Secure communications
To secure the communication between your Site and Citrix Workspace app for Mac, you can integrate your connections with a range of security technologies, including Citrix Gateway. For information about configuring Citrix Gateway with Citrix StoreFront, see StoreFront documentation.
Note:
Citrix recommends using Citrix Gateway to secure communications between StoreFront servers and users’ devices.
- A SOCKS proxy server or secure proxy server (also known as security proxy server, HTTPS proxy server). You can use proxy servers to limit access to and from your network and to handle connections between Citrix Workspace and servers. Citrix Workspace app for Mac supports SOCKS and secure proxy protocols.
- Citrix Secure Web Gateway. You can use Citrix Secure Web Gateway to provide a single, secure, encrypted point of access through the internet to servers on internal corporate networks.
- SSL Relay solutions with Transport Layer Security (TLS) protocols
- A firewall. Network firewalls can allow or block packets based on the destination address and port. If you use a firewall that maps the server’s internal IP address to an external internet address such as network address translation (NAT), configure the external address.
Note:
Starting with macOS Catalina, Apple has enforced extra requirements for root CA certificates and intermediate certificates which administrators must configure. For more information, see Apple Support article HT210176.
Citrix Gateway
To enable remote users to connect to your XenMobile deployment through Citrix Gateway, you can configure Citrix Gateway to support StoreFront. The method for enabling access depends on the edition of XenMobile in your deployment.
If you deploy XenMobile in your network, allow connections from internal or remote users to StoreFront through Citrix Gateway, by integrating Citrix Gateway with StoreFront. This deployment allows users to connect to StoreFront to access published applications from XenApp and virtual desktops from XenDesktop. Users connect through Citrix Workspace app for Mac.
Connecting with the Citrix Secure Web™ Gateway
If the Citrix Secure Web Gateway Proxy is installed on a server in the secure network, you can use the Citrix Secure Web Gateway Proxy in Relay mode. For more information about Relay mode, see XenApp and Citrix Secure Web Gateway documentation.
If you’re using Relay mode, the Citrix Secure Web Gateway server functions as a proxy and you must configure Citrix Workspace app for Mac to use:
- The fully qualified domain name (FQDN) of the Citrix Secure Web Gateway server.
- The port number of the Citrix Secure Web Gateway server. Citrix Secure Web Gateway Version 2.0 does not support Relay mode.
The FQDN must list, in sequence, the following three components:
- Host name
- Intermediate domain
- Top-level domain
For example, my_computer.example.com is an FQDN, because it lists, in sequence, a host name (my_computer), an intermediate domain (example), and a top-level domain (com). The combination of intermediate and top-level domain (example.com) is referred to as the domain name.
Connecting through a proxy server
Proxy servers are used to limit access to and from your network, and to handle connections between Citrix Workspace app for Mac and servers. Citrix Workspace app for Mac supports both SOCKS and secure proxy protocols.
When the Citrix Workspace app for Mac communicates with the Web server, it uses the proxy server settings configured for the default web browser on the user device. Configure the proxy server settings for the default Web browser on the user device accordingly.
Provision to manage multiple proxy servers using PAC files
Starting with the version 2405, you can use multiple proxy servers that allow the HDX sessions to select appropriate proxy servers for accessing specific resources. This selection is based on the proxy rules configured in the Proxy Auto‑Configuration (PAC) file. Using this file, you can manage the network by mentioning which network traffic must be sent through a proxy server and which must be sent directly. Additionally, the PAC URL supports both http:// and file:// protocols.
Connecting through a firewall
Network firewalls can allow or block packets based on the destination address and port. Citrix Workspace app for Mac must be able to communicate through the firewall with both the Web server and Citrix server. The firewall must permit HTTP traffic (often over the standard HTTP port 80 or 443 for a secure Web server) for user device to Web server communication. For Citrix Workspace to Citrix server communication, the firewall must permit inbound ICA traffic on ports 1494 and 2598.
TLS
Transport Layer Security (TLS) is the latest, standardized version of the TLS protocol. The Internet Engineering Taskforce (IETF) renamed it TLS when it took over responsibility for the development of TLS as an open standard.
TLS secures data communications by providing server authentication, encryption of the data stream, and message integrity checks. Some organizations, including U.S. government organizations, require the use of TLS to secure data communications. These organizations might also require the use of validated cryptography, such as Federal Information Processing Standard (FIPS) 140. FIPS 140 is a standard for cryptography.
Citrix Workspace app for Mac supports RSA keys of 1024, 2048, and 3072-bit lengths. Root certificates with RSA keys of 4096-bit length are also supported.
