Citrix Virtual Apps and Desktops™ 7 2511
关于本版本
此 Citrix Virtual Apps and Desktops 版本包含新版 Windows Virtual Delivery Agent (VDA) 和多个核心组件的新版本。您可以:
-
安装或升级站点:使用此版本的 ISO 安装或升级核心组件和 VDA。安装或升级到最新版本可让您使用最新功能。
-
在现有站点中安装或升级 VDA:如果您已有部署且尚未准备好升级核心组件,仍可通过安装(或升级到)新 VDA 来使用多项最新的 HDX™ 功能。仅升级 VDA 在您希望在非生产环境中测试增强功能时会很有帮助。
将 VDA 升级到此版本后,无需更新计算机目录的功能级别。有关详细信息,请参阅VDA 版本和功能级别。
有关安装和升级说明:
Delivery Controller
Delivery Controller 升级的 LocalDB 自动安装
升级 Delivery Controller 时,元安装程序会自动安装最新支持的 SQL Server Express LocalDB 版本。此增强功能可简化您的升级过程。它可确保本地主机缓存数据库的兼容性,而无需手动安装 LocalDB。有关详细信息,请参阅自动更新。
HDX
设备
WIA 重定向增强功能
管理员不再需要在 VDA 上进行任何注册表更改即可使用 WIA 重定向。他们只需在 Studio 中启用 WIA 重定向策略设置即可。
USB 诊断工具增强功能
USB 诊断工具现在支持管理员和域用户,新增了“建议”部分,用于标记配置问题并提出优化建议。
改进了多跳会话的键盘和条形码输入可靠性
此功能增强了在扫描码输入模式下运行的非 Windows 客户端的输入可靠性,并确保 Windows VDA 按顺序处理按键事件,从而消除了RDP 双跳会话期间的字符错误,并确保条形码扫描仪正确呈现数字而不是特殊字符。
多媒体
优化了覆盖剪裁以增强性能和用户体验
多媒体优化功能(例如 HDX Microsoft Teams 优化和 UCSDK 优化)的覆盖剪裁机制已重新设计,以增强性能和视觉准确性。
此增强功能通过解决应用程序元素(例如菜单或通知)错误地出现在视频内容后面的视觉故障,提供了更无缝的用户体验。
新方法还取代了资源密集型方法,可显著降低 VDA 上的 CPU 利用率。有关详细信息,请参阅 MTOP 功能参考或 UCSDK 功能参考。
浏览器内容重定向的单点登录支持
浏览器内容重定向现在通过单点登录支持提供简化的用户体验,从而实现 VDA 侧身份验证和 Cookie 共享。此增强功能消除了冗余登录,通过在 BCR 会话中(即使在 BCR 窗口关闭后)保持身份验证和 Cookie 持久性来提高工作效率。这种无缝体验通过确保身份验证源自 VDA 而非客户端,进一步增强了安全性。
有关详细信息,请参阅 浏览器内容重定向文档。
浏览器内容重定向的服务器端证书验证
浏览器内容重定向通过支持证书验证得到了进一步增强。当从客户端访问重定向的网站时,客户端叠加浏览器可能不信任来自服务器或 MitM 代理的证书。在这种情况下,BCR 现在可以根据 VDA 的证书存储来验证主机或代理证书。
有关详细信息,请参阅服务器端证书验证文档。
图形
HDX 图形通用改进
此版本对 HDX 图形进行了显著改进,可显著降低 VDA 上的 CPU、内存和带宽消耗。除了性能改进之外,客户还将注意到 LAN 网络上开箱即用的图像质量更高。
Director 的 HDX 屏幕共享
HDX 屏幕共享可用于通过 Citrix Director 对 Citrix Virtual Apps and Desktops 本地部署进行影子会话,以及通过 Citrix Monitor 对 Citrix Cloud 部署进行影子会话。HDX 屏幕共享是新的影子会话方法,它提供了一种原生、低延迟的替代方案,取代了当前的影子会话。Director 的 HDX 屏幕共享适用于所有 VDA,包括未加入域和已加入 Entra ID 的 VDA。
HDX 屏幕共享改进
HDX 屏幕共享改进包括用于控制 HDX 屏幕共享端口和超时的配置策略。
支持 AMD V710 GPU
增加了对 AMD V710 GPU 的支持。
无缝应用程序
无缝应用程序改进
无缝应用程序现在支持透明窗口和动态窗口预览 (Windows peek)。
无缝应用程序的 Windows 辅助功能设置
无缝应用程序的 Windows 辅助功能设置现在默认对所有无缝会话启用。
HDX 连接
HDX Direct
已添加新事件,用于记录外部用户的额外 HDX Direct 状态详细信息。有关更多详细信息,请参阅 HDX Direct 故障排除。
Virtual Delivery Agents (VDA)
通过命令行生成自定义脚本以安装或升级 VDA
引入了一项新功能,用于通过命令行生成自定义脚本以安装或升级 VDA。在 VDA 安装程序 UI 中,用户现在可以创建用于无人值守安装或升级的自定义脚本。此增强功能提供了有关配置、保存和执行这些脚本的分步指导,其中包含安装程序路径和 WebSocket 令牌等参数。此功能显著提高了部署过程的自动化和准确性。
VDA Meta Installer 助手工具
现在提供了一个新的 VDA 元安装程序助手工具,以简化 VDA 安装和故障排除。它有助于验证和生成 SCCM 任务序列,确保与 VDA 安装要求兼容。该工具还包括一个日志分析器,可审查安装日志,突出显示错误或警告,并提供解决方案建议。通过简单的 MSI 安装和易于使用的界面,它有助于 IT 管理员更高效地部署 VDA 并减少问题。
VDA Meta 安装程序更改
