전자 메일 전략
조직에서 모빌리티 관리 이니셔티브를 시행하는 주된 이유는 모바일 장치에서 전자 메일에 안전하게 액세스할 수 있도록 하기 위해서입니다. XenMobile 설계의 주요 구성 요소 중 하나는 올바른 전자 메일 전략을 결정하는 것입니다. XenMobile은 보안, 사용자 환경 및 통합 요구 사항에 따라 다양한 사용 사례를 수용하는 다수의 옵션을 제공합니다. 이 문서에서는 클라이언트 선택부터 메일 트래픽 흐름에 이르는 올바른 솔루션을 선택하기 위한 일반적인 설계 의사 결정 프로세스와 고려 사항에 대해 다룹니다.
전자 메일 클라이언트 선택
전체 전자 메일 전략을 설계할 때는 일반적으로 클라이언트를 가장 먼저 선택합니다. Citrix Secure Mail, 특정 모바일 플랫폼 운영 체제에 포함되는 기본 메일 또는 공용 앱 스토어를 통해 제공되는 타사 클라이언트를 포함하는 여러 클라이언트 중에서 선택할 수 있습니다. 요구 사항에 따라 단일(표준) 클라이언트를 사용하여 사용자 커뮤니티를 지원하거나 클라이언트 조합을 사용해야 할 수 있습니다.
다음 표에는 사용 가능한 여러 클라이언트 옵션에 대한 몇 가지 간략한 설계 고려 사항이 나와 있습니다.
| 항목 | Secure Mail | 기본(예: iOS Mail) | 타사 메일 |
| 최소 XenMobile 버전 | 고급 | MDM | MDM |
| 구성 | MDX 정책을 통해 구성된 Exchange 계정 프로필. | MDM 정책을 통해 구성된 Exchange 계정 프로필. Android 지원은 SAFE/KNOX 및 Android Enterprise로 제한됩니다. 다른 모든 클라이언트는 타사 클라이언트로 간주됩니다. | 일반적으로 사용자가 수동으로 구성해야 합니다. |
| 보안 | 설계 시부터 보안이 적용되어 가장 높은 수준의 보안을 제공합니다. 데이터 암호화 수준이 추가된 MDX 정책을 사용합니다. Secure Mail은 MDX 정책을 통해 완벽하게 관리되는 앱입니다. Citrix PIN을 사용하여 인증 계층을 추가합니다. | 공급업체/앱 기능 집합에 따릅니다. 더 높은 수준의 보안을 제공합니다. 장치 암호화 설정을 사용합니다(MDX 정책을 통한 보안 없음). 앱 액세스에 대해 장치 수준 인증을 사용합니다. | 공급업체/앱 기능 집합에 따릅니다. 높은 수준의 보안을 제공합니다. |
| 통합 | 기본적으로 관리되는 앱(MDX)과의 상호 작용을 허용합니다. Citrix Secure Web을 사용하여 웹 URL을 엽니다. 파일 저장 및 첨부 시 Citrix Files를 사용합니다. GoToMeeting에 직접 참여하고 전화 접속합니다. | 기본적으로 관리되지 않는 다른 앱(비 MDX)과의 상호 작용만 가능합니다. | 기본적으로 관리되지 않는 다른 앱(비 MDX)과의 상호 작용만 가능합니다. |
| 배포/라이센스 | 공용 앱 스토어에서 MDM을 통해 직접 Secure Mail을 푸시할 수 있습니다. XenMobile Advanced 및 Enterprise 라이센스에 포함됩니다. | 플랫폼 운영 체제에 포함된 클라이언트 앱입니다. 추가 라이센스 요구 사항이 없습니다. | MDM을 통해 엔터프라이즈 앱으로 푸시하거나 공용 앱 스토어에서 직접 푸시할 수 있습니다. 앱 공급업체에 따라 연결된 라이센스 모델/비용이 적용됩니다. |
| 지원 | 클라이언트 및 EMM 솔루션을 단일 공급업체(Citrix)가 지원합니다. Secure Hub/앱 디버그 로깅 기능에 지원 연락처가 포함되어 있습니다. 하나의 클라이언트만 지원하면 됩니다. | 공급업체(Apple/Google)가 정의한 지원을 사용할 수 있습니다. 장치 플랫폼에 따라 여러 클라이언트를 지원해야 할 수 있습니다. | 공급업체가 정의한 지원을 사용할 수 있습니다. 모든 관리되는 장치 플랫폼에서 타사 클라이언트가 지원된다고 가정하면 하나의 클라이언트만 지원하면 됩니다. |
메일 트래픽 흐름 및 필터링 고려 사항
이 섹션에서는 XenMobile의 컨텍스트에서 메일(ActiveSync) 트래픽의 흐름과 관련된 세 가지 주요 시나리오 및 설계 고려 사항에 대해 설명합니다.
