Client certificate or certificate plus domain authentication
The default configuration for Citrix Endpoint Management is user name and password authentication. To add another layer of security for enrollment and access to Citrix Endpoint Management environment, consider using certificate-based authentication. In the Citrix Endpoint Management environment, this configuration is the best combination of security and user experience. Certificate plus domain authentication has the best SSO possibilities coupled with the security provided by two-factor authentication at NetScaler Gateway.
For optimal usability, you can combine certificate plus domain authentication with Citrix PIN and Active Directory password caching. As a result, users don’t have to enter their LDAP user names and passwords repeatedly. Users enter user names and passwords for enrollment, password expiration, and account lockout.
Important:
Citrix Endpoint Management doesn’t support changing the authentication mode from domain authentication to some other authentication mode after users enroll devices in Citrix Endpoint Management.
If you don’t allow LDAP and use smart cards or similar methods, configuring certificates allows you to represent a smart card to Citrix Endpoint Management. Users then enroll using a unique PIN that Citrix Endpoint Management generates for them. After a user has access, Citrix Endpoint Management then creates and deploys the certificate used to authenticate to the Citrix Endpoint Management environment.
You can use the NetScaler for XenMobile wizard to do the configuration required for Citrix Endpoint Management when using NetScaler Gateway certificate-only authentication or certificate plus domain authentication. You can run the NetScaler for XenMobile wizard one time only.
In highly secure environments, usage of LDAP credentials outside of an organization in public or insecure networks is considered a prime security threat for the organization. For highly secure environments, two-factor authentication that uses a client certificate and a security token is an option. For more information, see Configuring Citrix Endpoint Management for Certificate and Security Token Authentication.
Client certificate authentication is available for devices enrolled in MAM and MDM+MAM. To use client certificate authentication for those devices, you must configure the Microsoft server, Citrix Endpoint Management, and then NetScaler Gateway. Follow these general steps, as described in this article.
On the Microsoft server:
- Add a certificate snap-in to the Microsoft Management Console.
- Add the template to Certificate Authority (CA).
- Create a PFX certificate from the CA server.
On Citrix Endpoint Management:
- Upload the certificate to Citrix Endpoint Management.
- Create the PKI entity for certificate-based authentication.
- Configure credentials providers.
- Configure NetScaler Gateway to deliver a user certificate for authentication.
For information about the NetScaler Gateway configuration, see these articles in the Citrix ADC documentation:
- Client authentication
- SSL profile infrastructure
- Configuring and Binding a Client Certificate Authentication Policy.
Prerequisites
-
When you create a Microsoft Certificate Services Entity template, avoid possible authentication issues with enrolled devices by excluding special characters. For example, don’t use these characters in the template name:
: ! $ () # % + * ~ ? | {} [] - To configure Certificate-based Authentication for Exchange ActiveSync, see the Microsoft documentation on Exchange Server. Configure the certificate authority (CA) server site for Exchange ActiceSync to require client certificates.
- If you use private server certificates to secure the ActiveSync traffic to the Exchange Server, make sure that the mobile devices have all of the Root/Intermediate certificates. Otherwise, certificate-based authentication fails during the mailbox setup in Citrix Secure Mail. In the Exchange IIS Console, you must:
- Add a website for Citrix Endpoint Management use with Exchange and bind the web server certificate.
- Use port 9443.
- For that website, you must add two applications, one for “Microsoft-Server-ActiveSync” and one for “EWS”. For both of those applications, under SSL Settings, select Require SSL.
Add a certificate snap-in to the Microsoft Management Console
-
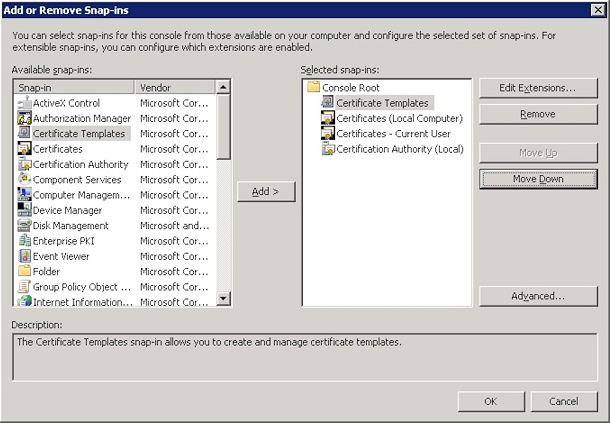
Open the console and then click Add/Remove Snap-ins.
