This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
System Log
The system log displays a timestamped list of events that occurred in Citrix Cloud. This includes configuration changes along with other events such as connector upgrades. You can export these changes as a CSV file to meet your organization’s regulatory compliance requirements or to support security analysis.
Note:
DaaS Studio writes logs to a separate log. For more information, see Configuration Logging.
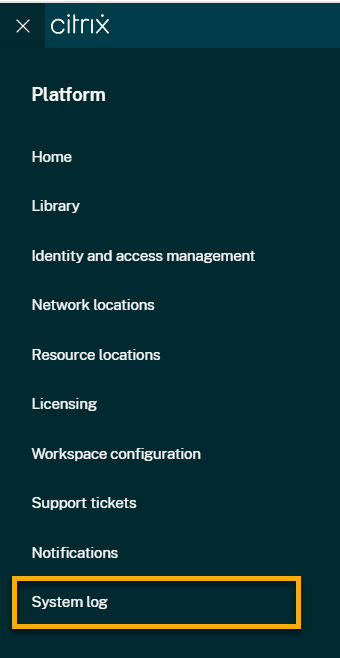
To view the system log, select System Log from the Citrix Cloud menu.
For more information about retention of data in system logs, see Data retention in this article.
Logged events
The system log captures events for certain Citrix Cloud platform and cloud service operations. For a complete list of these events and descriptions of captured data, see System Log Events Reference.
By default, the system log displays events that occurred in the last 30 days. The most recent events are displayed first.
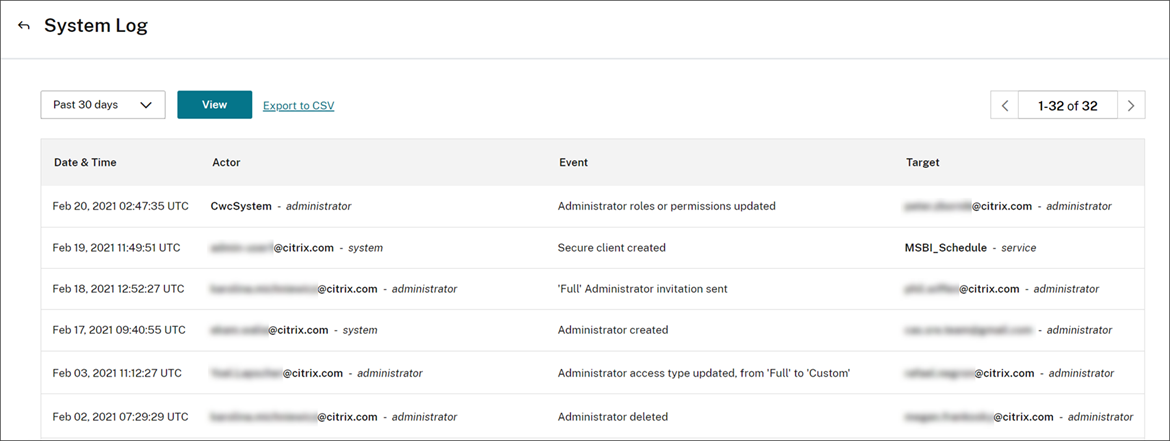
The displayed list includes the following information:
- Date and time (UTC) when the event occurred.
- Actor that initiated the event, such as an administrator, secure client, or service principal. Entries with the actor CwcSystem indicate that Citrix Cloud performed the operation.
- Brief description of the event, such as editing an administrator or creating a new secure client or service principal.
- Target of the event. The target is the system object that was impacted or changed as a result of the event. For example, a user who was added as an administrator.
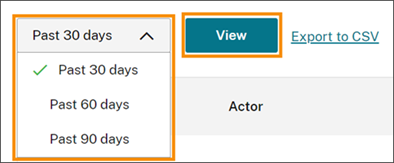
To view events more than 30 days in the past, filter the list by selecting the time period you want to view and select View. You can view events that occurred up to 90 days in the past.
To retrieve older events that occurred during a time period that you specify, you can use the SystemLog API. For more information, see Retrieve events for a specific time period in this article.
Export events
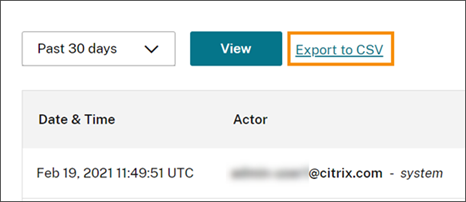
You can export a CSV file of system log events that occurred up to the last 90 days. The name of the downloaded file follows the format of SystemLog-CustomerName-OrgID-DateTimeStamp.csv.
- From the Citrix Cloud menu, select System Log.
- If needed, filter the list to display the time period for which you want to export events.
- Select Export to CSV and save the file.
The CSV file includes the following information:
- UTC timestamp of each event
- Details of the actor who initiated the event, including the name and actor ID.
- Event details such as the type of event and the text of the event
- Details of the target of the event such as the target ID, the name of the administrator and a secure client or service principal.
Retrieve events for a specific time period
If you need to retrieve events for specific periods of time, use the SystemLog API.
SystemLog API
you can use the SystemLog API to read log entires and export them to another system. Before you use the API, you’ll need to create a service principal or secure client as described in Getting Started on the Citrix Developer Docs web site.
For more information about using the SystemLog API, see Citrix Cloud - SystemLog on the Citrix Developer Docs web site.
For Citrix DaaS logs, see How to get configuration operations in Citrix DaaS.
Data retention
Citrix shares responsibility with you, the customer, for retaining the system log data that Citrix Cloud captures.
Citrix® retains system log records for 90 days after events are recorded.
You are responsible for downloading the system log records that you want to retain to meet your organization’s compliance requirements and for storing these records in a long-term storage solution.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.