시나리오 1: 공개된 Exchange
일반적으로 Exchange ActiveSync 서비스를 인터넷에 공개하는 외부 클라이언트를 지원하는 환경입니다. 모바일 ActiveSync 클라이언트는 이 외부 대상 경로를 통해 역방향 프록시(예: Citrix ADC) 또는 에지 서버를 사용하여 연결합니다. 이 옵션은 기본 또는 타사 메일 클라이언트를 사용하려는 경우 필요하며 이 시나리오에서 이러한 클라이언트가 주로 사용될 수 있도록 합니다. 일반적인 사례는 아니지만 이 시나리오에서 Secure Mail 클라이언트를 사용할 수도 있습니다. 이 경우 앱의 MDX 정책 및 관리를 통해 제공되는 보안 기능을 활용할 수 있습니다.
시나리오 2: Citrix ADC를 통해 터널링됨(Micro VPN 및 STA)
Secure Mail 클라이언트를 사용하는 경우 Micro VPN 기능을 사용하려면 이 시나리오가 기본적으로 적용됩니다. 이 경우 Secure Mail 클라이언트는 Citrix Gateway를 통해 ActiveSync에 대한 보안 연결을 설정합니다. 기본적으로, Secure Mail은 내부 네트워크에서 ActiveSync에 직접 연결하는 클라이언트로 간주될 수 있습니다. Citrix 고객은 Secure Mail을 모바일 ActiveSync 클라이언트로 표준화하는 경우가 많습니다. 이러한 표준화는 첫 번째 시나리오에 설명된 것과 같이 공개된 Exchange Server에서 ActiveSync 서비스가 인터넷에 공개되는 것을 방지하기 위해 수행됩니다.
MAM SDK 사용 또는 MDX 래핑 앱에서만 마이크로 VPN 기능을 사용할 수 있습니다. MDX 래핑을 사용하는 경우 이 시나리오는 기본 클라이언트에 적용되지 않습니다. 타사 클라이언트를 MDX Toolkit으로 래핑할 수도 있지만 일반적인 사례는 아닙니다. 장치 수준 VPN 클라이언트를 사용하여 기본 또는 타사 클라이언트에 대한 터널링된 액세스를 허용하려는 솔루션은 과정이 복잡하고 실행 가능하지 않은 것으로 검증되었습니다.
시나리오 3: 클라우드에서 호스트되는 Exchange 서비스
클라우드에서 호스트되는 Exchange 서비스(예: Microsoft Office 365)의 인기가 높아지고 있습니다. XenMobile의 컨텍스트에서 이 시나리오는 첫 번째 시나리오와 동일하게 다뤄질 수 있습니다. ActiveSync 서비스가 인터넷에 공개되기 때문입니다. 이 경우 클라우드 서비스 공급자 요구 사항에 따라 클라이언트를 선택해야 합니다. 일반적으로 대부분의 ActiveSync 클라이언트(예: Secure Mail) 및 다른 기본 또는 타사 클라이언트를 선택할 수 있습니다.
XenMobile은 이 시나리오의 세 가지 영역에서 더 많은 가치를 제공합니다.
- Secure Mail의 MDX 정책 및 앱 관리를 사용하는 클라이언트
- 지원되는 기본 이메일 클라이언트에서 MDM 정책을 사용하여 클라이언트 구성
- Exchange ActiveSync용 Endpoint Management 커넥터를 사용한 ActiveSync 필터링 옵션
메일 트래픽 필터링 고려 사항
인터넷에 공개되는 대부분의 서비스와 마찬가지로, 경로를 보호하고 허가된 액세스에 대한 필터링을 제공해야 합니다. XenMobile 솔루션에는 기본 및 타사 클라이언트를 위한 ActiveSync 필터링 기능을 제공하도록 설계된 두 가지 구성 요소가 포함되어 있습니다. Exchange ActiveSync용 Citrix Gateway 커넥터와 Exchange ActiveSync용 Endpoint Management 커넥터입니다.
