Support for TCP/UDP apps
Secure Private Access service enables you to access TCP/UDP applications that are present in your on-premises environment either using a native browser or a native client application through the Citrix Secure Access client running on your machine. For details, see the following sections:
- Prerequisites
- Configure Secure Private Access for TCP/UDP apps
- Admin Configuration – Citrix Secure Access client-based access to HTTP/HTTPS apps
- Adaptive access to TCP/UDP and HTTP(S) apps
- Troubleshoot application domains IP address conflict
Prerequisites
- Citrix Secure Access client - For details, see Citrix Secure Access client.
- Connector Appliance – Citrix recommends installing two Connector Appliances in a high availability set-up in your resource location. The connector can be installed either on-premises, in the data center hypervisor, or in public cloud. For more information on Connector Appliance and its installation, see Connector Appliance for Cloud Services. You must use a Connector Appliance for TCP/UDP apps. The Connector Appliance must have a DNS server configuration for DNS resolution.
Configure Secure Private Access for TCP/UDP apps
- Log in to Citrix Cloud and select Secure Private Access.
- Click Applications > App Configuration and then click Add an app.
-
In the Choose a template section, click Skip. Templates are available only for SaaS apps.
App is a logical grouping of destinations. We can create an app for multiple destinations – Each destination means different servers in the back end. For example, one app can have one SSH, one RDP, one Database server, and one Web server. You don’t have to create one app per destination, but one app can have many destinations.
-
In the App Details section, select Inside my corporate network, enter the following details, and click Next.
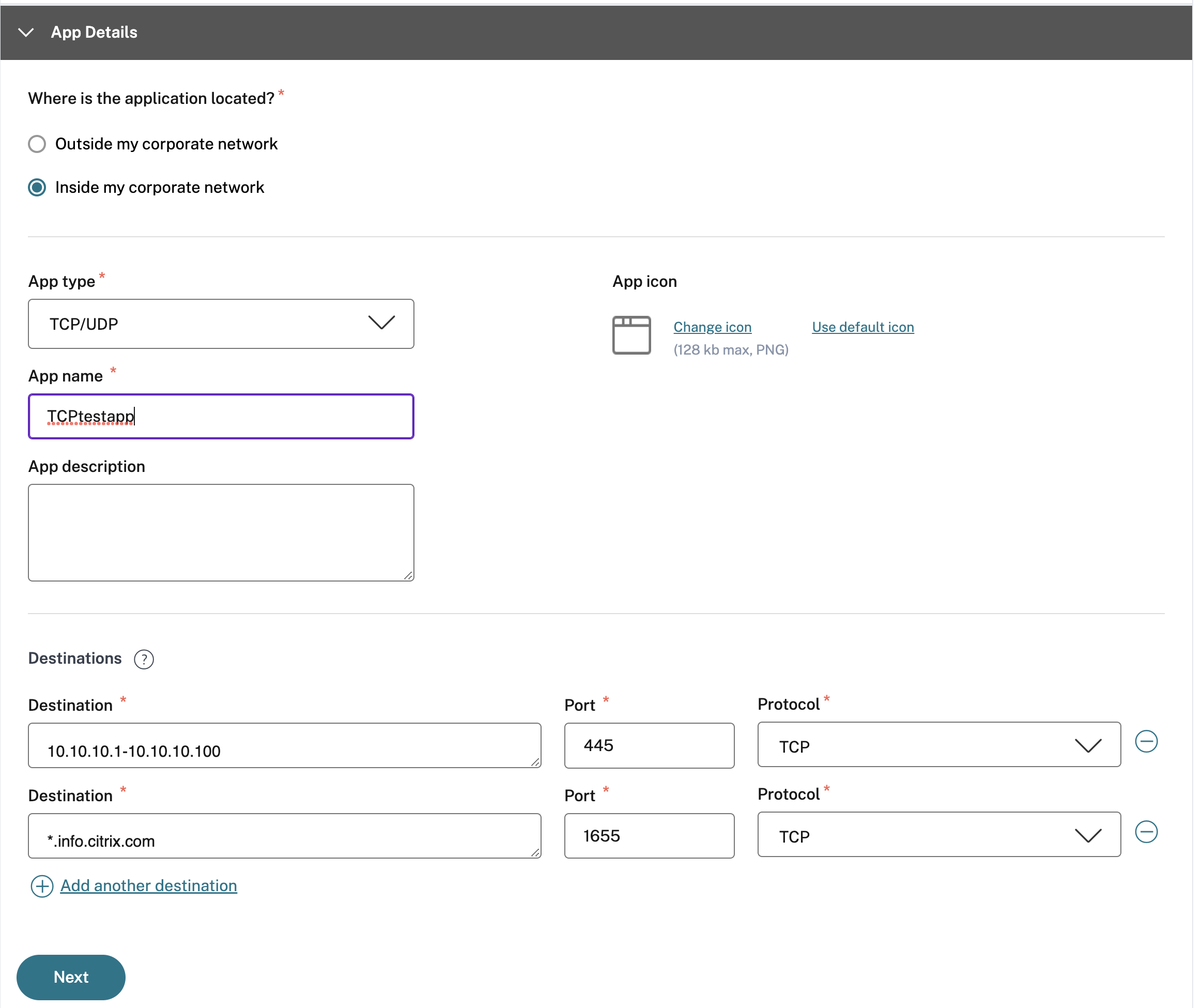
- App type – Select TCP/UDP.