Citrix Virtual Apps and Desktops 7 2511 引入了在 VDA 中集成安装 Citrix Device Trust、uberAgent 和 Workspace Environment Management 代理的功能,并提供灵活的命令行选项(如 /components 和 /exclude)来自定义安装、升级或卸载组件,例如 Citrix Workspace app、Secure Access Client 和 User Personalization Layer,而单会话和多会话 OS VDA 之间的默认行为和组件选择有所不同。有关详细信息,请参阅安装 VDA 和使用命令行安装。
用于单会话核心服务虚拟投递代理的新型元安装程序
现在,Windows 365 云电脑和远程电脑部署可使用新型轻量级单会话 VDA 元安装程序。此安装程序基于现有远程电脑安装程序构建,是完整单会话 VDA 的精简版,可提供核心 VDA 组件以及配置文件管理、deviceTRUST、uberAgent、WEM、备份和还原以及 VDA 升级代理。它显著减小程序包大小并提高基于云的工作负载的安装可靠性。此安装程序专为现代远程电脑场景设计,为在 Windows 365 和远程电脑上部署 Citrix 工作负载提供了简化且高性能的选项。
Citrix 始终在线跟踪
适用于所有 CVAD 组件的 Citrix AOT
最新更新引入了始终在线跟踪 (AOT) 的重大扩展,使跨整个 Citrix 环境收集、集中和分析日志变得更加容易。Web Studio 中的新配置体验允许管理员定义日志服务器、控制日志记录范围以及从一个位置启用 Director 访问,所有设置都会通过站点数据库自动传播。Director 现在包含一个专用的“日志”视图,使管理员能够通过搜索、时间筛选器、类别、严重性筛选器和计算机级别筛选实时查看 AOT 事件。AOT 覆盖范围已扩展到更多 Citrix 组件,包括所有核心组件(Mac VDA、Linux VDA、FAS 和会话录制服务器等),从而在控制平面和数据平面工作流中实现真正的端到端跟踪。
AOT 日志服务器已得到增强,具有更好的引入性能,支持每个节点多达 10,000 个组件,并使用 LZ4 改进压缩以实现更高效的存储。新的大小调整指南和性能基准可帮助管理员规划容量并调整其环境的存储和 IOPS。独立组件现在可以通过简单的 PowerShell 命令将日志推送到日志服务器,使其与集中式日志记录模型保持一致。了解更多信息并在此处开始部署。
Web Studio
在 AWS 本地可用区中预配工作负载
您现在可以直接在 AWS 本地可用区中预配 Amazon WorkSpaces Core 托管实例和 EC2 工作负载。此新功能可帮助您:
- 通过将 Citrix 工作负载部署到更靠近最终用户的位置,为最终用户提供低延迟访问。
- 在没有完整 AWS 区域服务的区域中,提高 Citrix 基础架构的区域覆盖范围。
您可以在所需的本地可用区中创建具有托管单元的主机连接,然后在该本地可用区中预配 VM。
有关详细信息,请参阅:
- Amazon WorkSpaces Core 托管实例:
-
AWS EC2:
使用 Web Studio 在 AWS EC2 中进行跨账户预配
在某些用例中,Cloud Connector 可能需要放置在单独的 AWS 账户(共享服务账户或站点组件账户)中,其中 IAM 角色具有跨账户访问权限(跨账户 IAM 角色),并且 MCS 预配的计算机目录位于单独的辅助 AWS 账户(工作负载账户)中,而无需在单独的账户中额外部署 Cloud Connector。这种部署模型已通过 PowerShell SDK 得到支持,现在也通过 Web Studio UI 得到支持。
AWS EC2 中的备份 VM 配置
Web Studio 现在允许您在 AWS 环境中定义备份 EC2 实例类型列表(可以是按需实例或 Spot 实例的“备份 SKU”),以便在出现容量相关问题时,Machine Creation Services (MCS) 可以回退到这些实例类型。MCS 会尝试按照您提供的列表中的顺序回退到备份 EC2 实例类型。有关详细信息,请参阅使用 Studio 创建目录。
AWS EC2 安全组配置
当您在 Web Studio 中使用计算机配置文件创建或编辑目录时,安全组配置过程已得到简化。您不再需要手动配置安全组,并且会跳过专用配置页面,从而确保与计算机配置文件设置的一致性。现有非计算机配置文件目录的工作流保持不变。此外,租用类型选择菜单已从目录创建向导中的“安全”选项卡重新定位到“虚拟机”选项卡。有关详细信息,请参阅使用 Web Studio 创建目录。
在 Azure 中跨区域共享加密的准备好的映像
Azure Compute Gallery (ACG) 映像可以使用磁盘加密集 (DES) 进行加密。借助此功能,您可以使用 DES 在同一订阅和租户中的多个区域之间共享加密的准备好的 ACG 映像。之后,您可以在共享加密的准备好的映像的区域中创建计算机目录。有关详细信息,请参阅跨区域、订阅、租户共享加密的准备好的映像。
在 Azure 中为 MCS 计算机目录启用 ZRS
您现在可以为 Azure MCS 计算机目录中的磁盘配置配置区域冗余存储 (ZRS)。此增强功能有助于:
- 提高 VM 抵御区域级中断的复原能力。
- 使 Azure 能够在任何可用区域中启动 VM,从而增强 VM 放置灵活性。
- 通过确保 VM 可用性(即使磁盘的原始区域不可用),克服本地冗余存储 (LRS) 的限制。
您可以在创建和编辑现有 Azure MCS 计算机目录时配置 ZRS。
有关详细信息,请参阅:
显示用于临时 OSDisk 用途的 NVMe v6 SKU
您现在可以使用 Web Studio 将临时 OS 磁盘存储在 NVMe 磁盘上。有关详细信息,请参阅Azure 临时磁盘。
使用 Web Studio 支持 Azure 机密 VM 的映像管理
您现在可以使用映像节点来准备和管理与 Azure 机密 VM 兼容的映像。您还可以使用 PowerShell 命令来实现此目标。有关详细信息,请参阅Azure 机密 VM。
在 Azure 中选择本地冗余存储 (LRS) 类型或区域冗余存储类型选项