Exchange ActiveSync용 Citrix Gateway 커넥터
Exchange ActiveSync용 Citrix Gateway 커넥터는 Citrix ADC를 ActiveSync 트래픽의 프록시로 사용하여 경계에서 ActiveSync 필터링을 제공합니다. 필터링 구성 요소가 메일 트래픽 흐름의 경로에 배치되므로 메일이 환경에 들어오거나 환경에서 나갈 때 트래픽을 가로챕니다. Exchange ActiveSync용 Citrix Gateway 커넥터는 Citrix ADC와 XenMobile Server의 중간자 역할을 합니다. 장치가 Citrix ADC의 ActiveSync 가상 서버를 통해 Exchange와 통신하면 Citrix ADC가 Exchange ActiveSync용 커넥터 서비스에 대한 HTTP 콜아웃을 수행합니다. 그러면 이 서비스가 XenMobile을 통해 장치 상태를 확인합니다. 장치 상태에 따라 Exchange ActiveSync용 커넥터는 연결 허용 또는 거부에 대한 회신을 Citrix ADC로 보냅니다. 사용자, 에이전트 및 장치 유형 또는 ID에 따라 액세스를 필터링하는 정적 규칙을 구성할 수도 있습니다.
이 설정을 사용하면 추가 보안 계층을 통해 Exchange ActiveSync 서비스를 인터넷에 공개하여 허가되지 않은 액세스를 방지할 수 있습니다. 설계 고려 사항은 다음과 같습니다.
- Windows Server: Exchange ActiveSync용 커넥터 구성 요소를 사용하려면 Windows Server가 필요합니다.
- 필터링 규칙 설정: Exchange ActiveSync용 커넥터는 사용자 정보가 아닌 장치 상태 및 정보를 바탕으로 필터링하도록 설계되었습니다. 사용자 ID로 필터링하는 정적 규칙을 구성할 수는 있지만 예를 들어 Active Directory 그룹 구성원 자격으로 필터링하는 옵션은 없습니다. Active Directory 그룹 필터링에 대한 요구 사항이 있는 경우 Exchange ActiveSync용 Endpoint Management 커넥터를 대신 사용할 수 있습니다.
- Citrix ADC 확장성: Citrix ADC를 통한 ActiveSync 트래픽 프록시에 대한 요구 사항이 있는 경우 Citrix ADC 인스턴스 크기를 올바르게 조정하여 모든 ActiveSync SSL 연결의 추가된 작업 부하를 지원하는 것이 중요합니다.
- Citrix ADC 통합 캐싱: Citrix ADC의 Exchange ActiveSync용 커넥터 구성은 통합 캐싱 기능을 사용하여 Exchange ActiveSync용 커넥터의 응답을 캐싱합니다. 이 구성으로 인해 Citrix ADC는 지정된 세션의 모든 ActiveSync 트랜잭션에 대한 요청을 Exchange ActiveSync용 Citrix Gateway 커넥터에 전송하지 않아도 됩니다. 이 구성은 충분한 성능 및 확장성에 대해서도 중요한 역할을 합니다. 통합 캐싱은 Citrix ADC Platinum Edition을 통해 사용하거나 Enterprise Edition의 기능에 대한 라이센스를 개별적으로 취득할 수 있습니다.
- 사용자 지정 필터링 정책: 사용자 지정 Citrix ADC 정책을 만들어 표준의 기본 모바일 클라이언트 외의 특정 ActiveSync 클라이언트를 제한해야 할 수 있습니다. 이 구성을 사용하려면 ActiveSync HTTP 요청 및 Citrix ADC 응답자 정책 만들기에 대한 지식이 있어야 합니다.
