-
-
WebSocket communication between VDA and Delivery Controller™
-
-
-
-
-
Rendezvous V2
-
-
-
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Rendezvous V2
When using the Citrix Gateway Service, the Rendezvous protocol allows VDAs to bypass the Citrix Cloud™ Connectors to connect directly and securely with the Citrix Cloud control plane.
Rendezvous V2 is supported with standard domain joined machines, Microsoft Entra hybrid joined machines, Microsoft Entra joined machines, and non-domain joined machines.
Note:
Currently, connectorless deployments are possible with Azure AD joined and non-domain joined machines only. Standard AD domain joined machines and Microsoft Entra hybrid joined machines still require Cloud Connectors for VDA registration and session brokering. However, there are no DNS requirements for using Rendezvous V2.
Cloud Connector requirements for other functions not related to VDA communication, such as connecting to your on-prem AD domain, MCS provisioniong to on-prem hypervisors, etc., remain the same.
Requirements
The requirements for using Rendezvous V2 are:
- Access to the environment using Citrix Workspace™ and Citrix Gateway Service
- Control plane: Citrix DaaS™
- VDA version 2203
- Enable the Rendezvous protocol in the Citrix policy. For more information, see Rendezvous protocol policy setting.
- Session Reliability must be enabled on the VDAs
- The VDA machines must have access to:
-
https://*.xendesktop.netonTCP 443. If you can’t allow all subdomains in that manner, you can usehttps://<customer_ID>.xendesktop.net, where <customer_ID> is your Citrix Cloud customer ID as shown in the Citrix Cloud administrator portal. -
https://*.*.nssvc.netonTCP 443for the control connection with Gateway Service. -
https://*.*.nssvc.netonTCP 443andUDP 443for HDX sessions over TCP and EDT, respectively.
Note:
If you can’t allow all subdomains using
https://*.*.nssvc.net, you can usehttps://*.c.nssvc.netandhttps://*.g.nssvc.netinstead. For more information, see Knowledge Center article CTX270584. -
Proxy configuration
The VDA supports connecting through proxies for both control traffic and HDX™ session traffic when using Rendezvous. The requirements and considerations for both types of traffic are different, so review them carefully.
Control traffic proxy considerations
- Only HTTP proxies are supported.
- Packet decryption and inspection are not supported. Configure an exception so the control traffic between the VDA and the Citrix Cloud control plane is not intercepted, decrypted, or inspected. Otherwise, the connection fails.
- Machine-based authentication is supported only if the VDA machine is AD domain joined. It can use Negotiate/Kerberos or NTLM authentication.
Note:
To use Kerberos, create the service principal name (SPN) for the proxy server and associate it with the proxy’s Active Directory account. The VDA generates the SPN in the format
HTTP/<proxyURL>when establishing a connection with Citrix Cloud. If you don’t create an SPN, authentication falls back to NTLM. In both cases, the VDA machine’s identity is used for authentication.
HDX traffic proxy considerations
- HTTP and SOCKS5 proxies are supported.
- EDT can only be used with SOCKS5 proxies.
- By default, HDX traffic uses the proxy defined for control traffic. If you must use a different proxy for HDX traffic, whether a different HTTP proxy or a SOCKS5 proxy, use the Rendezvous proxy configuration policy setting.
- Packet decryption and inspection are not supported. Configure an exception so the HDX traffic between the VDA and the Citrix Cloud control plane is not intercepted, decrypted, or inspected. Otherwise, the connection fails.
- Machine-based authentication is supported only with HTTP proxies and if the VDA machine is AD domain joined. It can use Negotiate/Kerberos or NTLM authentication.
Note:
To use Kerberos, create the service principal name (SPN) for the proxy server and associate it with the proxy’s Active Directory account. The VDA generates the SPN in the format
HTTP/<proxyURL>when establishing a session, where the proxy URL is retrieved from the Rendezvous proxy configuration policy setting. If you don’t create an SPN, authentication falls back to NTLM. In both cases, the VDA machine’s identity is used for authentication. - Authentication with a SOCKS5 proxy is not currently supported. If using a SOCKS5 proxy, configure an exception so that traffic destined to Gateway Service addresses (specified in the requirements) can bypass authentication.
- Only SOCKS5 proxies support data transport through EDT. For an HTTP proxy, use TCP as the transport protocol for ICA.
Transparent proxy
If using a transparent proxy in your network, no additional configuration is required on the VDA.
