What’s new history
We move sections about older Citrix Endpoint Management releases from What’s new to this article.
Citrix Endpoint Management 23.9.0
Note:
The documentation updates for Citrix Endpoint Management 23.9.0 has been rolled back because of product release rollback.
Citrix Endpoint Management 23.7.0
- Play Integrity API: The Play Integrity API replaces the soon to be deprecated SafetyNet Attestation API as per the deprecation timeline by Google. For more information and steps to enable this API, see Enable the Play Integrity API.
- Support for eSIM and dual SIM capabilities on iOS devices: Citrix Endpoint Management now supports eSIM and dual SIM capabilities on iOS devices. eSIM support allows you to retrieve information such as phone number, IMEI, ICCID from the iOS device and displays on the Citrix Endpoint Management UI. For more information about the device properties, see Device property names and values.
Citrix Endpoint Management 23.6.0
Support for macOS 14 devices: Citrix Endpoint Management now supports Apple devices that are using macOS 14. For more information, see the Operating system support list.
This release addresses several issues that help to improve overall performance and stability.
Citrix Endpoint Management 23.4.0
This release addresses several issues that help to improve overall performance and stability. No new features were added.
Citrix Endpoint Management 23.2.0
This release addresses several issues that help to improve overall performance and stability. No new features were added.
Citrix Endpoint Management 23.1.0
This release addresses several issues that help to improve overall performance and stability. No new features were added.
Citrix Endpoint Management 22.12.0
This release addresses several issues that help to improve overall performance and stability. No new features were added.
Citrix Endpoint Management 22.10.0
The following features are now rolling out to commercial customers. Releases to US government customers begin within three months. For feature differences between the commercial and US government offerings, see Citrix Endpoint Management service for US Government.
The Windows Information Protection policy has been removed. For more information, see Deprecation.
Support for Windows 11 22H2. Citrix Endpoint Management now allows IT admins to enroll Windows 11 22H2 devices with CEM using existing MDM functionality. See Windows Desktop and Tablet for more information on enrolling Windows devices.
macOS 13 is now supported. Citrix Endpoint Management now supports Apple devices using macOS version 13.
This release also addresses various issues that help to improve overall performance and stability.
Citrix Endpoint Management 22.9.0
Android 13 and iOS 16 support. Citrix Endpoint Management now supports Android 13 and iOS 16.
Processor Type and Processor Architecture. Windows devices on the CEM console now also display the Processor Type and Processor Architecture for each device.
This release also addresses various issues that help to improve overall performance and stability.
Citrix Endpoint Management 22.7.0
This release addresses various issues that help to improve overall performance and stability. No new features were added.
Fixes
Intermittently, selecting all three log types (Debug, Admin Audit, User Audit) to download under Troubleshooting and Support > Logs isn’t working. Only Debug logs are being downloaded. As a workaround, you can download each log separately, or open your browser in incognito mode to download all logs by marking all three checkboxes. [CXM-105334]
When creating a web link in Android Enterprise, an error occurs when trying to save the app with an icon. This is a Google services issue. As a workaround, save the app without uploading an icon. [CXM-105395]
Samsung Knox/SAFE policies are still active on enrolled devices even after deprecation, and can’t be disabled or configured. As a workaround, unenroll and reenroll the device. [CXM-104303]
Citrix Endpoint Management 22.6.0
Added new restriction policy to allow non-Google Play apps for all profiles on the device. See Restrictions device policy for more details.
Deprecated support for the Mobile Service Provider (MSP) interface. Added a new server property that removes the MSP interface from the console. See Server properties for details.
Deprecated support for Nexmo SMS gateway. Support for Nexmo SMS has been deprecated by adding a server property called deprecate.carrier.sms.gateway, which is set to True by default. Nexmo SMS has also been deprecated in the Self-Help Portal. See Notifications for details.
Selected apps can now communicate across work and personal profiles for Android Enterprise. A new toggle called Enable connected apps is available in the Restriction policy for Android Enterprise, allowing selected apps to use both work and personal data. See Restrictions policy for details.
Google is deprecating several APIs used for app categories and licenses in Citrix Endpoint Management:
- You now select apps to add rather than approve. See Managed app store apps.
- You now organize apps into collections rather than categories for Android Enterprise. See Organize apps (Android Enterprise).
- You no longer must approve MDX apps. See Add an MDX app.
- You can no longer disassociate app licenses from users. See Add apps.
Citrix Endpoint Management 22.5.0
Support for the ‘Allow auto-connect to WiFi Sense hotspots’ restriction policy for Windows 10 devices has been removed. For more information, see Windows Desktop/Tablet settings.
This release also addresses a number of issues that help to improve overall performance and stability.
Citrix Endpoint Management 22.4.0
Added a new option to the OS update device policy to set a freeze period where no OS updates can be installed. See OS Update device policy for details.
This release also addresses a number of issues that help to improve overall performance and stability.
Citrix Endpoint Management 22.3.0
Devices that have been inactive for a set period of time can now be automatically removed. (Preview) A new server property was added as a preview called Allows The Removal of Devices That Have Been Marked Inactive For A Specified Period Of Time, which will run a background job to remove devices that have been inactive for a specified time (in days). See Server properties for details.
This release also addresses a number of issues that help to improve overall performance and stability.
Citrix Endpoint Management 22.2.0
Added a note to the App inventory device policy that you must wait 24 hours for inventory results to appear when using a Windows 11 device. See App inventory device policy for details.
Added the ‘Default’ option to the ‘System update policy’ for Android Enterprise, allowing admins to restore the system update policy to its default value. See OS Update device policy for details.
Added new restriction policy to allow non-Google Play apps for all profiles on the device. See Restrictions device policy for more details.
Support for the following features has now been removed:
- RBAC role - shared and COSU devices enroller
- Android - Sony and HTC
- High Security enrollment mode
- Derived credentials
- SEAMS
- Windows Phone devices See Deprecation for more information.
Added new restriction policy to restrict copying, pasting, and importing files from a personal profile to a work profile. For more details, see Restrictions device policy.
Citrix Endpoint Management 22.1.0
This release addresses a number of issues that help to improve overall performance and stability. No new features were added.
Citrix Endpoint Management 21.12.0
Support for enrolling Apple Deployment Program enabled iOS devices by using Citrix Identity Provider. When deploying iOS devices through the Apple Deployment Program, you can now enable Apple Business Manager users to use Citrix Identity Provider as the identity provider to enroll their devices. This feature supports authentication with Azure Active Directory and with Okta through Citrix Cloud. For more information, see Deploy devices through the Apple Deployment Program.
Allow users to configure and use a proxy on iOS by default. Users with iOS devices can now use a proxy that they’ve configured on their device by default. To prevent the use of client-side proxies, change the client property for this feature to false. For more information about this setting, see Client properties.
Bluetooth device policy added for iOS devices. You can now configure a Bluetooth device policy to enable or disable Bluetooth on supervised iOS devices. For more information about this setting, see Bluetooth device policy.
Fixed issues in Citrix Endpoint Management 21.12.0
Using the Automatically Update Managed Apps policy for Android Enterprise fails to apply on devices when the CEM server is upgraded to 21.11.0. The policy failure impacts app updates on the device. As a workaround, an administrator can edit and save the policy to refresh the default values. [CXM-102446]
Citrix Endpoint Management 21.11.0
Configure a priority for automatically updating Android Enterprise managed apps. You can now specify whether Android Enterprise managed apps update automatically with a low priority or a high priority. You can also postpone automatic updates. For more information, see Automatically update managed apps device policy.
App notification device policy support for Grouping Type and Preview Type settings. With these two settings, you can control how app notifications are grouped and previewed on supervised iOS devices. For more information, see Apps notifications device policy.
App attributes device policy supports more iOS app attributes. You can now specify the following attributes for apps installed on iOS devices:
- Removable app: Specify whether an app is removable by users when it’s a managed app. Applies to iOS 14 and later.
Attributes for the associated domains feature:
- Associated Domains: Specify the associated domains to add to an app. Applies to iOS 13 and later.
- Enable associated domain direct download: Specify whether to enable claimed site association verification at the domains directly. Applies to iOS 14 and later.
For more information, see App attributes device policy.
Fixed issues in Citrix Endpoint Management 21.11.0
Intermittently, when you click Export Configuration Script from the Settings > NetScaler Gateway page, you receive a corrupt CSV file. As a workaround, download the configuration script while adding or editing a NetScaler Gateway configuration. [CXM-100908]
Citrix Endpoint Management 21.10.1
Lock device after inactivity extension. The maximum amount of device inactivity time before the device locks has been increased to 15 minutes. For more information, see Passcode device policy.
Added the restriction setting for pasting content from iOS apps. The restrictions device policy now supports Require managed pasteboard for iOS. With this restriction setting, you can block or allow the pasting of content from managed apps to unmanaged apps, and the opposite way.
This setting applies to iOS 15 and later. For more information, see Restrictions device policy for iOS.
Fixed issues in Citrix Endpoint Management 21.10.1
The network policy fails to deploy to iOS and macOS devices using WPA2 and WPA3 network security types. [CXM-96166]
Citrix Endpoint Management 21.10.0
Assign custom roles for cloud administrators in Citrix Cloud. New Citrix Endpoint Management customers onboarded after October 4, 2021 can now assign custom roles to cloud administrators in Citrix Cloud. Before, you had to assign custom roles in Citrix Endpoint Management. This feature lets you perform your administrator-related customizations without having to switch between Citrix Cloud and Citrix Endpoint Management. In addition, the COSU devices enroller and Shared devices enroller templates were removed from Citrix Endpoint Management. COSU devices enroller is now handled through enrollment profiles and Shared devices enroller is handled at the platform level with kiosk mode or Citrix Launcher.
Support for Windows 11 devices. You can now use Citrix Endpoint Management to manage Windows 11 devices. For more information, see the Operating system support list.
iOS User Enrollment mode is now available as a public preview. You can now take advantage of Apple User Enrollment features on iOS and iPadOS devices. User Enrollment integrates Managed Apple IDs to create a user identity on devices. For more information about User Enrollment, see Managed Apple IDs.
Updated maximum value for tracking iOS device location. You can now configure the location policy to track the location of an iOS device for up to 10 hours. See Location device policy.
Fixed issues in Citrix Endpoint Management 21.10.0
When updating an administrator role in the Citrix Cloud console, the change is not reflected in the Citrix Endpoint Management console. This issue is strictly a user interface issue and does not impact any functionality. Only customers onboarded in version 21.10.0 or later are affected. [CXM-101044]
When creating an enrollment profile for Android devices to enroll in the work profile on corporate-owned devices mode, you must enable the BYOD work profile setting. If you don’t enable this setting, the devices fail to enroll. [CXM-100418]
Citrix Endpoint Management 21.9.1
Configure Azure AD or Okta as an identity provider to enroll and manage user devices without a Cloud Connector (Preview). If you configure an identity provider through Citrix Cloud, you don’t need a Cloud Connector to establish communication between Citrix Endpoint Management and Citrix Cloud. Citrix Endpoint Management still requires a Cloud Connector for the following:
- LDAP
- PKI Server
- Internal DNS queries
- Citrix Virtual Apps™
For more information about this feature, see Identity provider authentication.
Support for iOS 15 and macOS 12 devices. You can now use Citrix Endpoint Management to manage iOS 15 and macOS 12 devices. For more information, see the Operating system support list.
Always-on VPN for Android Enterprise. You can now enable an always-on VPN for Android Enterprise devices. You can choose to enable a lockdown feature as well. Apps require a VPN connection to access the network unless you exclude them from the lockdown. For more information, see VPN device policy.