- App name– Name of the application.
- App icon– An app icon is displayed. This field is optional.
- App description – Description of the app you are adding. This field is optional.
-
Destinations – IP Addresses or FQDNs of the back-end machines residing in the resource location. One or more destinations can be specified as follows.
- IP address v4
- IP address Range – Example: 10.68.90.10-10.68.90.99
- CIDR – Example: 10.106.90.0/24
-
FQDN of the machines or Domain name – Single or wildcard domain. Example: ex.destination.domain.com, *.domain.com
Important:
End users can access the apps using FQDN even if the admin has configured the apps using the IP address. This is possible because the Citrix Secure Access™ client can resolve an FQDN to the real IP address. The following table provides examples of various destinations and how to access the apps with these destinations:
Destination input How to access the app 10.10.10.1-10.10.10.100 End user is expected to access the app only through IP addresses in this range. 10.10.10.0/24 End user is expected to access the app only through IP addresses configured in the IP CIDR. 10.10.10.101 End user is expected to access the app only through 10.10.10.101 *.info.citrix.comEnd user is expected to access subdomains of info.citrix.comand alsoinfo.citrix.com(the parent domain). For example,info.citrix.com, sub1.info.citrix.com, level1.sub1.info.citrix.comNote: The wildcard must always be the starting character of the domain and only one *. is allowed.info.citrix.com End user is expected to access info.citrix.comonly and no subdomains. For example,sub1.info.citrix.comis not accessible.
-
Port – The port on which the app is running. Admins can configure multiple ports or port ranges per destination.
The following table provides examples of ports that can be configured for a destination.
Port input Description * By default, the port field is set to “*”(any port). The port numbers from 1 to 65535 are supported for the destination.1300–2400 The port numbers from 1300 to 2400 are supported for the destination. 38389 Only the port number 38389 is supported for the destination. 22,345,5678 The ports 22, 345, 5678 are supported for the destination. 1300–2400, 42000-43000,22,443 The port number range from 1300 to 2400, 42000–43000, and ports 22 and 443 are supported for the destination. Note:
Wildcard port (*) cannot co-exist with port numbers or ranges.