Web Studio 现在允许您在创建计算机目录时,选择本地冗余存储 (LRS) 类型和区域冗余存储 (ZRS) 类型作为数据恢复选项。您可以查看这些冗余存储类型各自的优势,并根据您的要求进行选择。
与 AHV 上的 Nutanix Prism Central 集成
您现在可以使用新的主机连接 Nutanix AHV Prism Central,通过 Nutanix Prism Central 将 Citrix Virtual Apps and Desktops 环境连接到 Nutanix AHV 群集。
使用 Nutanix AHV Prism Central 主机连接的优势包括:
- 支持仅电源管理和 MCS 预配 VDA 的计算机目录。
- 通过模板版本实现 MCS 主 VM 在 AHV 群集之间的共享。
- 简化主机连接上的证书信任。
- 无需单独在 Delivery Controller 上安装插件。
有关详细信息,请参阅:
在 Azure Local 上预配 Windows 和 Linux 虚拟机
您现在可以使用 MCS 在 Azure Local 上预配和管理 MCS 计算机目录以及 Citrix Provisioning 目录,以用于 Windows 和 Linux VM。
对于 Windows VM,您可以创建和管理托管连接和单元,预配 Windows 10/11 单会话和 Windows Server 多会话 VM(包括持久和非持久)。您还可以在创建新 VM 后更新网络、回写缓存 (WBC) 或 AD 服务帐户设置。这支持本地 AD、未加入域和 Entra 混合加入设备。
对于 Linux VM,此功能支持 Ubuntu、CentOS、Red Hat Enterprise 和 SUSE。您可以预配包含这些 OS 类型的目录,部署持久和非持久 Linux VM,与本地 AD 或未加入域的 VM 集成以进行身份验证,管理主机单元(包括存储和网络设置),以及对目录中新预配的 VM 执行配置更改。
有关详细信息,请参阅:
- 连接到 Azure Local
- 创建 Azure Local 目录
- Citrix Provisioning 文档:在 Citrix Studio 中创建 Citrix Provisioning™ 目录
在 XenServer 中管理准备好的映像版本
映像管理功能现已在 XenServer 虚拟化环境中普遍可用。您可以使用映像节点创建多个映像版本,并将其应用或更新到多个计算机目录。此实现显著降低了存储和时间成本,并简化了 VM 部署和映像更新过程。您还可以使用 PowerShell 命令来实现此目标。有关详细信息,请参阅在 XenServer 中创建准备好的映像计算机目录。
在分配准备好的映像时添加备注
借助此功能,您现在可以在使用准备好的映像创建或更新 MCS 目录时,使用 Web Studio 和 PowerShell 添加自定义备注。MCS 会保留所有准备好的映像分配记录。这有助于您:
- 检索分配给目录的所有准备好的映像的映像分配历史记录。
- 使用使用以前的映像分配进行快速回滚操作,将计算机目录快速回滚到以前分配的准备好的映像。只需从历史记录列表中选择一个版本,即可进行快速且明智的回滚。有关回滚的信息,请参阅使用不同的准备好的映像更新计算机目录。
此功能适用于 Azure 和 VMware 环境。
有关使用准备好的映像创建目录的信息,请参阅:
有关使用预准备映像更新目录的信息,请参阅管理预准备映像计算机目录。
预配成本洞察可视化
您现在可以查看计算机目录的详细成本信息。此可视化功能可提供过去 30 天的预配成本和趋势概览。
该报告根据各个目录细分预配成本,从而清晰了解每个类别对总成本的贡献。该报告:
- 显示过去 30 天内产生的总成本。
- 将当前 30 天的总成本与前一个 30 天的周期进行比较。
-
显示以下成本详细信息:
- 计算成本
- 存储成本
- 网络成本
- 其他成本
有关详细信息,请参阅查看目录详细信息。
针对不受信任的主机连接证书的重新信任选项
如果由于不受信任的证书导致主机连接中断,您可以在 Web Studio 中重新信任该主机连接的证书。有关详细信息,请参阅测试 TLS 证书信任。
节假日自定义计划
Autoscale 现在允许您创建自定义计划,以便在特定日期(例如节假日)关闭交付组中未使用的 VM,从而减少不必要的资源消耗。
要创建自定义计划:
- 在 Web Studio 中,转至交付组。右键单击交付组,然后选择管理 Autoscale。
- 在计划页面上,单击创建计划。
有关详细信息,请参阅使用 Studio 创建自定义节假日计划。
搜索节点中的计算机硬件视图
您现在可以在搜索节点中访问使用 Machine Creation Services (MCS) 预配的计算机的专用硬件视图。此视图可提供更好的计算机硬件详细信息可见性,并使 MCS 预配的计算机管理更加轻松。 主要优势包括:
- 查看详细的硬件配置,包括计算机大小、操作系统、许可证类型、安全设置、网络、映像和模板以及磁盘设置。
- 使用硬件筛选器和搜索选项轻松查找计算机。
目前,硬件视图适用于 VMware、XenServer、SCVMM/Hyper-V、Nutanix PC、Azure、Azure Arc、Azure Local、AWS EC2 和 GCP 中的 MCS 预配计算机。OpenShift 和 Amazon WorkSpaces Core 托管实例目前仅以列的形式显示基本硬件信息。有关详细信息,请参阅在搜索 > 硬件视图中监视 MCS 预配的计算机。
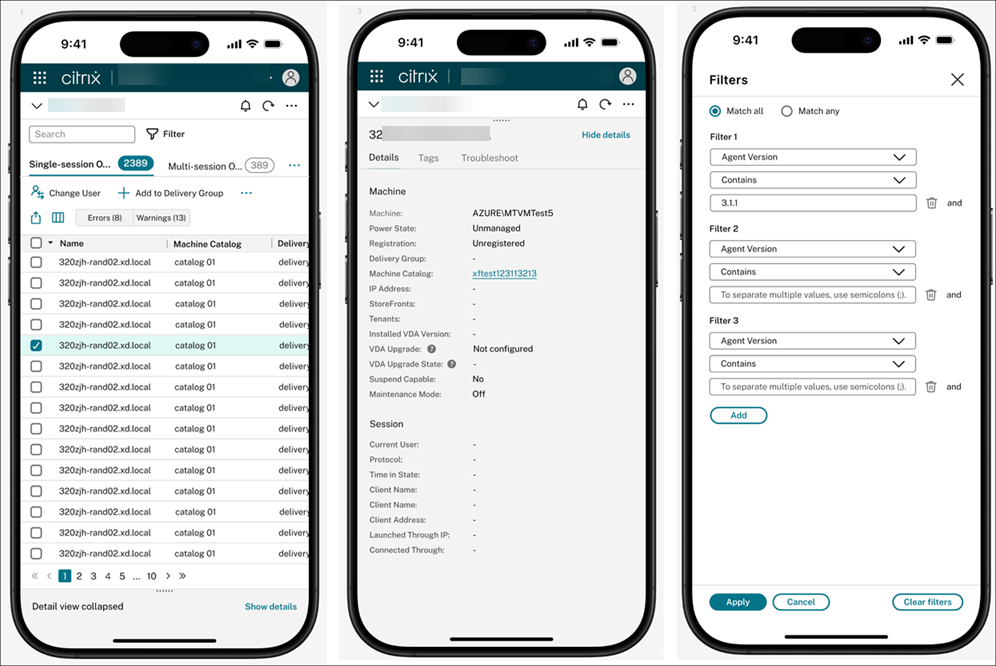
增强型移动体验,助力关键的移动任务
您现在可以更轻松地通过移动设备管理 Citrix Virtual Apps and Desktops 部署。更新后的体验针对小屏幕进行了优化,使得在没有桌面设备时,通过移动设备访问 Studio 变得更加容易。无论您是响应警报还是快速检查配置错误,都可以立即采取行动,无需等到回到办公桌前。