-
Add the following snap-ins:
- Certificate Templates
- Certificates (Local Computer)
- Certificates - Current User
- Certificate Authority (Local)
-
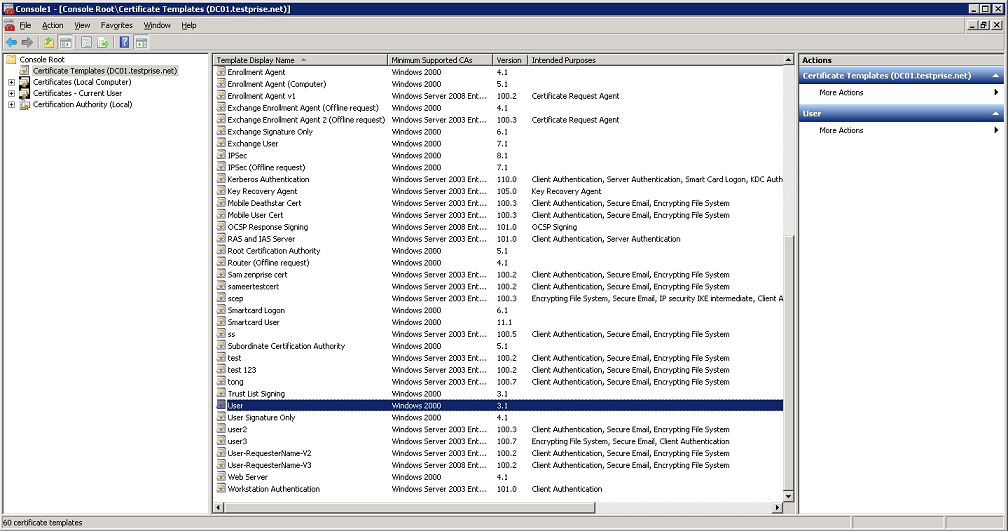
Expand Certificate Templates.
-
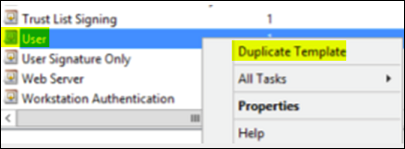
Select the User template and Duplicate Template.
-
Provide the Template display name.
Important:
It is not recommended to select the Publish certificate in Active Directory option. If this option is selected, it creates client certificates for all users in Active Directory, which might clutter your Active Directory database.
-
Select Windows 2003 Server for the template type. In the Windows 2012 R2 server, under Compatibility, select Certificate authority, and set the recipient as Windows 2003.
-
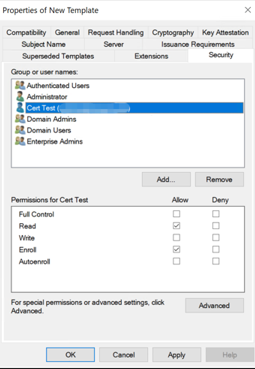
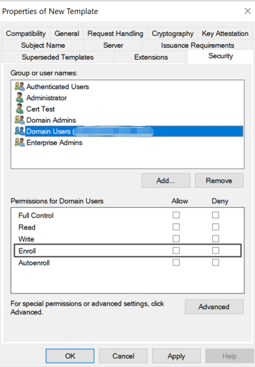
Under Security, configure the following:
-
Click Add and then select the AD user account that Citrix Endpoint Management uses to generate certificates.
Important:
Add only the service account user here. Add the Enroll permission only to this AD user account.
As described later in this article, you create a user .pfx certificate using the service account. For information, see Creating a PFX certificate from the CA server.
-
Revoke the Enroll permission from Domain Users.
-
-
Under Cryptography, make sure that you provide the key size. You later enter the key size during Citrix Endpoint Management configuration.

-
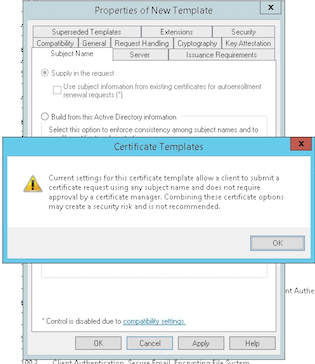
Under Subject Name, select Supply in the request. Apply the changes and then save.
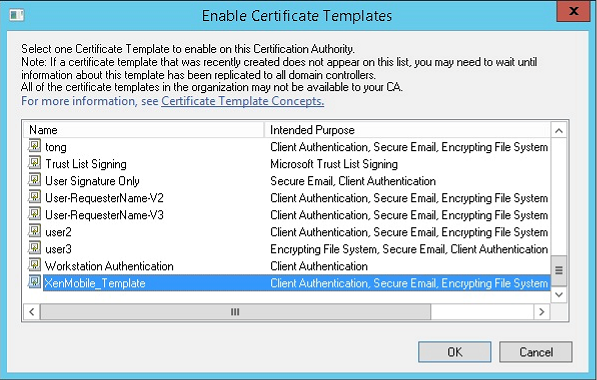
Adding the template to Certificate Authority
-
Go to Certificate Authority and select Certificate Templates.
-
Right-click in the right pane and then select New > Certificate Template to Issue.