Note:
Citrix Workspace app for Mac uses platform (OS X) crypto for connections between Citrix Workspace app for Mac and StoreFront.
The following cipher suites are deprecated for enhanced security:
- Cipher suites with prefix “TLS_RSA_*”
- Cipher suites RC4 and 3DES
- TLS_RSA_WITH_AES_256_GCM_SHA384 (0x009d)
- TLS_RSA_WITH_AES_128_GCM_SHA256 (0x009c)
- TLS_RSA_WITH_AES_256_CBC_SHA256 (0x003d)
- TLS_RSA_WITH_AES_256_CBC_SHA (0x0035)
- TLS_RSA_WITH_AES_128_CBC_SHA (0x002f)
- TLS_RSA_WITH_RC4_128_SHA (0x0005)
- TLS_RSA_WITH_3DES_EDE_CBC_SHA (0x000a)
Citrix Workspace app for Mac supports only the following cipher suites:
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (0xc030)
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (0xc028)
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (0xc013)
For DTLS 1.0 users, Citrix Workspace app for Mac 1910 and later supports only the following cipher suite:
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (0xc013)
Upgrade your Citrix Gateway version to 12.1 or later if you want to use DTLS 1.0. Otherwise, it falls back to TLS based on the DDC policy.
The following matrices provide details of internal and external network connections:
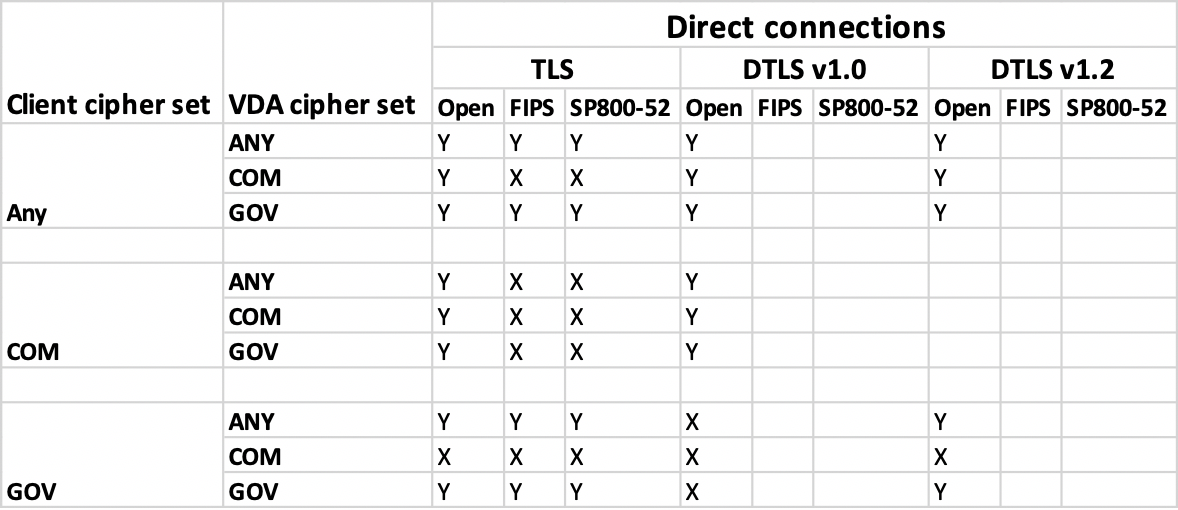
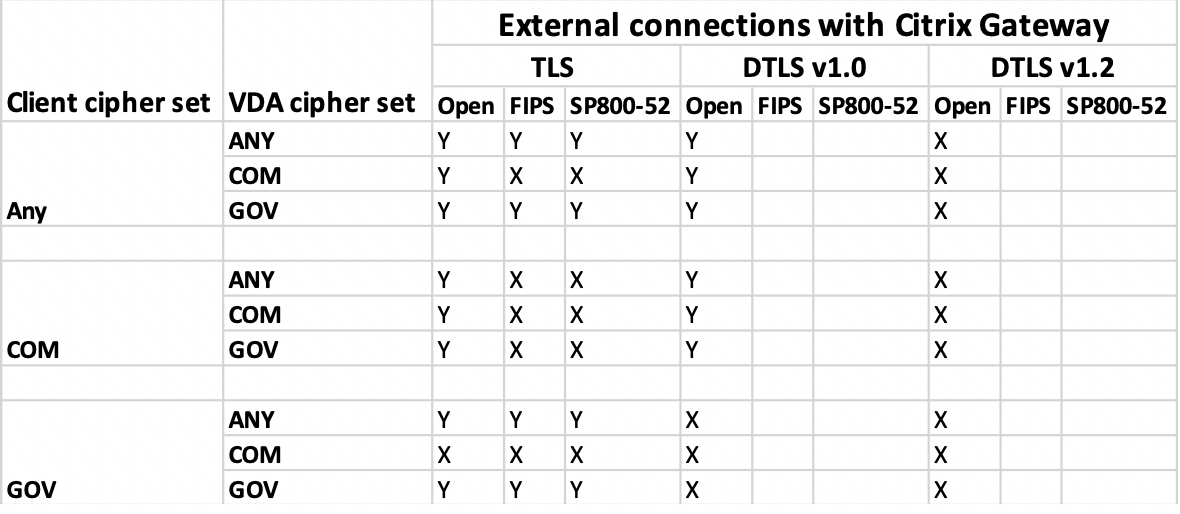
Note:
- Use Citrix Gateway 12.1 or later for EDT to work properly. Older versions do not support ECDHE cipher suites in DTLS mode.
