This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Create a new deployment
-
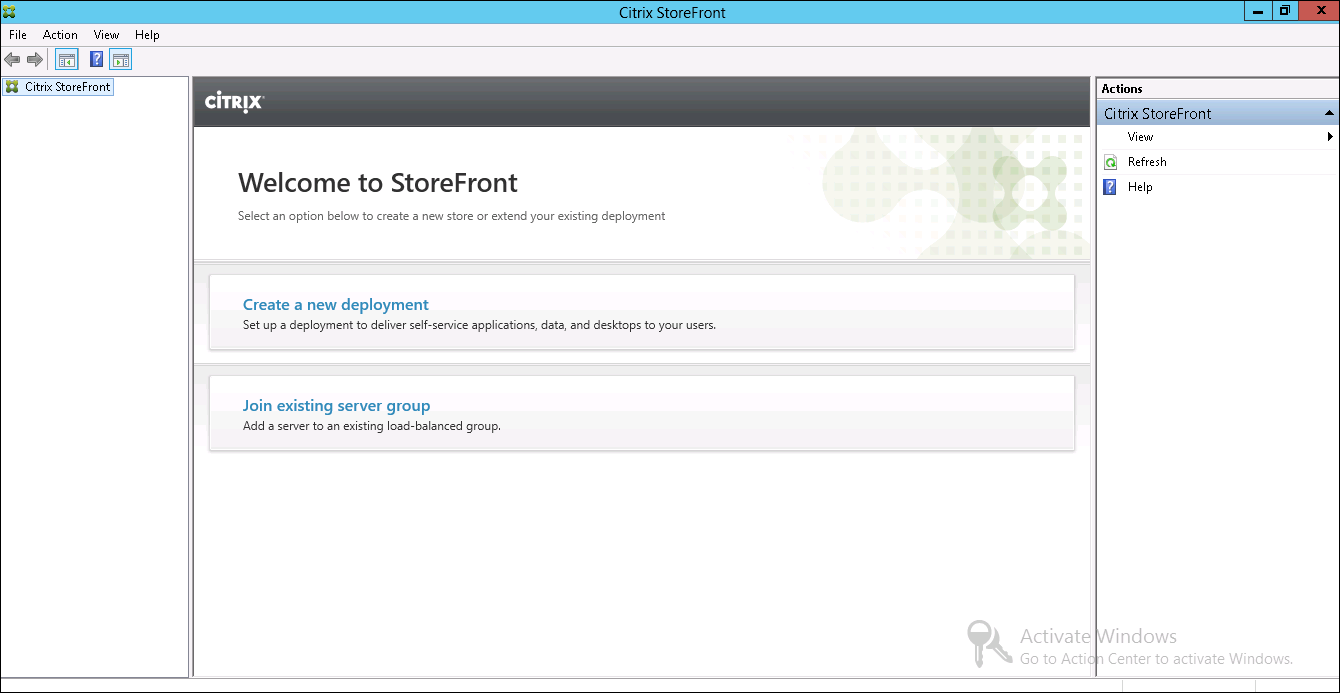
If the StoreFront management console is not already open after installation of StoreFront, open it.
-
In the results pane of the Citrix StoreFront management console, click Create a new deployment.
-
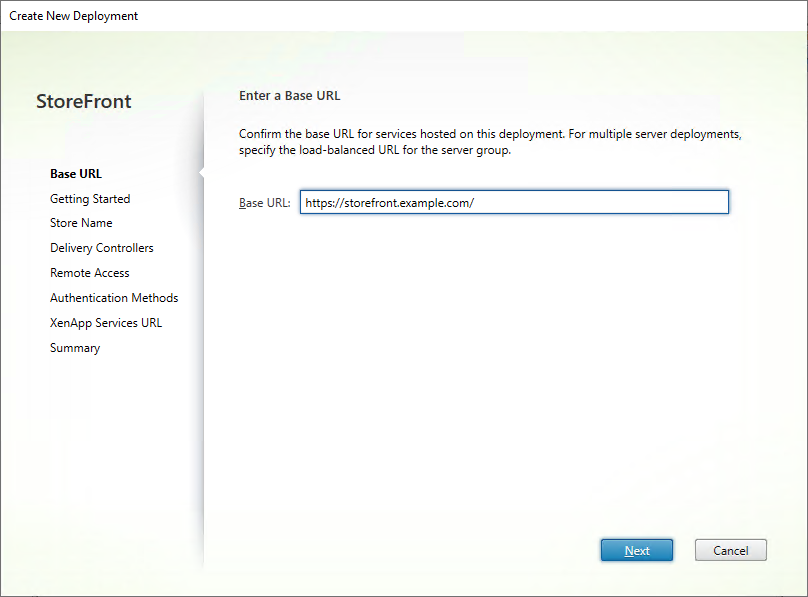
If there are multiple IIS sites, choose from the IIS site drop down which site you would like to use.
-
If using a single StoreFront server, enter the server URL Base URL. If you will be configuring multiple StoreFront servers behind a load balancer, enter the load balancing url as the Base URL.
If you have not yet set up your load balancing environment, enter the server URL. You can modify the base URL for your deployment at any time.
-
Click Next and configure your first store as described in Create Store.
-
Once you have completed all of the configuration steps, Click Create to create the deployment and the store.
-
StoreFront displays a summary of the store that it created. Click Finish.
Create a new deployment using PowerShell
To create a deployment using PowerShell, run cmdlet Add-STFDeployment.
Multiple Internet Information Services (IIS) websites
StoreFront allows you to deploy different Stores in different IIS websites per Windows server so that each store can have a different host name and certificate binding.
To create multiple web sites see Microsoft IIS documentation.
It is not possible to create multiple StoreFront deployments using the management console; you must use PowerShell. For example to create two IIS website deployments, one for applications and one for desktop use the following commands:
Add-STFDeployment -SiteID 1 -HostBaseURL "https://apps.example.com"
Add-STFDeployment -SiteID 2 -HostBaseURL "https://desktops.example.com"
<!--NeedCopy-->
Once you have enabled multiple sites, StoreFront disables the management console and it is not possible to return StoreFront to single site mode. You must perform all StoreFront configuration using the PowerShell modules and include the SiteID in each command.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.