Fully managed Android 11+ devices enroll in work profile on corporate-owned devices mode. The new mode further separates the personal and work profiles on a device. This change offers an organization greater control on the managed profile and offers users more privacy on their personal profile. For more information, see Android Enterprise.
Ability to set global consent for client apps. You can now set global consent so that users don’t need to provide consent on each device. For details, see Configure Citrix Endpoint Management for Azure AD compliance management.
Azure AD permissions changes now detected. When a change occurs in Azure AD permissions, Citrix Endpoint Management now warns automatically about the change so you can approve it using the Azure AD compliance management setting. Follow the consent link and click Approve to accept the changes. Previously, you had to initiate this approval manually. For more information, see Configure Citrix Endpoint Management for Azure AD compliance management.
Fixed issues in Citrix Endpoint Management 21.9.1
If you add deployment rules to a delivery group, any new or existing deployment rules at the resource level (policies, apps, actions) no longer apply. [CXM-98013]
The Export Data feature of Citrix Endpoint Management doesn’t export complete sets of data. Use these workarounds to retrieve data about managed devices:
- Export data from the console by navigating to Analyze > Reporting > Device Enrollment.
- Export data by using the reporting API. For information about the reporting API, see the developer documentation. [CXM-99906]
If accessing Citrix Endpoint Management through Citrix Cloud, adding an enterprise app for macOS causes an authorization error to occur. As a workaround, contact support and request direct access to your Citrix Endpoint Management console. You can then add enterprise apps for macOS devices. [CXM-100046]
Citrix Endpoint Management 21.9.0
Chrome OS credential policy settings (preview). Credential policy settings are now available for Chrome OS. Chromebook devices can use the credential policy to take advantage of the Chrome operating system’s built-in certificate management. Administrators can upload a certificate authority’s private certificate for signing and issuing the client certificates. This certificate allows Citrix Endpoint Management to create and push certificates to Chromebook devices. For more information, see Credentials device policy.
Fixed issues in Citrix Endpoint Management 21.9.0
After enrolling an iOS 15 or macOS 12 device, the MDM Configuration profile shows as “Not Verified.” [CXM-98526]
Citrix Endpoint Management 21.8.0
Support for Android 12. Citrix Endpoint Management now supports Android Enterprise device updates to Android 12. For a summary of security and privacy benefits, see the Android documentation.
Support for editing JSON output when you generate a QR code for Android Enterprise Enrollment. When generating a QR code for Android Enterprise enrollment, you can now add enrollment information to the QR code by editing the JSON output directly. For more information, see Android Enterprise.
Update managed optional apps automatically. Managed optional apps now receive updates automatically. This feature includes optional enterprise apps, optional Volume Purchase apps, and optional public apps. For information about Volume Purchase apps, see Add an Apple Volume Purchase account.
Use Active Directory to authenticate users when they connect their macOS devices to Wi-Fi networks. Citrix Endpoint Management now supports authentication with Active Directory for macOS devices each time they connect to the configured Wi-Fi network. This feature applies only to the following security types:
- WEP Enterprise
- WPA Enterprise
- WPA2 Enterprise
- Any (Enterprise)
For more information, see Network device policy.
Clone a delivery group to use as the basis for a new delivery group. This feature lets you copy a complex delivery group that includes multiple policies, apps, and actions. You can then edit the copy, such as adding enrollment profiles or a new set of Active Directory users. For details, see Clone a delivery group.
Azure AD device compliance general availability. Citrix Endpoint Management now supports Azure AD device compliance through Azure AD conditional access policies. For more information on this feature, see Integrate with Azure AD Conditional Access.
Fixed issues in Citrix Endpoint Management 21.8.0
Users with certain special characters in their user name or password can’t enroll. [CXM-98777]
Citrix Endpoint Management 21.7.1
This release has enhancements that help improve overall performance and stability.
Fixed issues in Citrix Endpoint Management 21.7.1
When configuring an identity provider for Citrix Endpoint Management, if you don’t configure the optional fields, end users can’t authenticate. [CXM-97394]
Citrix Endpoint Management 21.7.0
If you authenticate with Azure Active Directory or Okta through Citrix Cloud, you can now create different enrollment profiles for iOS and Android devices. When you configure Azure Active Directory or Okta as authentication methods through Citrix Cloud, Citrix Endpoint Management supports a number of enrollment profiles with different enrollment types. For more information, see Enrollment profiles.
Automatically tag devices by device type and enrollment mode. If you enable the server property enable.device.tagging, Citrix Endpoint Management tags any newly enrolled device. You can use device tags to deploy policies and apps or configure delivery groups. Citrix Endpoint Management applies tags to devices for the following:
- BYOD tags
- iOS User Enrollment
- Android Enterprise work profile
- Corporate tags
- Android Enterprise fully managed corporate devices
- Bulk enrollment
- Apple Business Manager devices
- Apple School Manager devices
- Windows AutoPilot devices
- Android Enterprise bulk enrollment
For more information, see Server properties
For Citrix Endpoint Management customers with the workspace experience enabled: Citrix Endpoint Management supports authentication with Azure Active Directory, Okta, and an on-premises NetScaler Gateway for users enrolling in MDM through the Citrix Workspace app. For more information, see Authentication with Azure Active Directory through Citrix Cloud, Authentication with Okta through Citrix Cloud, and Authentication with an on-premises NetScaler Gateway through Citrix Cloud.
Citrix Endpoint Management 21.6.0
Renamed the Wi-Fi device policy to network device policy. We renamed the Wi-Fi device policy to “network device policy” to accommodate Ethernet support for macOS. For macOS, in addition to the Wi-Fi option, you now have the following Ethernet options:
- Global Ethernet
- First Active Ethernet
- Second Active Ethernet
- Third Active Ethernet
- First Ethernet
- Second Ethernet
- Third Ethernet
For more information, see Network device policy.
Apple Business Manager (ABM) and Delete All Users support for Shared iPads. Users can now sign in to Shared iPads using ABM accounts. The Delete All Users security action is also available for Shared iPads. For more information, see Shared iPads.
Upload certificates to iOS devices in bulk with the Citrix Endpoint Management REST API. If uploading certificates one at a time isn’t practical, use the Citrix Endpoint Management Server REST API to upload the certificates to iOS devices in bulk.
- Configure an iOS VPN device policy with the connection type Always on IKEv2.
- Select Device Certificate Based on Device Identity as the device authentication method.
- Select the Device identity type to use.
- Bulk import your device certificates with the REST API.
For information about configuring the VPN device policy, see VPN device policy. For information about importing certificates in bulk, see Upload certificates to iOS devices in bulk with the REST API.
Deprecation of full tunnel mode for iOS apps. From this release onward, MDX no longer supports the full tunnel mode in the Citrix mobile productivity apps for iOS. The following options are removed from the Network access app policy:
- Use Previous Settings
- Tunneled - Full VPN
- Tunneled - Full VPN and Web SSO
If you’re using the Tunneled - Full VPN or the Tunneled - Full VPN and Web SSO policies, you must switch to the Tunneled - Web SSO policy. Your emails don’t synchronize if you continue to use the deprecated policies. For more information, see SSO and proxy considerations for MDX apps.
More informative certificate selection. When you configure a Microsoft PKI, generic PKI, credential policy, or credential providers, the certificate menu provides more helpful information to distinguish certificates. This information includes:
- The certificate name
- The date from which the certificate is valid
- The date to which the certificate is valid
- The certificate serial number
Citrix Endpoint Management 21.5.1
This release has enhancements that help improve overall performance and stability.
Citrix Endpoint Management 21.5.0
Citrix Secure Hub APNs certificate renewal. The Citrix Secure Hub Apple Push Notification Service (APNs) certificate for Citrix Endpoint Management expires on June 17, 2021. This update renews the Citrix Secure Hub APNs certificate, which will expire on May 7, 2022.
FIPS 140-2 compliance. Citrix Endpoint Management server-side components are now FIPS 140-2 compliant. For more information, see FIPS 14-2 compliance.
Fixed issues in Citrix Endpoint Management 21.5.0
We have a new “Get Devices by Filters” API which resolves issues in the prior “Get Devices by Filters” APIs and returns paginated results for up to 100 devices at a time. See the section “3.16.3 Get Devices by Filters” in the Public API for REST Services PDF. [CXM-92791]
When you use a package ID to search for a Google Play app to add to the Citrix Endpoint Management console, the mandatory Name field displays as empty. You can still enter the app name manually. [CXM-93655]
Citrix Endpoint Management 21.4.0
Citrix received verification for the Google Android Enterprise Advanced Management Solution Set. See Citrix Endpoint Management earns new Android Enterprise verification.
Integrate with Azure AD Conditional Access (Preview). You can now configure Citrix Endpoint Management to apply Azure AD Conditional Access support to Office 365 applications. This feature, now in Preview, lets you deploy the Zero Trust methodology to device users when deploying Office 365 applications. You can use device state, risk score, location, and device protections to define access to the Office 365 applications on managed Android Enterprise and iOS devices. For information, see Integrate with Azure AD Conditional Access.
Use Android device property rules to manage the deployment of a delivery group to Android Enterprise devices. If you enroll multiple Android Enterprise devices to the same user, you can now deploy delivery group resources based on the device enrollment profile or the application package ID. Within the delivery group, use device properties for the Android platform to create advanced rules for new or existing Android Enterprise devices. For more information, see Add a delivery group.
Support for rotating administrator password for macOS devices enrolled through Apple Deployment Program. When adding your Apple Business Manager account to Citrix Endpoint Management, you can specify settings to create an administrator account on the macOS device. Citrix Endpoint Management automatically creates the administrator account on the device during the Setup Assistant workflow. Users then sign in to their macOS device with the specified information. Citrix Endpoint Management now supports rotating the password of that administrator account for enhanced security. For more information, see Deploy devices through the Apple Deployment Program.
The new AutoDiscovery service configuration through Citrix Cloud. The AutoDiscovery service is now hosted in Citrix Cloud. Citrix migrated all existing AutoDiscovery service configurations without a disruption in service. To access the new AutoDiscovery service or change your configuration, go to https://adsui.cloud.com (commercial) or https://adsui.cem.cloud.us/ (government). For more information, see Set up the AutoDiscovery service for Citrix Endpoint Management.
In the new AutoDiscovery service configuration, use the MAM Port setting instead of NetScaler Gateway FQDN to direct MAM traffic to your data center. If you enter a fully qualified domain name along with the port of your NetScaler Gateway, the client device uses the configuration from the MAM Port setting.
When you go to https://adsui.cloud.com (commercial) or https://adsui.cem.cloud.us/ (government) to access the new AutoDiscovery service user interface, an ad blocker can prevent the site from opening. To access the AutoDiscovery service, disable the ad blocker for the entire website.
Added settings to Android Enterprise restrictions. We added two settings to all enrollment modes to more closely align with Google settings and to simplify configuration.
- Allow Bluetooth sharing: If unselected, users can’t establish outgoing Bluetooth sharing on their device.
- Allow app uninstall: Allows users to uninstall apps from within the Managed Google Play Store.
Also, we moved the Allow over-the-air upgrade setting from the Restrictions policy to the OS update policy.
For more information about these changes, see Restrictions device policy and OS Update device policy.
Support for delivering MDX apps from a content delivery network (CDN). CDN support is now available for MDX apps. To speed the delivery of app downloads, CDN sends those MDX apps to user devices located near an Citrix Endpoint Management server. That use of the CDN reduces app download times. To get started, see Deliver MDX apps from the Citrix CDN.