- Protocol – TCP/UDP
-
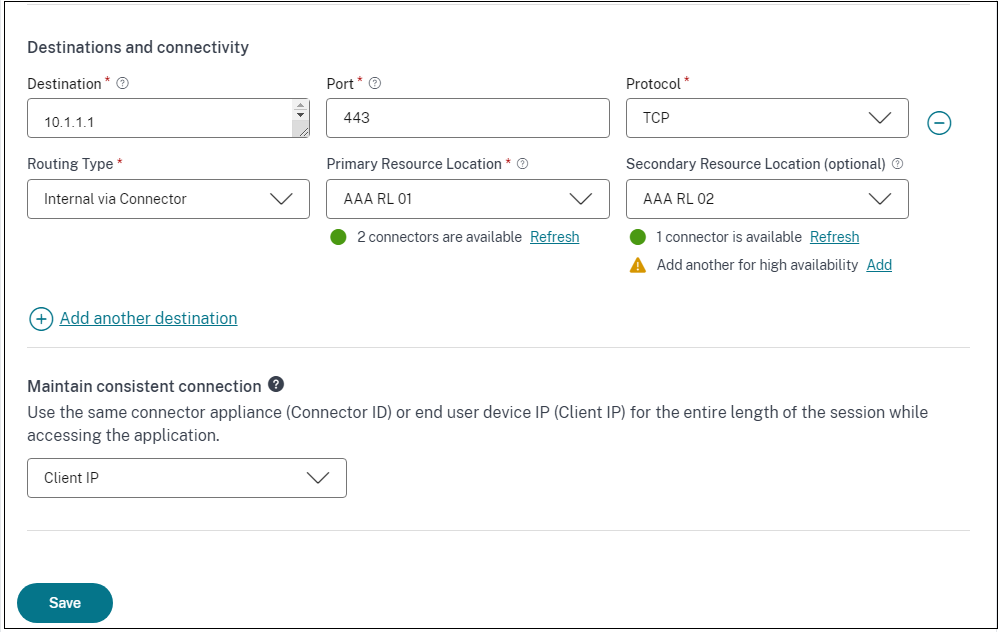
In the App Connectivity section, you define routing for the applications, if the domains must be routed externally or internally through Citrix Connector™ Appliance.
-
Routing Type - Select one of the following:
- Internal via Connector - The apps can be external but the traffic must flow through the Connector Appliance to the outside network.
- External – The traffic flows directly to the internet.
-
Primary and secondary resource locations - Admins can ensure high availability of applications even during disruptions by configuring a secondary resource location or by using the First Available option.
- Primary Resource Location: Select the primary resource location where the application is hosted. Alternatively, admins can select the option First Available in Primary Resource Location.
- First available: The First Available option ensures that a working resource location is used. When First Available is selected, the system automatically routes traffic to the first available location. This ensures continuous application access without manual intervention. For instance, if ResourceLocation1 is unavailable but ResourceLocation2 is reachable, then ResourceLocation2 is selected by default to front-end the application.
- Secondary Resource Location - The Secondary Resource Location option becomes available only if a primary resource location is explicitly specified. If the primary resource location becomes unavailable, for reasons such as a Connector Appliance or data center failure, the application fails over to the specified secondary resource location. The secondary resource location can also act as a failover even when the application is hosted in another data center.
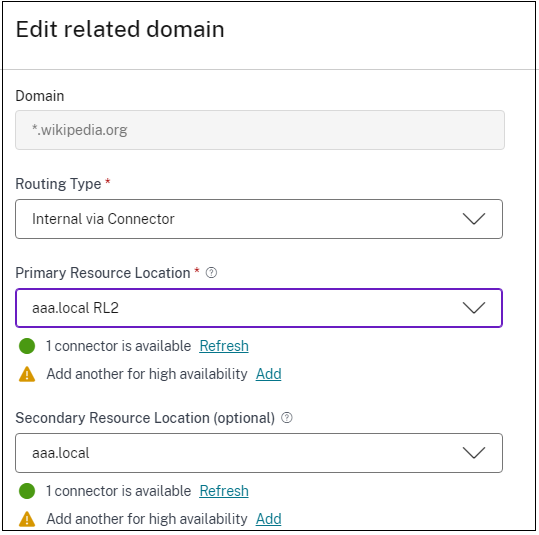
You can also set a primary and secondary resource location or select the First Available option for each of the related domains.
- Click the edit icon in the Actions column of the Related Domains table.
- Set the primary and secondary resource location or choose the First Available option.
Note:
Setting the backup resource location and using the First Available option feature is currently in Preview.
-
Maintain consistent connection - You can enable connector stickiness or client IP stickiness for the TCP/UDP apps. Select the Maintain consistent connection checkbox and then select on the following options:
- Do not use: The application does not require any persistence. The application can work with any source IP address.
- Client IP: The application uses the same source IP address for the client with each connection.
- Connector ID: The application connects to the same connector appliance with each session.Select one of the following options:
For details about consistent connections, see Maintain consistent connection.
-
-
Click Save and then click Finish.
The app is added to the Applications page. You can edit or delete an app from the Applications page after you have configured the application. To do so, click the ellipsis button on an app and select the actions accordingly.
