information, see Connect to a StoreFront deployment.
August 28, 2023
Microapps service (End of Life)
Citrix Microapps service has reached its end of life and is no longer available to users.
August 01, 2023
Citrix Analytics - Usage (End of Life)
Citrix Usage Analytics has reached its end of life and is no longer available to users.
February 23, 2023
Fixed issues
Prior to the release of Citrix Virtual Apps and Desktops™ 2112, Citrix Analytics fails to discover the on-premises sites that are connected from Citrix Director and are recently registered on Citrix Cloud. So, you don’t see these connected sites on your Virtual Apps and Desktops- Monitoring site card. This issue is fixed now. [CAS-63132]
September 28, 2022
Webhooks for Alert Notifications
You can use webhooks to send Citrix Analytics alert notifications to any third-party applications that have incoming webhook URLs configured. Webhooks are HTTP callbacks that enable real-time messaging between the service provider applications and consumer applications. Since the alert notifications are sent in real time, you get notified when the events occur. For more information, see Webhooks for Alert Notifications.
September 08, 2022
Export limit in CSV export increased
The limit on the number of rows that you can export using the Export to CSV format feature is now increased from 10K rows to 100K rows. For more information, see Export the events to a CSV file.
August 18, 2022
Fixed issue
- In the Self-Service search for Apps and Desktops, the Workspace app version value was populated as NA (not available) in the downloaded CSV file, while it was available in the page view. This issue is now fixed. [CAS-70361]
August 10, 2022
StoreFront onboarding without site aggregation
The site aggregation dependency for StoreFront has been removed from Apps and Desktops- Workspace app site card. You can see the Connect Storefront Deployment option on your workspace application, even if you do not have any site added to the site aggregation. For more details, refer Citrix Virtual Apps and Desktops data source.
April 05, 2022
Secure Workspace Access is renamed to Secure Private Access
On the Analytics dashboards and reports, all the Secure Workspace Access labels are now updated as Secure Private Access to align with the rebranded product name.
For example, on the Data Sources page and the Self-service search page, the Secure Workspace Access labels are renamed as Secure Private Access.
March 21, 2022
Fixed issue
-
In the Search page, auto-suggestions for dimensions and operators do not work if the previous condition of your search query contains a dimension value that is separated by a space.
For example, in the following query, auto-suggestions stop working after you select the city as
San Jose. This issue is now fixed. [CAS-64126]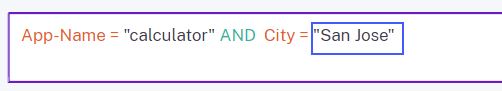
February 10, 2022
What’s new
Auto suggested values for the dimensions in the self-service search box
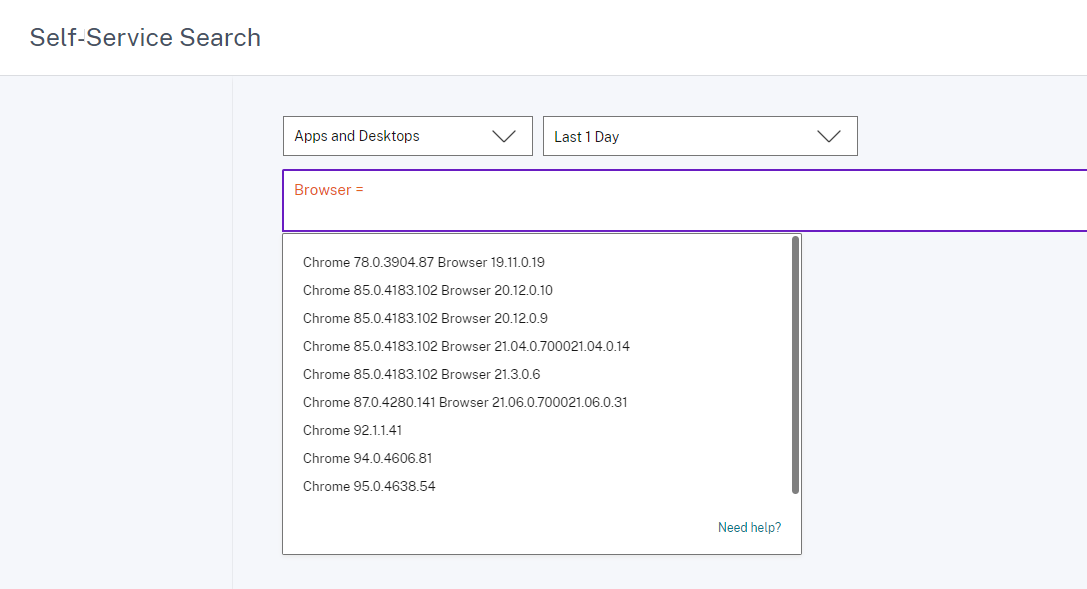
In the self-service search page, when you select a dimension and a valid operator in the search box, the values for the dimension are shown automatically. Select a value from the auto-suggested list or manually enter a value depending on your use cases. When you type a value, the matching values available in the records are auto-suggested.