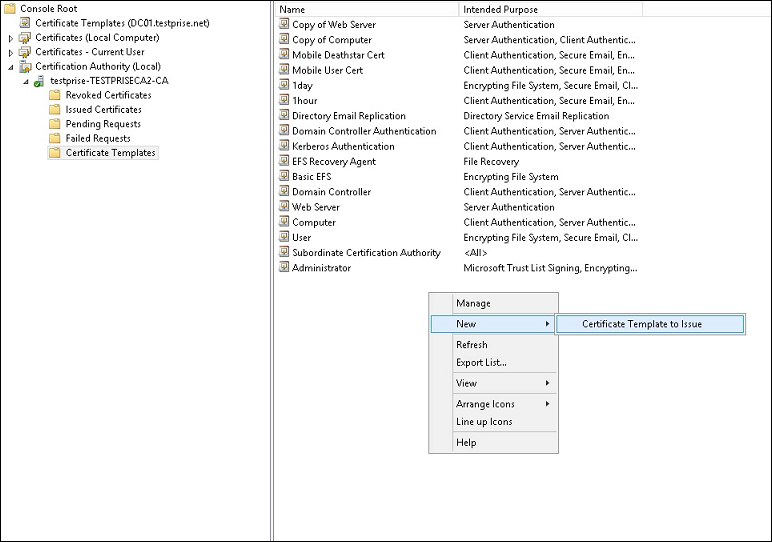
-
Select the template that you created in the previous step and then click OK to add it into the Certificate Authority.
Creating a PFX certificate from the CA server
-
Create a user .pfx cert using the service account with which you logged in. The .pfx uploads to Citrix Endpoint Management, which then requests a user certificate for the users who enroll their devices.
-
Under Current User, expand Certificates.
-
Right-click in the right pane and then click Request New Certificate.
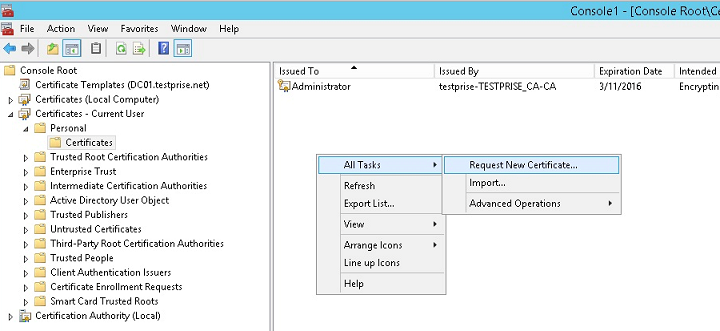
-
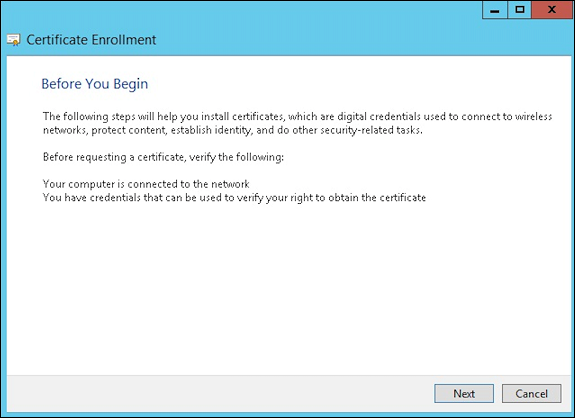
The Certificate Enrollment screen appears. Click Next.
-
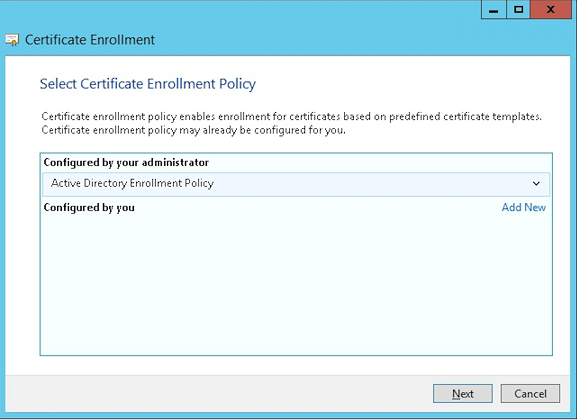
Select Active Directory Enrollment Policy and then click Next.
-
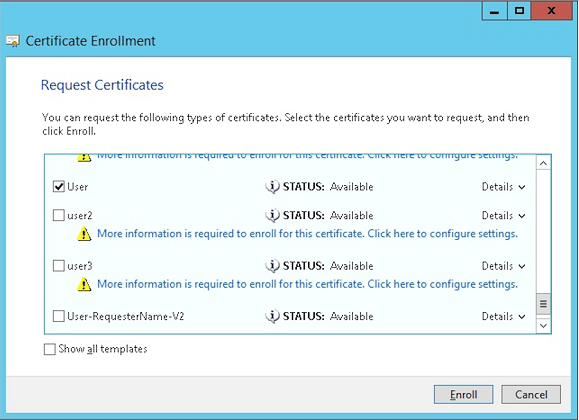
Select the User template and then click Enroll.
-
Export the .pfx file that you created in the previous step.