Non-transparent proxy
If using a non-transparent proxy in your network, specify the proxy during the VDA installation so that control traffic can reach the Citrix Cloud control plane. Make sure to review the control traffic proxy considerations before proceeding with the installation and configuration.
In the VDA installation wizard, select Rendezvous Proxy Configuration in the Additional Components page. This option makes the Rendezvous Proxy Configuration page available later in the installation wizard. Once here, enter the proxy address or the path to the PAC file for the VDA to know which proxy to use. For example:
- Proxy address:
http://<URL or IP>:<port> - PAC file:
http://<URL or IP>/<path/<filename>.pac
As stated in the HDX traffic proxy considerations, HDX traffic uses the proxy defined during the VDA installation by default. If you must use a different proxy for HDX traffic, whether a different HTTP proxy or a SOCKS5 proxy, use the Rendezvous proxy configuration policy setting. When the setting is enabled, specify the HTTP or SOCKS5 proxy address. You can also enter the path to the PAC file so the VDA knows which proxy to use. For example:
- Proxy address:
http://<URL or IP>:<port>orsocks5://<URL or IP>:<port> - PAC file:
http://<URL or IP>/<path/<filename>.pac
If you use the PAC file to configure the proxy, define the proxy using the syntax required by the Windows HTTP service: PROXY [<scheme>=]<URL or IP>:<port>. For example, PROXY socks5=<URL or IP>:<port>.
How to configure Rendezvous
Following are the steps for configuring Rendezvous in your environment:
- Make sure that all requirements are met.
- If you must use a non-transparent HTTP proxy in your environment, configure it during the VDA installation. Refer to the proxy configuration section for details.
- Reboot the VDA machine after installation is complete.
- Create a Citrix policy, or edit an existing one:
- Set the Rendezvous Protocol setting to Allowed.
- If you must configure an HTTP or SOCKS5 proxy for HDX traffic, configure the Rendezvous proxy configuration setting.
- Ensure that the Citrix policy filters are set properly. The policy applies to the machines that need Rendezvous enabled.
- Ensure that the Citrix policy has the correct priority so that it does not overwrite another one.
Note:
If you are using VDA version 2308 or older, V1 is used by default. For more information on how to configure the version to use, see HDX features managed through the registry.
Rendezvous validation
If you meet all requirements and have completed the configuration, follow these steps to validate if Rendezvous is in use:
- Within the virtual desktop, open a command prompt or PowerShell.
- Run
ctxsession.exe -v. - The transport protocols displayed indicate the type of connection:
- TCP Rendezvous: TCP > SSL > CGP > ICA
- EDT Rendezvous: UDP > DTLS > CGP > ICA
- Not Rendezvous: TCP > CGP > ICA
- The Rendezvous version reported indicates the version in use.
Other considerations
Windows cipher suite order
If the cipher suite order has been modified in the VDA machines, make sure that you include the VDA-supported cipher suites:
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
If the custom cipher suite order does not contain these cipher suites, the Rendezvous connection fails.
Zscaler Private Access
If using Zscaler Private Access (ZPA), it is recommended that you configure bypass settings for the Gateway Service to avoid increased latency and the associated performance impact. To do so, you must define application segments for the Gateway Service addresses – specified in the requirements – and set them to always bypass. For information on configuring application segments to bypass ZPA, see the Zscaler documentation.
Known Issues
VDA 2203 installer does not allow entering a slash ( / ) for the proxy address
As a workaround, you can configure the proxy in the registry after the VDA is installed:
Key: HKEY_LOCAL_MACHINE\SOFTWARE\Citrix\VirtualDesktopAgent
Value type: String
Value name: ProxySettings
Value data: Proxy address or path to pac file. For example:
Proxy address: http://squidk.test.local:3128
Pac file: http://file.test.com/config/proxy.pac
Rendezvous traffic flow
The following diagram illustrates the sequence of steps about Rendezvous traffic flow.
