OIDC Entra ID authentication
This section describes how to configure NetScaler and StoreFront so users can authenticate using Entra ID. In this configuration, users can either have a hybrid identity, or an Entra only identity without an Active Directory account.
Prerequisites
- NetScaler ADC
- StoreFront 2603 or higher
- Microsoft Entra ID and account with one of the following permissions:
- Cloud Application Administrator
- Application Administrator
- Global Administrator
Create a Microsoft Azure Entra ID application
An App Registration in Microsoft Entra ID defines your application so that Entra ID recognizes it—in this case, NetScaler OIDC. This registration also manages the application’s authentication and authorization requests. Because OAuth requires a trusted Identity Provider (IdP) to authenticate users and issue tokens, registering your app tells Entra ID: “This application uses you as its IdP for OAuth flows.”
- Sign in to the Azure portal for the Entra ID tenant that you use for NetScaler or StoreFront authentication.
- Go to Microsoft Entra ID resource > Manage > App registrations, then select New registration.
- Name the application, for example, NetScaler StoreFront Authentication.
- Under Supported account types, select Accounts in this organizational directory only.
-
Under Redirect URI, select Web for the type of application you want to create. Enter the URI where the access token is sent. Use the format <NetScaler Virtual Server URL>/oauth/login, for example
https://netscalerentra.customer.com/oauth/login.
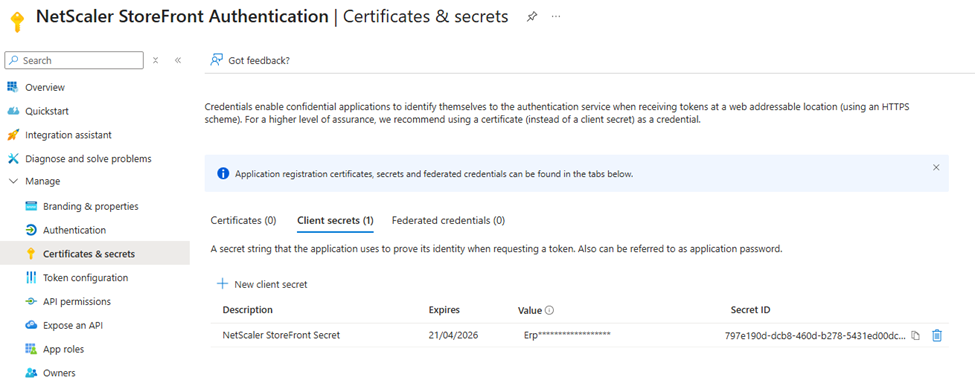
Create client secret
To create client secret:
- After you register the application, go to Manage > Certificates & Secrets.
- Select Client secrets, and then select New client secret. Your app uses these credentials to securely communicate with the IdP and request tokens.
- Provide a description of the secret and a duration.
- After you create the secret, record the secret value because you need it later in the setup process and it’s only visible during this stage of creation.
Configure application permissions
To configure app permissions:
- Go to Manage > App registrations, then select your application.
- Select Manage > API Permissions.
- The User.Read permission is already added by default.
- Add openid and profile.
- Select Grant admin consent for <tenant name> and accept.
“Grant admin consent for” in API permissions in Microsoft Entra ID means that an administrator gives approval, on behalf of all users in the organization, for an application to access specific resources or APIs with the requested permissions.

Configure Citrix DaaS to enable XML trust
By default Citrix DaaS authenticates requests using the user’s Active Directory credentials. With Entra ID authentication, StoreFront does not have the credentials. Therefore you must configure DaaS to trust StoreFront without requiring using authentication. It is strongly recommended that you enable security keys to provide service level authentication instead.
- Sign in to Citrix Cloud and go to the DaaS console.
- Go to Settings.
-
Turn on XML trust.
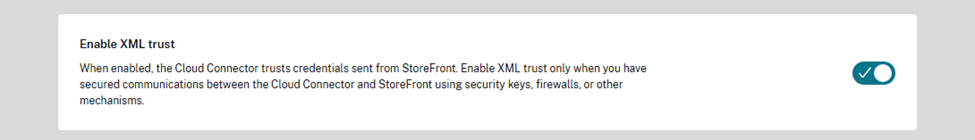
- (Optional step) For added security you can enable security keys between DaaS and StoreFront. For more information, see Manage security keys in the Citrix DaaS™ documentation.
Configure NetScaler authentication profile
This section describes how to configure a NetScaler authentication profile that you can bind to your gateway VPN virtual server. This configuration tells the ADC how to redirect users to an external OAuth IdP (like Microsoft Entra ID) for sign-in and how to handle the OAuth tokens received after authentication. It specifies endpoints, client credentials, scopes, and how the ADC extracts user information from tokens.
You need the client secret from the previous steps and the Microsoft Entra ID authentication endpoints. You can find the authentication endpoints in the Azure portal by going to your App Registration Overview and clicking the Endpoints tab.