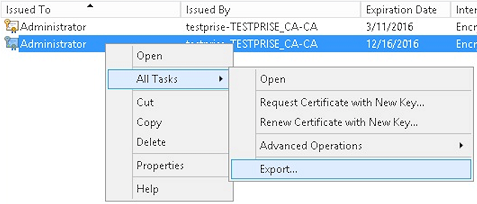
-
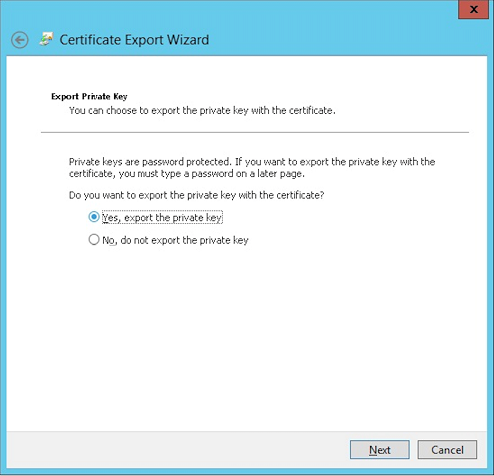
Click Yes, export the private key.
-
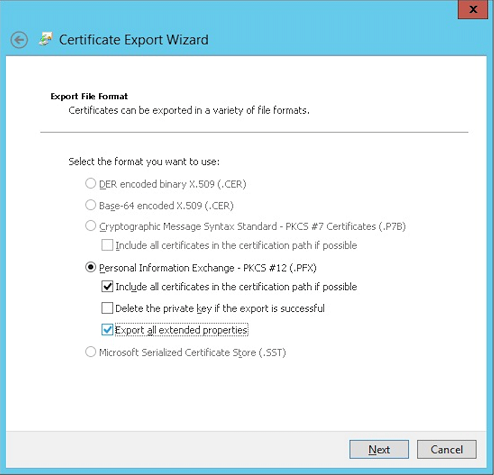
Select Include all certificates in the certification path if possible and select the Export all extended properties checkbox.
-
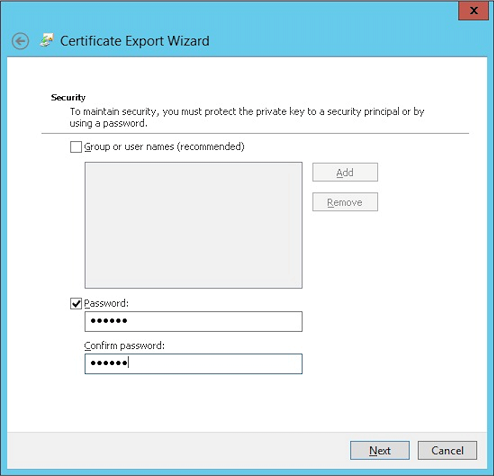
Set a password to use when uploading this certificate into Citrix Endpoint Management.
-
Save the certificate onto your hard drive.
Uploading the certificate to Citrix Endpoint Management
-
In the Citrix Endpoint Management console, click the gear icon in the upper-right corner. The Settings screen appears.
-
Click Certificates and then click Import.
-
Enter the following parameters:
- Import: Keystore
- Keystore type: PKCS #12
- Use as: Server
- Keystore file: Click Browse to select the .pfx certificate you created.
- Password: Enter the password that you created for this certificate.
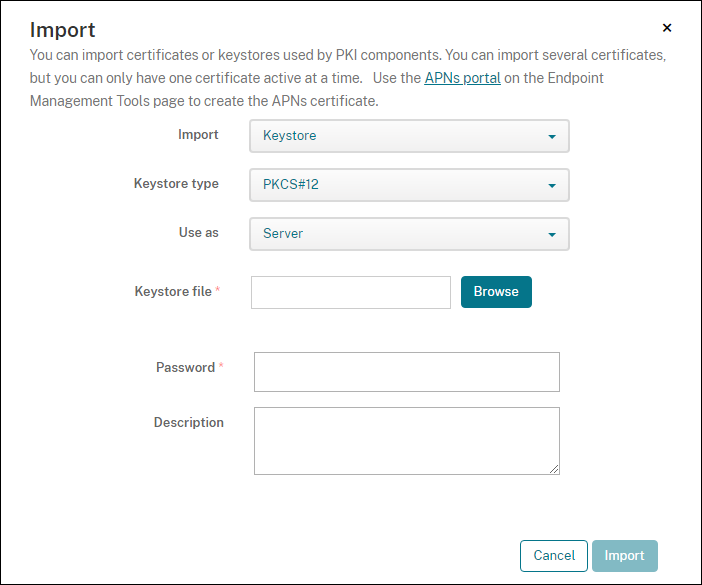
-
Click Import.
-
Verify that the certificate installed correctly. A correctly installed certificate displays as a User certificate.
