This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Cloud Connector Proxy and Firewall Configuration
The Cloud Connector supports connection to the Internet through an unauthenticated web proxy server. Both the installer and the services it installs need connections to Citrix Cloud. Internet access needs to be available at both of these points.
Connectivity requirements
Use port 443 for HTTP traffic, egress only. For a list of required contactable addresses, see the following resources:
The required contactable addresses for Citrix Cloud are specified as domain names, not IP addresses. Because IP addresses might change, allowing domain names ensures that the connection to Citrix Cloud remains stable.
For a list of required ports, see Inbound and outbound ports configuration.
Important:
- Enabling SSL interception on certain proxies might prevent the Cloud Connector from connecting successfully to Citrix Cloud.
- SSL interception cannot be performed on Citrix Gateway addresses. For more information, see Citrix Gateway Services connectivity requirements.
- SSL interception must not impact the network connectivity or stability. For more information, see Citrix Cloud Connector
- If you are using a proxy, it is the following traffic flows must bypass the proxy:
- Communication between Connectors (for example, during LHC events).
- Communication between Connectors and VDA (WCF connection).
- Communication between Connectors and Domain Controllers (AD requests).
Furthermore, it is important to note that the connector utilizes the WinHTTP proxy settings. For configuration settings, see CTX222727.
Check Cloud Connector connectivity
The Cloud Connector Advanced Connectivity Check Tool can help verify connectivity between the Cloud Connector and Citrix Cloud using a series of connectivity checks.
For more information, see Cloud Connector Advanced Connectivity Check Tool.
Installer
The installer uses the settings configured for Internet connections. If you can browse the Internet from the machine then the installer should also function.
Services at Runtime
The runtime service operates in the context of a local service. It does not use the settings defined for the user (as described above).
You can configure the proxy settings during the installation process.
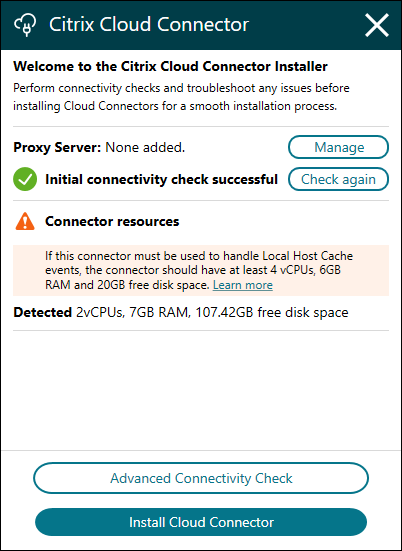
After the installer starts, before logging into Citrix Cloud, click Configure Proxy. You are prompted to add the proxy information and addresses to bypass the proxy. Both fully qualified domain names (FQDNs) and wildcard addresses are supported when specifying bypass addresses.
Note:
If you are using a proxy server, you must use manual proxy setup. Automatic proxy setup, through either automatic detection or PAC/setup scripts is not supported.
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.