Configure access to workspaces
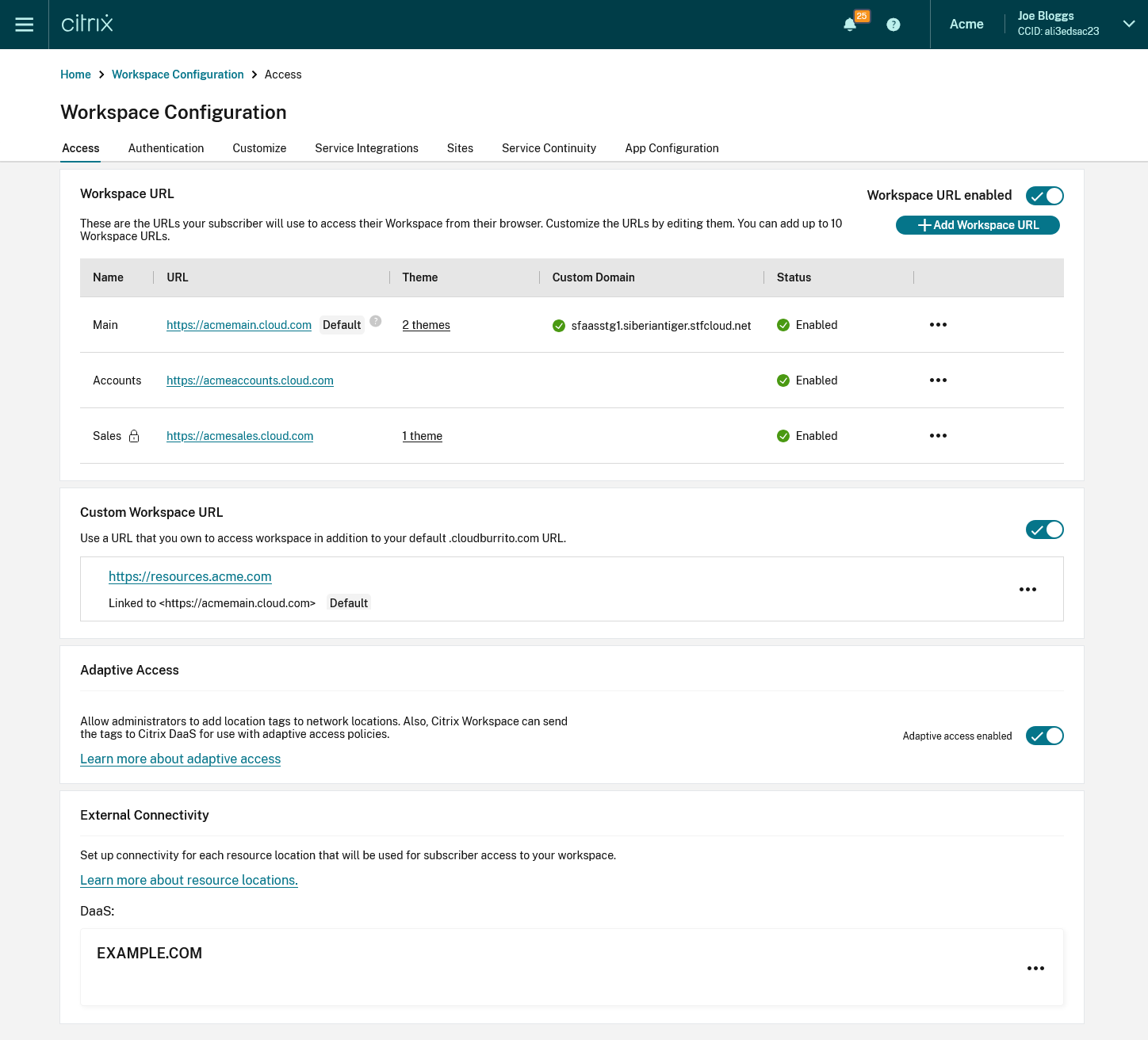
When you first enable Workspace, a default cloud.com Workspace URL is created to allow users to access the Workspace from their locally installed Citrix Workspace app or web browsers. You can customize this URL or add additional URLs. For more information, see Workspace URL in this article.
For information on how users can connect to Citrix Workspace, see User access options.
To configure how users authenticate to Workspace, see Configure Authentication.
When a user launches a resource, the user’s device must be able to reach the Virtual Delivery Agent (VDA). For internal users, the endpoint must connect directly to the IP address of the Virtual Delivery Agent (VDA). Remote users can gain external access to their resources if you configure external connectivity with Citrix Gateway or the Citrix Gateway service. For information on enabling remote access to workspaces, see External connectivity in this article.
To configure access settings:
- Go to Citrix Cloud™ and sign in with your credentials.
- Navigate to Workspace Configuration > Access.
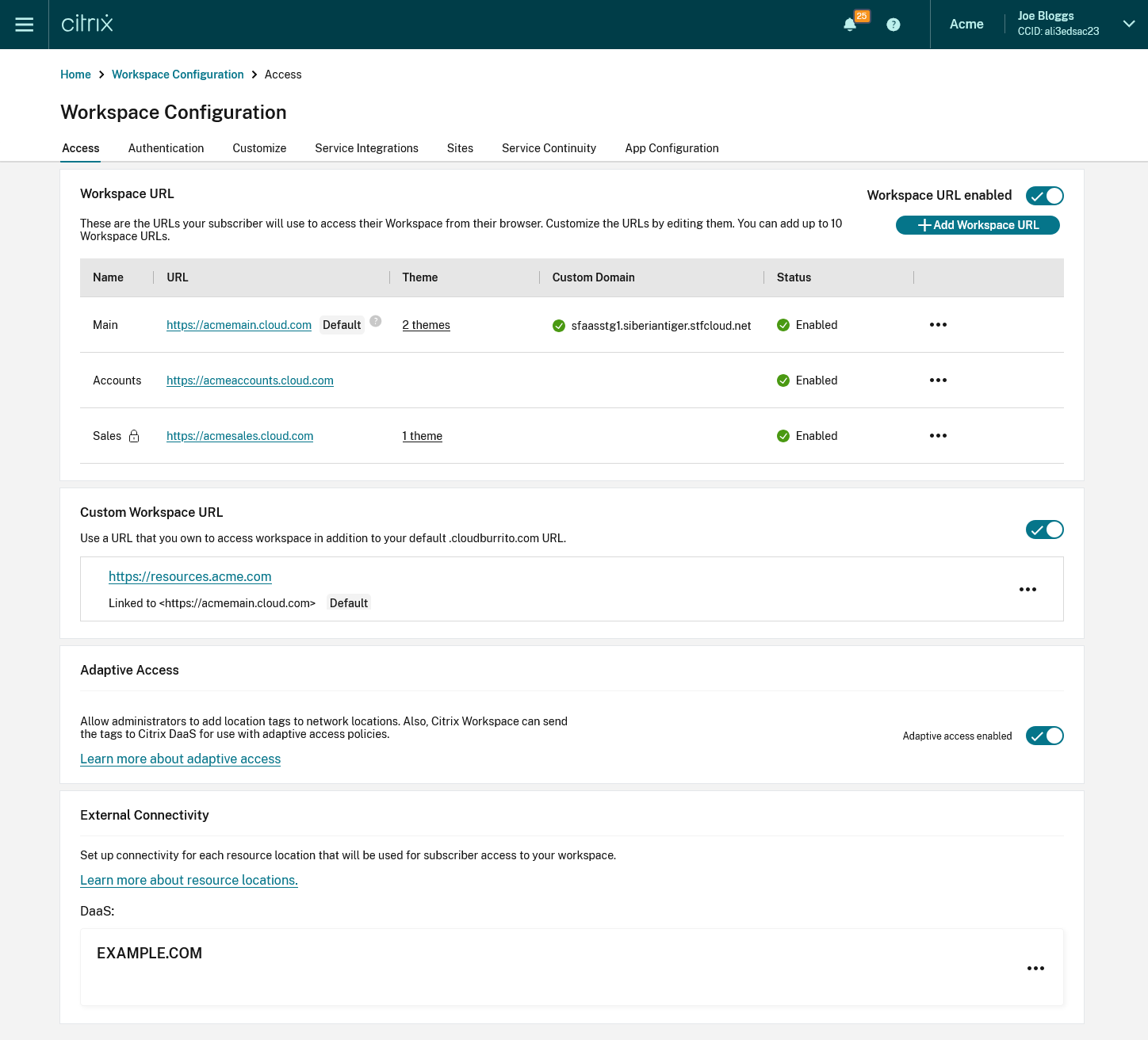
Workspace URL
To configure the cloud.com URLs that your end users use to access their Workspace, see Configure Workspace URLs.
Custom Workspace URL
In addition to the cloud.com Workspace URLs, you can use your own custom URL in place of the default Workspace URL. For more information, see Configure a custom domain.
Adaptive Access
The Adaptive access feature enables admins to provide granular level access to the apps that users can access based on the context. For more information, see Adaptive access.
To enable Adaptive Access
- Go to the Access tab
- Go to the section Adaptive access and click the toggle. A confirmation screen appears.
- Press Enable.
To disable Adaptive Access:
- Go to the Access tab
- Go to the section Adaptive access and click the toggle. A confirmation screen appears.
- Press Disable.
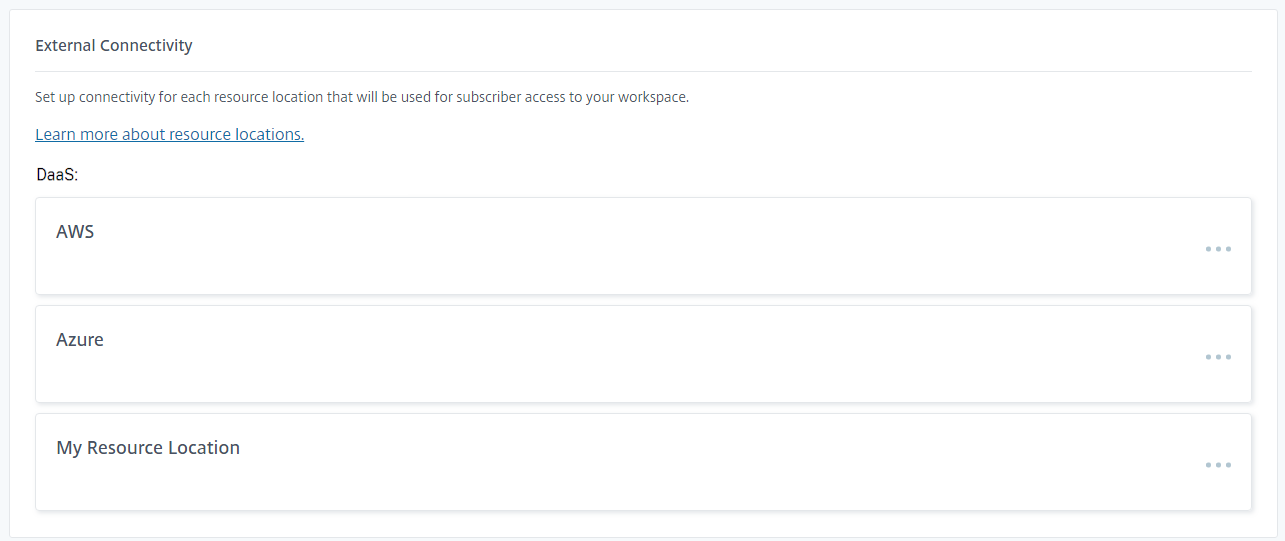
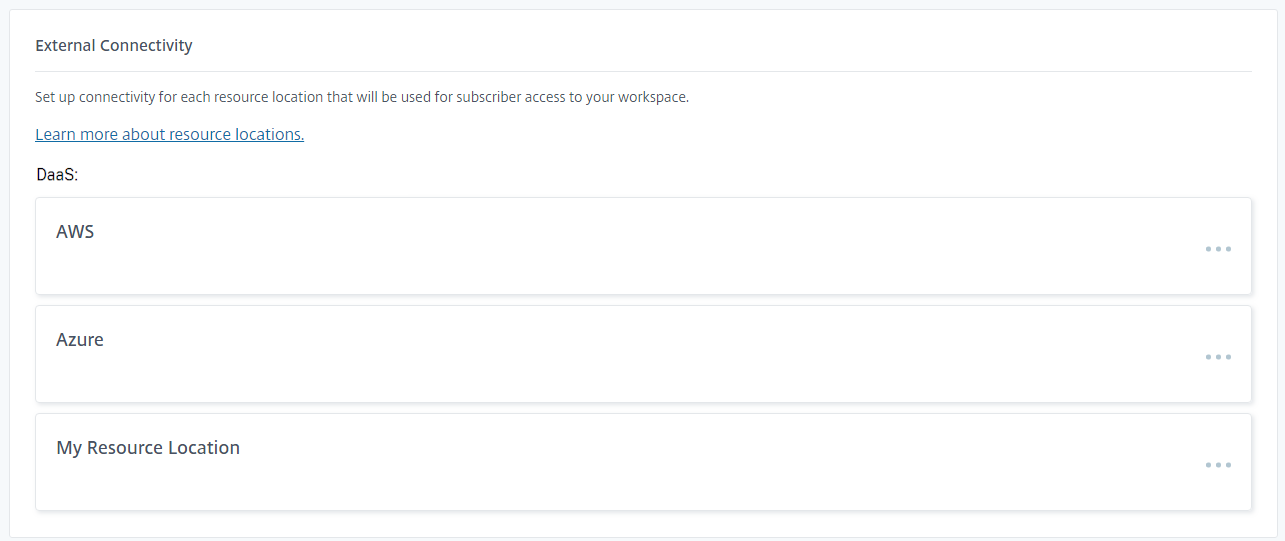
External connectivity
The Exernal connectivity panel lists each resource locations and allows you to configure how users connect to resources in those locations. For more information, see Connectivity to DaaS resources.
The official version of this content is in English. Some of the Cloud Software Group documentation content is machine translated for your convenience only. Cloud Software Group has no control over machine-translated content, which may contain errors, inaccuracies or unsuitable language. No warranty of any kind, either expressed or implied, is made as to the accuracy, reliability, suitability, or correctness of any translations made from the English original into any other language, or that your Cloud Software Group product or service conforms to any machine translated content, and any warranty provided under the applicable end user license agreement or terms of service, or any other agreement with Cloud Software Group, that the product or service conforms with any documentation shall not apply to the extent that such documentation has been machine translated. Cloud Software Group will not be held responsible for any damage or issues that may arise from using machine-translated content.
DIESER DIENST KANN ÜBERSETZUNGEN ENTHALTEN, DIE VON GOOGLE BEREITGESTELLT WERDEN. GOOGLE LEHNT JEDE AUSDRÜCKLICHE ODER STILLSCHWEIGENDE GEWÄHRLEISTUNG IN BEZUG AUF DIE ÜBERSETZUNGEN AB, EINSCHLIESSLICH JEGLICHER GEWÄHRLEISTUNG DER GENAUIGKEIT, ZUVERLÄSSIGKEIT UND JEGLICHER STILLSCHWEIGENDEN GEWÄHRLEISTUNG DER MARKTGÄNGIGKEIT, DER EIGNUNG FÜR EINEN BESTIMMTEN ZWECK UND DER NICHTVERLETZUNG VON RECHTEN DRITTER.
CE SERVICE PEUT CONTENIR DES TRADUCTIONS FOURNIES PAR GOOGLE. GOOGLE EXCLUT TOUTE GARANTIE RELATIVE AUX TRADUCTIONS, EXPRESSE OU IMPLICITE, Y COMPRIS TOUTE GARANTIE D'EXACTITUDE, DE FIABILITÉ ET TOUTE GARANTIE IMPLICITE DE QUALITÉ MARCHANDE, D'ADÉQUATION À UN USAGE PARTICULIER ET D'ABSENCE DE CONTREFAÇON.
ESTE SERVICIO PUEDE CONTENER TRADUCCIONES CON TECNOLOGÍA DE GOOGLE. GOOGLE RENUNCIA A TODAS LAS GARANTÍAS RELACIONADAS CON LAS TRADUCCIONES, TANTO IMPLÍCITAS COMO EXPLÍCITAS, INCLUIDAS LAS GARANTÍAS DE EXACTITUD, FIABILIDAD Y OTRAS GARANTÍAS IMPLÍCITAS DE COMERCIABILIDAD, IDONEIDAD PARA UN FIN EN PARTICULAR Y AUSENCIA DE INFRACCIÓN DE DERECHOS.
本服务可能包含由 Google 提供技术支持的翻译。Google 对这些翻译内容不做任何明示或暗示的保证,包括对准确性、可靠性的任何保证以及对适销性、特定用途的适用性和非侵权性的任何暗示保证。
このサービスには、Google が提供する翻訳が含まれている可能性があります。Google は翻訳について、明示的か黙示的かを問わず、精度と信頼性に関するあらゆる保証、および商品性、特定目的への適合性、第三者の権利を侵害しないことに関するあらゆる黙示的保証を含め、一切保証しません。
ESTE SERVIÇO PODE CONTER TRADUÇÕES FORNECIDAS PELO GOOGLE. O GOOGLE SE EXIME DE TODAS AS GARANTIAS RELACIONADAS COM AS TRADUÇÕES, EXPRESSAS OU IMPLÍCITAS, INCLUINDO QUALQUER GARANTIA DE PRECISÃO, CONFIABILIDADE E QUALQUER GARANTIA IMPLÍCITA DE COMERCIALIZAÇÃO, ADEQUAÇÃO A UM PROPÓSITO ESPECÍFICO E NÃO INFRAÇÃO.