Passcode device policy
Create a passcode policy in Citrix Endpoint Management based on your organization’s standards. You can require passcodes on users’ devices and can set various formatting and passcode rules. Create policies for iOS, macOS, Android, Android Enterprise, and Windows desktop/tablet. Each platform requires a different set of values, which are described in this article.
To add or configure this policy, go to Configure > Device Policies. For more information, see Device policies.
iOS settings
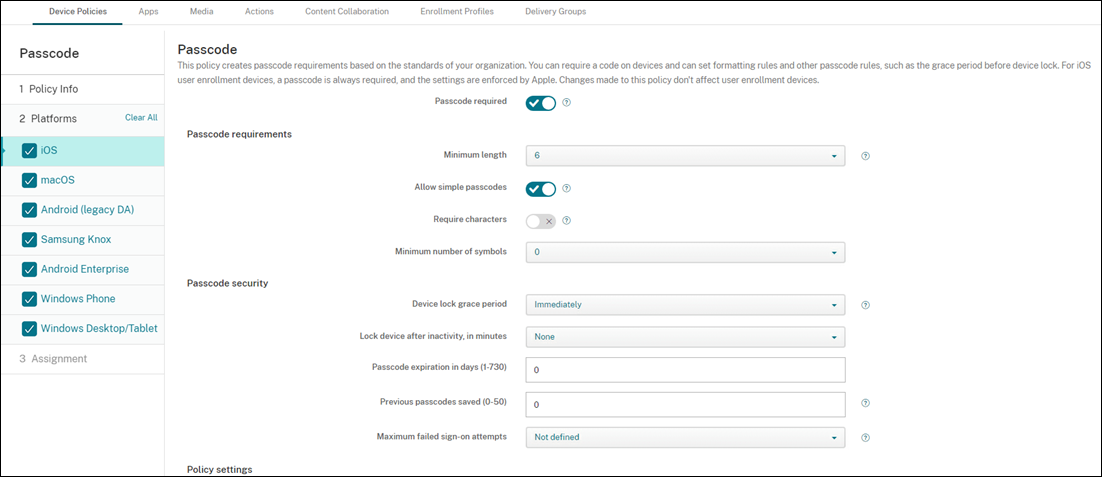
- Passcode required: Select this option to require a passcode and to display the configuration options for an iOS passcode device policy. The page expands to let you configure settings for passcode requirements, passcode security, and policy settings.
-
Passcode requirements
- Minimum length: Click the minimum passcode length in the drop-down list. The default is 6.
- Allow simple passcodes: Select whether to allow simple passcodes. Simple passcodes are a repeated or sequential set of characters. The default is On.
- Required characters: Select whether to require passcodes to have at least one letter. The default is Off.
- Minimum number of symbols: In the list, click the number of symbols the passcode must have. The default is 0.
-
Passcode security
- Device lock grace period: In the list, click the length of time before users must enter a passcode to unlock a locked device. The default is Immediately.
- Lock device after inactivity: In the box, enter the length of time a device can be inactive before it is locked. The value can be between 1 and 15 minutes. Set the value to None to disable the policy. The default is None.
- Passcode expiration in days (1-730): Type the number of days after which the passcode expires. Valid values are 1–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-50): Type the number of used passwords to save. Users are unable to use any password found in this list. Valid values are 0–50. The default is 0, which means users can reuse passwords.
-
Maximum failed sign-on attempts: In the list, click the number of times a user can fail to sign in.
- If you set this number higher than 6, after the sixth attempt, the device imposes a time delay between attempts. The time delay increases with each failed attempt. After the final attempt, all data and settings are securely erased.
- If you set the number at 6 or lower, the device is erased without implementing a time delay.
- If you select Not defined, after 6 attempts, the device imposes an increasing time limit between attempts but isn’t wiped.
The default is Not defined.
-
Policy settings
-
Remove policy: Choose a method for scheduling policy removal. Available options are Select date and Duration until removal (in hours)
- Select date: Click the calendar to select the specific date for removal.