- Secure Mail 클라이언트: Secure Mail에는 Micro VPN 기능이 있습니다. 이 기능을 사용하면 경계에서 필터링을 수행하지 않아도 됩니다. Secure Mail 클라이언트는 Citrix Gateway를 통해 연결되는 경우 일반적으로 내부(신뢰할 수 있는) ActiveSync 클라이언트로 여겨집니다. 기본 및 타사(Exchange ActiveSync용 커넥터 포함) 클라이언트와 Secure Mail 클라이언트를 모두 지원해야 합니다. Secure Mail 트래픽은 Exchange ActiveSync용 커넥터에 사용된 Citrix ADC 가상 서버를 통하지 않는 것이 좋습니다. 이 트래픽이 DNS를 통해 흐르도록 하고 Exchange ActiveSync용 커넥터 정책이 Secure Mail 클라이언트에 영향을 미치지 않도록 할 수 있습니다.
XenMobile 배포의 Exchange ActiveSync용 Citrix Gateway 커넥터 다이어그램은 온-프레미스 배포용 참조 아키텍처를 참조하십시오.
Exchange ActiveSync용 Endpoint Management 커넥터
Exchange ActiveSync용 Endpoint Management 커넥터는 Exchange 서비스 수준에서 ActiveSync 필터링을 제공하는 XenMobile 구성 요소입니다. 따라서 메일이 XenMobile 환경에 들어올 때가 아니라 Exchange 서비스에 도달할 때만 필터링이 한 번 수행됩니다. Mail Manager은 PowerShell을 사용하여 Exchange ActiveSync에 장치 파트너 관계 정보를 쿼리하고 장치 격리 동작을 통해 액세스를 제어합니다. 이러한 동작은 Exchange ActiveSync용 Endpoint Management 커넥터 규칙 기준에 따라 장치를 격리하거나 격리 해제합니다. Exchange ActiveSync용 Citrix Gateway 커넥터와 마찬가지로 Exchange ActiveSync용 Endpoint Management 커넥터는 XenMobile을 통해 장치 상태를 확인하여 장치 규정 준수에 따라 액세스를 필터링합니다. 장치 유형 또는 ID, 에이전트 버전 및 Active Directory 그룹 구성원 자격에 따라 액세스를 필터링하는 정적 규칙을 구생할 수도 있습니다.
이 솔루션에는 Citrix ADC의 사용이 필요하지 않습니다. 기존 ActiveSync 트래픽의 라우팅을 변경하지 않고 Exchange ActiveSync용 Endpoint Management 커넥터를 배포할 수 있습니다. 설계 고려 사항은 다음과 같습니다.
- Windows Server: Exchange ActiveSync용 Endpoint Management 커넥터 구성 요소를 사용하려면 Windows Server를 배포해야 합니다.
- 필터링 규칙 설정: Exchange ActiveSync용 Citrix Gateway 커넥터와 마찬가지로 Exchange ActiveSync용 Endpoint Management 커넥터에는 장치 상태를 평가하는 필터링 규칙이 포함됩니다. 또한 Exchange ActiveSync용 Endpoint Management 커넥터는 Active Directory 그룹 구성원 자격을 기준으로 필터링하는 정적 규칙을 지원합니다.
- Exchange 통합: Exchange ActiveSync용 Endpoint Management 커넥터는 ActiveSync 역할을 호스트하는 Exchange CAS(클라이언트 액세스 서버)에 직접 액세스하고 장치 격리 동작을 제어할 수 있어야 합니다. 이 요구 사항은 환경 아키텍처 및 보안 상태에 따라 문제가 될 수 있습니다. 따라서 이 기술 요구 사항을 사전에 평가하는 것이 중요합니다.
- 다른 ActiveSync 클라이언트: Exchange ActiveSync용 Endpoint Management 커넥터는 ActiveSync 서비스 수준에서 필터링을 수행하므로 XenMobile 환경 외의 다른 ActiveSync 클라이언트를 고려해야 합니다. Exchange ActiveSync용 Endpoint Management 커넥터 정적 규칙을 구성하면 다른 ActiveSync 클라이언트에 의도하지 않은 영향이 발생하는 것을 방지할 수 있습니다.
- 확장된 Exchange 기능: Exchange ActiveSync와 Exchange ActiveSync용 Endpoint Management 커넥터를 직접 통합하면 XenMobile이 모바일 장치에서 Exchange ActiveSync 초기화를 수행할 수 있습니다. 또한 XenMobile은 Exchange ActiveSync용 Endpoint Management 커넥터를 통해 Blackberry 장치에 대한 정보에 액세스하고 다른 제어 작업을 수행할 수 있습니다.