Fixed issues in Citrix Endpoint Management 21.4.0
Enterprise apps fail to install on devices running macOS 11.0 or later, but the Citrix Endpoint Management console shows that they have installed successfully. [CXM-90839]
Citrix Endpoint Management 21.3.0
Streamlined flow for adding Android Enterprise apps to Intune managed environments. You can now add Android Enterprise apps to the Citrix Endpoint Management console and the Intune console at the same time. For more information about this workflow, see Add Android Enterprise apps to the Citrix Cloud Library.
Generate a QR code for Android Enterprise enrollment. Citrix Endpoint Management can now generate QR codes for Android Enterprise enrollment. By using the Citrix Endpoint Management console to generate a QR code for enrollments, you avoid external sites that can be malicious. For more information about generating QR codes, see Create a QR code.
Bootstrap token support for macOS devices. Citrix Endpoint Management now supports escrowing bootstrap tokens for macOS devices. A bootstrap token is generated during the Setup Assistant workflow. One benefit of escrowing bootstrap tokens with Citrix Endpoint Management is that remote accounts can be enabled for FileVault and able to unlock the FileVault volume. For more information, see Bootstrap token.
Citrix Endpoint Management 21.2.0
Updated Citrix Launcher app lets you restrict user access to one app or a small set of apps on Android Enterprise devices. You can also optionally upload a custom logo image for the Citrix Launcher icon and specify a password that users must enter to exit the app. For more information, see Citrix Launcher.
New Setup Assistant options for iOS and macOS. You can now specify more setup screens to skip when users set up iOS or macOS devices.
- iOS
- Restore completed: Prevents users from seeing whether a restore completes during setup. For iOS 14.0 and later.
- Update completed: Prevents users from seeing whether a software update completes during setup. For iOS 14.0 and later.
- macOS
- Accessibility: Prevents the user from hearing Voice Over automatically. Only available if the device is connected to Ethernet. For macOS 11 and later.
- Biometric: Prevents the user from setting up Touch ID and Face ID. For macOS 10.12.4 and later.
- True Tone: Prevents users from setting up four-channel sensors to dynamically adjust the white balance of the display. For macOS 10.13.6 and later.
- Apple Pay: Prevents users from setting up Apple Pay. If this setting is cleared, users must set up Touch ID and Apple ID. Make sure that the Apple ID and Biometric settings are cleared.
- Screen Time: Prevents users from enabling Screen Time. For macOS 10.15 and later.
For more information about configuring setup options, see Deploy devices through the Apple Deployment Program.
macOS PKG file uploads now limited by upload time instead of file size. You can now upload larger PKG files such as Microsoft Office for macOS devices. Citrix Endpoint Management has removed the previous file size limit of 0.5 GB and instead limits file upload time. By default, you must complete your upload within 100 seconds. For more information, see Add an enterprise app.
Citrix Endpoint Management no longer supports weak cryptographic algorithms for certificate-based authentication. When you create a certificate signing request for a credential provider in the Citrix Endpoint Management console, choose a stronger cipher. For the list of removed signature algorithms, see Deprecation.
Fixed issues in Citrix Endpoint Management 21.2.0
When creating a user, two PKI certificates are created for the same user. The user may not be able to access internal websites through Citrix Secure Web or receive email through Citrix Secure Mail. [CXM-88134]
When adding an RBAC role, Citrix Endpoint Management becomes unresponsive after these actions:
- Apply a permission to a specific user group, and then clear an Active Directory domain checkbox.
- Select an authorized access item or console feature item repeatedly. [CXM-90861]
Citrix Endpoint Management 21.1.1
Note:
As the result of an outage, your delivery group history might have been removed. Delivery group history collection has resumed.
New look and feel. Citrix has updated the Citrix Endpoint Management console with new colors, fonts, toggles, and other formatting changes. Some new UI elements may not load correctly until you clear your browser cache and refresh.
App uninstall policy now available for macOS. You can now remove managed apps from macOS devices by using the App uninstall policy. For more information, see the App uninstall device policy.
Enhancements for a delivery group. You can now manage the deployment of a delivery group using device property rules along with the existing user property rules. If you enroll multiple devices to the same user, you can now create advanced filters within the delivery group based on the unique device properties, such as device ownership, model, OS version, compliance, and others. For more information, see Add a delivery group.
APIs are now available for creating reports. The Reporting APIs are read-only APIs using JSON as the query language. The APIs allow you to do the following:
- Create robust compliance reports on application versioning, device OS patching, Android DA (Legacy) to Android Enterprise migration progress, and more.
- Issue custom queries against your cloud database in a secure way.
- Export data about your cloud service, such as lists of applications, devices, users, enrollments, and software.
- Save information in JSON or CSV format.
These APIs are the cloud equivalent to having access to an on-premises database and running custom SQL queries. To learn more about the reporting APIs, see the documentation on the Citrix Developer portal.
Citrix Endpoint Management 21.1.0
Authenticate to the REST API with the Citrix Cloud API keys. You can now generate the unique client ID and client secret to access the REST API using your Citrix Cloud account. For more information, see REST APIs.
Reorganization of Android Enterprise restrictions. The restriction settings for Android Enterprise have been reorganized for clarity. Sometimes, minor changes to setting names have been made. For more information about the reorganization, see Android Enterprise settings.
Citrix Endpoint Management 20.12.0
This release has enhancements that help improve overall performance and stability.
Use Azure Active Directory (AAD) or Okta to authenticate when enrolling Android Enterprise devices (Preview). The ability to use AAD or Okta as authentication methods when enrolling Android Enterprise devices is now available as a preview. This feature supports BYOD and fully managed modes in addition to enhanced enrollment profiles. For more information about using Okta for single sign-on, see Authentication with Okta through Citrix Cloud. For more information about using AAD for single sign-on, see Authentication with Azure Active Directory through Citrix Cloud.
Installing enterprise and Volume Purchase apps to macOS devices as managed apps. The Force app to be managed setting is now available for macOS. If you want to manage an app that is installed but not yet managed, turn on the setting for that app and deploy the app to the devices. The app automatically installs as a managed app. Users don’t receive any prompts. If you deploy an app to devices where the app doesn’t exist, the app is installed as a managed app regardless of the state of the setting. For more information, see Add an enterprise app and Configure the Volume Purchase apps.
Fixed issues in Citrix Endpoint Management 20.12.0
The default notification templates use the name XenMobile instead of Citrix Endpoint Management. [CXM-60513]
Android Enterprise users might not receive apps added after they enroll. [CXM-82840]
BitLocker encryption recovery keys for Windows devices aren’t available in the Self-Help Portal (SHP). When you enable the OS drive recovery setting in the BitLocker device policy and encrypt an enrolled Windows device using BitLocker, the recovery keys don’t appear in the SHP. As a workaround, open a CEMHELP ticket and request an SRE discussion with the product management. [CXM-89333]
Citrix Endpoint Management 20.11.0
Removal of Android TouchDown support. DigiCert stopped supporting Android TouchDown from July 2, 2018. All Android TouchDown options have been removed from the Citrix Endpoint Management console.
Citrix Endpoint Management 20.10.1
Limit methods to access the REST API. By contacting Citrix support, you can make sure that only Citrix Cloud accounts can access the REST API. Local administrator accounts can’t access the API with this feature enabled. See REST APIs.
Fixed issues in Citrix Endpoint Management 20.10.1
Users don’t receive enrollment invitation emails. [XMHELP-3081]
If you configure Citrix Endpoint Management as a discretionary certificate authority, the VPN, network, and other credentials device policies don’t deploy. [XMHELP-3093]
Citrix Endpoint Management 20.10.0
Allow static or dynamic MAC addresses. As part of the network policy, iOS and iPadOS devices can now use a different MAC address each time they connect to the configured Wi-Fi network. You can also choose to have the MAC address remain static. However, using a dynamic MAC address makes it more difficult to identify the device consistently, enhancing privacy. See Network policy.
Use Azure Active Directory (AAD) or Okta as identity platforms. The ability to use AAD or Okta as your identity platform is now available as a public preview. Users enrolling through Citrix Secure Hub can use their AAD or Okta credentials. To use either of these methods for single sign-on, configure NetScaler Gateway for certificate-based authentication. For more information about using Okta for single sign-on, see Authentication with Okta through Citrix Cloud. For more information about using AAD for single sign-on, see Authentication with Azure Active Directory through Citrix Cloud.
Use UPN or email for Okta authentication. When you set up Okta as your identity platform, you can allow users to log in with their UPN or their email address. See Single sign on with Okta.
Fixed issues in Citrix Endpoint Management 20.10.0
Users don’t receive enrollment invitation emails. [XMHELP-3081]
Citrix Endpoint Management 20.9.1
Redeploy assigned policies to iOS and Android devices. If the user removes a policy, you can now redeploy the policy to iOS and Android devices. Go to Manage > Devices > Assigned Policies, select the policy, and click Reset status to change the deployment status to pending. For more information, see Supported enrollment methods for iOS and Supported enrollment methods for Android devices.
The FileVault device policy now allows for key storage and rotation. Using the FileVault device policy, you can now store personal recovery keys within Citrix Endpoint Management. End users can request their recovery key using the Self-Help Portal, and administrators can rotate personal recovery keys using security actions. For more information about the new features, see FileVault device policy.
More granular control over macOS update options. The OS Update device policy now allows you to control how macOS devices check for, download, and install updates. You can also configure the types of software updates allowed. For more information about the new settings, see OS Update device policy.
Fixed issues in Citrix Endpoint Management 20.9.1
The MDM certificate on some iOS devices doesn’t renew. In that case, the Manage > Devices > Device details > Certificates page shows an Apple MDM certificate that is close to expiration. The Citrix Endpoint Management server log includes the message The new MDM payload does not match the old payload. We recommend that you re-enroll the affected devices to resolve this issue. Citrix Technical Support can identify the devices to re-enroll and implement a temporary mitigation if needed. [CXM-86729]
Citrix Endpoint Management 20.9.0
This release has enhancements that help improve overall performance and stability.
Fixed issues in Citrix Endpoint Management 20.9.0
When an Azure AD user logs into some Azure AD-joined Windows 10 devices configured to be a kiosk, kiosk mode does not activate. [CXM-66123]
Right after enrolling a device running macOS 10.14+, the device properties don’t always populate in the Citrix Endpoint Management console. Restart the device to view the properties. [CXM-84106]
Deployed resources sometimes don’t take effect on macOS 10.14+ devices until the device restarts. [CXM-84110]
Citrix Endpoint Management 20.8.0
Easier use of the certificate alias in Managed configurations. Use the new Certificate alias setting in the Credentials device policy with the Android Enterprise managed configuration device policy. Doing so allows apps to authenticate on the VPN without user action. Instead of finding the credential alias in the app logs, you create the credential alias. Create the alias by typing it in the Certificate alias field of the Android Enterprise managed configuration device policy. Then you type the same certificate alias in the Certificate alias setting in the Credentials device policy. See Managed configurations policy and Credentials device policy.
Passcode device policy allows you to show apps and shortcuts on Android Enterprise devices that are not in compliance. The Passcode device policy for Android Enterprise has a new setting, Show apps and shortcuts while passcode is not in compliance. Enable the setting to cause the apps and shortcuts to remain visible when the device passcode is no longer compliant. Citrix recommends you create an automated action to mark the device as out of compliance when the passcode isn’t in compliance. See Passcode device policy.
Control of Use one lock setting on Android Enterprise devices. The new Enable unified passcode setting in the Passcode device policy lets you control whether a device requires a separate passcode for the device and the work profile. Before this setting, users controlled this behavior with the Use one lock setting on the device. When Enable unified passcode is On, users can use the same passcode for the device as the work profile. If Enabled unified passcode is Off users can’t use the same passcode for the device as the work profile. The default is Off. The Enable unified lock setting is available for Android Enterprise devices running Android 9.0 or later. See Passcode device policy.