- Duration until removal (in hours): Type a number, in hours, until policy removal occurs. Only available for iOS 6.0 and later.
-
Remove policy: Choose a method for scheduling policy removal. Available options are Select date and Duration until removal (in hours)
macOS settings
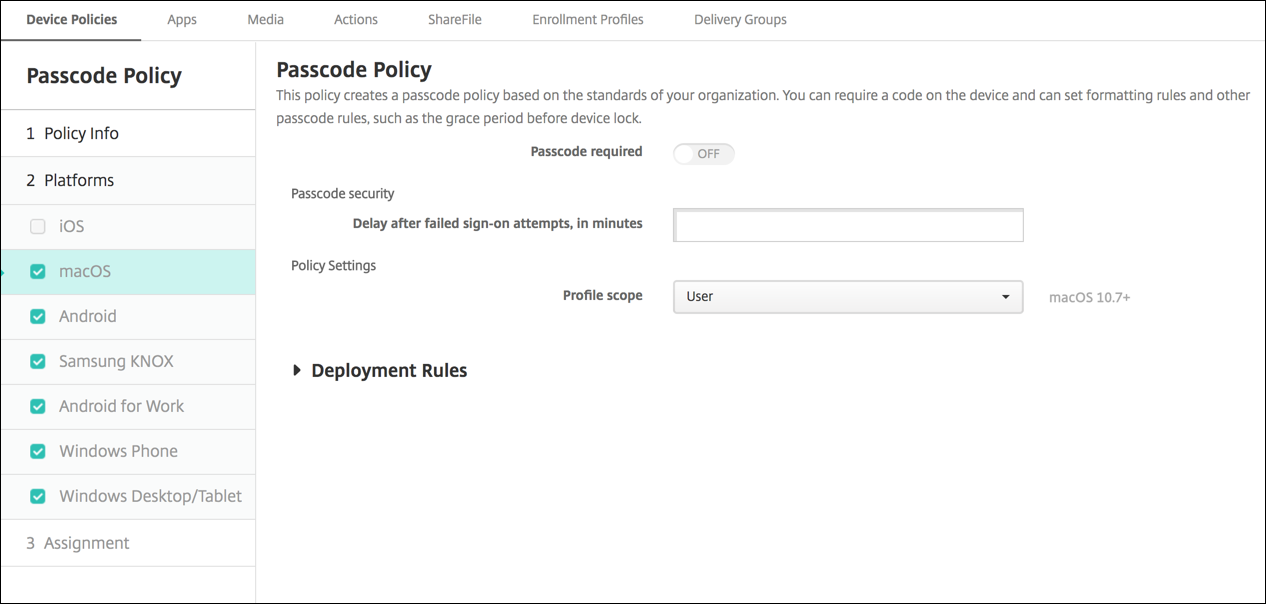
- Passcode required: Select this option to require a passcode and to display the configuration options for an iOS passcode device policy. The page expands to let you configure settings for passcode requirements, passcode security, and policy settings.
- If Passcode required is disabled, next to Delay after failed sign-on attempts, in minutes, type the number of minutes to delay before allowing users to reenter their passcodes.
- If you enable Passcode required, configure the following settings:
-
Passcode requirements
- Minimum length: Click the minimum passcode length in the drop-down list. The default is 6.
- Allow simple passcodes: Select whether to allow simple passcodes. Simple passcodes are a repeated or sequential set of characters. The default is On.
- Required characters: Select whether to require passcodes to have at least one letter. The default is Off.
- Minimum number of symbols: In the list, click the number of symbols the passcode must have. The default is 0.
-
Passcode security
- Device lock grace period: In the list, click the length of time before users must enter a passcode to unlock a locked device. The default is None.
- Lock device after inactivity: In the list, click the length of time a device can be inactive before it is locked. The value can be between 1 and 5 minutes. Set the value to None to disable the policy. The default is None.
- Passcode expiration in days (1-730): Type the number of days after which the passcode expires. Valid values are 1–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-50): Type the number of used passwords to save. Users are unable to use any password found in this list. Valid values are 0–50. The default is 0, which means users can reuse passwords.
