Get started
This article is a reference document to help you set up your environment after you install Citrix Workspace app.
Store
A store aggregates available applications and desktops for a user into a single place. A user can have multiple stores and switch across stores as needed. An admin delivers the store url that has pre-configured resources and settings. You can access these stores through the Citrix Workspace app.
Types of stores
You can add the following store types in the Citrix Workspace app: Workspace, StoreFront, Citrix Gateway Store, and Custom web store.
Workspace
Citrix Workspace is a cloud-based enterprise app store that provides secure and unified access to apps, desktops, and content (resources) from anywhere, on any device. These resources can be Citrix DaaS, content apps, local and mobile apps, SaaS and Web apps, and browser apps. For more information, see Citrix Workspace Overview.
StoreFront
StoreFront is an on-premises enterprise app store that aggregates applications and desktops from Citrix Virtual Apps and Desktops sites into a single easy-to-use store for users.
For more information, see StoreFront documentation.
Citrix Gateway Store
Configure Citrix Gateway to enable users to connect from outside the internal network. For example, users who connect from the Internet or from remote locations.
Custom web stores
This feature provides access to your organization’s custom web store from the Citrix Workspace app for Windows. To use this feature, the admin must add the domain or custom web store to the Global App Configuration Service allowed URLs.
For more information about configuring web store URLs for end-users, see Global App Configuration Service.
You can provide the custom web store URL in the Add Account screen in Citrix Workspace app. The custom web store opens in the native Citrix Workspace app window.
To remove the custom web store, go to Accounts > Add or Remove accounts, select the custom web store URL, and click Remove.
Sign out custom web store upon Citrix Workspace app exit
When the signoutCustomWebstoreOnExit attribute is set to True, closing the Citrix Workspace app signs you out of custom webstores. You can configure the signoutCustomWebstoreOnExit attribute in Global App Configuration Service.
For more information, see Global App Configuration Service documentation.
Adding store URL to Citrix Workspace app
You can provide users with the account information that they need to access virtual desktops and applications using the following:
- Providing users with account information to enter manually
- Configuring email-based account discovery
- Adding store through CLI
- Provisioning file
- Using the Group Policy Object administrative template
Provide users with account information to enter manually
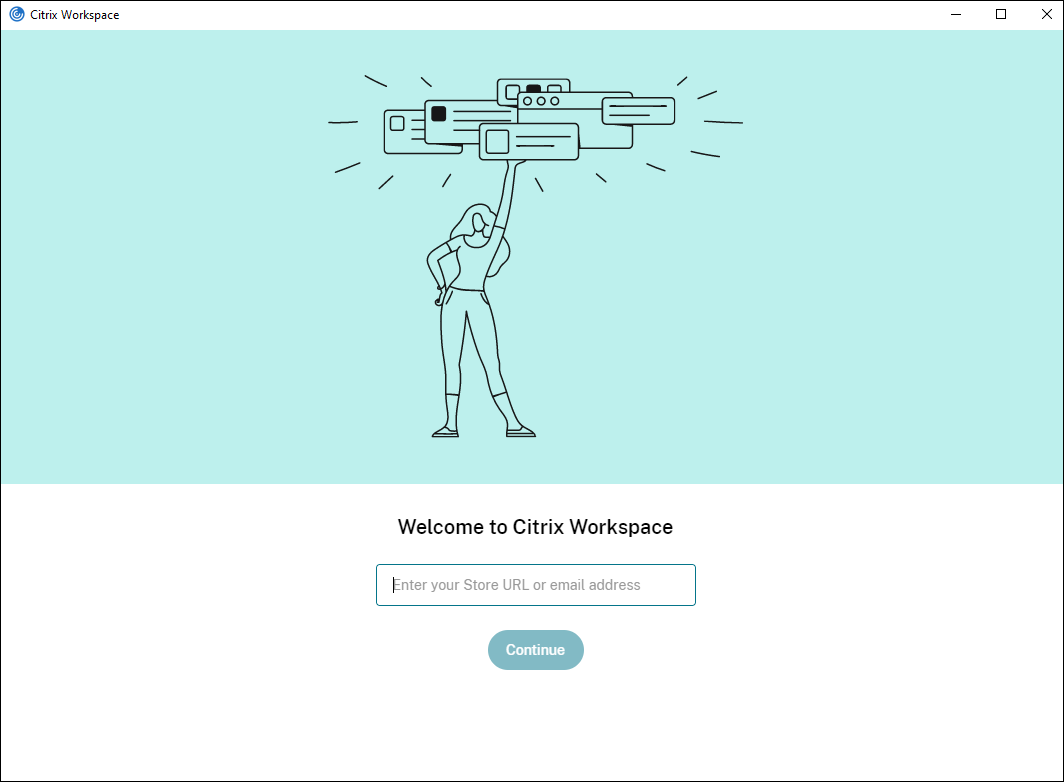
Upon successful installation of Citrix Workspace app, the following screen appears. Users are required to enter an email or server address to access the apps and desktops. When a user enters the details for a new account, Citrix Workspace app tries to verify the connection. If successful, Citrix Workspace app prompts the user to log on to the account.