Creating the PKI entity for certificate-based authentication
-
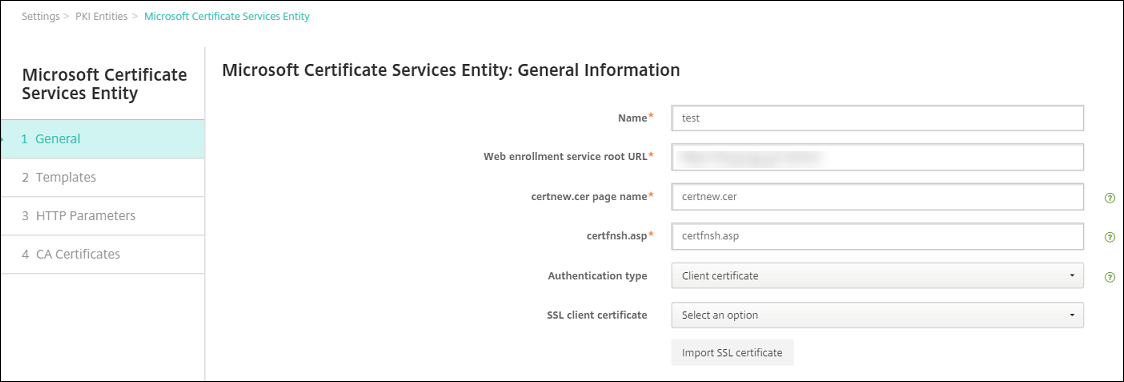
In Settings, go to More > Certificate Management > PKI Entities.
-
Click Add and then click Microsoft Certificate Services Entity. The Microsoft Certificate Services Entity: General Information screen appears.
-
Enter the following parameters:
- Name: Type any name.
-
Web enrollment service root URL:
https://RootCA-URL/certsrv/(Be sure to add the last slash, /, in the URL path.) - certnew.cer page name: certnew.cer (default value)
- certfnsh.asp: certfnsh.asp (default value)
- Authentication type: Client certificate
- SSL client certificate: Select the user certificate to be used to issue the Citrix Endpoint Management client certificate. If no certificate exists, follow the procedure in the preceding section to upload certificates.
-
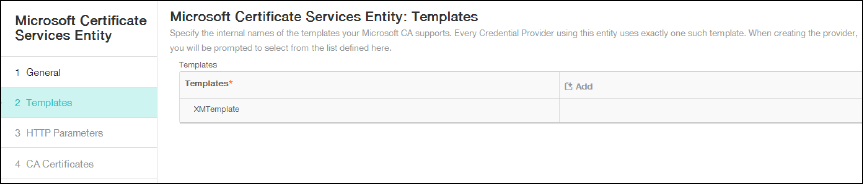
Under Templates, add the template that you created when configuring the Microsoft certificate. Don’t add spaces.
-
Skip HTTP Parameters and then click CA Certificates.
-
Select the root CA name that corresponds to your environment. This root CA is part of the chain imported from the Citrix Endpoint Management client certificate.
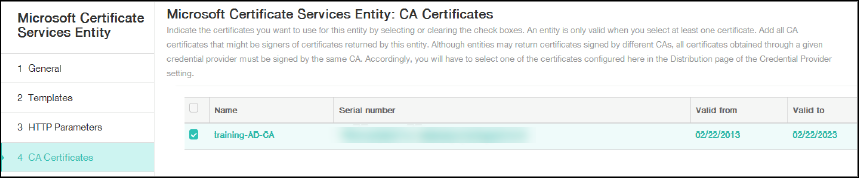
-
Click Save.
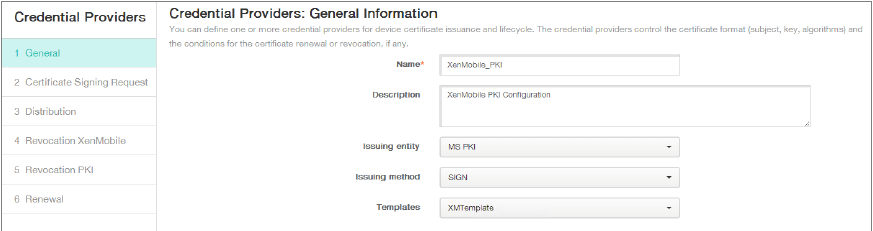
Configuring credentials providers
-
In Settings, go to More > Certificate Management > Credential Providers.
-
Click Add.
-
Under General, enter the following parameters:
- Name: Type any name.
- Description: Type any description.
- Issuing entity: Select the PKI entity created earlier.
- Issuing method: SIGN
- Templates: Select the template added under the PKI entity.
-
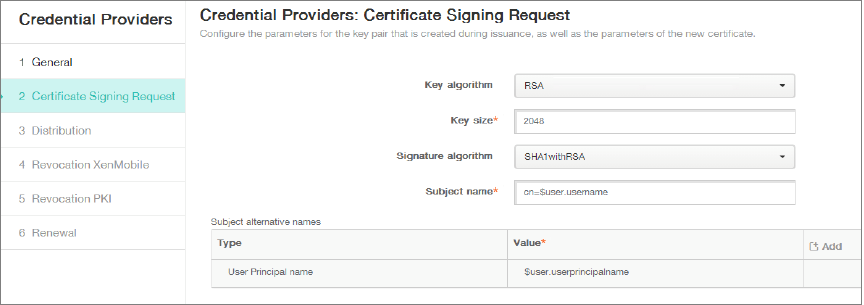
Click Certificate Signing Request and then enter the following parameters:
- Key algorithm: RSA
- Key size: 2048
- Signature algorithm: SHA256withRSA
-
Subject name:
cn=$user.username
For Subject Alternative Names, click Add and then enter the following parameters:
- Type: User Principal name
-
Value:
$user.userprincipalname
-
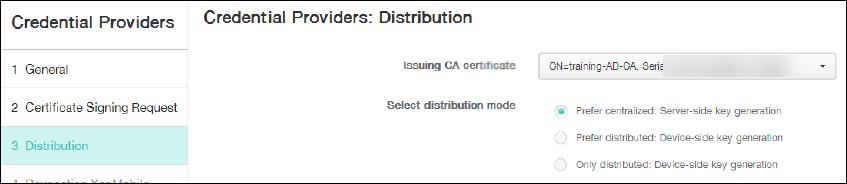
Click Distribution and enter the following parameters:
- Issuing CA certificate: Select the Issuing CA that signed the Citrix Endpoint Management Client Certificate.