-
Maximum failed sign-on attempts: In the list, click the number of times a user can fail to sign in.
- If you set this number higher than 6, after the sixth attempt, the device imposes a time delay between attempts. The time delay increases with each failed attempt. After the final attempt, the device locks.
- If you set the number at 6 or lower, the device locks without implementing a time delay.
- If you select Not defined, after 6 attempts, the device imposes an increasing time limit between attempts but does not lock.
The default is Not defined.
- Delay after failed sign-on attempts, in minutes: Type the number of minutes before the login window appears after a user reaches the maximum number of failed attempts.
- Force passcode reset: If Off, users don’t need to reset their passcode the next time they authenticate after their device receives this policy. The default is On.
-
Policy settings
-
Remove policy: Choose a method for scheduling policy removal. Available options are Select date and Duration until removal (in hours)
- Select date: Click the calendar to select the specific date for removal.
- Duration until removal (in hours): Type a number, in hours, until policy removal occurs.
- Allow user to remove policy: You can select when users can remove the policy from their device. Select Always, Passcode required, or Never from the menu. If you select Passcode required, type a passcode in the Removal passcode field.
- Profile scope: Select whether this policy applies to a User or an entire System. The default is User. This option is available only on macOS 10.7 and later.
-
Remove policy: Choose a method for scheduling policy removal. Available options are Select date and Duration until removal (in hours)
Android (legacy DA) settings
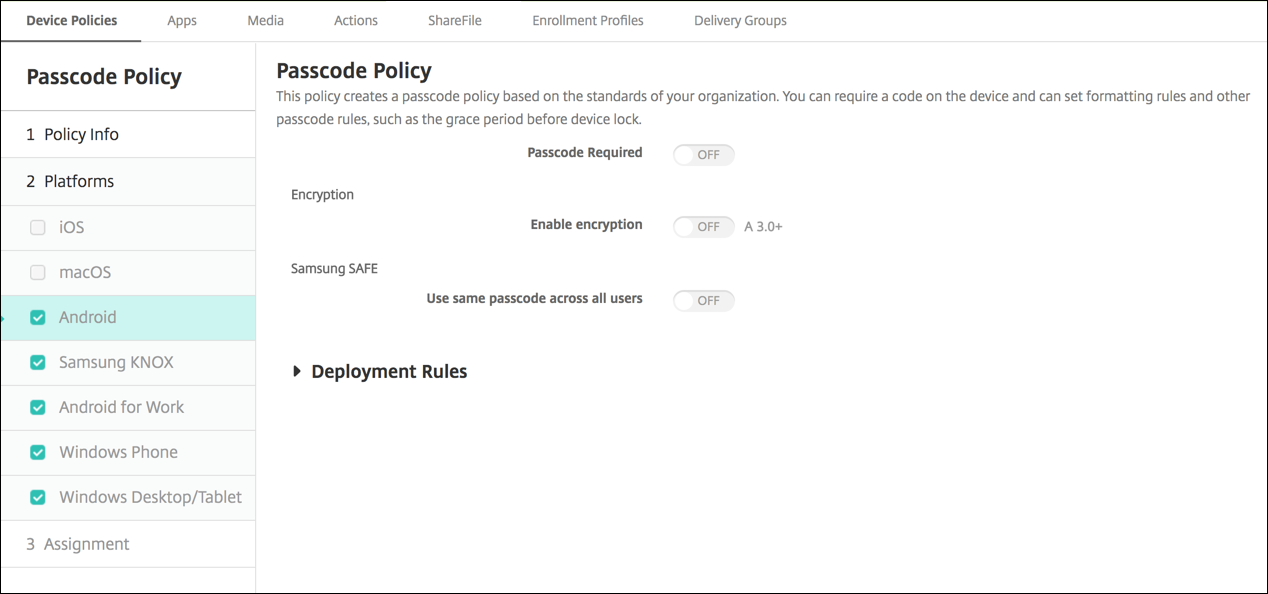
Note:
The default setting for Android is Off.