Fixed issues in Citrix Endpoint Management 20.8.0
If you onboarded Citrix Endpoint Management in 19.12.0 or later, to remove the Android Enterprise subscription, unenroll Android Enterprise from the console. Then remove the configuration from Google Play. If you click Remove Enterprise in the Google Play store first, the Android Enterprise subscription remains active in the Citrix Endpoint Management console. [CXM-83601]
Citrix Endpoint Management 20.7.1
Changed the profile name in enrollment screens to Citrix Workspace. When users enroll their device to Citrix Endpoint Management, the profile name that displays is now Citrix Workspace. You can customize this name and display your organization name instead. To customize the name, change the value for the new server property apple.mdm.enrollment.profile.organization.name. See Server properties.
Fixed issues in Citrix Endpoint Management 20.7.1
On some cloud sites, the Monitor page of the Citrix Endpoint Management console does not load. [CXM-83365]
When you edit the values in the optional.user.identity.attributes server property and save the changes, an error message appears. [CXM-84209]
Citrix Endpoint Management 20.7.0
Citrix Endpoint Management supports authentication with an on-premises NetScaler Gateway as a preview feature. You can now configure an on-premises NetScaler Gateway as your identity provider for users enrolling through Citrix Secure Hub. For more information, see Authentication with an on-premises NetScaler Gateway through Citrix Cloud (Preview).
Customize the list of optional Active Directory user attributes. A new server property, optional.user.identity.attributes, enables you to remove and restore optional attributes that Citrix Endpoint Management uses to identify a user account in the Active Directory. For more information, see Customize Active Directory user attributes.
Fixed issues in Citrix Endpoint Management 20.7.0
Apple iTunes Volume Purchase apps can’t synchronize with Citrix Endpoint Management. [CXM-81271]
When you install multiple LDAP Active Directories (AD) on Citrix Endpoint Management using the Citrix Cloud Connector, only the first installed AD populates in the Citrix Endpoint Management settings. As a workaround, you can check Citrix Cloud. If those domains are marked as unused, manually mark them as Used. Marking the domain as used makes it available in Citrix Endpoint Management. [CXM-81697]
If you onboarded Citrix Endpoint Management in 19.12.0 (December 2019) or later: When you add multiple LDAP authentication domains, you can’t change the default domain. [CXM-82952]
Citrix Endpoint Management 20.6.0
If you onboarded Citrix Endpoint Management after the 19.8.0 release (August 1, 2019), sign in to Citrix Cloud and click the Citrix Endpoint Management service tile to access the console. All customers who onboarded before 19.8.0 will soon transition to Citrix Cloud sign-in. To provide enhanced security, Citrix recommends that you configure a single sign-on. For assistance, contact Citrix Technical Support.
The Citrix Secure Hub Apple Push Notification Service (APNs) certificate for Citrix Endpoint Management expires on July 12, 2020. As a result, the Agent Notification fails and the application push might be delayed on iOS devices. This update renews the Citrix Secure Hub APNs certificate, which expires on June 18, 2021.
Disable the ability to print on the Android Enterprise work profiles or fully managed devices. In the Restrictions device policy, the Don’t allow printing setting lets you specify whether users can print to any printer accessible from the Android Enterprise device. For more information, see Android Enterprise settings.
Configure the connection mode and network priority for macOS. In the network device policy, enable the Connection mode setting for macOS devices to choose how users join the network. The device can use the system credentials or credentials entered at the login window to authenticate the user. If you have multiple networks, type a number in the Priority field to set the priority of the network connection. The device chooses the network with the lowest number. For more information, see the macOS settings in Network device policy.
Enable a proxy configured on iOS devices. Citrix Endpoint Management now requires that you enable a new client property, ALLOW_CLIENTSIDE_PROXY, if you want to allow iOS users to use proxy servers that they configure in Settings > Network. For more information, see ALLOW_CLIENTSIDE_PROXY in Client property reference.
Automatically update managed apps policy for managed Google Play apps. This new policy allows you to restrict the ability of users to configure automatic app updates for managed Google Play apps on Android Enterprise devices. You can allow users to configure the policy. Or, you can specify that automatic updates apply always, never, or only when a device is connected to Wi-Fi.
Fixed issues in Citrix Endpoint Management 20.6.0
In the Citrix Endpoint Management console, you can’t see that the package ID for MDX wrapped iOS and Android apps. [CXM-81021]
When Citrix Endpoint Management sends the queries for the Active Directory group members, the identity service runs the queries recursively. These queries consume more resources. So, sites with many Active Directory users might experience a disturbance in daily operations. [CXM-81112]
On the Citrix Endpoint Management console, some apps’ status displays as “Pending” even though they’re already installed. This limitation is because of macOS and is specific to PKG files with different pkg and app identifiers. [CXM-72203]
Citrix Endpoint Management 20.5.0
Simplified configuration of Intune managed apps when using Citrix Endpoint Management integration with Microsoft Endpoint Manager. When you configure Intune managed apps, you no longer set the Force app to be managed option in the Citrix Endpoint Management console. You now set the option in the EMS console.
Support for restricting web content transfer for Intune managed apps published through Microsoft Edge using Citrix Endpoint Management integration with Microsoft Endpoint Manager. Citrix Endpoint Management integration with Microsoft Endpoint Manager supports the new managed browser policy for Microsoft Edge, Restrict web content transfer with other apps, in the EMS console.
Unlock a local user account. If a user reaches the maximum number of consecutive invalid login attempts, the local user account locks for 30 minutes. The system denies all further authentication attempts until the lockout period expires. To unlock the account in the Citrix Endpoint Management console, go to Manage > Users, select the user account, and click Unlock Local User. For more information, see To unlock a local user account. To change the number of failed login attempts and the lockout time, update the local.user.account.lockout.time and local.user.account.lockout.limit server properties. For more information, see Server properties.
The Citrix Content Delivery Network (CDN) now delivers enterprise apps for macOS (MDM enrollment). To speed the delivery of app downloads, CDN sends macOS apps to user devices located near the Citrix Endpoint Management servers throughout the world. For more information, see Deliver enterprise apps from the Citrix CDN.
Fixed issues in Citrix Endpoint Management 20.5.0
Administrators with the RBAC permission to export enrollment invitations can export all enrollment invitations, regardless of limitations. [CXM-79928]
Attempts to deploy a PowerShell script to trigger an automated action on Windows devices might fail with a 500 internal server error. The issue occurs if you leave the Description field on the Action Information page blank and select Policy returned value as a trigger. To work around the issue, do not leave the Description field blank when using Policy returned value as a trigger. [CXM-80997]
When you edit an existing iOS restriction policy, an error occurs. [CXM-82180]
Citrix Endpoint Management 20.4.1
Support for the latest HTTP/2-based APNs provider API. Apple support for the Apple Push Notification service legacy binary protocol ends from March 31, 2021. Apple recommends that you use the HTTP/2-based APNs provider API instead. Citrix Endpoint Management now supports the HTTP/2-based API. For more information, see the news update, “Apple Push Notification Service Update” in https://developer.apple.com/. For help with checking connectivity to APNs, see Connectivity checks.
Password requirements for a local user account. When you add or edit a local user account in the Citrix Endpoint Management console, make sure that you follow the latest password requirements. For more information, see To add a local user account.
Use the app bundle ID number to add apps to the Apps notifications device policy. Click Add new and type the app bundle ID in the field that appears. For more information, see Apps notifications device policy.
Device policy updates for iOS 13. Device policies for iOS 13 now have the following features:
- Network usage policy: We added more features to the App network usage policy and renamed it to Network usage policy. You can now also configure network usage rules based on SIM ICCIDs on iOS 13 devices. See Network usage device policy
- Restrictions policy: You can now restrict shared device temporary sessions, eSIM modification, Find My iPhone, and more. For more information, see the iOS settings section in Restrictions device policy.
Fixed issues in Citrix Endpoint Management 20.4.1
With Azure Active Directory based authentication and device enrollment, users with Android devices fail to enroll. An error states that user authentication has no device access. [CXM-80404]
Citrix Endpoint Management 20.4.0
Publish web apps for Android Enterprise in the Citrix Endpoint Management console. You no longer need to go to managed Google Play or the Google Developer portal to publish Android Enterprise web apps for Citrix Endpoint Management. When you click Upload in Configure > Apps > Web link, a managed Google Play store UI opens for you to upload and save the file. The app approval and publishing can take about 10 minutes. For more information, see Add a Web link.
Device policy updates for iOS 13. Device policies for iOS 13 now have the following features:
- App lock policy: You can enable voice control and give users access to voice control adjustment. See App lock device policy.
- Exchange policy: You can enable or disable syncing of calendars, contacts, mail, notes, and reminders. See Exchange device policy.
- Profile removal policy: Removed the settings for allowing policy removal on iOS devices, as iOS no longer supports that feature. See Profile Removal device policy.
-
VPN policy: You can now include all network traffic or exclude local networks from the VPN, for the following connection protocols:
You can now allow traffic to flow through the cellular VPN tunnel when Wi-Fi Assist switches away from Wi-Fi, for the following connection protocols:
- Network policy: You can now use WPA3 Personal and WPA3 Enterprise as Security type options. See Network device policy.
Fixed issues in Citrix Endpoint Management 20.4.0
Data visualization charts on the Analyze dashboard don’t scale correctly when using your browser’s zoom. [CXM-79652]
When using MAM-only enrollment, users can still access the Apple Over-the-Air Enrollment portal for MDM. [CXM-77449]
The selective wipe action fails when the device is on standby. [CXM-76051]
Citrix Endpoint Management 20.3.0
Enhanced enrollment profiles enabled for all customers
This release enables for all customers the enhanced enrollment profile features released to some customers in Citrix Endpoint Management 20.2.1. For information about this feature, see Configure multiple device and app management modes in a single environment.
Android devices are enrolled in Android Enterprise by default
Starting with this release, Android Enterprise is the default enrollment option for Android devices. If Android Enterprise is enabled for your Citrix Endpoint Management deployment, all newly enrolled or re-enrolled Android devices are enrolled as Android Enterprise devices by default.
This change supports the changes Google is making to Android. Google deprecated the device administrator mode of device management and encourages customers to manage all Android devices using Android Enterprise. (See Device admin deprecation in the Google Android Enterprise developer guides.)
Starting with Citrix Endpoint Management 19.11.0, Citrix communicated the required actions to migrate all Android devices to Android Enterprise. For more information about Citrix Endpoint Management support for the transition to Android Enterprise, see the blog, Android Enterprise as the default for Citrix Endpoint Management service.
If your Citrix Endpoint Management deployment includes devices that you must continue to manage in device admin mode, create an enrollment profile for these legacy devices.
To create an enrollment profile for legacy devices:
-
In the Citrix Endpoint Management console, go to Configure > Enrollment Profiles.
-
To add an enrollment profile, click Add. In the Enrollment Info page, type a name for the enrollment profile.
-
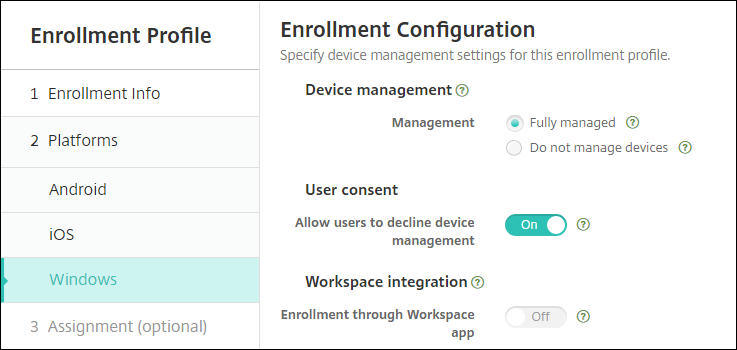
Click Next or select Android under Platforms. The Enrollment Configuration page appears.