The list of values suggested for a dimension is either predefined (known values) in the data base or based on historical events.
For example, when you select the dimension Browser and the assignment operator, the known values are auto-suggested. You can select a value depending on your requirement.
For more information, see Self-service search.
December 20, 2021
What’s new
Access Control is renamed to Secure Workspace Access
On the Analytics dashboards and reports, all the Access Control labels are now updated as Secure Workspace Access to align with the rebranded product name.
For example, on the Data Sources page and the Self-service search page, the Access Control labels are renamed as Secure Workspace Access.
December 06, 2021
What’s new
Citrix Analytics is now supported in the Asia Pacific South region
-
You can now choose Asia Pacific South as a home region while onboarding your organization to Citrix Cloud and use the Citrix Analytics service. For more information, see Geographical Considerations.
-
Citrix Analytics now stores the user events and metadata of your organization in the Asia Pacific South region when you choose it as your home region. For more information, see Data governance.
-
For information about the network requirements for the Asia Pacific South region, see Technical security overview.
-
For information about supported data sources in the Asia Pacific South region, see Data sources.
August 19, 2021
What’s new
Support for the IS EMPTY operator
In the self-service search, you can now use the IS EMPTY operator in your condition to check for null or empty dimension.
Note
The operator works for only string-type dimensions such as App-Name, Browser, and Country.
For more information, see Self-service search.
July 14, 2021
What’s new
Support for the IS NOT EMPTY operator
In the self-service search, you can now use the IS NOT EMPTY operator in your query to check if the dimension is not empty (not blank).
Note
The operator works for only string-type dimensions such as App-Name, Browser, and Country.
For more information, see Self-service search.
June 07, 2021
Deprecated feature
Removed Citrix Analytics demo environment
The Try Demo links for Security Analytics and Performance Analytics are now removed from the Analytics overview page. You can no longer access the demo environment for each offering. For more information on how to get access to Citrix Analytics offerings, see Getting started.
May 18, 2021
What’s new
Support for * operator with != operator
In your search query, you can now use the * operator with the != operator to find the user events. For example:
-
To find all the user events that do not begin with the name “John”, use the query: User-Name != John*
-
To find all the user events that do not end with the name “Smith”, use the query: User-Name != *Smith
Note
The search results are case-sensitive.
For more information, see Self-service search.
Enhanced search bar experience in the self-service search page
-
The search bar now provides a better view of your queries when it extends to multiple lines. Use the scroll bar to scroll your multi-line queries. Previously, it was difficult to view the multi-line queries.