移动界面提供了改进的可访问性,并专为触控友好型交互而设计。布局和功能可能与桌面体验略有不同,以更好地适应移动工作流。
凭借响应式布局和简化的导航,您可以:
- 一目了然地监视部署运行状况
- 查看计算机目录和交付组的详细信息
- 执行关键操作,例如重新启动计算机或禁用交付组
在目录创建期间估算 Azure VM 成本
创建计算机目录时,您现在可以估算 Azure 虚拟机的每月成本,包括 VM 大小和磁盘成本。您还可以通过调整每日开机时间、工作日、节省计划、预留实例和关机存储等设置来优化估算。此功能可帮助您更高效地规划部署并及早优化成本。
有关详细信息,请参阅在“摘要”页面上查看每月估算详细信息。
用于配置运行状况检查的站点诊断测试
您现在可以从“主页”中的“站点详细信息”小组件运行站点诊断测试。此功能可帮助您快速评估 Citrix Virtual Apps and Desktops 环境的运行状况并识别常见的配置问题。无论您是排查性能问题还是准备升级,这些测试都能提供快速、可操作的见解。检测到的典型问题包括:
- Delivery Controller 通信失败
- 数据库连接或配置错误
此功能在升级期间特别有用,有助于确保您的站点在部署前后都稳定且就绪。有关详细信息,请参阅站点详细信息。
改进的重新启动 UI,可实现更清晰的控制和自定义
我们改进了重新启动计划 UI,使重新启动模式更清晰、更具可自定义性。您现在可以轻松区分正常重新启动和强制重新启动,并配置自定义重新启动持续时间以满足您的需求。 为了帮助您做出明智的选择,我们还添加了工具提示,解释了关键选项,例如强制重新启动如何强制重新启动计算机,即使会话无响应。
有关详细信息,请参阅创建重新启动计划。
新的登录页面设置
Web Studio 中的“设置”节点现在包含两个选项,可增强 Web Studio 登录体验:
- 登录页面通知:显示自定义消息以与管理员共享重要信息。
- 显示已连接的 Delivery Controller:显示已连接的 Delivery Controller 的 FQDN,以提高可见性和透明度。
有关详细信息,请参阅设置。
使用“我的首选项”设置自定义您的 Studio 视图
“设置”节点下现已提供新的“我的首选项”选项卡。此选项卡上的设置允许您根据自己的偏好调整 Studio 界面。这些设置仅适用于您的帐户,不会影响其他管理员。 您可以配置以下选项:
- 日期和时间:设置您的默认时区、日期格式和时间格式。这些设置在整个 Studio 中用于时间相关的显示,例如计划的重新启动和自动缩放。
- 文件夹视图:选择是在“计算机目录”、“交付组”和“应用程序”节点中显示还是隐藏文件夹视图。
- 搜索中的选项卡顺序:自定义“搜索”节点中的选项卡顺序。
有关详细信息,请参阅设置。
增强的 SQL Server 连接设置
您现在可以为 SQL Server 连接配置三个安全设置:“加密”、“信任服务器证书”和“证书中的主机名”。这些设置提供了更大的灵活性,并有助于根据生产环境的要求增强数据库连接的安全性。 我们已更新以下 UI 以支持此增强功能:
- Citrix Site Manager:允许您在创建站点或更改数据库设置时配置这些选项。
- Web Studio 中的“设置”页面:允许您在更改数据库设置时配置这些选项。
Web Studio 安装灵活性
您现在可以将 Web Studio 安装在 site ID = 1 的任何 IIS 网站上,无论站点名称如何。此增强功能允许您在自定义 IIS 站点下托管 Web Studio,而不是仅限于“默认网站”。
如果在运行安装程序时未安装 IIS,则会自动设置 IIS,并将 Web Studio 部署在“默认网站”下。如果已安装 IIS,您可以预先创建具有首选名称和路径的站点,只要其 site ID 为 1 即可。
有关详细信息,请参阅安装 Web Studio。
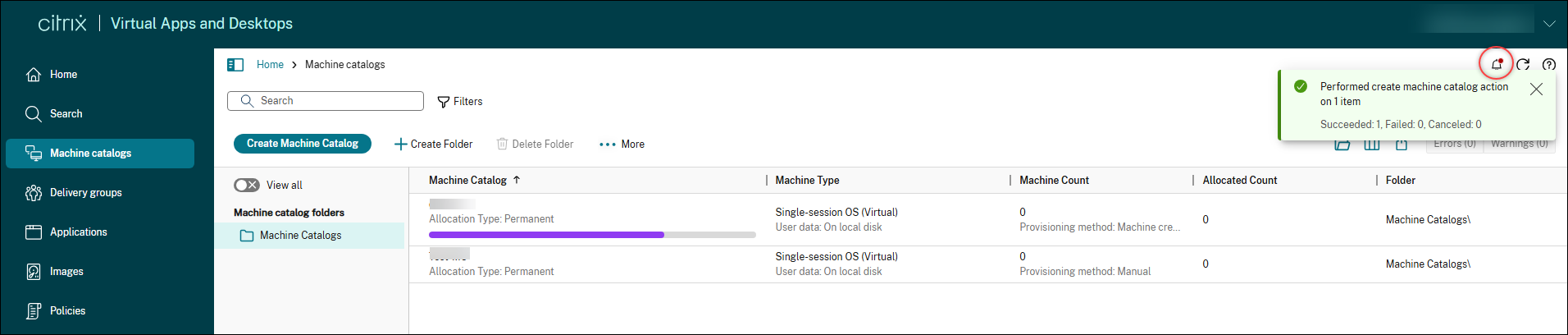
会话内通知和后台操作
Web Studio 现在包含一个通知中心,可让您实时查看后台操作并报告操作结果。当您启动耗时操作时,通知会显示在右上角,告知您操作正在进行中。以前会阻止 UI 的操作现在在后台运行,因此您可以继续工作而不会中断。操作完成后,会显示实时状态通知,结果也会保存在通知中心。通知中心会保留 48 小时历史记录,方便您跟踪近期活动。
Studio 始终在线模式
Web Studio 现已引入始终在线模式,以增强弹性并减少基础设施故障期间的停机时间。在此只读模式下,即使在服务中断期间,您也可以安全地查看和监控您的 Citrix Virtual Apps and Desktops 环境,从而有助于保持运营连续性。始终在线模式适用于所有 MANAGE 节点,Quick Deploy 除外。有关更多信息,请参阅此博客文章。
支持将 Citrix 组策略分配给 Microsoft Entra ID 用户
您现在可以在 Studio 中将 Citrix 组策略分配给来自多个身份提供程序 (IDP) 的 Microsoft Entra ID 用户。此增强功能使您在将策略应用于特定用户组时具有更大的灵活性,并简化了使用 Citrix Virtual Apps and Desktops 与 Windows 365 的部署。
跨平台自定义桌面图标
Web Studio 现在允许您自定义所选的任何桌面图标。以前,所有桌面都使用默认图标,并且您无法在 Studio 中更改它。您现在可以:
- 上传图标并将其用于桌面或应用程序
- 更改单个桌面的图标
- 从内置图标中选择您所选的桌面图标
支持对交付组中的访问策略进行更精细的控制
以前,您只能使用 PowerShell 或 REST API 将访问策略应用于特定用户。现在,您可以在 Studio 中直接实现此目标。此增强功能使您在为不同用户或用户组定义不同访问条件时具有更大的灵活性,从而实现更精细的访问控制。有关更多信息,请参阅配置访问策略的用户范围。
