-
-
-
Secure ICA®
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Secure ICA 2.0
macOS VDA support Secure ICA 2.0
The Secure ICA 2.0 Feature evolves from the original Secure ICA. The main drawback of the original Secure ICA was its susceptibility to MITM attacks, which Secure ICA 2.0 addresses. In addition, the up-to-date Advanced Encryption Standard (AES) cipher is used. One key aspect of Secure ICA 2.0 vs. network-level encryption (TLS or DTLS) is the ability to provide true end-to-end encryption (E2EE) between the Citrix Workspace App (CWA) and the VDA. This means that no intermediate network elements (including the Citrix Gateway) are able to decrypt the ICA traffic.
| Phase | Algorithm |
|---|---|
| key exchange | ECDHE |
| authentication | RSA |
| session cipher | AES-256 |
| cipher-block dependency and additional options | GCM |
| message authentication | SHA256 |
Network encryption consideration
Network level encryption and Secure ICA 2.0 are complementary: customers can choose to enable both simultaneously.
Feature toggle/Group policy
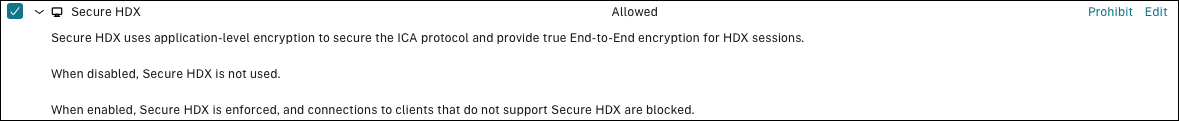
The feature toggle Secure HDX policy, is designed to turn on/off this feature.
Backward compatibility & limitation
Capability negotiation is performed during the ICA® initialization phase, so this feature is compatible with old versions; macOS VDA does not support “Shield” at the moment, so currently we support “non-Shield” scenarios. In “non-Shield” mode, VDA self-signed certificate is provided to CWA via a trusted path, while in “Shield” mode, VDA self-signed certificate is provided to CWA via CLXMTP protocol.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.