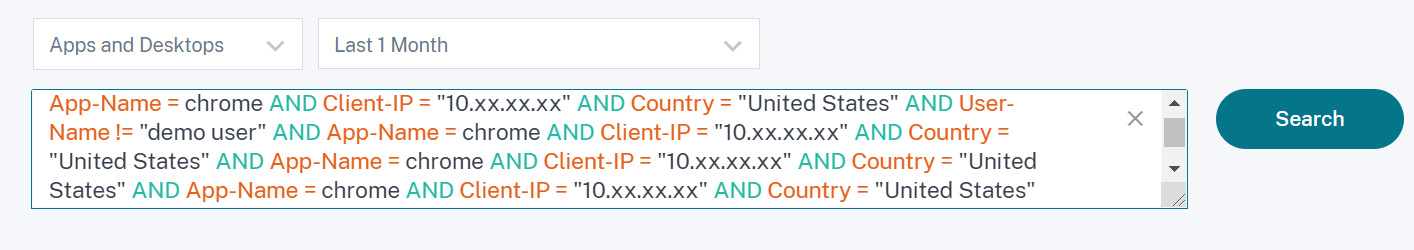
-
The cursor jumping issue that was observed in the Safari browser is now fixed.
For more information, see Self-service search.
Redesigned chips view in self-service search
-
The redesigned chips now provide you a better view of the multiple facets that you have selected.
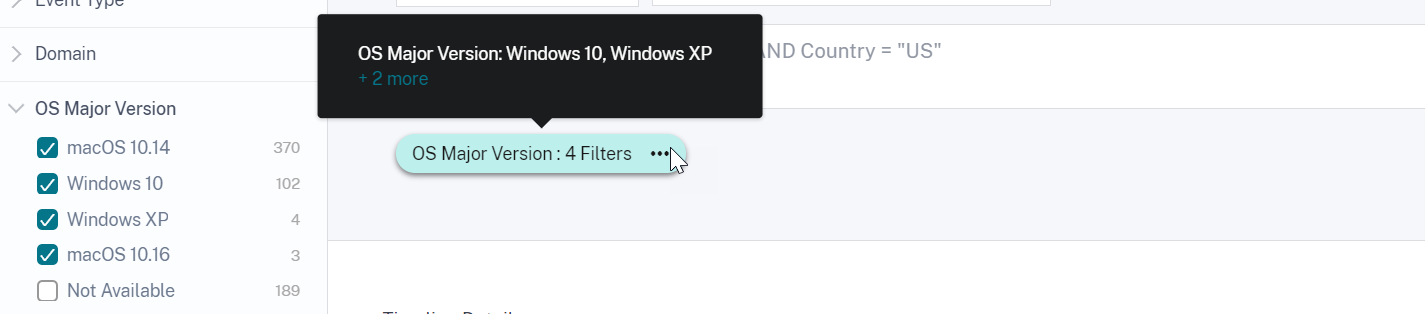
-
Click a chip to select or deselect the facets based on your requirements.
Fixed issue
- On Citrix Director, the Go to Analytics link is not working. This issue is observed for a user who has onboarded their organization in the European Union region of Citrix Cloud. [CAS-50224]
March 31, 2021
Support for the IN and NOT IN operators for Apps and Desktops search query
With the Apps and Desktops dimensions- Device ID, Domain, Event-Type, and User-Name, you can now use the following operators:
-
IN: Assign multiple values to a dimension to get the events related to one or more values.
-
NOT IN: Assign multiple values to a dimension and find the events that do not contain the specified values.
Note
These operators are applicable only for the string values.
For more information about the operators, see Self-service search.
March 18, 2021
What’s new
Support for the NOT LIKE (!~) operator
For the self-service search query, you can now use the NOT LIKE (!~) operator. The operator checks for the user events for the matching pattern that you have specified. It returns the events that do not contain the specified pattern anywhere in the event string.
For example, the query User-Name !~ “John” displays events for the users except John, John Smith, or any such users that contain the matching name “John”.
For more information, see Self-service search.
