Prerequisites
Using SAML authentication with Citrix Cloud has the following requirements:
- SAML provider that supports SAML 2.0.
- On-premises AD domain.
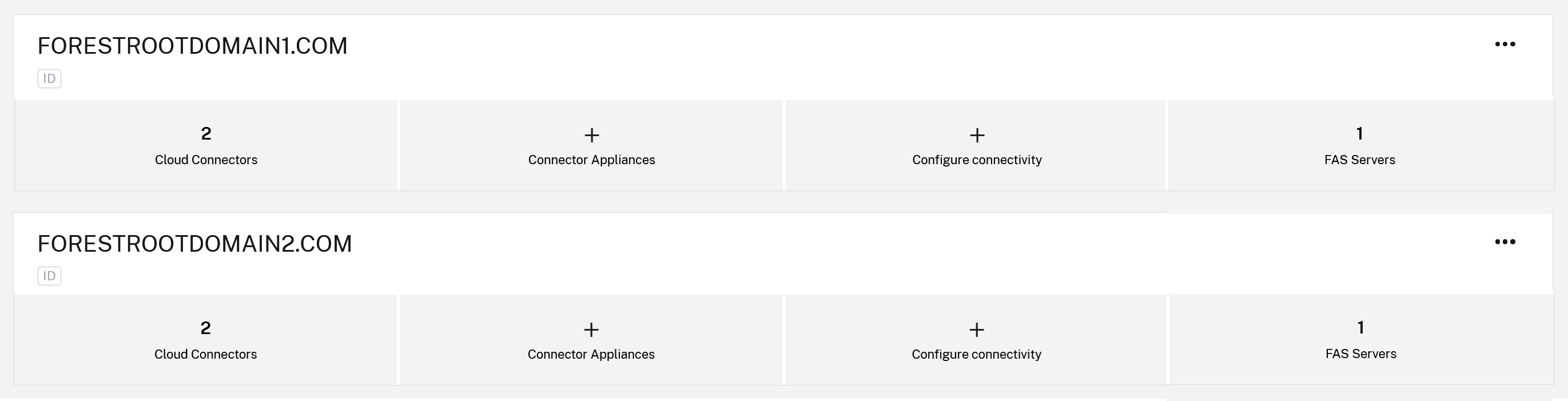
- Two Cloud Connectors deployed to a resource location and joined to your on-premises AD domain. The Cloud Connectors are used to ensure Citrix Cloud can communicate with your resource location.
- AD integration with your SAML provider.
Cloud Connectors
You need at least two (2) servers on which to install the Citrix Cloud Connector™ software. Citrix recommends at least two servers for Cloud Connector high availability. These servers must meet the following requirements:
- Meets the system requirements described in Cloud Connector Technical Details.
- Does not have any other Citrix® components installed, is not an AD domain controller, and is not a machine critical to your resource location infrastructure.
-
Joined to the AD domain where your AD users and resources reside. If users access resources in multiple domains, you need to install at least two Cloud Connectors in each domain.
- Connected to a network that can contact the resources that subscribers access through Citrix Workspace.
- Connected to the Internet. For more information, see System and Connectivity Requirements.
For more information about installing the Cloud Connector, see Cloud Connector Installation.
Active Directory (Default AD Identities SAML Flow)
-
Verify that your workspace subscribers have user accounts in your AD. Subscribers without AD accounts can’t sign in to their workspaces successfully when SAML authentication is configured.
-
Connect your AD to your Citrix Cloud account by deploying Cloud Connectors in your on-premises AD.
-
Synchronize your AD users to the SAML provider. Citrix Cloud requires the AD user attributes for your workspace subscribers so they can sign in successfully.
-
Only Universal AD groups should be used.
-
You MUST define any UPN suffixes inside Active Directory that your SAML users are configured to use. Citrix Cloud connectors cannot use undefined or ambiguous UPN suffixes to determine Active Directory domain context.
-
An EntraID OIDC IdP connection is NOT required for the default SAML flow as this uses AD identities.
EntraID Directory (EntraID Identities SAML Flow)
- EntraID B2B and external user support require AD shadow accounts with UPNs that match the FrontEnd users inside EntraID.
-
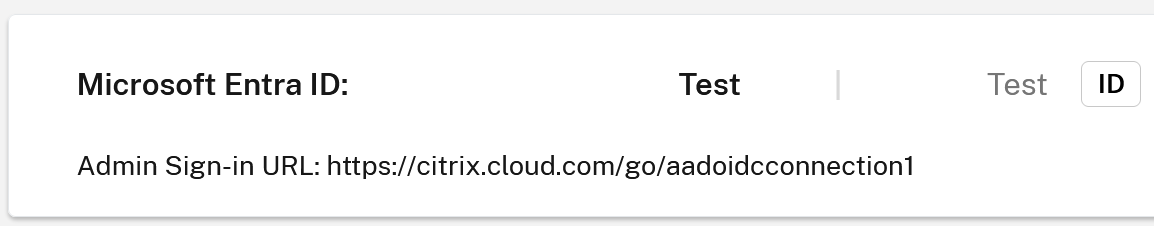
If using the SAML using Entra ID identities SAML flow as documented in SAML with Entra ID identities then you must also connect the correct EntraID tenant inside identity and Access Management > Authentication.
AD user attributes
The following attributes are required for all Active Directory user objects and must be populated:
- Common name
- SAM account name
- User Principal Name (UPN)
- Object GUID
- SID
Citrix Cloud uses the Object GUID and SID attributes from your AD to establish the user context when subscribers sign in to Citrix Workspace. If either of these properties isn’t populated, subscribers can’t sign in.
The following attributes aren’t required for using SAML authentication with Citrix Cloud, but Citrix recommends populating them to ensure the best user experience:
- Email address
- Display Name
Citrix Cloud uses the Display Name attribute to show subscribers’ names correctly in Citrix Workspace. If this attribute isn’t populated, subscribers can still sign in, but their names might not be displayed as expected.
SAML integration with Active Directory
Before enabling SAML authentication, you must integrate your on-premises AD with your SAML provider. This integration allows the SAML provider to pass the following required AD user attributes to Citrix Cloud in the SAML assertion:
- objectSID (SID)
- objectGUID (OID)
- userPrincipalName (UPN)
- Mail (email)
- Display Name (displayName)
You can configure a subset of these attributes, provided either the SID or UPN attributes are included in the SAML assertion. Citrix Cloud retrieves the other attributes from your AD as needed.
Note:
To ensure the best performance, Citrix recommends configuring all of the attributes mentioned in this section.
Although the precise integration steps vary among SAML providers, the integration process typically includes the following tasks:
- Install a synchronization agent in your AD domain to establish a connection between your domain and your SAML provider. If you’re using ADFS as your SAML provider, this step isn’t required.
- Create custom attributes and map them to the required AD user attributes mentioned earlier in this section. For reference, the general steps for this task are described in Create and map custom SAML attributes in this article.
- Synchronize your AD users to your SAML provider.
For more information about integrating your AD with your SAML provider, consult your SAML provider’s product documentation.