Create authentication virtual server
The authentication virtual server handles user authentication.
add authentication vserver EntraId_Authentication_VirtualServer SSL 0.0.0.0 443 \
-state ENABLED \
-authentication ON \
-td 0 -appflowLog ENABLED \
-noDefaultBindings NO
<!--NeedCopy-->
Create OAuth policy and action
The OAuth action specifies how NetScaler ADC interacts with an OAuth IdP such as Microsoft Entra ID. This action allows the Citrix Gateway to redirect users to the IdP for sign-in and handle the OAuth token returned. It sets the userNameField to oid which causes the gateway to pass the OID as the username when authenticating to StoreFront. StoreFront validates that the oid matches the details it gets from looking up the Entra ID access token, otherwise authentication fails.
You need the Client ID and Client secret from the previous steps.
add authentication OAuthAction EntraId_Oauth_Server \
-authorizationEndpoint "https://login.microsoftonline.com/<TenantId>/oauth2/v2.0/authorize\?prompt=login" \
-tokenEndpoint "https://login.microsoftonline.com/<TenantId>/oauth2/v2.0/token" \
-clientID <ClientId> \
-clientSecret <ClientSecret> \
-Attribute1 email \
-Attribute2 family_name \
-Attribute3 given_name \
-Attribute4 upn \
-CertEndpoint "https://login.microsoftonline.com/<TenantId>/discovery/v2.0/keys" \
-userNameField oid \
-allowedAlgorithms HS256 RS256 RS512 \
-PKCE ENABLED \
-tokenEndpointAuthMethod client_secret_post \
-OAuthType GENERIC \
-grantType CODE \
-refreshInterval 1440
add authentication Policy EntraId_Authentication_Policy \
-rule true \
-action EntraId_Oauth_Server
<!--NeedCopy-->
The authorizationEndpoint includes the query string parameter prompt=login so that users are forced to reauthenticate when they attempt to access StoreFront through the NetScaler.
Bind the authentication policy to the virtual server
bind authentication vserver EntraId_Authentication_VirtualServer \
-policy EntraId_Authentication_Policy \
-priority 100 \
-gotoPriorityExpression END
<!--NeedCopy-->
Create authentication profile
add authentication authnProfile EntraId_Auth_Profile \
-authnVsName EntraId_Authentication_VirtualServer \
-AuthenticationLevel 0
<!--NeedCopy-->
Create VPN Virtual Server and bind the authentication profile
Complete steps 1, 2 and 4 from Integrate NetScaler Gateway with StoreFront, using the authentication profile created in the previous steps.
Alternatively, if you already have a suitable Citrix Gateway then you can bind the new authentication profile to it. Running this command replaces the existing authentication profile.
set vpn vserver <StoreFront ICA Proxy vServer> \
-authentication ON \
-authnProfile EntraId_Auth_Profile
<!--NeedCopy-->
Entra ID token injection configuration for SSO to StoreFront
After the Citrix gateway authenticates the user, it must pass sufficient information to StoreFront so that it can validate the user is authenticated and look up group membership. By default, the Citrix gateway only sends the Active Directory username and password. In the case of Entra ID authentication, it must pass the Entra ID access token so that StoreFront can look up user information using the Microsoft Graph API. To achieve this you must add a re-write policy that adds the Entra ID token to the call it makes to authenticate the user to StoreFront. If the rewrite Entra ID access token policy does not take effect, login will fail. If the rewrite policy feature is disabled by default and is not already enabled, then you must enable it first.
enable ns feature Rewrite
add rewrite action EntraId_Oauth_Insert_AccessToken_Header insert_http_header X-Citrix-OIDC-Access-Token "AAA.USER.ATTRIBUTE(\"accesstoken\")" \
-comment "A rewrite policy to add the OAUTH access_token to subsequent user authentication requests"
add rewrite policy EntraId_Oauth_Insert_AccessToken_Policy "HTTP.REQ.URL.TO_LOWER.ENDSWITH(\"gatewayauth/login\") || HTTP.REQ.URL.TO_LOWER.ENDSWITH(\"citrixagbasic/authenticate\")" EntraId_Oauth_Insert_AccessToken_Header \
-comment "A rewrite policy to add the OAUTH access_token to subsequent user authentication requests"
bind vpn vserver <StoreFront ICA Proxy vServer> \
-policy EntraId_Oauth_Insert_AccessToken_Policy \
-priority 100 \
-gotoPriorityExpression END \
-type REQUEST
<!--NeedCopy-->
Configure Citrix Gateway within StoreFront
-
Configure the Citrix Gateways.
-
Set Login type to Domain.
-
Specify a valid callback URL. This is required for Entra ID authentication with StoreFront.
-
-
Configure the gateway for remote access for the Store aggregating the Citrix DaaS resources.
-
On the Manage Authentication Methods screen, enable Pass-through from Citrix Gateway and configure Entra ID settings
In this article
- Prerequisites
- Create a Microsoft Azure Entra ID application
- Create client secret
- Configure application permissions
- Configure Citrix DaaS to enable XML trust
- Configure NetScaler authentication profile
- Entra ID token injection configuration for SSO to StoreFront
- Configure Citrix Gateway within StoreFront