Configure access to workspaces
When you first enable Workspace, a default cloud.com Workspace URL is created to allow users to access the Workspace from their locally installed Citrix Workspace app or web browsers. You can customize this URL or add additional URLs. For more information, see Workspace URL in this article.
For information on how users can connect to Citrix Workspace, see User access options.
To configure how users authenticate to Workspace, see Configure Authentication.
When a user launches a resource, the user’s device must be able to reach the Virtual Delivery Agent (VDA). For internal users, the endpoint must connect directly to the IP address of the Virtual Delivery Agent (VDA). Remote users can gain external access to their resources if you configure external connectivity with Citrix Gateway or the Citrix Gateway service. For information on enabling remote access to workspaces, see External connectivity in this article.
To configure access settings:
- Go to Citrix Cloud™ and sign in with your credentials.
- Navigate to Workspace Configuration > Access.
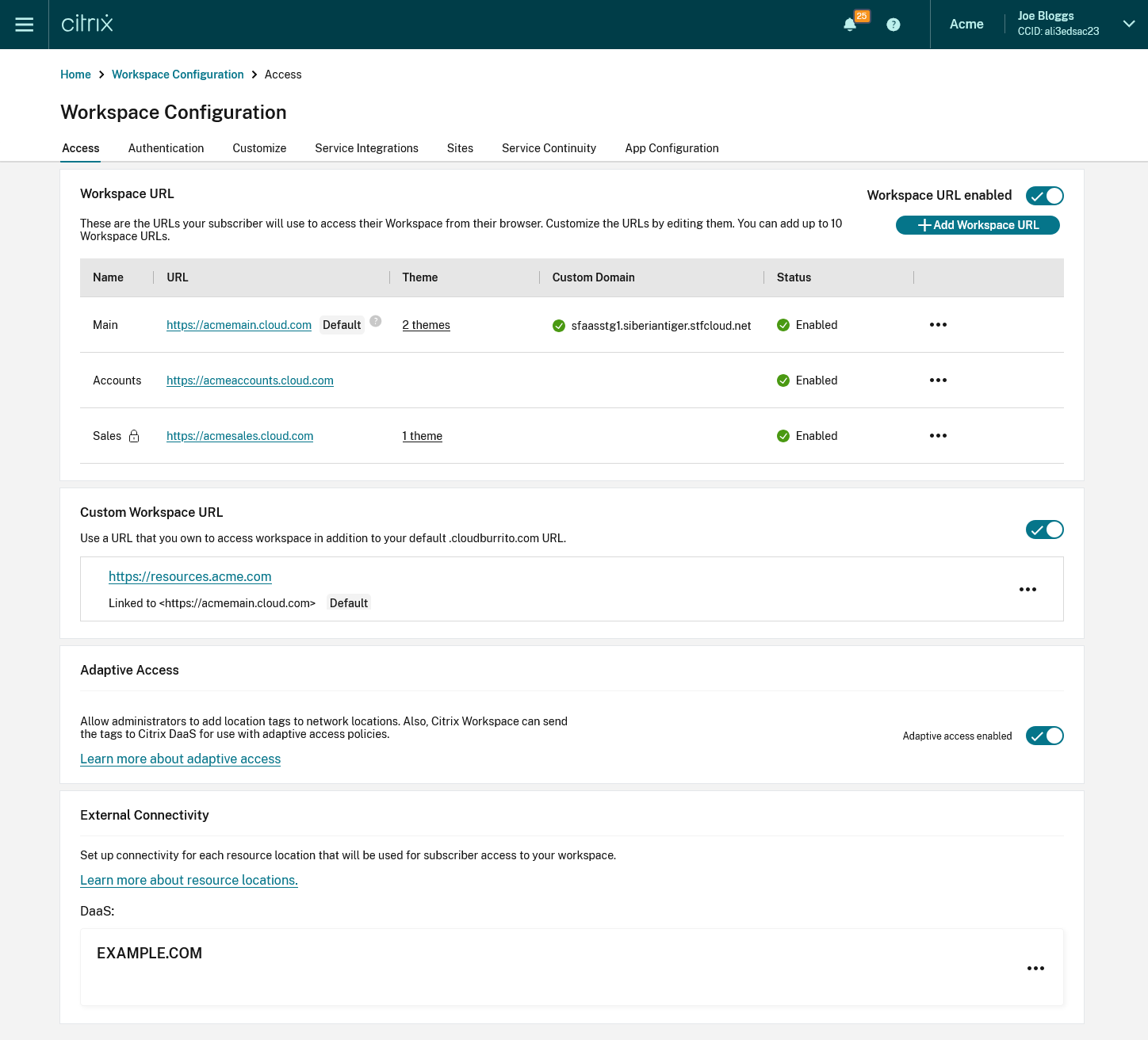
Workspace URL
To configure the cloud.com URLs that your end users use to access their Workspace, see Configure Workspace URLs.