- Passcode required: Select this option to require a passcode and to display the configuration options for an Android passcode device policy. The page expands to let you configure settings for passcode requirements, passcode security, and encryption.
-
Passcode requirements
- Minimum length: Click the minimum passcode length in the drop-down list. The default is 6.
- Biometric recognition: Select whether to enable biometric recognition. If you enable this option, the Required characters field is hidden. The default is Off.
- Required characters: In the list, click No Restriction, Both numbers and letters, Numbers only, or Letters only to configure how passcodes are composed. The default is No restriction.
- Advanced rules: Select whether to apply advanced passcode rules. The default is Off.
- When you enable Advanced rules, from each of the following lists, click the minimum number of each character type that a passcode must have:
- Symbols: The minimum number of symbols.
- Letters: The minimum number of letters.
- Lowercase letters: The minimum number of lowercase letters.
- Uppercase letters: The minimum number of uppercase letters.
- Numbers or symbols: The minimum number of numbers or symbols.
- Numbers: The minimum number of numbers.
-
Passcode security
- Lock device after inactivity: In the list, click the length of time a device can be inactive before it is locked. The default is None
- Passcode expiration in days (1-730): Type the number of days after which the passcode expires. Valid values are 1–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-50): Type the number of used passwords to save. Users are unable to use any password found in this list. Valid values are 0–50. The default is 0, which means users can reuse passwords.
- Maximum failed sign-on attempts: In the list, click the number of times a user can fail to sign in successfully after which the device is wiped. The default is Not defined.
-
Encryption
-
Enable encryption: Select whether to enable encryption. The option is available regardless of the Passcode required setting.
To encrypt their devices, users must start with a charged battery and keep the device plugged in until encryption completes. The process can take an hour or more. If they interrupt the encryption process, they can lose some or all data on their devices. After a device is encrypted, the process can’t be reversed except by doing a factory reset, which erases all the data on the device.
-
Android Enterprise settings
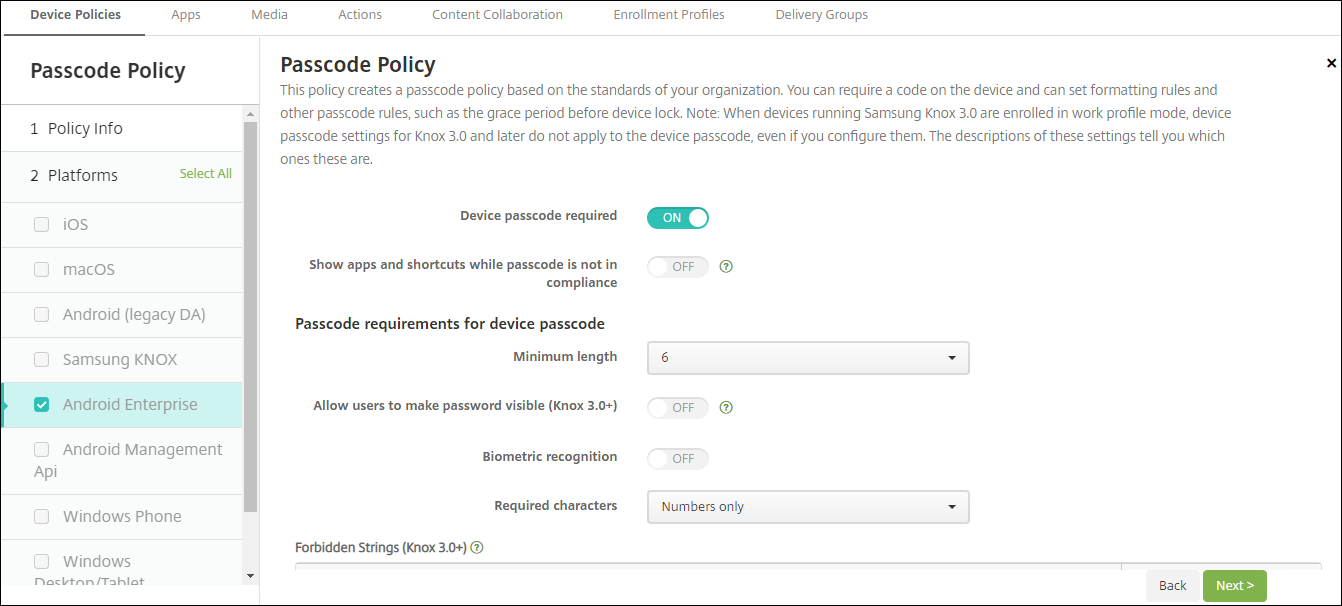
For Android Enterprise devices, you can require a passcode for the device or a security challenge for the Android Enterprise work profile or both.