- Citrix Gateway doesn’t support DTLS 1.2. So,
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384andTLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384aren’t supported. Citrix Gateway must be configured to useTLS_ECDHE_RSA_WITH_AES_128_CBC_SHAto work properly in DTLS 1.0.
Configuring and enabling Citrix Workspace app for TLS
There are two main steps involved in setting up TLS:
-
Set up SSL Relay on your Citrix Virtual Apps and Desktops™ and Citrix DaaS (formerly Citrix Virtual Apps and Desktops service) server. Then, obtain and install the necessary server certificate.
-
Install the equivalent root certificate on the user device.
Installing root certificates on user devices
To use TLS to secure communications between TLS-enabled Citrix Workspace app for Mac and the server farm, you need a root certificate on the user device. This root certificate verifies the signature of the Certificate Authority on the server certificate.
macOS X comes with about 100 commercial root certificates already installed. However, if you want to use another certificate, you can obtain one from the Certificate Authority and install it on each user device.
Install the root certificate on each device, depending on your organization’s policies and procedures, instead of prompting users to install it. The easiest and safest way is to add root certificates to the macOS X keychain.
To add a root certificate to the keychain
- Double-click the file containing the certificate. This action automatically starts the Keychain Access application.
- In the Add Certificates dialog box, choose one of the following from the Keychain pop-up menu:
- login (The certificate applies only to the current user.)
- System (The certificate applies to all users of a device.)
- Click OK.
- Type your password in the Authenticate dialog box and then click OK.
The root certificate is installed and used by TLS-enabled clients and by any other application using TLS.
About TLS policies
This section provides information for configuring security policies for ICA sessions over TLS. You can configure certain TLS settings used for ICA connections in Citrix Workspace app for Mac. These settings are not exposed in the user interface. Changing them requires running a command on the device running Citrix Workspace app for Mac.
Note:
TLS policies are managed in other ways - by devices controlled by an OS X server or another mobile device management solution.
TLS policies include the following settings:
SecurityComplianceMode. Sets the security compliance mode for the policy. If you don’t configure SecurityComplianceMode, FIPS is used as the default value. Applicable values for this setting include:
- None. No compliance mode is enforced
- FIPS. FIPS cryptographic modules are used
- SP800-52. NIST SP800-52r1 compliance is enforced
defaults write com.citrix.receiver.nomas SecurityComplianceMode SP800-52
SecurityAllowedTLSVersions. Specifies the TLS protocol versions that are accepted during protocol negotiation. This information is represented as an array and any combination of the possible values is supported. When this setting isn’t configured, the values TLS10, TLS11, and TLS12 are used as the default values. Applicable values for this setting include:
- TLS10. Specifies that the TLS 1.0 protocol is allowed.
- TLS11. Specifies that the TLS 1.1 protocol is allowed.
- TLS12. Specifies that the TLS 1.2 protocol is allowed.
- TLS13. Specifies that the TLS 1.3 protocol is allowed.
defaults write com.citrix.receiver.nomas SecurityAllowedTLSVersions -array TLS11 TLS12
SSLCertificateRevocationCheckPolicy. Improves the cryptographic authentication of the Citrix server and improves the overall security of the SSL/TLS connections between a client and a server. This setting governs the handling of a trusted root certificate authority (CA) while opening a remote session through SSL when using the client for OS X.
When you enable this setting, the client checks whether the server’s certificate is revoked. There are several levels of certificate revocation list checking. For example, the client can be configured to check only its local certificate list, or to check the local and network certificate lists. In addition, certificate checking can be configured to allow users to log on only if all Certificate Revocation lists are verified.