February 23, 2021
What’s new
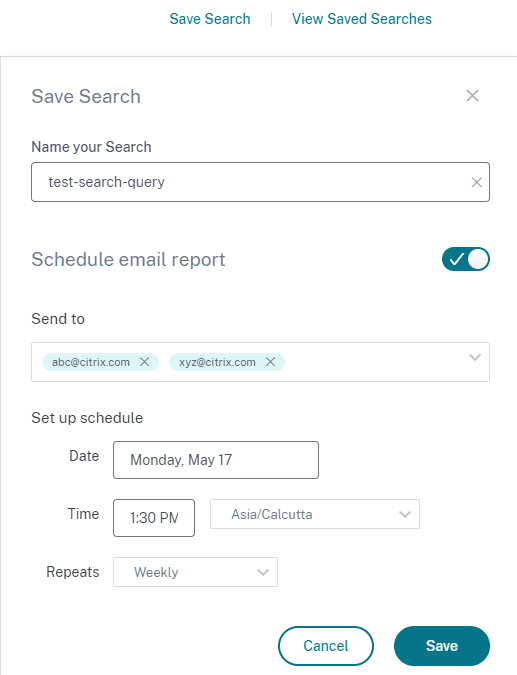
Schedule email delivery for a search query
On the self-service search page, while saving a search query, you can also schedule an email delivery to send a copy of the saved search query and the corresponding visual summary report to yourself and other users. Set the date, time, and frequency-daily, weekly, or monthly to start sending an email. You can also schedule email delivery of the search queries that you previously saved.
For more information, see Self-service search.
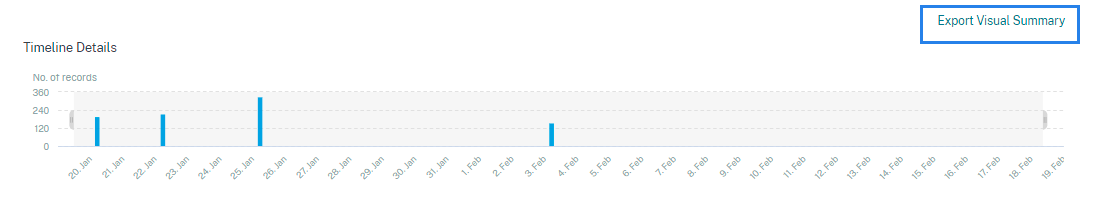
Download visual summary of a search query
On the self-service page, you can now download the visual summary report of your search query for a selected time period and share a copy with other users. Click Export Visual Summary to download the visual summary report as a PDF.
The report contains the following information:
-
The search query that you have specified for the events.
-
The facets (filters) that you have applied on the events.
-
The visual summary such as the timeline charts, bar charts, or graphs of the search events.
For more information, see Self-service search.
November 12, 2020
New feature
Save a self-service query
After you create a self-service query, you can save it for later use. The following options are saved with the query:
- Applied search filters
- Selected data source and duration
For more information, see How to save the self-service search.
October 20, 2020
New features
Support for Citrix Gateway in the European Union region
Citrix Analytics now supports Citrix Gateway in the EU region. For more information, see Citrix Gateway data source.
July 09, 2020
Deprecated support
Microsoft Internet Explorer 11 is now removed from the supported browsers list. This deprecation is because of the security vulnerability observed in the browser. For the list of supported browsers, see System requirements.
June 02, 2020
New features
Redesigned overview page and top bar in Analytics
The Analytics overview page displays the Usage tile that replaces the previously existed Operations tile. Also, the Productivity tile is removed from this page. To view the overview page, select Help > Overview.
Similarly, on the top bar, the Usage tab replaces the Operations tab.

February 20, 2020
New features
Citrix Analytics subscription offerings
Delivering flexible purchase options to users, Citrix now offers three individual subscription-based Citrix Analytics products. Citrix Analytics provides unique security or performance (or both) insights based on the offering that you subscribe to.
You can purchase the following Citrix Analytics subscription offerings:
- Citrix Analytics for Security
- Citrix Analytics for Performance
- Citrix Analytics for Security™ and Performance (bundle)
Data governance logs updates
Added new logs for the following data sources:
- Citrix Identity Provider
- Citrix Gateway
- Secure Browser
- Microsoft Graph Security
- Microsoft Active Directory
For more information, see Data governance.