To enable users to set up accounts manually, be sure to distribute the information required to connect to their virtual desktops and applications.
- To connect to a Workspace store, provide the Workspace URL.
- To connect to a StoreFront store, provide the URL for that server. For example:
https://servername.company.com. -
To connect through Citrix Gateway, first determine whether a user must see all configured stores or just the store with remote access enabled for a particular Citrix Gateway.
-
To present all configured stores: Provide users with the Citrix Gateway fully qualified domain name.
-
To limit access to a particular store: Provide users with the Citrix Gateway fully qualified domain name and the store name in the form:
CitrixGatewayFQDN?MyStoreName:
For example, if a store named “SalesApps” has remote access enabled for server1.com and a store named HRApps has remote access enabled for server2.com, a user must enter:
- server1.com?SalesApps to access SalesApps or
- server2.com?HRApps to access HRApps.
CitrixGatewayFQDN?MyStoreName feature requires a new user to create an account by entering a URL and isn’t available for email-based discovery.
-
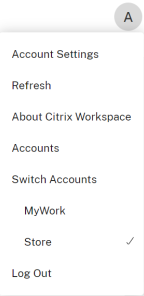
Once the Citrix Workspace app is configured with the Store URL, the account can be managed from the Accounts option in the profile menu.
On client machines configured for proxy authentication, if the proxy credentials aren’t stored in the Windows Credential Manager, an authentication prompt appears, asking you to enter the proxy credentials. Citrix Workspace app then saves the proxy server credentials in Windows Credential Manager. This results in a seamless login experience because you don’t need to manually save your credentials in Windows Credential Manager before accessing Citrix Workspace app.
Configure email-based account discovery
When you configure Citrix Workspace app for email-based account discovery, users enter their email address rather than a server URL during initial Citrix Workspace app installation and configuration. Citrix Workspace app determines the Citrix Gateway or StoreFront Server associated with the email address based on Domain Name System (DNS) Service (SRV) records. The app then prompts the user to log on to access virtual desktops and applications.
To configure email-based account discovery for Citrix Workspace stores, see Getting started in the Global App Configuration Service documentation. To configure email-based account discovery for Citrix StoreFront or Citrix Gateway stores, see Configuring email-based account discovery.
Adding store through CLI
Install Citrix Workspace app for Windows as an administrator using the command-line interface.
For more information, see List of command-line parameters.
Provide users with provisioning files
StoreFront provides provisioning files that users can open to connect to stores.
You can use StoreFront to create provisioning files that include connection details for accounts. Make these files available to your users to enable them to configure Citrix Workspace app automatically. After installing Citrix Workspace app, users simply open the file to configure Citrix Workspace app. If you configure workspace for web, users can also get Citrix Workspace app provisioning files from those sites.
For more information, see To export store provisioning files for users in the StoreFront documentation.
Using the Group Policy Object Administrative Template
To add or specify a Citrix StoreFront or Gateway using the Group Policy Object administrative template:
- Open the Citrix Workspace app Group Policy Object administrative template by running
gpedit.msc. - Under the Computer Configuration node, go to Administrative Templates > Classic Administrative Templates (ADM) > Citrix Components > Citrix Workspace > StoreFront.
- Select Citrix Gateway URL/StoreFront Accounts List.
- Select Enabled option and click Show. If you enable this policy setting, you can enter a list of StoreFront Accounts and NetScaler Gateway URL.
- Enter the URL in the Value field.
-
Specify the store URL that is used with the Citrix Workspace app:
STOREx="storename;http[s]://servername.domain/IISLocation/discovery;[On, Off]; [storedescription]"Values:
- x - Integers 0 through 9 used to identify a store.
- storename - Name of the store. This value must match the name configured on the StoreFront server.
- servername.domain - The fully qualified domain name of the server hosting the store.
- IISLocation - the path to the store within IIS. The store URL must match the URL in the StoreFront provision file. The store URL is in the following format /Citrix/store/discovery. To get the URL, export a provisioning file from StoreFront, launch it in Notepad and copy the URL from the Address element.
- [On, Off] - The Off option lets you deliver disabled stores, giving users the choice of whether they access them. When the store status isn’t specified, the default setting is On.
- storedescription - Description of the store, such as HR App Store.
-
Add or specify the Citrix Gateway URL. Enter the name of the URL, delimited by a semi-colon:
Example:
STORE0= HRStore;https://ag.mycompany.com#Storename;On;StoreWhere #Store name is the name of the store behind Citrix Gateway.
Note:
- The Citrix Gateway store URL must be first in the list (parameter STORE0).
- In a multi-store setup, only one Citrix Gateway store URL configuration is allowed.
- The Citrix Gateway store URL configured using this method does not support the PNA Services Sites that are using Citrix Gateway.