Certificate Revocation List (CRL) checking is an advanced feature supported by some certificate issuers. It allows admins to revoke security certificates (invalidated before their expiry date) if there is cryptographic compromise of certificate private keys, or unexpected changes in the DNS name.
Applicable values for this setting include:
- NoCheck. No Certificate Revocation List check is performed.
- CheckWithNoNetworkAccess. Certificate revocation list check is performed. Only local certificate revocation list stores are used. All distribution points are ignored. Finding a Certificate Revocation List isn’t critical for verification of the server certificate that presented by the target SSL Relay or Citrix Secure Web Gateway server.
- FullAccessCheck. Certificate Revocation List check is performed. Local Certificate Revocation List stores and all distribution points are used. Finding a Certificate Revocation List isn’t critical for verification of the server certificate presented by the target SSL Relay or Citrix Secure Web Gateway server.
- FullAccessCheckAndCRLRequired. Certificate Revocation List check is performed, excluding the root Certificate Authority. Local Certificate Revocation List stores and all distribution points are used. Finding all required Certificate Revocation Lists is critical for verification.
- FullAccessCheckAndCRLRequiredAll. Certificate Revocation List check is performed, including the root certificate authority. Local Certificate Revocation List stores and all distribution points are used. Finding all required Certificate Revocation Lists is critical for verification.
Note:
If you don’t set SSLCertificateRevocationCheckPolicy, FullAccessCheck is used as the default value.
defaults write com.citrix.receiver.nomas SSLCertificateRevocationCheckPolicy FullAccessCheckAndCRLRequired
Configuring TLS policies
To configure TLS settings on an unmanaged computer, run the defaults command in Terminal.app.
defaults is a command line application that you can use to add, edit, and delete app settings in an OS X preferences list file.
To change settings:
-
Open Applications > Utilities \ > Terminal.
-
In Terminal, run the command:
defaults write com.citrix.receiver.nomas <name> <type> <value>
Where:
<name>: The name of the setting as described earlier.
<type>: A switch identifying the type of the setting, either -string or -array. If the setting type is a string, this setting can be omitted.
<value>: The value for the setting. If the value is an array and multiple values need to be specified, separate the values with a space.
defaults write com.citrix.receiver.nomas SecurityAllowedTLSVersions -array TLS11 TLS12
Reverting to the default configuration
To reset a setting back to its default:
-
Open Applications > Utilities \ > Terminal.
-
In Terminal, run the command:
defaults delete com.citrix.receiver.nomas <name>
Where:
<name>: The name of the setting as described earlier.
defaults delete com.citrix.receiver.nomas SecurityAllowedTLSVersions
Security settings
Security improvements and enhancements were introduced with Citrix Receiver for Mac version 12.3, including the following:
- improved security configuration user interface. In previous releases, the command line was the preferred method to make security-related changes. Configuration settings related to session security are now simple and accessible from the UI. This improvement improves the user experience while creating a seamless method for the adoption of security-related preferences.
- view TLS connections. You can verify connections that use a specific TLS version, encryption algorithms, mode, key size, and SecureICA status. In addition, you can view the server certificate for TLS connections.
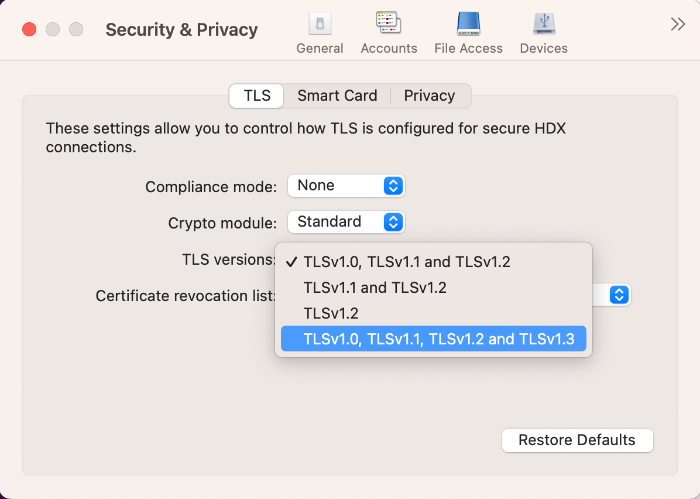
The improved Security and Privacy screen includes the following new options in the TLS tab:
- set the compliance mode
- configure the crypto module
- select the appropriate TLS version
- select the certificate revocation list
- enable settings for all TLS connections
The following image illustrates the Security and Privacy settings accessible from the UI: