Rendezvous V2
When using the Citrix Gateway service, the Rendezvous protocol allows traffic to bypass the Citrix Cloud™ Connectors and connect directly and securely with the Citrix Cloud control plane.
There are two types of traffic to consider: 1) control traffic for VDA registration and session brokering; 2) HDX™ session traffic.
Rendezvous V1 allows for HDX session traffic to bypass Cloud Connectors, but it still requires Cloud Connectors to proxy all control traffic for VDA registration and session brokering.
Standard AD domain joined machines and non-domain joined machines are supported for using Rendezvous V2 with single-session and multi-session Linux VDAs. With non-domain joined machines, Rendezvous V2 allows for both HDX traffic and control traffic to bypass the Cloud Connectors.
Requirements
The requirements for using Rendezvous V2 are:
- Access to the environment using Citrix Workspace™ and Citrix Gateway service.
- Control Plane: Citrix DaaS (formerly Citrix Virtual Apps and Desktops™ service).
- VDA version 2201 or later.
- Version 2204 is the minimum required for HTTP and SOCKS5 proxies.
- Enable the Rendezvous protocol in the Citrix policy. For more information, see Rendezvous protocol policy setting.
-
The VDAs must have access to:
-
https://*.xendesktop.netonTCP 443. If you can’t allow all subdomains in that manner, you can usehttps://<customer_ID>.xendesktop.net, where<customer_ID>is your Citrix Cloud customer ID as shown in the Citrix Cloud administrator portal. -
https://*.nssvc.net, including all subdomains. If you cannot whitelist all subdomains in that manner, usehttps://*.c.nssvc.netandhttps://*.g.nssvc.netinstead. For more information, see the Internet Connectivity Requirements section of the Citrix Cloud documentation (under Virtual Apps and Desktop service) and the Knowledge Center article CTX270584.
-
- The VDAs must be able to connect to the addresses mentioned previously:
- On TCP 443, for TCP Rendezvous.
- On UDP 443, for EDT Rendezvous.
Proxy configuration
The VDA supports connecting through proxies for both control traffic and HDX session traffic when using Rendezvous. The requirements and considerations for both types of traffic are different, so review them carefully.
Control traffic proxy considerations
- Only HTTP proxies are supported.
- Packet decryption and inspection are not supported. Configure an exception so the control traffic between the VDA and the Citrix Cloud control plane is not intercepted, decrypted, or inspected. Otherwise, the connection fails.
- Proxy authentication is not supported.
-
To configure a proxy for control traffic, edit the registry as follows:
/opt/Citrix/VDA/bin/ctxreg create -k "HKLM\Software\Citrix\VirtualDesktopAgent" -t "REG_SZ" -v "ProxySettings" -d "http://<URL or IP>:<port>" --force <!--NeedCopy-->
HDX traffic proxy considerations
- HTTP and SOCKS5 proxies are supported.
- EDT can only be used with SOCKS5 proxies.
- To configure a proxy for HDX traffic, use the Rendezvous proxy configuration policy setting.
- Packet decryption and inspection are not supported. Configure an exception so the HDX traffic between the VDA and the Citrix Cloud control plane is not intercepted, decrypted, or inspected. Otherwise, the connection fails.
-
HTTP proxies support machine-based authentication by using the Negotiate and Kerberos authentication protocols. When you connect to the proxy server, the Negotiate authentication scheme automatically selects the Kerberos protocol. Kerberos is the only scheme that the Linux VDA supports.
Note:
To use Kerberos, you must create the service principal name (SPN) for the proxy server and associate it with the proxy’s Active Directory account. The VDA generates the SPN in the format
HTTP/<proxyURL>when establishing a session, where the proxy URL is retrieved from the Rendezvous proxy policy setting. If you don’t create an SPN, authentication fails. - Authentication with a SOCKS5 proxy is not currently supported. If using a SOCKS5 proxy, you must configure an exception so that traffic destined to Gateway Service addresses (specified in the requirements) can bypass authentication.
- Only SOCKS5 proxies support data transport through EDT. For an HTTP proxy, use TCP as the transport protocol for ICA.
Transparent proxy
Transparent HTTP proxy is supported for Rendezvous. If using a transparent proxy in your network, no additional configuration is required on the VDA.
How to configure Rendezvous V2
Following are the steps for configuring Rendezvous in your environment:
- Make sure that all requirements are met.
-
After the VDA is installed, run the following command to set the required registry key:
/opt/Citrix/VDA/bin/ctxreg create -k "HKLM\Software\Citrix\VirtualDesktopAgent" -t "REG_DWORD" -v "GctRegistration" -d "0x00000001" --force <!--NeedCopy--> - (Optional) Set the optional registry key to enable caching the CGS FQDN IP address
/opt/Citrix/VDA/bin/ctxreg create -k "HKLM\Software\Citrix\Ica\EdgeNodeCache" -t "REG_DWORD" -v "EnableDNSCache" -d "0x00000001" --force - Restart the VDA machine.
- Create a Citrix policy, or edit an existing one:
- Set the Rendezvous Protocol setting to Allowed. The Rendezvous Protocol is disabled by default. When the Rendezvous Protocol is enabled (Allowed), Rendezvous V2 instead of V1 takes effect.
- Ensure that the Citrix policy filters are set properly. The policy applies to the machines that need Rendezvous to be enabled.
- Ensure that the Citrix policy has the correct priority so that it does not overwrite another one.
Rendezvous validation
To check whether a session is using the Rendezvous protocol, run the /opt/Citrix/VDA/bin/ctxquery -f iP command in the terminal.