- Edit Application
- Delete
Note:
- To grant access to the apps for the users, admins are required to create access policies. In access policies, admins add app subscribers and configure security controls. For details, see Create access policies.
To configure the authentication methods required for the users, see Setup identity and authentication.
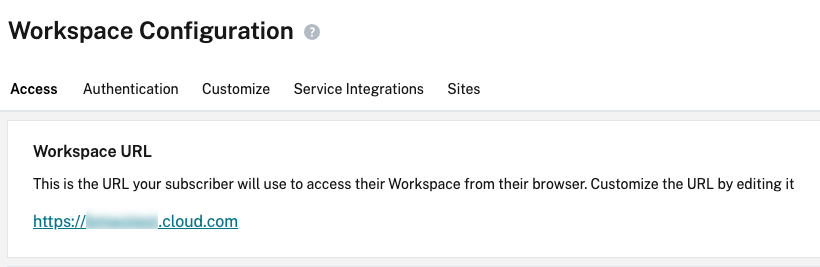
- To obtain the Workspace URL to be shared with the users, from the Citrix Cloud™ menu, click Workspace Configuration, and select the Access tab.
Admin Configuration – Citrix Secure Access client-based access to HTTP/HTTPS apps
Note:
To access existing or new HTTP/HTTPS apps using the Citrix Secure Access client, you must install at least one (recommended two for high-availability) Connector Appliance in your resource location. The connector appliance can be installed on-premises, in the data center hypervisor, or in the public cloud. For details of Connector Appliance and its installation, see Connector Appliance for Cloud Services.
Prerequisites
- Access to Citrix Secure Private Access in Citrix Cloud.
Points to note
- Internal web apps enforced with enhanced security controls cannot be accessed through the Citrix Secure Access client.
- SaaS apps cannot be accessed via the Citrix Secure Access client.
-
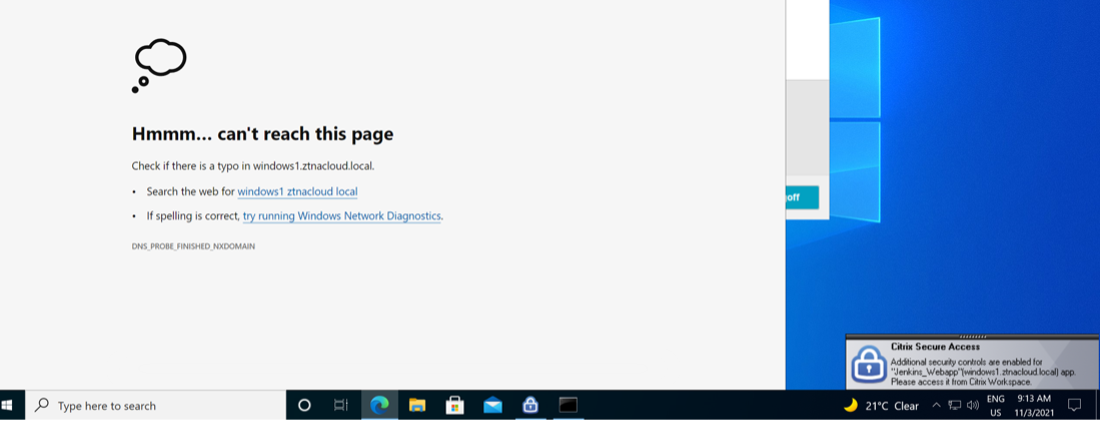
If you try to access an HTTP(S) application, which has enhanced security controls enabled, then the following pop-up message is displayed. Additional security controls are enabled for “app name”(FQDN) app. Please access it from Citrix Workspace.
- If you want to enable SSO experience, access the web apps using Citrix Workspace app or web portal.
The steps to configure HTTP(S) apps remain the same as existing functionality explained under Support for Enterprise web apps.
Adaptive access to TCP/UDP and HTTP(S) apps
Adaptive access provides the ability for admins to govern access to business-critical apps based on multiple contextual factors like device posture check, user geo-location, user role, and the Citrix Analytics service provided risk score.
Note:
You can deny access to TCP/UDP applications, admins create policies based on the users, user groups, the devices from which the users access the applications, and the location (country) from where an application is accessed. Access to applications is allowed by default.