- Select distribution mode: Select Prefer centralized: Server-side key generation.
-
For the next two sections, Revocation Citrix Endpoint Management and Revocation PKI, set the parameters as required. In this example, both options are skipped.
-
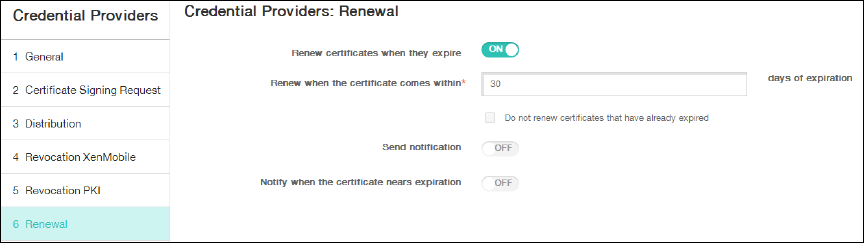
Click Renewal.
-
Enable Renew certificates when they expire.
-
Leave all other settings as default or change them as required.
-
Click Save.
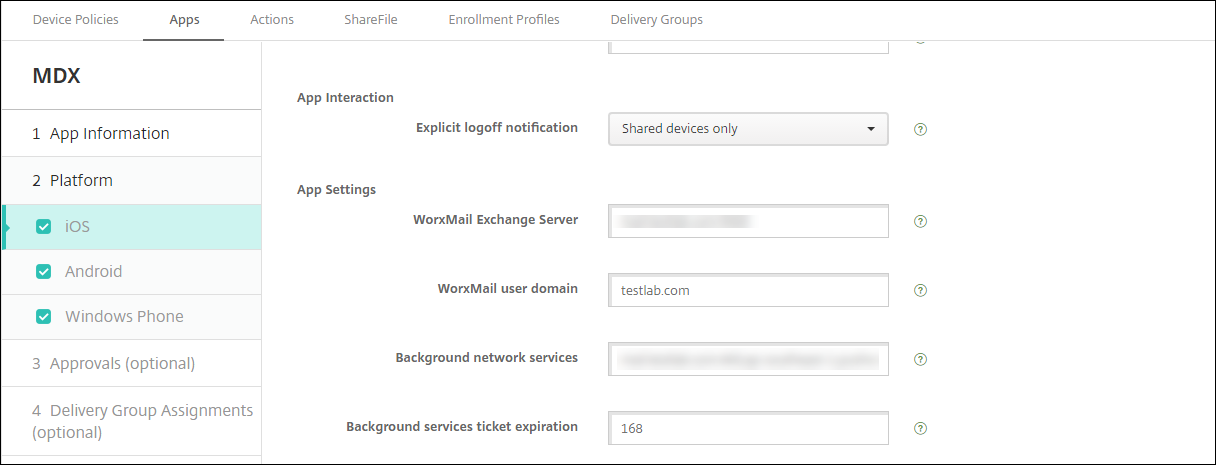
Configuring Citrix Secure Mail to use certificate-based authentication
When you add Citrix Secure Mail to Citrix Endpoint Management, be sure to configure the Exchange settings under App Settings.
Configuring NetScaler Gateway certificate delivery in Citrix Endpoint Management
-
In the Citrix Endpoint Management console, click the gear icon in the upper-right corner. The Settings screen appears.
-
Under Server, click NetScaler Gateway.
-
If NetScaler Gateway isn’t already added, click Add and specify the settings:
- Name: A descriptive name for the appliance.
- Alias: An optional alias for the appliance.
-
External URL:
https://YourCitrixGatewayURL - Logon Type: Select Certificate and domain
- Password Required: Off
- Set as Default: On
-
For Authentication and Deliver user certificate for authentication, select On.
