-
-
-
-
-
-
uberAgent Log Collector Splunk App
-
Quickstart
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
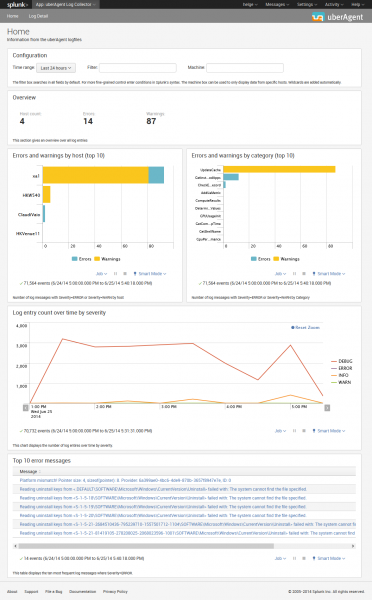
uberAgent® Log Collector Splunk App
uberAgent maintains a very detailed and informative log file that can tell you a lot not only about uberAgent’s health but also about the machine uberAgent is running on. Naturally, the log file is stored locally on the computer uberAgent is running on which makes analysis and troubleshooting a bit difficult in large environments. But luckily it is very easy to solve that problem with Splunk!
What is it
uberAgent Log Collector is a set of associated Splunk apps that collect the data logged by uberAgent, send it to Splunk for indexing and provide dashboards for easy access.
Installation
uberAgent Log Collector consists of the Splunk app containing the dashboards and a technology add-on (TA) for collecting the data with Splunk’s Universal Forwarder. These two components need to be installed on the following systems:
- App: search head(s)
- TA: endpoints where uberAgent and the Splunk Universal Forwarder are deployed
Splunk Index
You need to create the Splunk index ua_meta_log that stores the logs.
To add the new index ua_meta_log with the CLI run splunk add index ua_meta_log. The full documentation on creating Splunk indexes is available in the Splunk docs.
Configuration
Configurable Log Path
Since uberAgent 7.3, the log path is configurable. If you set a custom log path, you have to modify the TA app: copy the default/inputs.conf to local/inputs.conf and adjust the paths accordingly.
System Requirements
The TA requires Splunk’s Universal Forwarder to be installed on the same machine.
Download
The uberAgent Log Collector apps are available in the Splunk App Directory:
- Download uberAgent Log Collector app
- Download uberAgent Log Collector TA
Share
Share
In this article
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.