-
Set Management to Legacy device administration (not recommended). Click Next.
-
Select Assignment (options). The Delivery Group Assignment screen appears.
-
Choose the delivery group or delivery groups that has the administrators who enroll the dedicated devices. Then click Save.
To continue managing legacy devices in device administrator mode, enroll or re-enroll them using this profile. You enroll device administrator devices similar to work profile devices, by having users download Citrix Secure Hub and providing an enrollment server URL.
Fixed issues in Citrix Endpoint Management 20.3.0
Trying to sort devices by Last access or Inactivity days results in a 500 internal server error. [CXM-79414]
For customers using Amazon Web Services and the new Citrix enhanced enrollment profiles: iOS devices don’t enroll. As a work-around, create a default enrollment profile that includes all delivery groups. See To create an enrollment profile. [CXM-79019]
When you deploy a Passcode device policy to macOS devices, the policy applies to the system level instead of the user level. As a result, users aren’t prompted to change their passcode for hours, or even days. [CXM-75344]
Citrix Endpoint Management 20.2.1
Configure multiple device and app management modes in a single environment
About this feature:
Enhanced enrollment profile support is rolling out over two releases. Citrix® sends notifications about upcoming releases.
Until the enhanced enrollment profile feature gets enabled for you, an enrollment profile only limits the number of devices a user can enroll.
You can now configure a single Citrix Endpoint Management site to support multiple enrollment configurations. The role of enrollment profiles expanded to include enrollment settings for device and app management.
Enrollment profiles support multiple use cases and device migration paths within a single Citrix Endpoint Management console. Use cases include:
- Mobile Device Management (MDM only)
- MDM+Mobile Application Management (MAM)
- MAM only
- Corporate-owned enrollments
- BYOD enrollments (the ability to opt out of MDM enrollment)
- Migration of Android device administrator enrollments to Android Enterprise enrollments (fully managed, work profile, dedicated device)
Enrollment profiles replace the now deprecated server property, xms.server.mode. This change does not impact your existing delivery groups and enrolled devices.
The following table shows the automated migration path from the existing server property mode to the new enrollment profile feature:
| Existing server property | New management mode |
|---|---|
| ENT mode (iOS) | Apple device enrollment with Citrix MAM |
| ENT mode (Android) | Legacy device administrator with Citrix MAM |
| ENT mode (Android Enterprise) | Work profile on fully managed, with Citrix MAM |
| MAM mode (iOS and Android) | Citrix MAM |
| MDM mode (iOS) | Apple device enrollment |
| MDM mode (Android) | Legacy device administrator |
| MDM mode (Android Enterprise) | Work profile on fully managed |
When you create a delivery group, you can attach an enrollment profile to the group. If you don’t attach an enrollment profile, Citrix Endpoint Management attaches the Global enrollment profile.
Enrollment profiles provide the following device management features:
-
Easier migration from Android device administrator (DA) mode to Android Enterprise. For Android Enterprise devices, settings include a device owner mode such as: Fully managed, work profile on fully managed, or dedicated. For more information, see Android Enterprise.
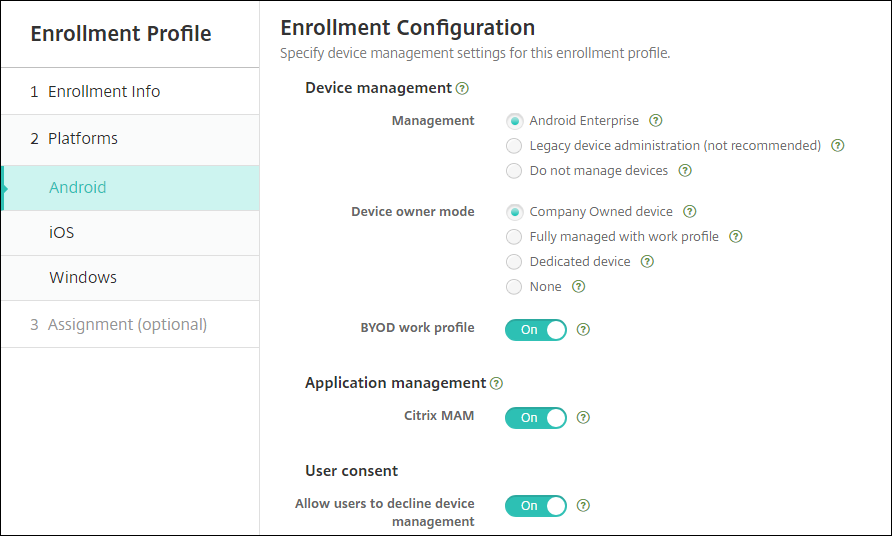
For this upgrade, your current Citrix Endpoint Management configurations for server mode and Settings > Android Enterprise map to the new enrollment profile settings as follows.
Current configuration Management setting Device owner mode setting Citrix MAM setting MDM; managed Google Play (Android Enterprise) Android Enterprise Work profile on fully managed Off MDM; Google Workspace (legacy DA) Legacy DA not applicable Off MAM Do not manage devices not applicable On MDM+MAM; managed Google Play (Android Enterprise) Android Enterprise* Work profile on fully managed On MDM+MAM; Google Workspace (legacy DA) Legacy DA* not applicable On * If enrollment is required, Allow users to decline device management is Off.
After the upgrade, your current enrollment profiles reflect those mappings. Consider whether you want to create other enrollment profiles to handle any new use cases as you transition away from legacy DA.
If you onboard to Citrix Endpoint Management 19.12.0 or later, the Global enrollment profile has these predefined settings.
-
Easier iOS management. For iOS devices, settings include a choice between enrolling devices as managed or unmanaged.
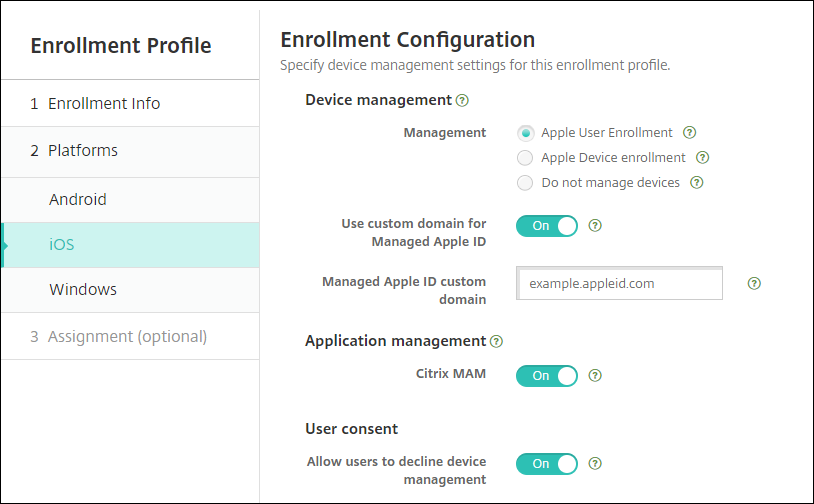
For this upgrade, your prior configurations map to the new enrollment profile settings as follows.
Server mode Management setting Citrix MAM setting MDM Device enrollment Off MAM Do not manage devices On MDM+MAM Device enrollment On If enrollment is required, Allow users to decline device management is Off.
If you onboard to Citrix Endpoint Management 19.12.0 or later, the Global enrollment profile has these predefined settings.
-
Allow Windows 10 devices to automatically enroll in Citrix Workspace app.
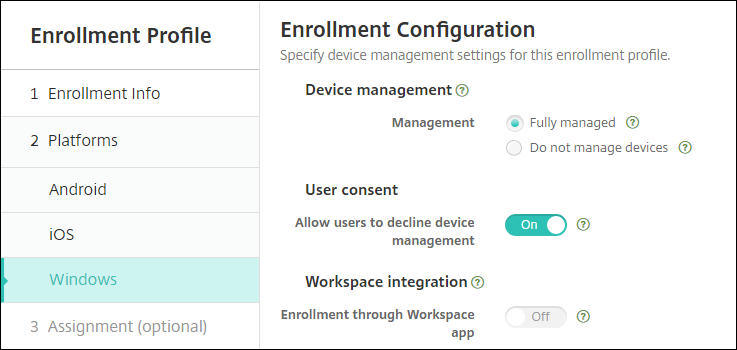
For this upgrade, your prior MDM configuration maps to the new enrollment profile setting Fully managed.
If you onboard to Citrix Endpoint Management 19.12.0 or later, the Global enrollment profile has these predefined settings.
The following limitations exist for enhanced enrollment profiles:
-
The enhanced enrollment profile feature doesn’t work for iOS and Android devices when Citrix Endpoint Management is integrated with Citrix Workspace.
-
The enhanced enrollment profile feature isn’t available for one-time PIN or two-factor authentication enrollment invitations.
For more information, see Enrollment profiles.
Other updates in Citrix Endpoint Management 20.2.1
-
Simplified enrollment of dedicated Android Enterprise (COSU) devices. Citrix Endpoint Management now enables you to enroll dedicated Android Enterprise devices (also known as COSU devices) by creating an enrollment profile. You’re no longer required to create a role-based access control (RBAC) role for enrolling dedicated devices. See Provisioning dedicated Android Enterprise devices.
-
Disable biometric authentication on Android devices with the Keyguard management policy. The Keyguard Management device policy now lets you disable fingerprint unlock, face authentication, iris authentication, or all biometric authentication for devices running Android 9.0 and later.
-
Get guidance in the Resource Center. Use the Resource Center to access the in-product data. For guidance from the dashboard, click the icon in the lower right corner.

Fixed issues in Citrix Endpoint Management 20.2.1
You previously needed permission to edit devices before you can use the Citrix Endpoint Management API to send notifications to devices. You now need Send Notification permission to send notifications. [CXM-76689]
When you enroll a WEM enabled Windows Desktop/Tablet device and then enroll the same device in the MDM, the Citrix Endpoint Management console displays two separate entries for the device. [CXM-77412]
Citrix Endpoint Management 20.1.0
-
Support for Android Enterprise COPE devices. Citrix Endpoint Management supports Android Enterprise fully managed devices with work profiles. Google previously referred to those devices as COPE (corporate-owned personally enabled) devices.
Android Enterprise fully managed devices have a device profile and a work profile. You can apply separate policy settings to the device and the work profile. For this release:
- You can apply separate settings to the device and the work profile using these device policies: Credentials, Keyguard Management, Passcode, and Restrictions.
- You can apply the location mode setting of the Location device policy to the COPE device itself but not to the work profile of the COPE device. Other settings in the Location device policy aren’t available for COPE devices. See the Location device policy.
- You can apply the Lock security action separately to the device or the work profile.
-
Auto-enrollment of Windows 10 devices through Citrix Workspace app. Citrix Endpoint Management can now auto-enroll Windows 10 desktops and tablets using the Citrix Workspace app.
Fixed issues in Citrix Endpoint Management 20.1.0
The Settings > Apple Deployment Program page doesn’t include skip options for the new iOS 13 Setup Assistant screens. During enrollment, users must click through the screens for Get Started and Appearance. [CXM-71370]
The Filters tab is open by default for Manage > Devices. [CXM-75823]
ShareFile single sign-on (SSO) fails for multitenant customers on the same set of virtual machines. [CXM-75886]
Citrix Endpoint Management 19.12.0
You can now configure delivery groups for Windows devices based on device properties. (Preview) When configuring delivery groups, you can now configure groups based on device properties. This feature is only available for Windows desktops and tablets. To request access to this Preview feature, contact your Citrix sales or support representative. For more information about this feature, see Add a delivery group (Preview).