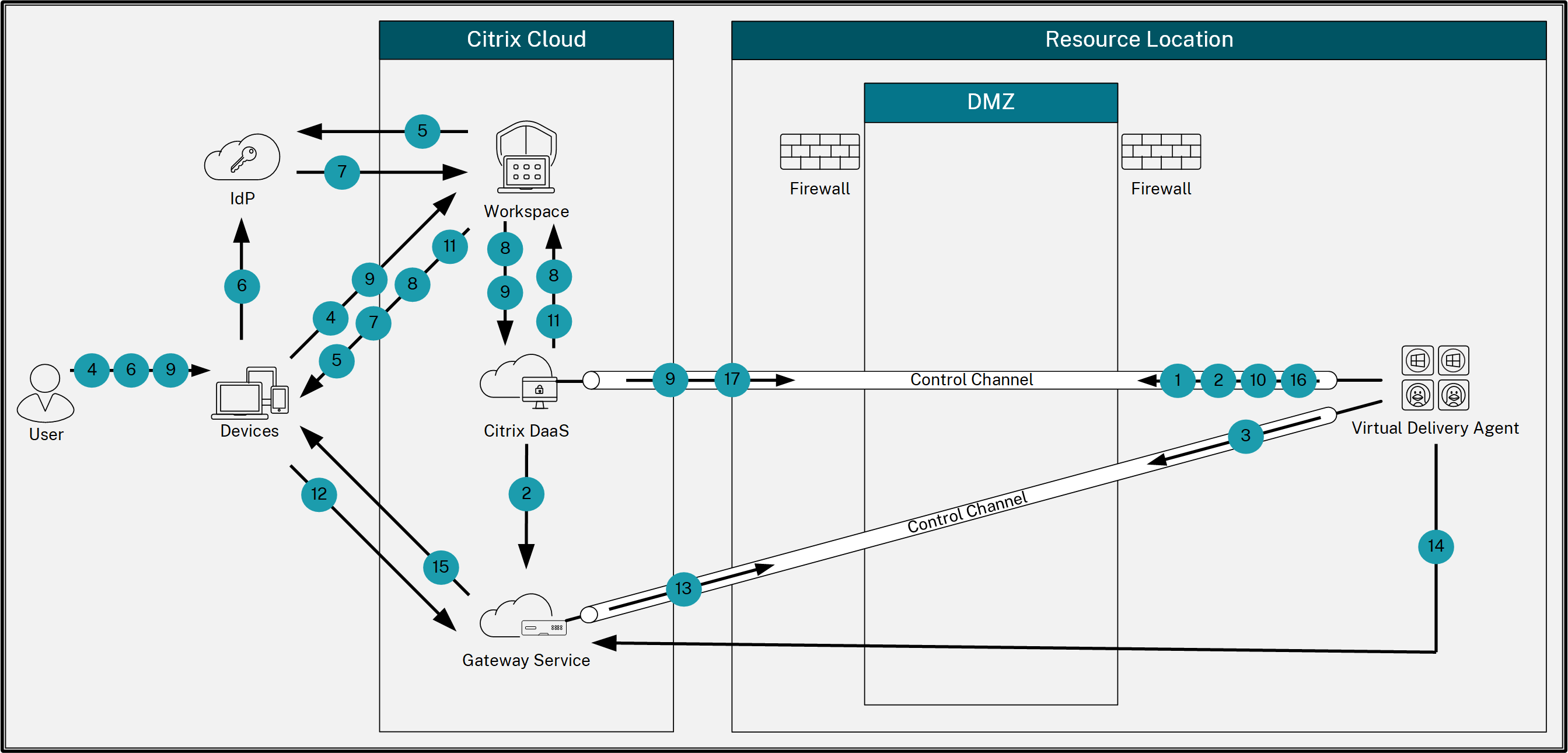
- The VDA establishes a WebSocket connection with Citrix Cloud and registers.
- The VDA registers with Citrix Gateway Service and obtains a dedicated token.
- The VDA establishes a persistent control connection with the Gateway Service.
- The user navigates to Citrix Workspace.
- Workspace evaluates authentication configuration and redirects users to the appropriate IdP for authentication.
- The user enters their credentials.
- After successfully validating the user credentials, the user is redirected to Workspace.
- Workspace counts resources for the user and displays them.
- The user selects a desktop or application from Workspace. Workspace sends the request to Citrix DaaS, which brokers the connection and instructs the VDA to prepare for the session.
- The VDA responds with the Rendezvous capability and its identity.
- Citrix DaaS generates a launch ticket and sends it to the user device through Workspace.
- The user’s endpoint connects to the Gateway Service and provides the launch ticket to authenticate and identify the resource to connect to.
- The Gateway Service sends the connection information to the VDA.
- The VDA establishes a direct connection for the session with the Gateway Service.
- The Gateway Service completes the connection between the endpoint and the VDA.
- The VDA verifies licensing for the session.
- Citrix DaaS sends applicable policies to the VDA.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.