- Device passcode required: Requires a passcode on the device. When this setting is On, configure the settings under Passcode requirements for device passcode and Passcode security for device passcode. Default is Off.
- Show apps and shortcuts while passcode is not in compliance: When this setting is On, apps and shortcuts on the device aren’t hidden, even when the passcode isn’t compliant. When this setting is Off, apps and shortcuts are hidden when the passcode isn’t compliant. If you enable this setting, Citrix® recommends you create an automated action to mark the device as out of compliance when the passcode isn’t in compliance. Default is Off.
-
Passcode requirements for device passcode:
- Minimum length: Specifies the minimum passcode length. The default is 6.
- Biometric recognition: Enables biometric recognition. If this setting is On, the Required characters field is hidden. The default is Off.
- Required characters: Specifies the types of characters required for passcodes. In the list, choose No Restriction, Both numbers and letters, Numbers only, or Letters only. Use No restrictions only for devices running Android 7.0. Android 7.1 and later don’t honor the No restrictions setting. The default is Both numbers and letters.
- Advanced rules: Applies advanced rules for the types of characters that can occur in passcodes. When this setting is On, configure the settings under Minimum number of and Maximum number of. This setting isn’t available for Android devices earlier than Android 5.0. The default is Off.
-
Minimum number of:
- Symbols: Specifies the minimum number of symbols. Default is 0.
- Letters: Specifies the minimum number of letters. Default is 0.
- Lowercase letters: Specifies the minimum number of lowercase letters. Default is 0.
- Uppercase letters: Specifies the minimum number of uppercase letters. Default is 0.
- Numbers or symbols: Specifies the minimum number of numbers or symbols. Default is 0.
- Numbers: Specifies the minimum number of numbers. Default is 0.
- Changed characters: For devices running Samsung Knox 3.0 and later that have a valid Knox license key configured. For fully managed devices only. This setting does not apply to devices enrolled as work profile devices. Specifies the number of characters users must change from their previous passcode. The default is 0.
-
Maximum number of: For devices running Samsung Knox 3.0 and later that have a valid Knox license key configured. For fully managed devices only. This setting does not apply to devices enrolled as work profile devices.
- Times a character can occur: Specifies the maximum number of times a character can occur in a passcode. The default is 0, which means there is no maximum limit.
- Alphabetic sequence length: Specifies the maximum length of an alphabetic sequence in a passcode. The default is 0, which means there is no maximum limit.
- Numeric sequence length: Specifies the maximum length of a numeric sequence in a passcode. The default is 0, which means there is no maximum limit.
-
Passcode complexity for device passcode (Android 12+):
- Apply passcode complexity: Requires a password with a complexity level defined by the platform, rather than a custom password requirement. Only for devices on Android 12+ and using Citrix Secure Hub 22.9 or later.
-
Complexity level: Predefined levels of password complexity.
- None: No password required.