Custom Workspace URL
In addition to the cloud.com Workspace URLs, you can use your own custom URL in place of the default Workspace URL. For more information, see Configure a custom domain.
Adaptive Access
The Adaptive access feature enables admins to provide granular level access to the apps that users can access based on the context. For more information, see Adaptive access.
To enable Adaptive Access
- Go to the Access tab
- Go to the section Adaptive access and click the toggle. A confirmation screen appears.
- Press Enable.
To disable Adaptive Access:
- Go to the Access tab
- Go to the section Adaptive access and click the toggle. A confirmation screen appears.
- Press Disable.
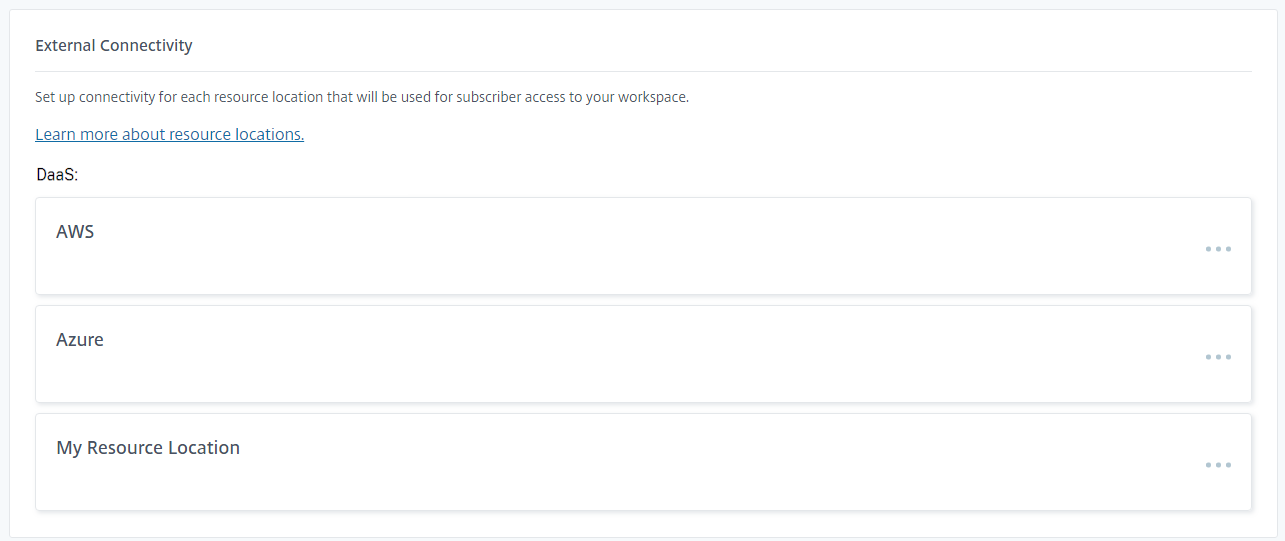
External connectivity
The Exernal connectivity panel lists each resource locations and allows you to configure how users connect to resources in those locations. For more information, see Connectivity to DaaS resources.