此外,我们还改进了 Studio 与 PowerShell 或 REST API 方法之间的兼容性。以前,如果您使用 PowerShell 或 REST API 配置了具有用户范围的访问策略,则 Studio 中的“用户”和“访问策略”页面会被阻止。Studio 现在完全支持这些场景,并在必要时提供清晰的信息或 UI 指导。
支持在交付组级别对应用程序进行访问控制
以前,在 Studio 中,您只能在单个应用程序级别(而非交付组级别)对应用程序进行访问控制。现在,您可以在交付组级别对应用程序执行访问控制。目前,此功能仅限于控制对交付组中所有应用程序的访问。
有关更多信息,请参阅限制特定用户对应用程序的访问。
增强的用户分配默认设置以提高安全性
我们更新了在交付组中分配用户时的默认行为。现在,受限控制是默认设置,可确保更好的安全性和更精细的访问控制。另一个选项“允许任何经过身份验证的用户使用资源”现在已明确标记为“不推荐”,并且只能用于特定场景,例如用于广泛访问的共享或池化桌面、自助服务终端环境或测试目的。此更改有助于降低风险,同时在需要时为您提供灵活性。
有关更多信息,请参阅配置访问策略的用户范围。
将始终在线跟踪 (AOT) 日志转发到您的日志服务器
借助 Web Studio,您现在可以将 Citrix 组件中的 AOT 日志转发到指定的日志服务器。此功能可实现集中式故障排除和对 Citrix 环境的高级监控。有关更多信息,请参阅设置。
改进的应用程序包管理
在 Web Studio 中,您现在可以选择在检查更新时自动删除源位置中不再存在的包。此“首选项”字段中的新“删除不存在的包”选项可帮助您通过从“包”选项卡中删除过时的条目来轻松清理应用程序包 UI。 此外,“应用程序包”节点中的几个选项卡和部分已重命名,以更好地与 Studio 现在支持的更广泛的包类型套件保持一致:
- “添加源”现已更名为“创建发现配置文件”
- “检查包更新”现已更名为“检查更新”
- “删除源”现已更名为“删除配置文件”
有关更多信息,请参阅管理应用程序包。
支持发现和分配 Elastic App 层
您现在可以使用 Web Studio 中的“应用程序包”节点发现和发布 Elastic App 层。借助此功能,您可以:
- 发现和枚举使用 Citrix App Layering 创作的 Elastic App 层库。
- 创建分配策略,以弹性方式将应用程序交付给非持久性计算机目录上的用户。
- 将可移植的 Elastic App 层交付到任何非持久性 Windows 计算机,无论映像是否从 App Layering 设备发布。
有关更多信息,请参阅Elastic App 应用程序。
支持发现和分配 Numecent Cloudpaging 应用程序
您现在可以使用 Web Studio 中的“应用程序包”节点发现和发布 Numecent Cloudpaging 应用程序。
有关详细信息,请参阅Cloudpaging 应用程序。
支持控制打包应用程序的可见性
借助 Web Studio,您现在可以控制打包应用程序的可见性,即在桌面上、在“Citrix Workspace > 应用程序”中或同时在这两者中。要更改特定打包应用程序的可见性,请转至“应用程序”节点,选择该应用程序,然后选择“属性 > 交付”。 默认情况下,打包应用程序仅在“Citrix Workspace > 应用程序”中交付。
有关详细信息,请参阅更改应用程序属性。
支持自动将 Azure 临时磁盘用于回写缓存磁盘
在 Studio 中编辑 MCS 预配的目录时,如果满足所需条件,该目录现在会自动将 Azure 临时磁盘用于回写缓存 (WBC) 磁盘。因此,添加到目录中的新 VM 将使用 Azure 临时磁盘作为 WBC 磁盘。 以前,如果目录在创建时不符合条件,则不会将 Azure 临时磁盘用于 WBC 磁盘,即使后来更新了目录以满足条件也是如此。 优势:
- 降低成本。VM 关闭电源时,临时磁盘不会产生存储成本。
- 提高灵活性。将临时磁盘用于 WBC,而无需重新创建目录。 当目录满足以下所有条件时,MCS 预配的目录会自动将 Azure 临时磁盘用于 WBC 磁盘:
- 已启用 MCSIO。
- WBC 磁盘是非持久性的。
- VM 大小包含一个足以用于 WBC 磁盘的临时磁盘。
- 未为 WBC 磁盘指定驱动器盘符。
有关详细信息,请参阅创建 Microsoft Azure 目录。
Citrix Director
计算机诊断见解
Citrix Director 中现已提供一个新的“计算机诊断见解”面板,可帮助您主动识别和解决会话故障和性能问题。此功能引入了每 15 分钟刷新一次的实时见解,突出显示整个站点中存在问题的计算机。
Director 与 Citrix Virtual Apps and Desktops 集中式日志服务器集成以实现 AOT
Director 与 Always On Tracing (AOT) 集成,作为一项基础诊断功能。这支持持续、低开销地捕获和分析关键 VDA 和会话事件。
主要功能包括:
- 查看 AOT 日志:访问各种 Citrix Virtual Apps and Desktops 组件的日志,例如 DDC、VDA 和 StoreFront。
- 筛选和搜索 AOT 日志:从特定时间段检索 AOT 日志,支持按“类别”、“日志类”和“主机名”进行搜索和筛选。
- 与 Director/Monitor 无缝集成:可轻松地从 Director/Monitor 中的“计算机筛选器”、“会话启动故障诊断”和“活动管理器”过渡到特定 VDA 或会话的精细 AOT 日志数据。
支持使用“IN”运算符多选关键实体
此增强功能引入了为关键筛选字段(例如用户、计算机和交付组)选择多个值的功能,利用“IN”运算符。
支持多选交付组
“趋势”选项卡下“会话”和“登录性能”页面中的交付组下拉列表已增强,具有以下功能:
- 使用文本输入搜索交付组名称