XenMobile 배포의 Exchange ActiveSync용 Endpoint Management 커넥터 다이어그램은 온-프레미스 배포용 참조 아키텍처를 참조하십시오.
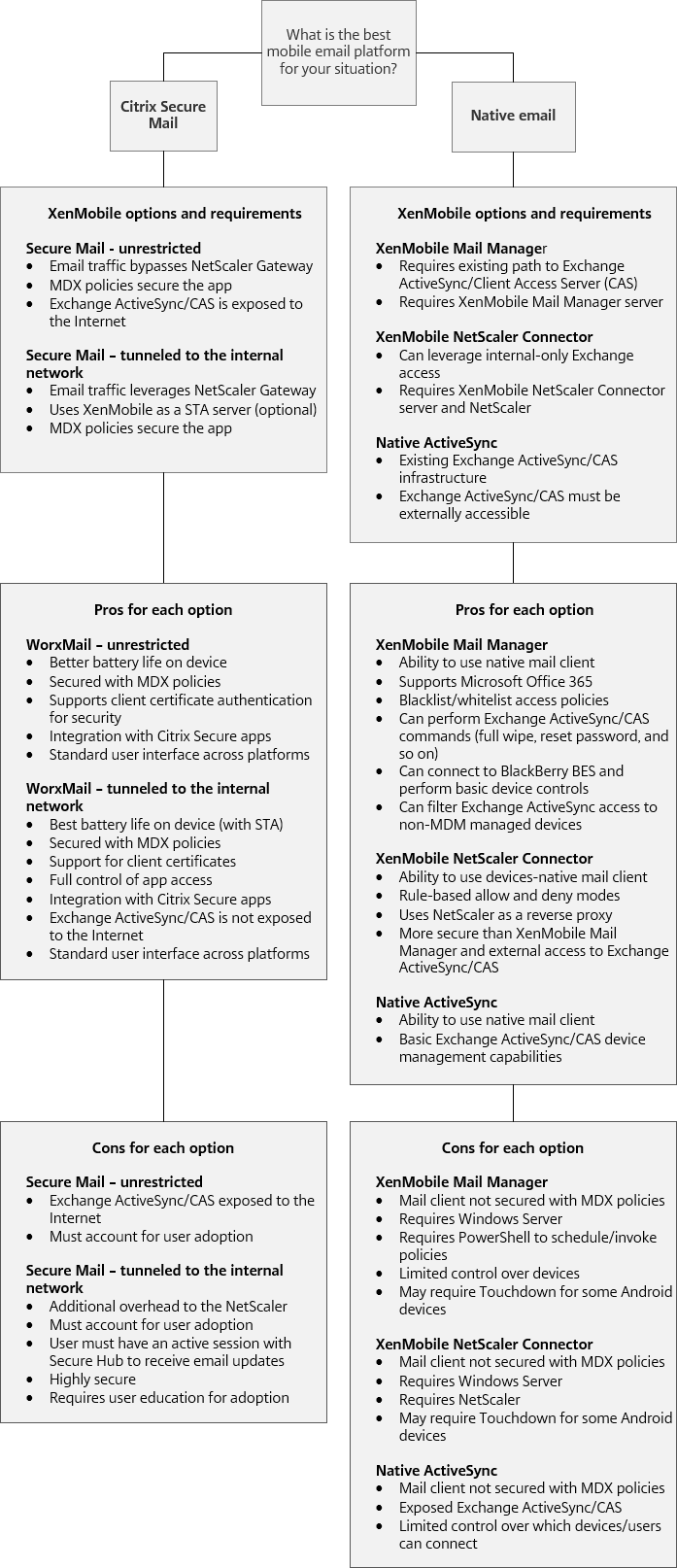
전자 메일 플랫폼 의사 결정 트리
다음 그림은 XenMobile 배포에서 기본 전자 메일과 Secure Mail 솔루션을 사용할 때의 장점과 단점을 이해하는 데 도움이 됩니다. 연결된 XenMobile 옵션과 서버, 네트워크 및 데이터베이스 액세스 지원을 위한 요구 사항을 고려하여 솔루션을 선택할 수 있습니다. 장점 및 단점에는 보안, 정책 및 사용자 인터페이스 고려 사항에 대한 세부 정보가 포함됩니다.