Fixed issues
- Self-service search does not work accurately on Internet Explorer 11. Therefore, you cannot type your search query and perform a search operation. [CAS-18657]
January 09, 2020
Fixed issues
- The Citrix Analytics walk-through functionality is not working for the users in the European Union home region. [CAS-26297]
December 18, 2019
Fixed issues
The Analytics tile on the Citrix Cloud page displayed the View Service button. This button is now changed to Manage for better user experience. [CAS-27922]
December 12, 2019
New features
Support for Microapps service events in Asia Pacific South
Citrix Analytics platform now processes notifications from the Microapps service in the Asia Pacific South region. However, records that measure performance, stability, usage, security, and support are aggregated and stored in the United States. For more information, see Data governance.
Note
Microapps service is offered as part of Citrix Workspace. For more information, see Microapps documentation.
December 04, 2019
Fixed issues
Some users in the Asia Pacific-South region are unable to sign in to Citrix Analytics although they have onboarded to Citrix Cloud by selecting United States as the home region. [CAS-27368]
November 22, 2019
New features
Redesigned overview page for Analytics
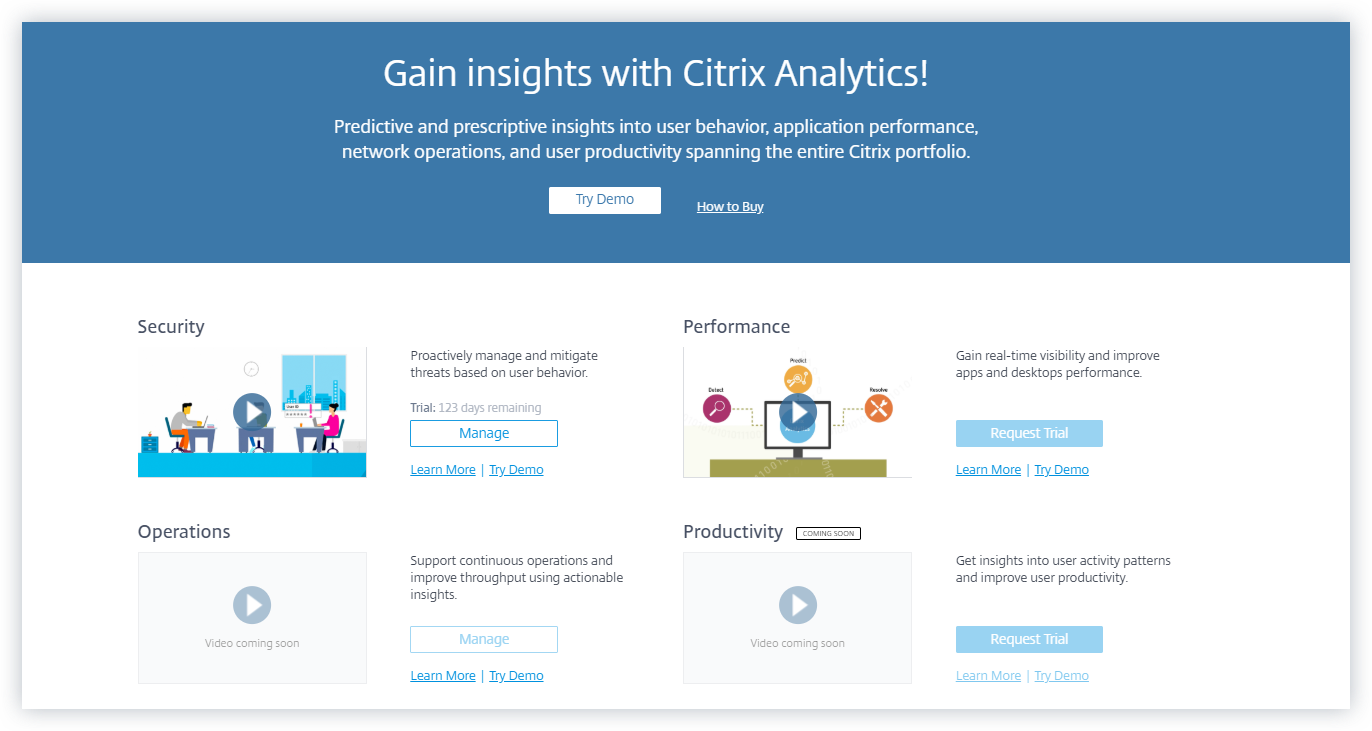
The Analytics overview page is redesigned to allow access to all the Analytics offerings from this page. You can request for a trial, try the demo, or manage your Analytics offering. Currently, only Security Analytics and Operations Analytics are generally available and therefore, active on this page.