- The
/Discoveryparameter is not required when specifying a Citrix Gateway store URL.
Starting with Version 1808, changes made to the Citrix Gateway URL/StoreFront Account List policy are applied in a session after app restart. A reset isn’t required.
Note:
Citrix Workspace app Version 1808 and later doesn’t require resetting on a fresh installation. If there’s an upgrade to 1808 or later, you must reset the Citrix Workspace app for the changes to take effect.
Limitations:
- Citrix Gateway URL must be listed first followed by StoreFront URLs.
- No support for Multiple Citrix Gateway URLs.
Note:
Users can also access the store via a web browser. Users can log in to the Citrix Store from a web browser and launch a virtual app or desktop from the web. The virtual app or desktop launch leverages the capabilities of the natively installed Citrix Workspace app.
In this case, it may be desirable to hide the Add Account prompt from users. This can be achieved via the following setting:
- Renaming Citrix execution file: Rename the CitrixWorkspaceApp.exe to CitrixWorkspaceAppWeb.exe to alter the behavior of Add Account dialog. When you rename the file, the Add Account dialog is not displayed from the Start menu.
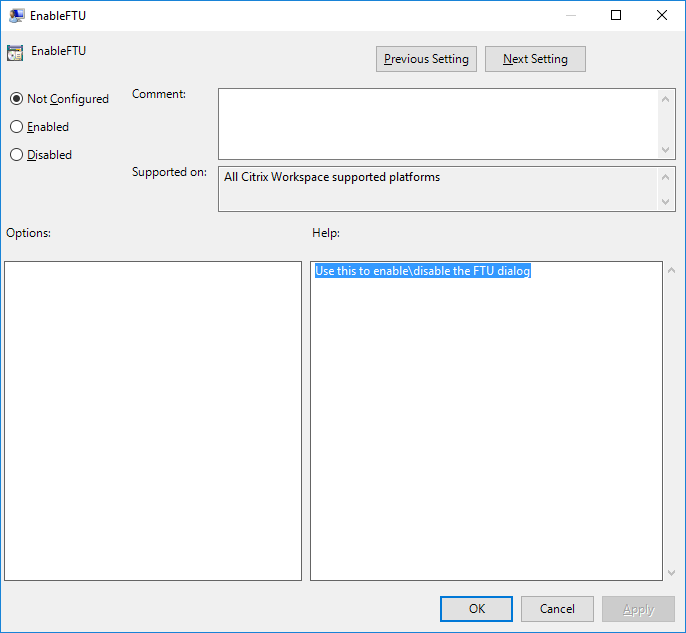
- Group Policy Object administrative template: To hide the Add Account option from the Citrix Workspace app installation wizard, disable EnableFTUpolicy under Self-Service node in Local Group Policy Object administrative template as shown below. This is a per-machine setting, hence the behavior is applicable for all users.
Domain Name Service name resolution
You can configure Citrix Workspace app for Windows that uses the Citrix XML Service to request a Domain Name Service (DNS) name for a server instead of an IP address.
Important:
Unless your DNS environment is configured specifically to use this feature, Citrix recommends that you do not enable DNS name resolution on the server.
By default, DNS name resolution is disabled on the server and enabled on the Citrix Workspace app. When DNS name resolution is disabled on the server, any Citrix Workspace app request for a DNS name returns an IP address. There’s no need to disable DNS name resolution on Citrix Workspace app.
To disable DNS name resolution for specific user devices:
If your server deployment uses DNS name resolution and you experience issues with specific user devices, you can disable DNS name resolution for those devices.
Caution:
Using the Registry Editor incorrectly might cause serious problems that require you to reinstall the operating system. We do not guarantee that problems resulting from the incorrect use of the Registry Editor can be solved. Use the Registry Editor at your own risk. Back up the registry before you edit it.
-
Add a string registry key xmlAddressResolutionType to
HKEY\_LOCAL\_MACHINE\Software\Wow6432Node\Citrix\ICA Client\Engine\Lockdown Profiles\All Regions\Lockdown\Application Browsing. -
Set the value to IPv4-Port.
-
Repeat for each user of the user devices.
Connect
Citrix Workspace app provides users with secure, self-service access to virtual desktops and applications, and on-demand access to Windows, web, and Software as a Service (SaaS) applications. Citrix StoreFront or legacy webpages created with Web Interface manage the user access.
To connect to resources using the Citrix Workspace UI
The Citrix Workspace app home page displays virtual desktops and applications that are available to the users based on their account settings (that is, the server they connect to) and settings configured by Citrix Virtual Apps and Desktops or Citrix DaaS administrators. Using the Preferences > Accounts page, you can configure the URL of a StoreFront server or, if email-based account discovery is configured, by entering the email address.
After connecting to a store, the self-service shows the tabs: Favorites, Desktops, and Apps. To launch a session, click the appropriate icon. To add an icon to Favorites, click the … icon and select Add to favorites.