Import Group Policy Objects (GPOs) into Citrix Endpoint Management and deploy them directly to Windows 10 devices. Rather than relying on an AD administrator to deploy GPOs from the Group Policy Management console, you can import and deploy GPOs through the Citrix Endpoint Management console. See Windows GPO Configuration device policy.
Install EXE apps for Windows desktops and tablets. You can now upload EXE applications as enterprise apps for Windows Desktops and Tablets. For more information, see Add Win32 apps as Enterprise apps.
Users can no longer remove policies from iOS devices. Some device policies no longer allow users to remove the policy from iOS devices. The setting Allow user to remove policy has been removed for iOS from the following policies: APN policy, Mail policy, Passcode policy, Provisioning Profile policy, Proxy policy, and VPN policy.
Fixed issues in Citrix Endpoint Management 19.12.0
If you update an app version number with the Citrix Endpoint Management Public REST API and then by using the console: The app version doesn’t update. [CXM-69216]
Sometimes Citrix Endpoint Management can’t install EXE apps on Windows devices because the file hash isn’t correct. [CXM-75506]
Citrix Endpoint Management 19.11.0
Apple Volume Purchase Program migration to Apple Business Manager (ABM) and Apple School Manager (ASM)
Companies and institutions using the Apple Volume Purchase Program (VPP) need to migrate to Apps and Books in the Apple Business Manager or Apple School Manager before December 1, 2019.
Before migrating VPP accounts in Citrix Endpoint Management, see this Apple support article.
If your organization or school only uses the Volume Purchase Program (VPP), you can enroll in ABM/ASM and then invite existing VPP Purchasers to your new ABM/ASM account. For ASM, navigate to https://school.apple.com. For ABM, navigate to https://business.apple.com.
To update your Volume Purchase (formerly VPP) account on Citrix Endpoint Management:
-
In the Citrix Endpoint Management console, click the gear icon in the upper-right corner. The Settings page appears.
-
Click Volume Purchase. The Volume Purchase configuration page appears.
-
Make sure that your ABM or ASM account has the same app config as your previous VPP account.
-
In the ABM or ASM portal, download an updated token.
-
In the Citrix Endpoint Management console, do the following:
-
Edit the existing Volume Purchase account with the updated token info for that location.
-
Edit your ABM or ASM credentials. Don’t change the suffix.
-
Click Save twice.
-
For more information, see:
- Apple Volume Purchase
- Deploy devices through Apple Deployment Program
- Bulk enrollment of Apple devices
Enrollment profiles control enrollment options for Android devices
Enrollment profiles now control how Android devices are enrolled if Android Enterprise in enabled for your Citrix Endpoint Management deployment. Enrollment profiles determine whether Android devices are enrolled in the default Android Enterprise mode (fully managed or work profile) or in legacy (device administrator) mode.
By default, the Global enrollment profile enrolls new and factory reset Android Enterprise devices as fully managed devices and enrolls BYOD Android Enterprise devices as work profile devices. For more information, see Android Enterprise.
Preparing legacy Android devices for Android Enterprise as default enrollment
Google is deprecating the device administrator mode of device management and encouraging customers manage all Android devices in device owner mode or profile owner mode. (See Device admin deprecation in the Google Android Enterprise developer guides.) To support this change, Citrix makes Android Enterprise the default enrollment option for Android devices.
This change means that if Android Enterprise is enabled for your Citrix Endpoint Management deployment, all newly enrolled or re-enrolled Android devices are enrolled as Android Enterprise devices.
So you can prepare for this change, Citrix Endpoint Management now allows you to create enrollment profiles that control how Android devices are enrolled.
Your organization might not be ready to begin managing legacy Android devices in device owner mode or profile owner mode. In that case, you can continue to manage them in device administrator mode. Create an enrollment profile for legacy devices and re-enroll all enrolled legacy devices.
To create an enrollment profile for legacy devices:
-
In the Citrix Endpoint Management console, go to Configure > Enrollment Profiles.
-
To add an enrollment profile, click Add. In the Enrollment Info page, type a name for the enrollment profile.
-
Click Next or select Android under Platforms. The Enrollment Configuration page appears.
-
Set Management to Legacy device administration (not recommended). Click Next.
-
Select Assignment (options). The Delivery Group Assignment screen appears.
-
Choose the delivery group or delivery groups that have the administrators who enroll the dedicated devices. Then click Save.
To continue managing the legacy devices in device administrator mode, enroll or re-enroll them using this profile. You enroll device administrator devices similar to work profile devices, by having users download Citrix Secure Hub and providing an enrollment server URL.
For more information about Citrix Endpoint Management support for the transition to Android Enterprise, see the blog, Android Enterprise as the default for Citrix Endpoint Management service.
Fixed issues in Citrix Endpoint Management 19.11.0
When searching for a Google Play Store app in the Citrix Endpoint Management console, the app name is empty. You can enter the name manually to save the app. [CXM-73261]
After uploading an MDX app for Android Enterprise, the managed Google Play store UI might not open in the Citrix Endpoint Management console. Until the issue is fixed, go to the managed Google Play store to approve and save the app manually. [CXM-73398]
For iOS, location tracking doesn’t work if you do the following: Configure and deploy a location policy, enable tracking from device security actions, and then delete the deployed location policy and create a new one. [CXM-73470]
Users with apostrophes in their user names can’t enroll their devices when their user name is imported from LDAP. [CXM-73780]
Citrix Endpoint Management 19.10.0
Expanded support for Zebra OEMConfig. Citrix Endpoint Management now supports managing Zebra devices using the Zebra Technologies administrative tool Zebra OEMConfig. (For information, see the Zebra Technologies website.) To manage devices using the Zebra OEMConfig app, publish the app and configure a Managed configurations device policy.
Content delivery network (CDN) availability for Windows apps. You can now deploy Windows apps by using a content delivery network. See Deliver enterprise apps from the Citrix CDN.
Group invitation support for users whose names include special characters. When you choose a group to receive enrollment invitations, Citrix Endpoint Management now gets the user list from the Active Directory. The list includes users whose names have special characters. See Enrollment invitations.
Fixed issues in Citrix Endpoint Management 19.10.0
After you enroll a new device or re-enroll an old device, an error message intermittently displays on Manage > Devices. [CXM-72634, CXM-73077]
When you select a Chrome or Workspace hub device in Manage > Devices > Enrolled Devices and then click Edit, the following message appears: A configuration error occurred. Please try again. That message also appears when you mouse over those devices in the devices list and click Show more. In either case, click OK to continue. [CXM-73010]
Citrix Endpoint Management 19.9.1
-
Support for encryption management for iOS and Android. Note: This feature is deprecated from March 2021. Instead, Citrix Endpoint Management uses the device encryption provided by the iOS and Android platforms. Citrix Endpoint Management supplements platform-based encryption with features such as compliance checking, available through the Citrix MAM SDK.
-
Support for iPadOS. Citrix Endpoint Management supports iPadOS 13.x. Device policies for iOS apply to devices running iPadOS.
-
Simplified app management for Android Enterprise. You no longer must go to managed Google Play or the Google Developer portal to approve or publish apps for Citrix Endpoint Management. As a result, app approval and publishing take about 10 minutes rather than hours.
-
Approve Android Enterprise apps for the Public App Store in the Citrix Endpoint Management console. You can now approve managed Google Play store apps without leaving the Citrix Endpoint Management console. After you enter an app name in the search field, the managed Google Play store UI opens with the instructions for you to approve and save the app. Your app then populates in the results allowing you to configure its details. See Add a public app store app.
-
Approve the MDX apps for Android Enterprise in the Citrix Endpoint Management console. You can now approve managed Google Play store apps for Android Enterprise without leaving the Citrix Endpoint Management console. After you upload an MDX file, the managed Google Play store UI opens with the instructions for you to approve and save the app. See Add an MDX app.
-
Publish enterprise apps for Android Enterprise in the Citrix Endpoint Management console. You no longer must register for a Google Play developer account when you add an Android Enterprise private app. The Citrix Endpoint Management console opens a managed Google Play store UI for you to upload and publish the APK file. See Add an enterprise app.
-
-
More certificate management features for Android Enterprise devices in work profile mode or fully managed mode. In addition to installing certificate authorities in the managed keystore, you can now manage the following features:
-
Configure the certificates used by specific managed apps. The Credentials device policy for Android Enterprise now includes the setting Apps to use the certificates. You can specify the apps to use the user certificates issued by the credential provider selected in this policy. Apps are silently granted access to certificates during run time. To use the certificates for all apps, leave the apps list blank. See Credentials device policy.
-
Silently remove certificates from the managed keystore or uninstall all non-system Certificate Authority certificates. See Credentials device policy.
-
Prevent users from modifying credentials stored in the managed keystore. The Restrictions device policy for Android Enterprise now includes the setting Allow user to configure user credentials. By default, that setting is set as On. See Restrictions device policy.
-
-
Location device policy now available for Android Enterprise. You can define location settings for Android Enterprise devices that are managed or running in managed profile mode. Android location tracking requires Android 8.5 and higher. See Location device policy.
-
Easy access to BitLocker recovery keys. If a user loses their BitLocker recovery key, unlocking their device can be a challenge. Citrix Endpoint Management now displays the BitLocker recovery key for Windows desktops and tablets under the device details. See BitLocker recovery key.
Fixed issues in Citrix Endpoint Management 19.9.1
After adding a custom property with a special character, admins can’t access the Devices page on the XenMobile® console. [CXM-57322]
On macOS, enterprise apps pushed from Citrix Endpoint Management remain in a pending state. This third-party issue is Apple bug #50311461 and is fixed in macOS 10.14.4. [CXM-65957]
The RBAC role Tier 2 techs can’t create enrollment invitations to a user group with more than 2000 users. Only full administrative users can create the invitations. [CXM-72086]
On iOS devices, administrators might lose the ability to send an “unlock device” command to passcode-protected devices after the device is upgraded to iOS 13.1.x. To resolve this issue, see https://support.citrix.com/article/CTX262076. [CXM-73151]
Citrix Endpoint Management 19.9.0
-
Manage keyguard features for Android Enterprise work profile and fully managed devices. Android keyguard manages the device and work challenge lock screens. Use the Keyguard Management device policy to control:
-
Keyguard management on work profile devices. You can specify the features available to users before they unlock the device keyguard and the work challenge keyguard. For example, by default users can use fingerprint unlock and view unredacted notifications on the lock screen.
-
Keyguard management on fully managed and dedicated devices. You can specify the features available, such as trust agents and secure camera, before they unlock the keyguard screen. Or, you can choose to disable all keyguard features.
-
-
Samsung Knox container password reset. The Container Password Reset security action is no longer available for Android Enterprise Samsung Knox devices. Use the Container Lock security action to reset passwords for Samsung Knox containers. The Container Password Reset security action is still available for Samsung devices in device administrator mode.
-
Configure the product track for your Android Enterprise apps. When adding a public store app or an MDX app for Android Enterprise, configure the product track you want to push to user devices. For example, if you have a track designed for testing, you can select and assign it to a specific delivery group. To learn more about rolling out your release, see the Google Play Help Center. For information on configuring the product track, see Add an MDX app or Add a public app store app.
-
Windows GPO configuration policy enabled automatically. The Windows GPO configuration policy enables automatically if you provision a Citrix Workspace Environment Management site in the Citrix Cloud. For more information see Windows GPO Configuration device policy.