- 最多可多选 15 个交付组以进行全面分析
此增强功能提高了可用性,并支持同时跨多个交付组进行更高效的监视和比较。
增强的工作负载大小调整
增强的工作负载大小调整页面可帮助您分析交付组的使用情况和大小调整方面。因此,可以根据计算机或用户活动分析交付组。 基于计算机的分析使您能够: 根据使用情况对虚拟桌面进行分类,以识别没有活动或活动量低的计算机,并减少在未使用资源上的开支。 分析虚拟桌面上的资源利用率,以识别需要调整大小的计算机,从而降低成本或改善用户体验。
基于用户的分析使您能够:
- 根据用户的活动对其进行分类。出于 IT 卫生原因,请考虑删除没有活动的用户访问权限。使用量低的用户可以移动到共享资源以更有效地利用资源。
- 分析用户的资源消耗,以识别资源消耗高于或低于平均水平的用户群,从而更有效地分配用户。
此分析非常适用于将虚拟桌面静态分配给用户的场景,例如 Windows 365 Enterprise 或 Frontline dedicated。您还可以分析具有随机分配的虚拟桌面或多会话计算机的交付组,但由于用户在这些计算机之间漫游,因此分析会显示平均值。
注意:
通过页面顶部的“所有工作负载”按钮访问的经典调整大小分析将在即将发布的版本中弃用。
改进了垂直和水平负载平衡警报的处理
以前,当您将 UseVerticalScalingForRdsLaunches 设置为 true 并在 Studio 中配置“最大会话数”策略时,计算机将进入“最大容量”状态。无论限制是由于垂直还是水平负载平衡而达到,Director 都会触发“最大容量”警报。在遇到特定错误(例如“达到最大负载”)时,无法区分垂直和水平负载平衡。这导致垂直扩展场景中的预期行为出现不必要的警报,浪费您的时间并造成混淆。
现在,当垂直负载平衡处于活动状态且计算机达到其会话限制时,它将进入新状态:“垂直扩展的最大容量”。Director 不再为此新状态生成警报。警报仅在水平扩展场景中针对“最大容量”触发。您可以在“筛选器”和“自定义报告”页面中查看新状态,从而更轻松地区分预期条件和异常条件。此增强功能可帮助您避免不必要的警报并专注于实际问题,从而简化监视和故障排除。当您使用 Set-BrokerSite 配置 UseVerticalScalingForRdsLaunches 并在 Studio 中设置“最大会话数”策略时,此功能适用。
成功会话启动的地图视图
Citrix Director 中的地图视图为管理员提供了其 Citrix 环境中成功会话启动的全面地理可视化。此功能在全球范围内直观地映射用户连接,帮助 IT 团队快速识别区域性能模式、解决地理连接问题,并根据位置数据优化最终用户体验。该地图显示了颜色编码的连接点,指示不同地理位置的登录性能。
将 Microsoft Teams 优化 (Slimcore) 详细信息扩展到适用于 Mac 的 Citrix Workspace 应用程序
我们正在将 Microsoft Teams Slimcore 优化的可见性扩展到运行 Citrix Workspace 应用程序 (CWA) 2508 及更高版本的 Mac 端点。以前仅限于 Windows 端点,现在使用 Director 的管理员可以为其 Mac 用户查看并利用此优化,从而确保整个环境中的性能洞察保持一致。
注意:
CWA Mac 版本必须至少为 2508。
会话失败洞察
以前,您在理解会话失败原因方面面临挑战。您缺乏关于用户会话为何失败的详细诊断洞察。现在,借助此功能,您可以获得全面的会话失败诊断洞察。您可以检测错误模式并快速识别主要失败原因。系统会突出显示影响特定交付组或计算机的失败。您还可以了解被阻止的用户连接。这提高了您更快地解决会话问题的能力。此增强功能适用于您的 Monitor 和 Director 服务。
会话拓扑现在可用于已断开连接和已结束的会话
Citrix Director 中的会话拓扑视图现在支持已断开连接和已结束的会话,显示上次已知状态的拓扑,以便进行全面的会话后分析。
成本节约中增加了延长的时间段和自定义日期范围
您现在可以查看采用电源管理的计算机的 90 天成本节约数据,高于以前的 45 天限制。我们还添加了一个自定义日期选择器,使管理员能够更好地控制和灵活地在特定、延长的时间范围内扫描和分析节约情况。
查看因会话启动失败而被阻止的用户
管理员现在可以了解因会话启动失败而被阻止的用户。此新摘要可在“连接”视图下的“筛选器”中找到,从而改进了故障的优先级排序和分析。
了解跨用户的会话重新连接持续时间
Citrix Director 中的会话重新连接持续时间功能扩展了现有会话登录持续时间功能,以包含与会话重新连接相关的指标。此增强功能使管理员能够了解重新连接性能趋势,从而更好地解决问题和优化用户体验。
能够查看跨用户会话的统一通信应用程序指标
“会话”视图现在包含几个新的显示列,可提供有关用户会话的统一通信 (UC) 应用程序使用情况的详细洞察。这些列是:所有 UC 应用程序名称、UC 应用程序名称、UC 应用程序优化状态、UC 应用程序插件管理器名称、UC 应用程序插件管理器版本、UC 应用程序插件已安装、UC 应用程序插件版本、UC 应用程序版本、UC 应用程序插件管理器、UC 应用程序虚拟通道状态和UC 应用程序虚拟通道允许列表。可以通过“选择列”选项选择这些属性以在主会话表视图中显示。有关详细信息,请参阅统一通信应用程序指标
增强了“趋势”中的交付组选择
“趋势”选项卡下的“会话”和“登录性能”页面中的“交付组”下拉列表已得到增强。您现在可以:
- 使用文本输入搜索交付组名称
- 最多选择 15 个交付组进行全面分析
此增强功能提高了可用性,并允许同时跨多个交付组进行更高效的监视和比较。
适用于单会话操作系统的 HDX 屏幕共享远程协助
Director 现已支持利用原生 HDX 屏幕共享技术提供远程协助。此功能为 IT 管理员和技术支持团队提供了一种安全、高性能的方法,可在单会话环境中为最终用户提供远程支持,从而补充或替代现有远程协助方法。