The transport protocols displayed indicate the type of connection:
- TCP Rendezvous: TCP - TLS - CGP - ICA
- EDT Rendezvous: UDP - DTLS - CGP - ICA
- Proxy through Cloud Connector: TCP - PROXY - SSL - CGP - ICA or UDP - PROXY - DTLS - CGP - ICA
If Rendezvous V2 is in use, the protocol version shows 2.0.
Tip:
If the VDA cannot reach the Citrix Gateway service directly with Rendezvous enabled, the VDA falls back to proxy the HDX session through the Cloud Connector.
Rendezvous traffic flow
The following diagram illustrates the sequence of steps about Rendezvous traffic flow.
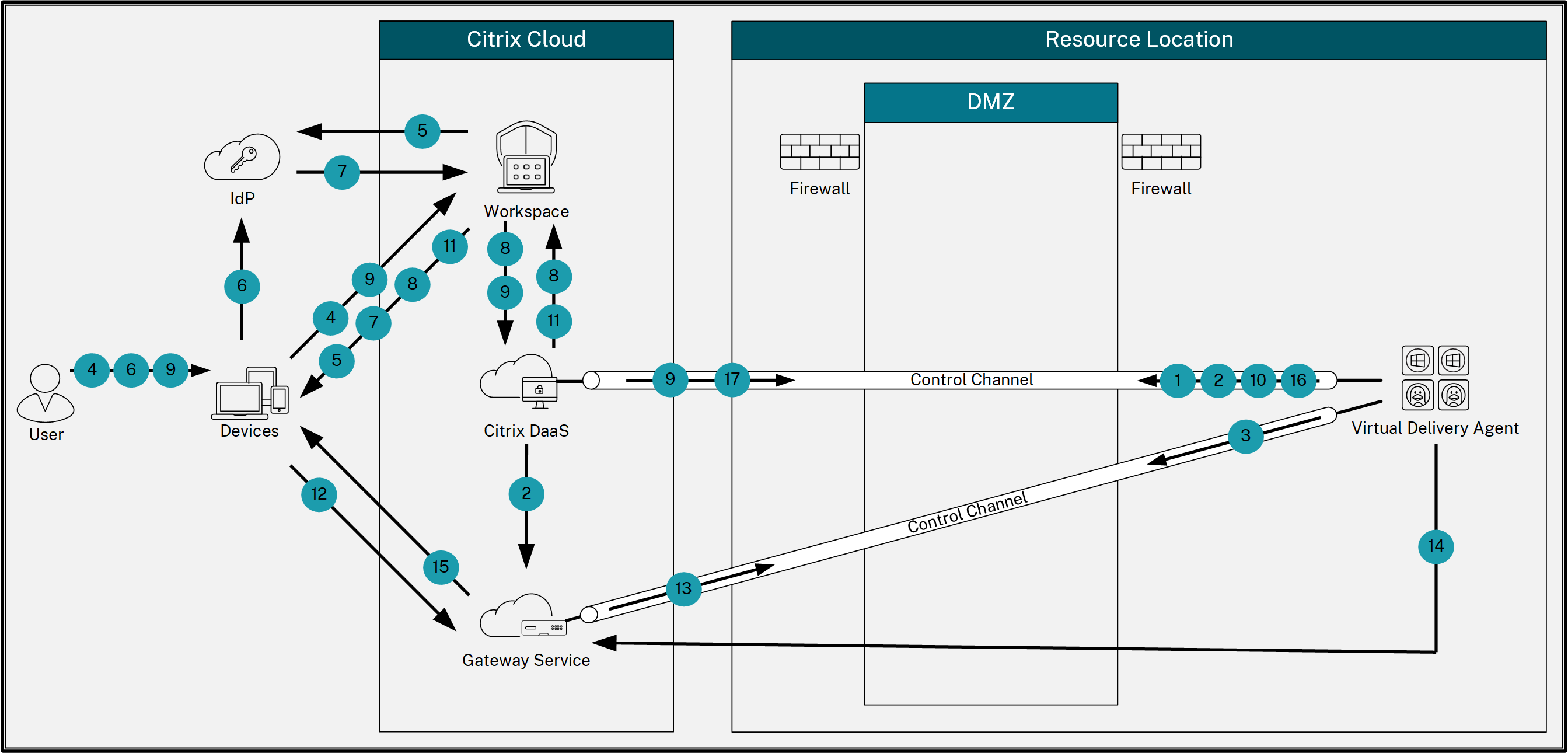
- The VDA establishes a WebSocket connection with Citrix Cloud and registers.
- The VDA registers with Citrix Gateway Service and obtains a dedicated token.
- The VDA establishes a persistent control connection with the Gateway Service.
- The user navigates to Citrix Workspace.
- Workspace evaluates authentication configuration and redirects users to the appropriate IdP for authentication.
- The user enters their credentials.
- After successfully validating the user credentials, the user is redirected to Workspace.
- Workspace counts resources for the user and displays them.
- The user selects a desktop or application from Workspace. Workspace sends the request to Citrix DaaS™, which brokers the connection and instructs the VDA to prepare for the session.
- The VDA responds with the Rendezvous capability and its identity.
- Citrix DaaS generates a launch ticket and sends it to the user device through Workspace.
- The user’s endpoint connects to the Gateway Service and provides the launch ticket to authenticate and identify the resource to connect to.
- The Gateway Service sends the connection information to the VDA.
- The VDA establishes a direct connection for the session with the Gateway Service.
- The Gateway Service completes the connection between the endpoint and the VDA.
- The VDA verifies licensing for the session.
- Citrix DaaS sends applicable policies to the VDA.