The user subscription made for an app is applicable for all the TCP/UDP app destinations configured for the ZTNA application.
To create an adaptive access policy
Admins can use the admin-guided workflow wizard to configure Zero Trust Network Access to SaaS apps, internal web apps, and TCP/UDP apps in the Secure Private Access service.
Note:
- For details on creating an adaptive access policy, see Create access policies.
- For an end-to-end configuration of Zero Trust Network Access to SaaS apps, internal web apps, and TCP/UDP apps in the Secure Private Access service, see Admin-guided workflow for easy onboarding and set up.
Login and logout script configuration registries
The Citrix Secure Access client accesses the login and logout script configuration from the following registries when the Citrix Secure Access client connects to the Citrix Secure Private Access cloud service.
Registry: HKEY_LOCAL_MACHINE>SOFTWARE>Citrix>Secure Access Client
- Login script path: SecureAccessLogInScript type REG_SZ
- Logout script path: SecureAccessLogOutScript type REG_SZ
Troubleshoot application domains IP address conflict
Destinations added while creating an app are added to a main routing table. The routing table is the source of truth for making the routing decision to direct connection establishment and traffic to the correct resource location.
- The destination IP address must be unique across resource locations.
- Citrix recommends that you avoid overlap of the IP addresses or domains in the routing table. In case you encounter an overlap, you must resolve it.
Following are the types of conflict scenarios. Complete Overlap is the only error scenario that restricts admin configuration until the conflict is resolved.
| Conflict Scenarios | Existing application domain entry | New entry from app addition | Behavior |
|---|---|---|---|
| Subset Overlap | 10.10.10.0-10.10.10.255 RL1 | 10.10.10.50-10.10.10.60 RL1 | Allow; Warning info - Subset overlap of IP domain with existing entries |
| Subset Overlap | 10.10.10.0-10.10.10.255 RL1 | 10.10.10.50-10.10.10.60 RL2 | Allow; Warning info - Subset overlap of IP domain with existing entrieS |
| Partial Overlap | 10.10.10.0-10.10.10.100 RL1 | 10.10.10.50-10.10.10.200 RL1 | Allow; Warning info - Partial overlap of IP domain with existing entries |
| Partial Overlap | 10.10.10.0-10.10.10.100 RL1 | 10.10.10.50-10.10.10.200 RL2 | Allow; Warning info - Partial overlap of IP domain with existing entries |
| Complete Overlap | 10.10.10.0/24 RL1 | 10.10.10.0-10.10.10.255 RL1 | Error; <Completely overlapping IP domain's value> IP domain completely overlaps with existing entries.Change the existing routing IP Entry or configure a different destination |
| Complete Overlap | 10.10.10.0/24 RL1 | 10.10.10.0-10.10.10.255 RL2 | Error; <Completely overlapping IP domain's value> IP domain completely overlaps with existing entries. Change the existing routing IP Entry or configure a different destination |
| Exact Match | 20.20.20.0/29 RL1 | 20.20.20.0/29 | Allow; Domains already exist in the domain routing table. Changes update the domain routing table |
Note:
If the destinations added results in a complete overlap, an error is displayed while configuring the app in the App Details section. The admin must resolve this error by modifying the destinations in the App Connectivity section.
If there are no errors in the App Details section, the admin can proceed to save the app details. However, in the App Connectivity section, if the destinations have a subset and partial overlap with each other or existing entries in the main routing table, a warning message is displayed. In this case, the admin can choose to either resolve the error or continue with the configuration.
Citrix recommends keeping a clean Application Domain table. It is easier to configure new routing entries if the IP address domains are broken into appropriate chunks without overlaps.
Points to note
- Access to an existing web app for which enhanced security is enabled is denied via the Secure Access client. An error message suggesting to log in using Citrix Workspace app is displayed.
- Policy configurations for web app based on user risk score, device posture check and so on via Citrix Workspace app are applicable while accessing the app via the Secure Access client.
- The policy bound to an application is applicable for all the destinations in the application.
In this article
- Prerequisites
- Configure Secure Private Access for TCP/UDP apps
- Admin Configuration – Citrix Secure Access client-based access to HTTP/HTTPS apps
- Adaptive access to TCP/UDP and HTTP(S) apps
- Login and logout script configuration registries
- Troubleshoot application domains IP address conflict
- Points to note