-
Mobile Device Management (MDM) and Workspace Environment Management (WEM) managed devices merged in the console. If a device is both MDM managed and WEM managed, it now displays as one device in the Citrix Endpoint Management console. The device label in the console is the MDM, WEM. Previously, the device would show as two different devices. You can also delete devices that are MDM and WEM managed now.
Fixed issues in Citrix Endpoint Management 19.9.0
After you deploy the App Access device policy, non-compliant devices don’t trigger the configured action. [CXM-69842]
You can’t configure Google Workspace admin credentials for Chrome OS devices. [CXM-71665]
Connectivity between Citrix Endpoint Management and Apple School Manager fails. [CXM-71844]
MAM devices wipe apps and app data because of a failure to get the user domain details. As a result, the device considers the user as deleted. [CXM-72093]
After enrolling a new device or re-enrolling an old device, an error message intermittently displays on the Manage tab. [CXM-72224]
Citrix Endpoint Management 19.8.0
-
For existing customers: Restricted port access to the Citrix Endpoint Management console and Self-Help Portal:
For customers who onboarded before Citrix Endpoint Management 19.8.0 (August 1, 2019):
-
You can require that administrators sign on to the Citrix Cloud console for SSO access to the Citrix Endpoint Management console. Citrix highly recommends all console access through Citrix Cloud.
Set the new server property
enable.cloud.console.ssoto True, which means you can’t directly access the Citrix Endpoint Management console. Attempts to directly access the Citrix Endpoint Management console on port 4443 result in a 500 error. -
Access to the Self-Help Portal is available only through port 443. Access attempts through port 4443 now result in an “Access Denied” message.
-
-
For customers who onboard starting with Citrix Endpoint Management 19.8.0 (August 1, 2019):
-
New customers sign on to the Citrix Cloud console for SSO access to the Citrix Endpoint Management console.
-
Access to the Self-Help Portal requires a server property change. By default, new customers can’t access the Self-Help Portal.
To give your users access to the Self-Help Portal, update
shp.console.enableto True.
-
Fixed issues in Citrix Endpoint Management 19.8.0
When importing a CA certificate, the console doesn’t display an updated or new certificate under PKI entities. [CXM-68419]
When configuring the VPN device policy for iOS to use the Citrix SSO protocol: After you enable the Prompt for PIN when connecting setting and save the policy, that setting reverts to Off. [CXM-68523]
For customers who have migrated from previous versions, opening the Manage tab in the console displays an error if a device’s enrollment profile has been deleted. [CXM-69750]
Citrix Endpoint Management 19.7.1
-
Access all Google Play apps in the managed Google Play store. The Access all apps in the managed Google Play store server property makes all apps from the public Google Play store accessible from the managed Google Play store. Setting this property to true allows the public Google Play store apps for all Android Enterprise users. Administrators can then use the Restrictions device policy to control access to these apps.
-
Enable system apps on Android Enterprise devices. To allow users to run pre-installed system apps in the Android Enterprise work profile mode or fully managed mode, configure the Restrictions device policy. That configuration grants the user access to default device apps, such as camera, gallery, and others. To restrict access to a particular app, set app permissions using the App permissions policy.
Fixed issues in Citrix Endpoint Management 19.7.1
When sending an enrollment link using SMTP/SMS, the link being sent doesn’t work. [CXM-67458]
When attempting to update a public iOS app using the Citrix Endpoint Management console, a configuration error displays. [CXM-69190]
Some third-party Volume Purchase apps fail to auto-update. This issue occurred because of blocked host names. For more information, see https://support.apple.com/en-us/HT201999. [CXM-69341]
When adding Microsoft Word or PowerPoint for iOS to the cloud app library, assigning the app to a user group fails. You must delete and re-add any Intune apps experiencing this issue. [CXM-69349]
Citrix Endpoint Management 19.6.1
- Location device policy now enables device tracking for Android. You can now enable device tracking to poll specific devices at a frequency you define. You might use this policy to track delivery personnel for more accurate delivery estimates, track lost or stolen devices, or enforce geographic boundaries. For more information, see Location device policy.
Fixed issues in Citrix Endpoint Management 19.6.1
App icons don’t show in the Citrix Endpoint Management console for apps that were automatically uploaded. [CXM-66444]
After the time period in the server property bulk.enrollment.fetchRosterInfoDelay ends and an Apple School Manager device syncs with the server: The Apple School Manager user account is deleted from the server and the device moves into an anonymous state. [CXM-67913]
Users with special German characters, such as umlauts, in their display name can’t enroll. [CXM-68097]
The following error message displays when you attempt to configure a Public App by using the new app URL from the Apple Store. “Could not find the app you entered. Check the URL and try again.” [CXM-68537]
Citrix Endpoint Management 19.6.0
- Auto updates for Apple volume purchase apps. When you add a volume purchase account (Settings > iOS Settings), you can now enable auto updates for all iOS apps. See the App Auto Update setting in Apple Volume Purchase.
Fixed issues in Citrix Endpoint Management 19.6.0
The following error is displayed while adding a registry key to a Windows Embedded Compact policy if the length of the registry value exceeds 2048 characters:
Console error: could not execute statement; SQL [n/a]; nested exception is org.hibernate.exception.DataException: could not execute statement. [CXM-59446]
During profile installation on an iOS device, “Not Verified” appears in the profile information. [CXM-64486]
When an Azure AD user signs in to some Windows 10 Azure AD joined devices configured as kiosks, kiosk mode does not activate. This issue doesn’t occur if you enter the Azure AD user name in the format azuread\user. For more information, see Kiosk device policy. [CXM-66123]
App icons don’t show in the Citrix Endpoint Management console for apps that were automatically uploaded. [CXM-66444]
When you add a Volume Purchase account (Settings > iOS Settings), the following message appears if the token exceeds 350 characters: The entered company token is not valid, please enter a new one. [CXM-68113]
Citrix Endpoint Management 19.5.0
-
iOS MDM enrollment workflow change. To improve platform security by reducing misleading profile installations, Apple released a new workflow for manually enrolling devices in MDM. This new workflow affects all MDM solutions, including Citrix Endpoint Management.
There is no change for MDM enrollment to servers assigned in Apple Business Manager or Apple School Manager. The workflow changes are only for manual enrollment in MDM.
Citrix has also simplified the enrollment. Previously, iOS device users receive two prompts during enrollment: A prompt for the root CA and a prompt for the MDM device certificate. Citrix installed the root CA for flexibility in using unsigned and signed certificates. Because all Citrix Cloud deployments use trusted certificates, the root CA is no longer needed.
iOS device users receive only the MDM device certificate prompt during enrollment. That prompt is labeled “XenMobile Profile Service”.
To support this change, Citrix changed the value of the server property,
ios.mdm.enrollment.installRootCaIfRequired, tofalse. A Safari window opens during MDM enrollment to simplify the profile installation for users. For more information, see Enroll iOS devices and the following YouTube video: -
Changes for new Citrix Endpoint Management customers:
- Workspace experience deployment. You can create a separate delivery group, named Workspace, to begin to deploy the Workspace experience to new devices. By using the Workspace delivery group, you can deliver the Workspace experience to a small group without disrupting all users.
- Preconfigured policies and apps for new customers of as Citrix Endpoint Management 19.5.0. If you onboard starting with Citrix Endpoint Management 19.5.0 or later, we preconfigure a few device policies and mobile productivity apps. That configuration enables you to immediately deploy basic functionality to device users. See Default device policies and mobile productivity apps.
-
Knox Platform for Enterprise device policy for Android Enterprise (Deprecated). You can now enter the KPE Premium and Standard license keys for Android Enterprise devices running Knox version 3.0 or later.
-
Public session device policy for Chrome OS. You can now configure Chrome OS devices to support guest sessions. For information on configuring this policy, see Public session device policy.
- RBAC permission changes. The RBAC permission Add/Delete Local Users is now split into two permissions: Add Local Users and Delete Local Users.
Fixed issues in Citrix Endpoint Management 19.5.0
Enterprise apps don’t silently upgrade on supervised devices running iOS 11.4 or later. [CXM-66005]
When you edit a device policy, the following error message appears: A configuration error occurred. Please try again. [CXM-66370]
Citrix Endpoint Management 19.4.1
-
Through Workspace Environment Management (WEM) integration with Citrix Endpoint Management, you can manage all supported domain-joined Windows devices. This integration offers the following benefits and features:
- With WEM alone, MDM deployments aren’t possible. With Citrix Endpoint Management alone, you’re limited to managing Windows 10 devices. By integrating the two products:
- WEM can access MDM features
- You can manage a wider spectrum of Windows operating systems through Citrix Endpoint Management
-
That management takes the form of configuring Windows GPOs. Currently, administrators import an ADMX file to Citrix Endpoint Management and push it to Windows 10 desktops and tablets to configure specific applications. Using the Windows GPO Configuration device policy, you can configure GPOs and push changes to the WEM service. The WEM Agent then applies the GPOs to devices and their apps.
-
MDM management isn’t a requirement for WEM integration. Any device that WEM supports can have GPO configurations pushed to it, even if Citrix Endpoint Management doesn’t support that device natively.
-
For a list of the devices supported, see Operating System requirements.
- Devices which receive the Windows GPO Configuration device policy run in a new Citrix Endpoint Management mode called WEM. In the Manage > Devices list of enrolled devices, the Mode column for WEM-managed devices lists WEM.
For more information, see Windows GPO Configuration device policy.
- With WEM alone, MDM deployments aren’t possible. With Citrix Endpoint Management alone, you’re limited to managing Windows 10 devices. By integrating the two products:
-
CDN delivery of enterprise apps is now the default for new multi-tenancy customers of as Citrix Endpoint Management 19.4.1. If you’re a new customer in the Asia Pacific region, contact your Citrix support representative to enable CDN delivery. In all regions, existing customers who want to deliver enterprise apps using CDN must reupload existing apps after enabling the feature. See Deliver enterprise apps from the Citrix CDN.
-
Support for Web and SaaS apps and Web links for Android Enterprise. Citrix Endpoint Management now supports delivering links for Web or SaaS apps and Web links to Android Enterprise devices. Web and SaaS apps and Web links are added for Android Enterprise in the same way that they’re added for other platforms. See Add a Web or SaaS app and Add a Web link.
-
More restrictions for Chrome OS devices:
-
Display instructions on disabled devices. You can now add a custom message to display on disabled Chrome OS devices.
-
Allow users to install specific extensions, apps, and themes. Enter the list of URLs to permit downloading from those sources.
For more information, see Chrome OS settings.
-
Fixed issues in Citrix Endpoint Management 19.4.1
On Android Enterprise devices, the following app types might not appear in Citrix Secure Hub: Public app store apps configured in the Google Play platform and enterprise apps configured in the Android platform. [CXM-63638]
Android Enterprise apps don’t appear for devices until they’re unenrolled and enrolled again. Apps also appear if you update them in their delivery groups. [CXM-64670]
Automated actions might not deploy to Android Enterprise devices. [CXM-64950]
The name and owner of your Android Enterprise enterprise might not display correctly in the Google Play store administrator console. [CXM-65647]
Citrix Endpoint Management 19.3.1
Fixed issues in Citrix Endpoint Management 19.3.1
If you deployed a Store device policy for Windows 10 Desktop and Tablet devices before release 19.3.1: When a user clicks the Windows store link in the Start menu, a message appears: “500 Internal Server Error” or “HTTP Status 404 - Either you’ve reached an old URL or this device isn’t registered”. To resolve this issue, you must recreate and deploy your Store device policy. [CXM-61785]
If an Active Directory user group is assigned to an RBAC role permission, you can’t delete the LDAP configuration that has that user group. As a workaround, if you unassign the corresponding Active Directory group from RBAC, you can delete the domain. [CXM-62737]
Citrix Endpoint Management 19.3.0
-
Support for Samsung Knox on Android Enterprise policy unification. For Android Enterprise devices running Samsung Knox 3.0 or later and Android 8.0 or later: Knox and Android Enterprise are combined into a unified device and profile management solution. Configure Knox settings on the Android Enterprise page of the following device policies:
-
OS Update device policy. Control Samsung Enterprise FOTA updates. See OS Update device policy.