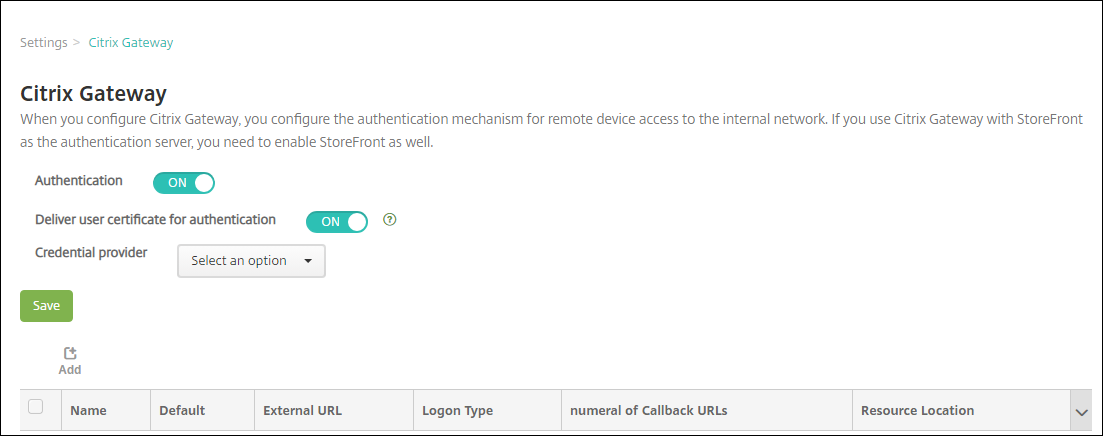
-
For Credential Provider, select a provider and then click Save.
-
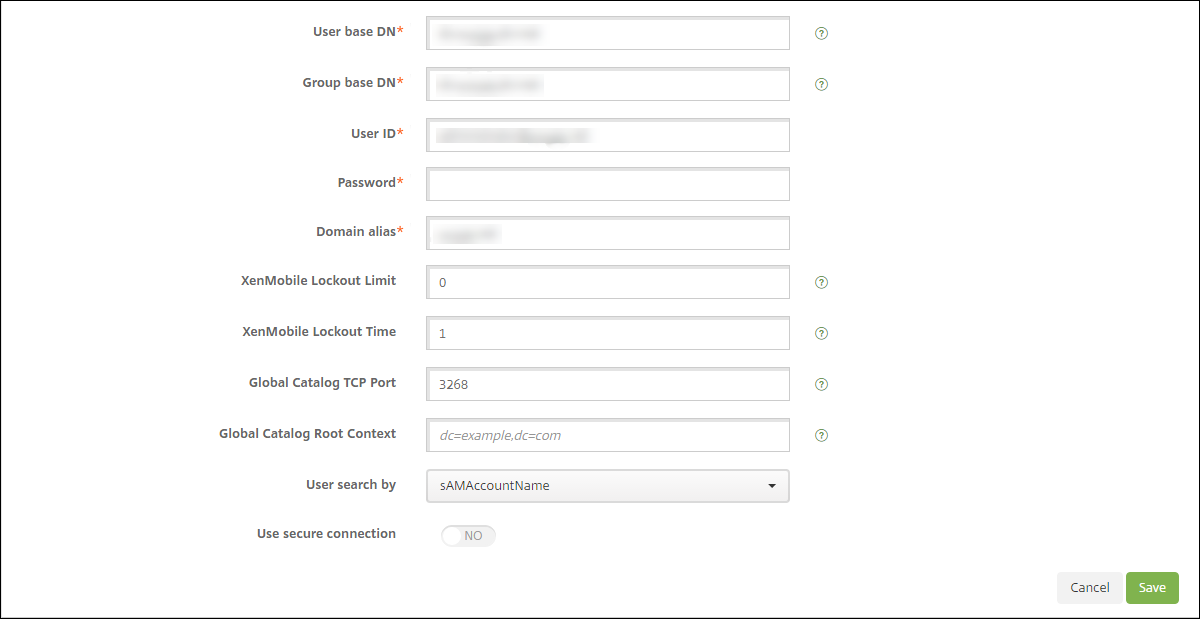
To use the sAMAccount attributes in the user certificates as an alternative to User Principal Name (UPN), configure the LDAP connector in Citrix Endpoint Management as follows: Go to Settings > LDAP, select the directory and click Edit, and select sAMAccountName in User search by.
Enable Citrix PIN and user password caching
To enable Citrix PIN and user password caching, go to Settings > Client Properties and select these checkboxes: Enable Citrix PIN Authentication and Enable User Password Caching. For more information, see Client properties.
Troubleshooting your client certificate configuration
After a successful configuration of the preceding configuration plus the NetScaler Gateway configuration, the user workflow is as follows:
-
Users enroll their mobile device.
-
Citrix Endpoint Management prompts users to create a Citrix PIN.
-
Users are then redirected to the app store.
-
When users start Citrix Secure Mail, Citrix Endpoint Management doesn’t prompt them for user credentials for mailbox configuration. Instead, Citrix Secure Mail requests the client certificate from Citrix Secure Hub and submits it to the Microsoft Exchange Server for authentication. If Citrix Endpoint Management prompts for credentials when users start Citrix Secure Mail, check your configuration.
If users can download and install Citrix Secure Mail, but during the mailbox configuration Citrix Secure Mail fails to finish the configuration:
-
If Microsoft Exchange Server ActiveSync uses private SSL server certificates to secure the traffic, verify that the Root/Intermediate certificates installed on the mobile device.
-
Verify that the authentication type selected for ActiveSync is set as Require client certificates.
