Manage remote access to stores through Citrix Gateway
Use the Remote Access Settings task to configure access to stores through Citrix Gateway for users connecting from public networks. Remote access through a Citrix Gateway cannot be applied to unauthenticated stores.
Important:
In multiple server deployments, use only one server at a time to make changes to the configuration of the server group. Ensure that the Citrix StoreFront management console is not running on any of the other servers in the deployment. Once complete, propagate your configuration changes to the server group so that the other servers in the deployment are updated.
-
Select the Stores node in the right pane of the Citrix StoreFront management console and, in the results pane, select a store. In the Actions pane, click Configure Remote Access Settings.
-
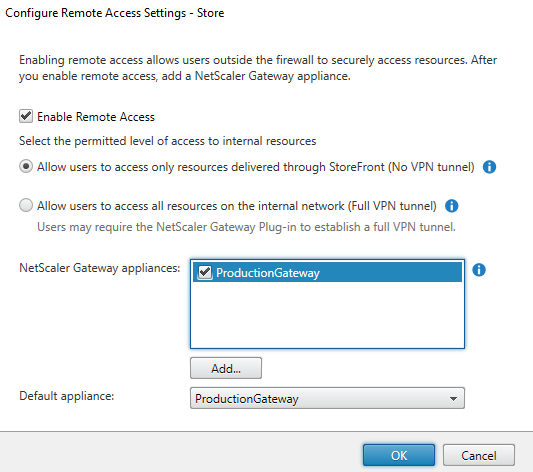
In the Configure Remote Access Settings dialog box, specify whether and how users connecting from public networks can access the store through Citrix Gateway.
- To make the store unavailable to users on public networks, do not check Enable remote access. Only local users on the internal network will be able to access the store.
- To enable remote access, check Enable Remote Access.
- To make resources delivered through the store available through Citrix Gateway, select No VPN tunnel. Users log on using either ICAProxy or clientless VPN (cVPN) to Citrix Gateway and do not need to use the Citrix Gateway plug-in to establish a full VPN.
- To make the store and other resources on the internal network available through a Secure Sockets Layer (SSL) virtual private network (VPN) tunnel, select Full VPN tunnel. Users require the Citrix Gateway plug-in to establish the VPN tunnel.
When you enable remote access to the store, the Pass-through from Citrix Gateway authentication method is automatically enabled. Users authenticate to Citrix Gateway and are automatically logged on when they access their stores.
-
If you enabled remote access, select from the Citrix Gateway appliances list the deployments through which users can access the store. Any deployments you configured previously for this and other stores are available for selection in the list. If you want to add a further deployment to the list, click Add and follow the steps in Add Citrix Gateway.
-
If you enable access through multiple appliances by selecting more than one entry in the list, specify the Default appliance to be used to access the store from Citrix Workspace app.
-
Click OK to save the configuation and close the Configure Remote Access dialog.
Citrix Workspace app uses beacon points to determine whether users are connected to local or public networks and then selects the appropriate access method. For more information about changing beacon points, see Configure beacon points.
By default StoreFront uses the Gateway through which the user is connected to the store to launch resources. To configure StoreFront to launch resources using an alternative gateway or no gateway, see Optimal HDX routing.