-
Passcode device policy. See Passcode device policy.
-
Restrictions device policy. See Restrictions device policy.
-
Samsung MDM license key device policy (Deprecated). Configure the Knox license key.
-
-
App inventory device policy for Android Enterprise. You can now collect an inventory of the Android Enterprise apps on managed devices. For more information, see App inventory device policy.
-
Files device policy for Android Enterprise. You can now add script files to Citrix Endpoint Management to do functions on Android Enterprise devices. See Files device policy.
-
Lock and reset the password for Android Enterprise. Citrix Endpoint Management now supports the Lock and Reset password security action for Android Enterprise devices enrolled in work profile mode running Android 8.0 and greater. See Security actions.
-
Azure Active Directory support in a kiosk on Windows 10 Desktop and Tablet devices. You can now add domain joined Azure AD devices in Kiosk mode. See Kiosk device policy.
-
For Citrix Endpoint Management customers with the workspace experience enabled: Citrix Endpoint Management supports federated authentication through the Citrix Workspace app on iOS and Android. This feature does not support Azure Active Directory. For information, see Choose or change authentication methods.
-
Public REST API change. The Citrix Endpoint Management Public API for REST Services now includes an API to edit platform details inside the container for MDX apps. See “Section 3.15.2.4 Update platform details inside the container for MDX apps” in the PDF, Public API for REST Services.
Fixed issues in Citrix Endpoint Management 19.3.0
Locking fully managed Android Enterprise devices remotely using the Lock with passcode security action might fail without notifying you of the failure. To make sure that a device is locked, set Lock with passcode twice. The device locks with the second passcode that you set. [CXM-61095]
If the enterprise is deleted from Managed Google Play and updated on the Citrix Endpoint Management server, Android Enterprise devices can’t enroll sometimes. [CXM-62769]
For Citrix Endpoint Management integration with Microsoft Endpoint Manager: Changes made to an Intune store app name or description don’t get saved. [CXM-62842]
After you edit an iOS Intune app, the app won’t install from the Microsoft Company Portal app. [CXM-62972]
If assigned permission as a Citrix Cloud custom administrator instead of a full administrator, you can’t click the Manage button to navigate resources. [CXM-63433]
Deprecation of TLS versions
To improve the security of the Citrix Endpoint Management service, Citrix now blocks any communication over Transport Layer Security (TLS) 1.0 and 1.1. Because of its weakening security, the PCI Council is deprecating TLS 1.0.
How this change impact you
If you use mobile application management through an on-premises NetScaler Gateway (NetScaler Gateway), you must update your load balancer service to enable TLS 1.2.
Older versions of the following connectors support TLS 1.0 only:
- Citrix Endpoint Management connector for Exchange ActiveSync
- NetScaler Gateway connector for Exchange ActiveSync
Upgrade your connector as follows:
-
If you use the Citrix Endpoint Management connector for Exchange ActiveSync build 10.1.3 or lower, upgrade to build 10.1.4 or higher.
-
If you use the NetScaler Gateway connector for Exchange ActiveSync build 8.5.0 or lower, upgrade to build 8.5.1.11 or higher.
What to do
If you use an on-premises NetScaler Gateway (NetScaler Gateway), enable TLS 1.2 on your load balancer service. For information, see https://support.citrix.com/article/CTX247095.
To download either connector for Exchange ActiveSync:
1. Go to <https://www.citrix.com/downloads>.
1. Navigate to **Citrix Endpoint Management (and Citrix XenMobile Server) > XenMobile Server (on-premises) > Product Software > XenMobile Server 10 > Server Components**.
1. Locate the connector tile and then click **Download File**.
Citrix Endpoint Management 19.2.1
- Run multiple apps in a kiosk on Chrome devices. You can now add multiple apps to the Kiosk policy for Chrome OS. You can optionally automatically start apps when the user starts the device. See the Kiosk device policy.
Fixed issues in Citrix Endpoint Management 19.2.1
After an Android Enterprise is unenrolled and then re-enrolled, approved apps might not appear on devices enrolled in work profile mode. [CXM-59994]
When users first run Citrix Secure Mail on Intune MDM+MAM, the setup takes users through a workflow to select Intune MAM/XenMobile. [CXM-31272]
Citrix Endpoint Management 19.2.0
-
Deliver enterprise apps from a content delivery network (CDN). When a user isn’t located near an Citrix Endpoint Management server, enterprise app delivery can take a while. For faster app downloads, you can instead have enterprise apps delivered from content delivery network (CDN) locations throughout the world. CDN support for enterprise apps is available for iOS apps (MDM or MAM enrollment) and Android apps (MDM or MAM enrollment). CDN support for enterprise apps isn’t available for Windows apps. To get started, see Deliver enterprise apps from the Citrix CDN.
-
DEP device enrollment change for Citrix Workspace. If Citrix Endpoint Management is integrated with Citrix Workspace, the Citrix Workspace app is included in the DEP deployment package as a required app. This feature requires that you configure your DEP account settings for iOS with the required credentials set to off. Citrix Secure Hub prompts users to enroll the device in Citrix Workspace before enrolling in Citrix Endpoint Management.
-
The server property ios.mdm.enrollment.installRootCaIfRequired is now set to false. Citrix Endpoint Management uses a publicly trusted certificate chain, thus it isn’t necessary to push a root CA to devices. As a result, iOS device users no longer receive a prompt to install a root CA during enrollment.
-
The network and Credentials policies now support Apple TV OS. In addition, you can now configure the AirPlay Security device policy to control which devices can connect to Apple TV devices. For more information, see the Network, Credentials, and Airplay Security device policy articles.
-
Location device policy now available for Android Enterprise. You can define location settings for Android Enterprise devices that are managed or running in managed profile mode. See Location device policy.
-
Enhanced support for Alexa for Business. Citrix Endpoint Management now includes support for Alexa for Business conferencing, adding Alexa skills to your organizations, editing skill groups. See Alexa for Business.
-
Automated actions for Windows Agent policy. Using the Windows Agent policy, you can automate actions to run on Windows desktops and tablets based on registry values. For more information see the Windows Agent device policy and Automated Actions articles.
-
For Android Enterprise, the No Restrictions option for required characters in a passcode is now deprecated. Android Enterprise devices running Android 7 or higher no longer support a passcode created without character restrictions. If you previously set Required characters to No Restrictions, this update changes that value to Numbers only. This change doesn’t affect the current user sign-in experience. For more information, see Android Enterprise settings.
Fixed issues in Citrix Endpoint Management 19.2.0
When an app is deleted from the Intune library, and a user tries to delete it from the Citrix Cloud library, they can’t delete it. [CXM-61645]
After you upload a Google Play app in the Endpoint Manager console without adding an app icon image: If you later upload an image for the app, the image doesn’t appear in the apps list. [CXM-60965]
Citrix Endpoint Management 19.1.2
-
Files device policy now available for Android Enterprise. You can add script files to Citrix Endpoint Management to do functions on Android Enterprise devices. See Files device policy.
-
Configure time zone settings for Chrome OS devices. You can now select a time zone for the Chrome device and specify how to detect the time zone. For more information, see Restrictions device policy.
-
An RBAC administrator’s group permissions now restricts the user information shown on the Users and Enrollment Invitations pages. Previously, the Citrix Endpoint Management console included information for all local users and domain users on the Manage > Users and Manage > Enrollment Invitations pages.
To specify which user groups an RBAC administrator has permission to view and manage, edit the administrator role and specify the user groups. For more information, see Configure roles with RBAC.
-
Launch third-party apps from the Citrix Workspace app. For customers with Citrix Workspace enabled: Before deploying new apps to users, you can add a comma-separated list of URLs to launch the apps from the Citrix Workspace app. For more information, see Add apps.
Fixed issues in Citrix Endpoint Management 19.1.2
You can’t upload Google Play services APK versions later than 11.5.09 in the Citrix Endpoint Management console. [CXM-59492]
Editing Windows Desktop and Tablet apps in Configure > Apps > Public App Store results in this message: “Application search failed”. Searching for those apps results in this message: “Error connecting to the windows desktop store url: Failed to retrieve public app details”. [CXM-61686]
In this article
- Citrix Endpoint Management 23.9.0
- Citrix Endpoint Management 23.7.0
- Citrix Endpoint Management 23.6.0
- Citrix Endpoint Management 23.4.0
- Citrix Endpoint Management 23.2.0
- Citrix Endpoint Management 23.1.0
- Citrix Endpoint Management 22.12.0
- Citrix Endpoint Management 22.10.0
- Citrix Endpoint Management 22.9.0
- Citrix Endpoint Management 22.7.0
- Citrix Endpoint Management 22.6.0
- Citrix Endpoint Management 22.5.0
- Citrix Endpoint Management 22.4.0
- Citrix Endpoint Management 22.3.0
- Citrix Endpoint Management 22.2.0
- Citrix Endpoint Management 22.1.0
- Citrix Endpoint Management 21.12.0
- Citrix Endpoint Management 21.11.0
- Citrix Endpoint Management 21.10.1
- Citrix Endpoint Management 21.10.0
- Citrix Endpoint Management 21.9.1
- Citrix Endpoint Management 21.9.0
- Citrix Endpoint Management 21.8.0
- Citrix Endpoint Management 21.7.1
- Citrix Endpoint Management 21.7.0
- Citrix Endpoint Management 21.6.0
- Citrix Endpoint Management 21.5.1
- Citrix Endpoint Management 21.5.0
- Citrix Endpoint Management 21.4.0
- Citrix Endpoint Management 21.3.0
- Citrix Endpoint Management 21.2.0
- Citrix Endpoint Management 21.1.1
- Citrix Endpoint Management 21.1.0
- Citrix Endpoint Management 20.12.0
- Citrix Endpoint Management 20.11.0
- Citrix Endpoint Management 20.10.1
- Citrix Endpoint Management 20.10.0
- Citrix Endpoint Management 20.9.1
- Citrix Endpoint Management 20.9.0
- Citrix Endpoint Management 20.8.0
- Citrix Endpoint Management 20.7.1
- Citrix Endpoint Management 20.7.0
- Citrix Endpoint Management 20.6.0
- Citrix Endpoint Management 20.5.0
- Citrix Endpoint Management 20.4.1
- Citrix Endpoint Management 20.4.0
- Citrix Endpoint Management 20.3.0
- Android devices are enrolled in Android Enterprise by default
- Citrix Endpoint Management 20.2.1
- Citrix Endpoint Management 20.1.0
- Citrix Endpoint Management 19.12.0
- Citrix Endpoint Management 19.11.0
- Citrix Endpoint Management 19.10.0
- Citrix Endpoint Management 19.9.1
- Citrix Endpoint Management 19.9.0
- Citrix Endpoint Management 19.8.0
- Citrix Endpoint Management 19.7.1
- Citrix Endpoint Management 19.6.1
- Citrix Endpoint Management 19.6.0
- Citrix Endpoint Management 19.5.0
- Citrix Endpoint Management 19.4.1
- Citrix Endpoint Management 19.3.1
- Citrix Endpoint Management 19.3.0
- Deprecation of TLS versions
- Citrix Endpoint Management 19.2.1
- Citrix Endpoint Management 19.2.0
- Citrix Endpoint Management 19.1.2