To view the overview page, select Help > Overview.
October 21, 2019
New features
Technical security overview
The technical security overview provides you an understanding of the security best practices related to Citrix Analytics. This document describes the data flow, data protection, network requirements, and the security responsibilities that need to be considered when using Citrix Analytics.
September 11, 2019
Fixed issues
- Citrix Cloud is unable to redirect users to the region-specific Citrix Analytics page. [CAS-20559]
August 20, 2019
Fixed issues
- The Citrix Analytics walkthrough functionality does not load accurately on the Microsoft Edge and Safari browsers. [CAS-20906]
July 31, 2019
New features
Support for the European Union region
Citrix Analytics now supports the European Union region. You can choose European Union as a home region while onboarding your organization to Citrix Cloud and use the Citrix Analytics service. Citrix Analytics stores the user events and metadata for your organization in the European Union region. For more information on Citrix Cloud regions, see Geographical Considerations.
June 26, 2019
Fixed issues
- Citrix Analytics does not load accurately on Internet Explorer 11. [CAS-19867]
June 19, 2019
Fixed issues
- Citrix Analytics does not load accurately on Microsoft Edge. [CAS-19930]
November 16, 2018
Fixed issues
- If you are accessing Citrix Analytics using Internet Explorer version 11.0, the Citrix Cloud navigation bar fails to load and restricts you from accessing the hamburger menu.
October 10, 2018
Architecture and platform enhancements
Multiple architectural and platform improvements were done in this release to enhance performance, scale, monitoring, supportability, security, and user experience.
August 23, 2018
Citrix Analytics is a cloud service delivered through Citrix Cloud. It collects data across Citrix portfolio products and provides actionable insights, enabling administrators to proactively handle security threats, improve app performance, and support continuous operations. Currently, Citrix Analytics provides the following analytics offerings:
-
Security Analytics: Collates and provides visibility into user and entity behavior. For more information, see Security Analytics.
-
Operations Analytics: Collates and presents information on the activities of users, such as, websites visited, and the bandwidth spent. For more information, see Operations Analytics.
New product names
The Citrix products supported by Citrix Analytics are now renamed as part of the Citrix unified product portfolio.
You might notice new names in our products and product documentation. This rebranding is a result of the expansion of the Citrix portfolio and cloud strategy. For more details about the Citrix unified portfolio, see Citrix product guide. Implementing this transition in our products and their documentation is an ongoing process.
-
In-product content and documentation might still contain former names. For example, you might see instances of earlier names in console text, messages, directory/file names, screenshots, and diagrams.
-
It is possible that some items (such as commands) might continue to retain their former names to prevent breaking existing customer scripts.
-
Related product documentation and other resources (such as videos and blog posts) that are linked from this product’s documentation might still contain former names.
In this article
- September 21, 2023
- August 28, 2023
- August 01, 2023
- February 23, 2023
- September 28, 2022
- September 08, 2022
- August 18, 2022
- August 10, 2022
- April 05, 2022
- March 21, 2022
- February 10, 2022
- December 20, 2021
- December 06, 2021
- August 19, 2021
- July 14, 2021
- June 07, 2021
- May 18, 2021
- March 31, 2021
- March 18, 2021
- February 23, 2021
- November 12, 2020
- October 20, 2020
- July 09, 2020
- June 02, 2020
- February 20, 2020
- January 09, 2020
- December 18, 2019
- December 12, 2019
- December 04, 2019
- November 22, 2019
- October 21, 2019
- September 11, 2019
- August 20, 2019
- July 31, 2019
- June 26, 2019
- June 19, 2019
- November 16, 2018
- October 10, 2018
- August 23, 2018