Machine Creation Services™ (MCS)
支持在 Amazon Workspaces Core Managed Instances 中创建 MCS 计算机目录
MCS 现已与 Amazon Workspaces Core Managed Instances 集成,可在客户的 AWS 账户中预配持久和非持久 MCS 计算机目录。
借助此功能:
- 您可以创建到 Amazon WorkSpaces Core Managed Instances 的主机连接。
- 创建准备好的映像,并使用准备好的映像和计算机配置文件创建持久或非持久 MCS 计算机目录。
- 在相同或不同的 AWS 区域内跨不同的可用区共享单个准备好的映像。当前,您只能使用 PowerShell 命令在不同的 AWS 区域之间共享准备好的映像。
MCS 中对 VMware vVols 的支持
您现在可以在 vSphere 环境中使用 VMware vVols 和 MCS。以前,在 vVols 上创建 MCS 目录会导致 PBM 错误。此更新解决了该问题。此集成提供了对 MCS 虚拟机存储的精细控制。有关信息,请参阅 存储配置文件 (vSAN)。
支持使用 AWS EC2 Spot 实例
借助此功能,您可以使用计算机配置文件工作流在 AWS 虚拟化环境中创建 Spot 实例的 MCS 计算机目录(仅限持久请求)。
与按需实例相比,Spot 实例可节省高达 90% 的成本。但是,如果容量不可用,Amazon EC2 可能会中断 Spot 实例,这使得它们仅适用于非关键应用程序和桌面。
此外,借助此功能,您可以将 Spot 实例用作备份 SKU。
有关详细信息,请参阅 使用 AWS Spot 实例创建目录。
支持跨所有本地管理程序进行 Azure Arc 载入
Azure Arc 使组织能够管理托管在任何位置的资源(例如虚拟机),就像它们在 Azure 中运行一样。借助 Azure Arc,您可以使用 Azure Monitor 等 Azure 服务,对资源进行全面的可见性和主动管理。
借助此功能,您现在可以使用 PowerShell 命令为 MCS 计算机目录启用 Azure Arc 载入。载入后,可以从 Azure 门户管理虚拟机,以执行电源管理、添加或删除扩展、分配策略以及通过内置 Azure 策略在已启用 Arc 的虚拟机上启用 Azure Monitor 等操作。
当前,此功能适用于所有 Citrix 本地管理程序 VMware、Nutanix 和 SCVMM。
有关详细信息,请参阅 将虚拟机载入 Azure Arc。
支持在 Azure 上预配数据磁盘
您现在可以创建并将持久数据磁盘分配给 Azure 中 MCS 计算机目录的 MCS 创建的持久或非持久虚拟机。数据磁盘用于存储事件日志、安全跟踪和应用程序数据等持久数据。
数据磁盘必须从主映像预配。如果自定义属性中未指定存储类型、加密设置、区域等属性,则这些属性将从自定义属性或操作系统磁盘模板派生。有关使用数据磁盘创建 MCS 计算机目录的信息,请参阅 预配数据磁盘。
MCS 维护唯一的计算机 GUID
在 VDA 版本 2511 或更高版本上,MCS 预配的 Windows 虚拟机现在保留一个唯一的 MachineGuid,该 GUID 在重新启动和映像更新后保持一致。此增强功能解决了多个虚拟机共享相同 MachineGuid 导致许可和应用程序注册受到影响的问题。
将 WinHttp (netsh) 代理服务器设置用于主机连接
此功能允许主机连接使用在 DDC 上配置的 WinHttp (netsh) 代理服务器设置。有关详细信息,请参阅 将 WinHttp (netsh) 代理服务器设置用于主机连接。
Azure:支持休眠虚拟机的跨系列备份虚拟机大小
Azure 上的 MCS 现在支持在启用休眠的计算机目录中使用跨系列虚拟机大小进行备份配置,从而提高了弹性。此功能消除了以前阻止跨系列回退以防止在恢复时出现蓝屏错误的限制。当恢复休眠虚拟机时发生分配失败时,MCS 会自动处理大小更改,确保您仍然获得一个可工作的虚拟机。请注意,切换虚拟机大小需要清除休眠状态,这将导致虚拟机内存状态(RAM 数据)的丢失。此功能适用于持久和非持久 MCS 目录。有关详细信息,请参阅 配置备份虚拟机大小。
Azure:克隆 MCS 目录
您现在可以使用 Copy-ProvScheme PowerShell 命令在 Azure 虚拟化环境中克隆现有的持久性和非持久性 MCS 计算机目录。此功能通过复制现有方案的详细信息(包括关联的配置、网络映射和安全组)来创建新的预配方案。这有助于您:
- 将现有单个目录拆分为多个目录,以应用不同的目录级策略和配置。
- 在大规模目录中隔离特定的虚拟机,以便进行快速测试或根据功能角色对其进行单独处理。
有关详细信息,请参阅克隆 MCS 目录。
Autoscale™
智能 Autoscale
智能 Autoscale 是一项数据驱动的 Autoscale 功能,具有最少的管理设置,可让您配置交付组的性能目标。性能目标值范围为 1 到 99,该值指定了用户体验和成本之间的目标平衡:
- 低值优先考虑节省成本。
- 高值优先考虑用户体验。
性能目标与历史使用数据相结合,可计算一天中每个 30 分钟块的最佳缓冲区容量(要开机的 VM 数量)。因此,每天开始时会计算 48 个最佳缓冲区容量。
最佳缓冲区容量取代了高峰/非高峰缓冲区容量和池大小来管理可用计算机。
有关详细信息,请参阅智能 Autoscale 计划插件。
Autoscale 节假日插件
借助此功能,您可以偏离与 VM 电源管理相关的标准 Autoscale 设置,并允许在指定的节假日关闭 VM。例如,对于工作日,您希望大多数 VM 处于开机状态,而默认情况下,在银行假日,则应用工作日计划。要管理此类情况,请使用 Autoscale 节假日插件在指定的节假日关闭 VM。有关详细信息,请参阅Autoscale 节假日插件。
识别计算机排空状态和原因