-
Low: Passwords can be:
- A pattern
- A PIN with a minimum of four numbers
-
Medium: Passwords can be:
- A PIN with no repeating sequences (4444) or ordered sequences (1234), and a minimum of four numbers
- Alphabetic with a minimum of four characters
- Alphanumeric with a minimum of four characters
-
High: Passwords can be:
- A PIN with no repeating sequences (4444) or ordered sequences (1234), and a minimum of eight numbers
- Alphabetic with a minimum of six characters
- Alphanumeric with a minimum of six characters
Note:
For BYOD devices, passcode settings such as Minimum length, Required characters, Biometric recognition, and Advanced rules aren’t applicable on Android 12+. Use passcode complexity instead.
-
Passcode security for device passcode:
- Wipe the device after (failed sign-on attempts): Specifies the number of times a user can fail to sign on after which the device is fully wiped. Default is Not defined.
- Lock device after inactivity: Specifies the number of minutes a device can be inactive before it is locked. Set the value to 0 to disable the policy.
- Passcode expiration in days (1-730): Specifies the number of days after which the passcode expires. Valid values are 1–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-50): Specifies the number of used passwords to save. Users are unable to use any password found in this list. Valid values are 0–50. Default is 0, which means users can reuse passwords.
- Work profile security challenge: Require users to complete a security challenge for access to apps running in an Android Enterprise work profile. For devices running Android 7.0 and later. When this setting is On, configure the settings under Passcode requirements for work profile security challenge and Passcode security for work profile security challenge. Default is Off.
-
Passcode requirements for work profile security challenge:
- Minimum length: Specifies the minimum passcode length. The default is 6.
- Biometric recognition: Enables biometric recognition. If this setting is On, the Required characters field is hidden. The default is Off.
- Required characters: Specifies the types of characters required for passcodes. In the list, choose No Restriction, Both numbers and letters, Numbers only, or Letters only. Use No restrictions only for devices running Android 7.0. Android 7.1 and later don’t honor the No restrictions setting. The default is Both numbers and letters.
- Advanced rules: Applies advanced rules for the types of characters that can occur in passcodes. When this setting is On, configure the settings under Minimum number of and Maximum number of. This setting isn’t available for Android devices earlier than Android 5.0. The default is Off.
-
Minimum number of:
- Symbols: Specifies the minimum number of symbols. Default is 0.
- Letters: Specifies the minimum number of letters. Default is 0.
- Lowercase letters: Specifies the minimum number of lowercase letters. Default is 0.
- Uppercase letters: Specifies the minimum number of uppercase letters. Default is 0.
- Numbers or symbols: Specifies the minimum number of numbers or symbols. Default is 0.
- Numbers: Specifies the minimum number of numbers. Default is 0.
- Changed characters: For devices running Knox 3.0 and later that have a valid Knox license key configured. Specifies the number of characters users must change from their previous passcode. The default is 0.
-
Maximum number of: For devices running Knox 3.0 and later that have a valid Knox license key configured.
- Times a character can occur: Specifies the maximum number of times a character can occur in a passcode. The default is 0, which means there is no maximum limit.
- Alphabetic sequence length: Specifies the maximum length of an alphabetic sequence in a passcode. The default is 0, which means there is no maximum limit.
- Numeric sequence length: Specifies the maximum length of a numeric sequence in a passcode. The default is 0, which means there is no maximum limit.
-
Passcode complexity for work profile security challenge (Android 12+):
- Apply passcode complexity: Requires a password with a complexity level defined by the platform, rather than a custom password requirement. Only for devices on Android 12+ and using Citrix Secure Hub 22.9 or later.
-
Complexity level: Predefined levels of password complexity.
- None: No password required.
-
Low: Passwords can be:
- A pattern
- A PIN with a minimum of four numbers
-
Medium: Passwords can be:
- A PIN with no repeating sequences (4444) or ordered sequences (1234), and a minimum of four numbers
- Alphabetic with a minimum of four characters
- Alphanumeric with a minimum of four characters
-
High: Passwords can be:
- A PIN with no repeating sequences (4444) or ordered sequences (1234), and a minimum of eight numbers
- Alphabetic with a minimum of six characters
- Alphanumeric with a minimum of six characters
Note:
If you enable passcode complexity for a work profile, you must also enable it for the device.