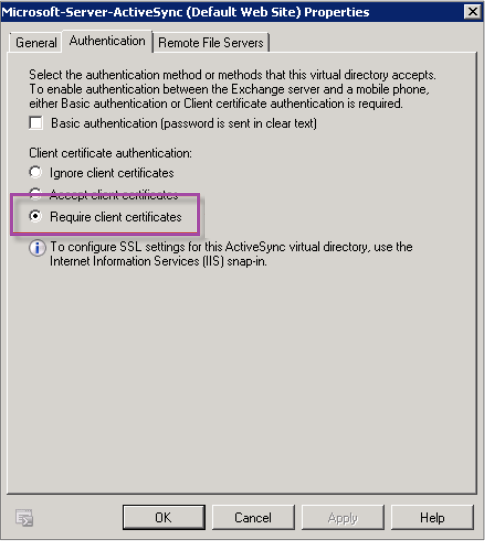
-
On the Microsoft Exchange Server, check the Microsoft-Server-ActiveSync site to verify that client certificate mapping authentication is enabled. By default client certificate mapping authentication is disabled. The option is under Configuration Editor > Security > Authentication.
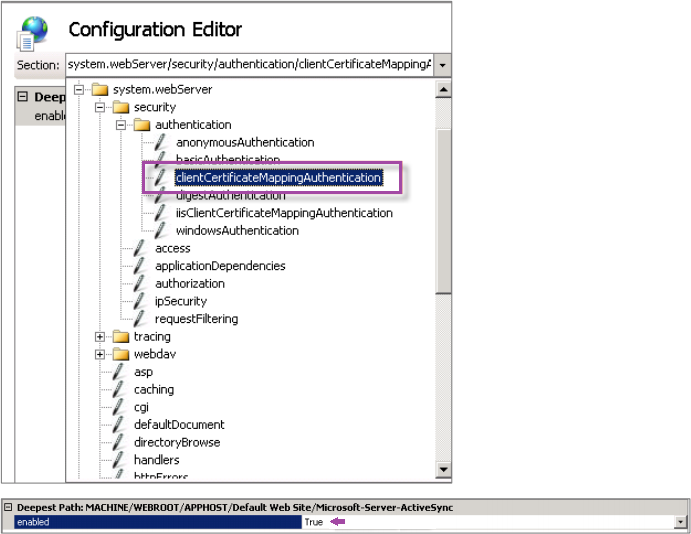
After selecting True, be sure to click Apply for the changes take effect.
-
Check the NetScaler Gateway settings in the Citrix Endpoint Management console: Make sure that Deliver user certificate for authentication is On and that Credential provider has the correct profile selected.
To determine if the client certificate was delivered to a mobile device
-
In the Citrix Endpoint Management console, go to Manage > Devices and select the device.
-
Click Edit or Show More.
-
Go to the Delivery Groups section, and search for this entry:
NetScaler Gateway Credentials: Requested credential, CertId=
To validate whether client certificate negotiation is enabled
-
Run this
netshcommand to show the SSL Certificate configuration that is bound on the IIS website:netsh http show sslcert -
If the value for Negotiate Client Certificate is Disabled, run the following command to enable it:
netsh http delete sslcert ipport=0.0.0.0:443netsh http add sslcert ipport=0.0.0.0:443 certhash=cert_hash appid={app_id} certstorename=store_name verifyclientcertrevocation=Enable VerifyRevocationWithCachedClientCertOnly=Disable UsageCheck=Enable clientcertnegotiation=EnableFor example:
netsh http add sslcert ipport=0.0.0.0:443 certhash=23498dfsdfhaf98rhkjqf9823rkjhdasf98asfk appid={123asd456jd-a12b-3c45-d678-123456lkjhgf} certstorename=ExampleCertStoreName verifyclientcertrevocation=Enable VerifyRevocationWithCachedClientCertOnly=Disable UsageCheck=Enable clientcertnegotiation=Enable
If you cannot deliver Root/Intermediate certificates to a Windows Phone 8.1 device through Citrix Endpoint Management:
- Send Root/Intermediate certificates (.cer) files through email to the Windows Phone 8.1 device and install them directly.
If Citrix Secure Mail doesn’t install successfully on Windows Phone 8.1, verify the following:
- The Application Enrollment Token (.AETX file) is delivered through Citrix Endpoint Management using the Enterprise Hub device policy.
- The Application Enrollment Token was created using the same Enterprise Certificate from the certificate provider used to wrap Citrix Secure Mail and sign Citrix Secure Hub apps.
- The same Publisher ID is used to sign and wrap Citrix Secure Hub, Citrix Secure Mail, and the Application Enrollment Token.
In this article
- Prerequisites
- Add a certificate snap-in to the Microsoft Management Console
- Adding the template to Certificate Authority
- Creating a PFX certificate from the CA server
- Uploading the certificate to Citrix Endpoint Management
- Creating the PKI entity for certificate-based authentication
- Configuring credentials providers
- Configuring Citrix Secure Mail to use certificate-based authentication
- Configuring NetScaler Gateway certificate delivery in Citrix Endpoint Management
- Troubleshooting your client certificate configuration