Get-BrokerMachineV2 PowerShell cmdlet 现在提供两个新属性:IsDraining 确认计算机是否正在排空,DrainingReason 指定确切的原因。这有助于您有效地排查和管理计算机可用性。来宾操作系统排空原因仅适用于多会话计算机。
示例:您注意到多会话计算机 VDA-01 不接受新的用户会话。您怀疑它处于排空状态。运行 Get-BrokerMachineV2 -MachineName "VDA-01" | Select-Object Name, IsDraining, DrainingReason。输出显示 IsDraining 为 True,DrainingReason 为 AutoscaleScaleDown。这确认 Autoscale 启动了排空状态以进行关机。您可以快速了解计算机的状态。
有关详细信息,请参阅排空状态。
从 Autoscale 计算中排除正在排空的计算机
您现在可以从 Autoscale 容量计算中排除因重新启动计划而正在排空的计算机。这可以防止过度预配,帮助您优化资源使用。要激活此行为,请在多会话交付组上将 ExcludeNaturalRebootDrainingFromAutoscale 属性设置为 True。
此功能仅适用于:
- 多会话操作系统交付组。
- 为云配置了正常重新启动或为本地部署配置了排空会话后重新启动所有计算机的重新启动计划。
例如,考虑一个具有 10 个活动会话的交付组。两台计算机因计划重新启动而正在排空。以前,Autoscale 可能会将这两台正在排空的计算机计为可用,这可能导致过度预配新计算机。借助此功能,Autoscale 会识别并忽略正在排空的计算机。它只计算真正可用的容量。这可确保您的 Autoscale 策略准确预配资源,从而避免不必要的基础设施成本。
有关详细信息,请参阅从 Autoscale 计算中排除正在排空的计算机
Citrix Virtual Desktop Assistant 应用程序
增强型 Citrix Virtual Desktop Assistant 应用程序
Citrix Virtual Desktop Assistant 应用程序现已增强,具有以下新功能:
- 工作站 VDA:该应用程序现在默认安装。它会监控 CPU 和内存使用情况,除非明确启动,以确保最小的资源使用。
- 服务器 VDA:该应用程序在 Citrix Virtual Apps and Desktops ISO 中提供,方便安装。
- 优化磁贴:重新设计以清晰显示内存回收详细信息,从而提供更好的资源洞察。
- 键盘页面:查看和管理键盘设置和同步状态。
- USB 页面:监控实时 USB 设备重定向状态。
有关详细信息,请参阅 Citrix Virtual Desktop Assistant 应用程序。
应用程序保护
应用程序保护对策略篡改检测的支持
从 Citrix Virtual Apps and Desktops 2511 版本开始,默认启用策略篡改检测功能。有关详细信息,请参阅 策略篡改检测。
注意:
从 Citrix Virtual Apps and Desktops 2511 版本开始,如果使用
Default.ica文件启用应用程序保护,会话启动将失败。请改为使用 Web Studio 或 PowerShell 在 Delivery Controller 中对交付组启用策略。请参阅 配置防键盘记录和防屏幕截图。
预览功能
适用于 NVIDIA 客户端 GPU 的 HDX 图形超分辨率
HDX 图形超分辨率现在还支持来自 NVIDIA 的兼容客户端 GPU。
使用合并组启用 Canary 部署
您现在可以使用合并组为您的应用程序和桌面资源实施 Canary 部署模型。此功能允许您发布同一资源的多个版本,同时将其作为单个图标呈现给最终用户。
合并组允许您将特定用户组定向到同一资源的不同实施版本。您可以指定一定比例的用户(例如 5%)来测试新版本,同时让其他用户保留在稳定版本上。如果新版本出现问题,您可以轻松地将用户故障转移到稳定版本,而不会中断他们的体验。此功能支持高可用性和灾难恢复方案,无需重新枚举或更改配置。
有关详细信息,请参阅 使用合并组启用 Canary 部署。
Profile Management
有关新功能的信息,请参阅其文档中的 新增功能 文章。
Linux VDA
有关新功能的信息,请参阅其文档中的 新增功能 文章。
Session Recording
有关新功能的信息,请参阅其文档中的 新增功能 文章。
Citrix Provisioning™
有关新功能的信息,请参阅其文档中的 新增功能 文章。
适用于 macOS 的 Citrix Virtual Delivery Agent
有关新功能的信息,请参阅其文档中的 新增功能 文章。
Workspace Environment Management™
有关新功能的信息,请参阅其文档中的 新增功能 文章。
Federated Authentication Service
有关新功能的信息,请参阅其文档中的 新增功能 文章。
在本文中
- 关于本版本
- Delivery Controller
- HDX
- Virtual Delivery Agents (VDA)
- Citrix 始终在线跟踪
- Web Studio
- Citrix Director
- Machine Creation Services™ (MCS)
- Autoscale™
- Citrix Virtual Desktop Assistant 应用程序
- 应用程序保护
- 预览功能
- Profile Management
- Linux VDA
- Session Recording
- Citrix Provisioning™
- 适用于 macOS 的 Citrix Virtual Delivery Agent
- Workspace Environment Management™
- Federated Authentication Service