-
Passcode security for work profile security challenge
- Wipe the container after (failed sign-on attempts): Specifies the number of times a user can fail to sign on, after which the work profile and its data are wiped from the device. Users must reinitialize the work profile after the wiping occurs. Default is Not defined.
- Lock container after inactivity: Specifies the number of minutes a device can be inactive before the work profile is locked. The value can be between 0 and 999 minutes. Set the value to 0 to disable the policy.
- Passcode expiration in days (1-730): Specifies the number of days after which the passcode expires. Valid values are 1–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-50): Specifies the number of used passwords to save. Users are unable to use any password found in this list. Valid values are 0–50. The default is 0, which means users can reuse passwords.
Windows Desktop/Tablet settings
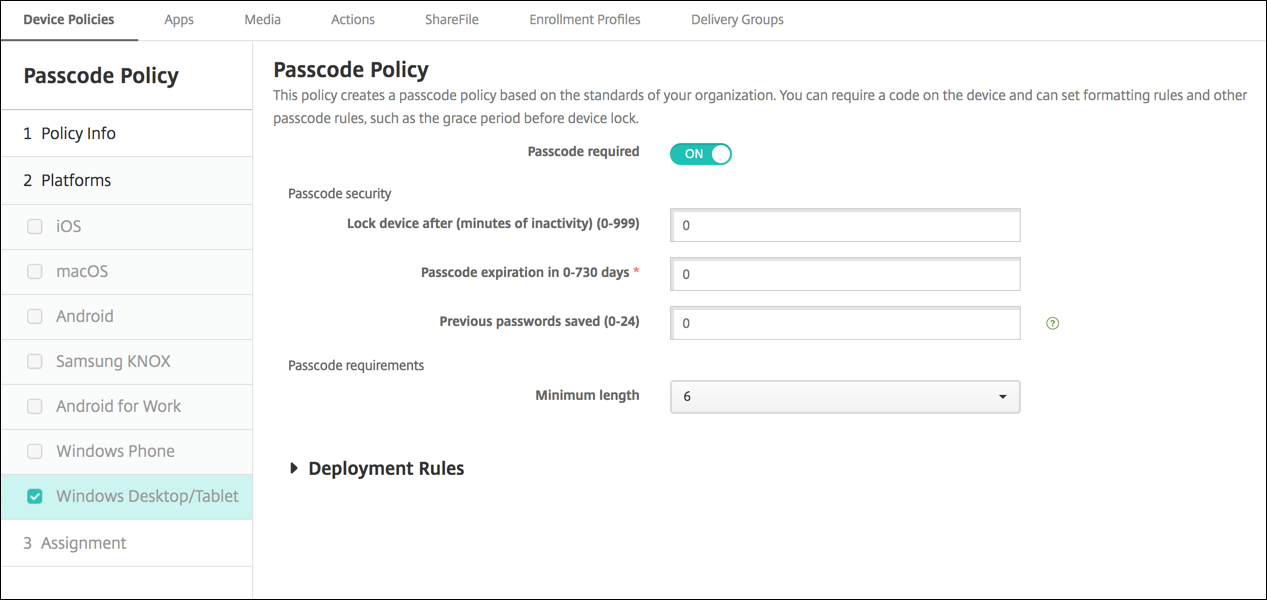
- Passcode required: Select this option to not require a passcode for Windows Desktop/Tablet devices. The default setting is On, which requires a passcode. The page collapses and the following options disappear when you disable this setting.
-
Passcode security
- Lock device after inactivity: Type the number of minutes a device can be inactive before it is locked. The default is 0.
- Passcode expiration in days (0-730): Type the number of days after which the passcode expires. Valid values are 0–730. The default is 0, which means the passcode never expires.
- Previous passwords saved (0-24): Type the number of used passcodes to save. Users are unable to use any passcode found in this list. Valid values are 1–24. Enter a number between 1 and 24 in this field. The default is 0.
-
Passcode requirements
- Minimum length: Click the minimum passcode length in the drop-down list. The default is 6.